New Encryption Method Withstands Attacks From Both Computers and Artificial Intelligence
•February 5, 2026
0
Why It Matters
Eidolon offers a non‑lattice alternative for post‑quantum signatures, expanding the security toolbox as quantum threats loom. Its demonstrated resistance to both classical and machine‑learning attacks strengthens confidence in combinatorial‑based cryptography.
Key Takeaways
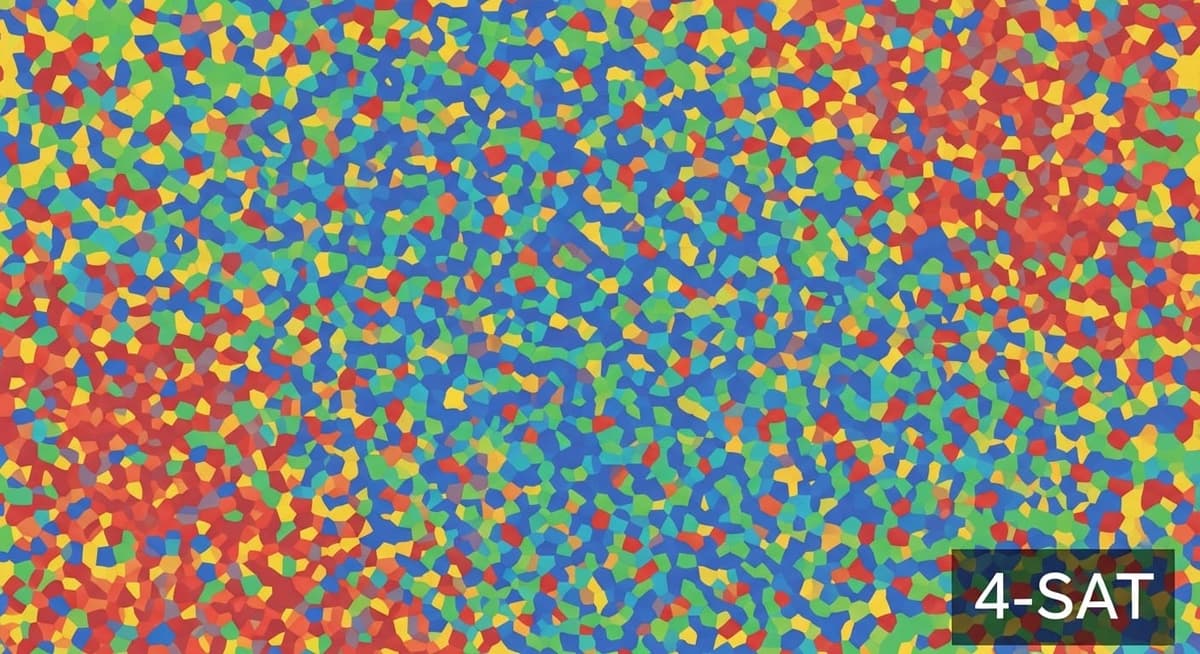
- •Eidolon uses k‑colourability NP‑complete problem for signatures.
- •Signature size reduced from O(t n) to O(t log n) via Merkle trees.
- •Graphs with ≥60 vertices resist classical solvers and GNN attacks.
- •“Quiet” colourings preserve random graph statistics, preventing easy solving.
- •Revives combinatorial hardness as alternative to lattice‑based post‑quantum crypto.
Pulse Analysis
The race to secure digital communications against quantum computers has largely centered on lattice‑based and code‑based schemes, yet reliance on a single class of hard problems creates systemic risk. Combinatorial problems such as graph k‑colourability have long been dismissed for cryptography because crafted instances can be solved efficiently, but recent advances in instance generation are changing that narrative. By embedding ‘quiet’ colourings—secret colour assignments that blend seamlessly into random Erdős‑Rényi graphs—researchers restore the intrinsic difficulty of the problem, providing a fresh hardness assumption for the post‑quantum era.
Eidolon translates this theoretical breakthrough into a practical signature protocol. It builds on a classic zero‑knowledge proof framework, replacing the linear‑size commitment phase with a Merkle‑tree structure that shrinks the communication overhead from O(t n) to O(t log n). The authors generated test instances ranging from 30 to 80 vertices, then challenged them with two conventional solvers—integer linear programming and the DSatur greedy algorithm—and a bespoke graph neural network trained to infer colourings. For graphs of 60 vertices or more, none of the attackers succeeded, confirming that the quiet‑colouring construction thwarts both exact and learning‑based attacks.
The significance of Eidolon extends beyond academic curiosity. By proving that combinatorial hardness can survive modern, AI‑driven cryptanalysis, the scheme offers a diversified portfolio of post‑quantum primitives, reducing the risk of a single point of failure. Enterprises seeking quantum‑resilient security can consider integrating Eidolon alongside lattice‑based standards, especially in environments where signature size and verification speed are critical. Ongoing work will need to address larger graph parameters, side‑channel resistance, and formal security reductions, but the current results mark a pivotal step toward broader adoption of graph‑based cryptography.
New Encryption Method Withstands Attacks from Both Computers and Artificial Intelligence
0
Comments
Want to join the conversation?
Loading comments...