Today's Cybersecurity Pulse
Microsoft tightens security on AI agents and code models
Microsoft announced new safeguards for its AI agents and code generation models, acknowledging emerging security risks. The company said it will impose stricter controls to limit autonomous agent actions, aiming to keep AI behavior in check.
Also developing:
By the numbers: Motorola Solutions to acquire D-Fend Solutions for $1.5B
Fuzzing Zephyr Apps - Struggles of Dynamic Analysis on Embedded Applications - Jayashree Srinivasan
The video presents Jayashree Srinivasan’s deep dive into fuzzing Zephyr‑based embedded applications, outlining why dynamic analysis is essential for safety‑critical IoT devices. She explains core concepts of fuzzing—randomized input injection, coverage collection, crash detection—and contrasts it with static analysis, noting lower false‑positive rates and ability to expose runtime faults such as buffer overflows in real‑time loops. Srinivasan cites concrete bugs discovered in Zephyr drivers (e.g., unchecked packet length leading to underflow) and highlights research tools like the LIP fuzzer integrated into LLVM, as well as rehosting frameworks (QEMU, Simics) and hardware‑in‑loop loops that emulate peripheral registers. The discussion underscores that building a faithful execution environment is the primary bottleneck; hybrid strategies that blend hardware‑in‑loop testing with high‑fidelity emulation can scale fuzzing across diverse MCU families, accelerating vulnerability discovery for manufacturers and regulators.

06-032026 WG-BEAR Regular Meeting
The WG-BEAR working group held a routine meeting to confirm interim co-chair arrangements while Marcela is away, onboard a new member (Raul), and review agendas and logistics for upcoming calls and SIG interactions. Members clarified that the DevRel/Zebra SIG runs...
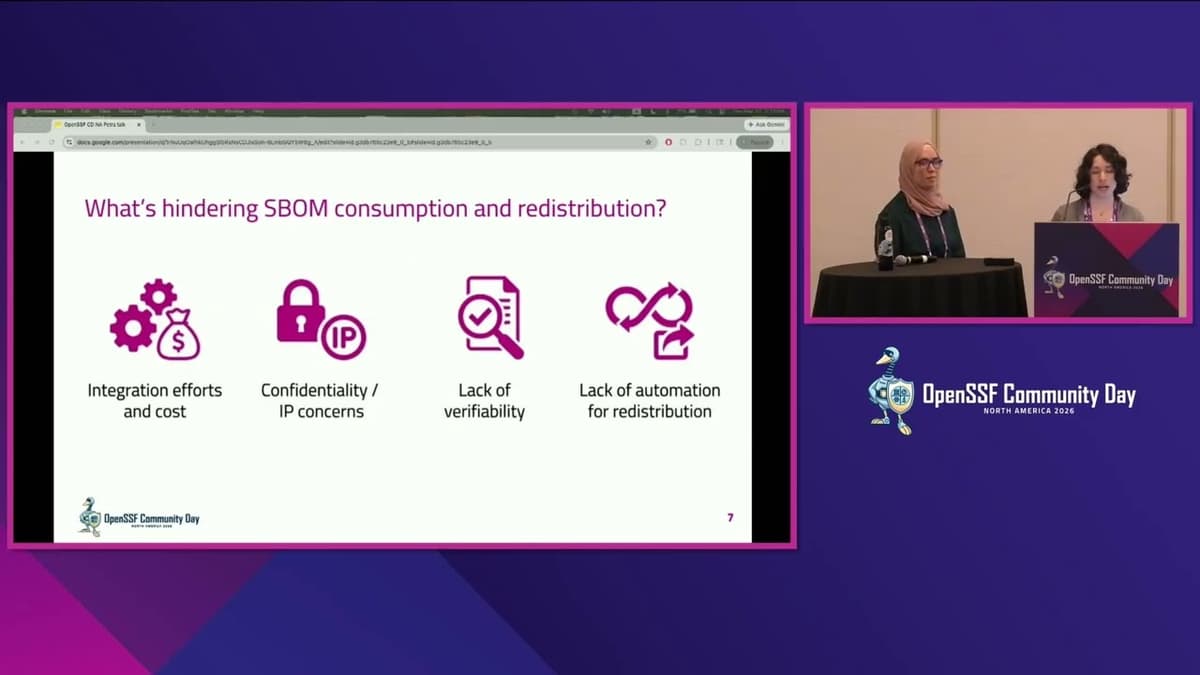
Petra: SBOMs Without Oversharing for Confidential Supply Chain... Eman Abu Ishgair & Marcela Melara
The presentation introduced Petra, a system designed to enable trustworthy and confidential exchange of Software Bill of Materials (SBOMs). The speakers highlighted the "SBOM paradox": while SBOMs are essential for compliance, auditing, and supply‑chain security, only about 21% of organizations...

🔴 Jun 3's Top Cyber News NOW! - Ep 1145
On Episode 1145 of Simply Cyber’s Daily Cyber Threat Brief, host Dr. Gerald broadcast live from Cisco Live in Las Vegas, mixing community engagement, sponsor plugs and a Wayback Wednesday segment while troubleshooting minor streaming issues. The show highlighted practical...

AI Won’t Save Cybersecurity
Two Cyber Chicks host Jax welcomes Kathleen Morerti, former CTO, CISO and founder of Security Bias, to dissect the hype that artificial intelligence will "fix" cybersecurity. Morerti draws on a decade of protocol‑level experience and recent work in cloud‑native, zero‑trust...

Navigating the Land of Git Commit Signatures With Gittuf - Patrick Zielinski & Yongjae Chung
In a talk demonstrating commit-signature pitfalls, Patrick Zielinski and Yongjae Chung show how author metadata can be easily spoofed and how forge “verified” badges can be misleading. They introduce GitTuf, an OpenSSF-incubating security layer that embeds signatures and policy metadata...

AI‑Generated Worm Unveiled by U of T Threatens All Internet‑Connected Devices
University of Toronto scientists demonstrated a new class of AI‑generated worm that can infiltrate any internet‑connected device using free, open‑weight models. The proof‑of‑concept shows attackers could launch sophisticated attacks at near‑zero cost, prompting immediate calls for new defenses.

Carnival Corporation Breach Exposes Personal Data of Nearly 6 Million Passengers
Carnival Corporation disclosed that a social‑engineering attack on April 14 gave hackers access to personal data of nearly 6 million cruise passengers. The company blocked the intrusion, engaged third‑party experts and is offering two years of free credit monitoring, while regulators probe...

CISA Warns of Active Attacks Exploiting Android, Linux Bugs
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added two high‑severity flaws to its Known Exploited Vulnerabilities (KEV) catalog: Android CVE‑2025‑48595 and Linux CVE‑2022‑0492. The Android bug is an integer overflow in the framework that grants privilege escalation on Android...
AI Is Worsening Firms’ Cybersecurity 'Fog of War'
At the BNY INSITE conference, Insigneo’s chief compliance officer demonstrated how a synthetic video can impersonate a high‑net‑worth client, highlighting AI’s ease of misuse. Panelists warned that frontier AI tools are now available to cyber‑criminals, enabling cheap, large‑scale deep‑fake phishing...

Trezor Says Safe 7 Chip Flaw Found by Ledger Does Not Put Funds at Risk
Trezor and chipmaker Tropic Square disclosed a vulnerability in the TROPIC01 secure‑element used in the Trezor Safe 7 hardware wallet. The flaw, uncovered by Ledger’s Donjon team through a laser fault‑injection test, allows extraction of certain chip‑held secrets but cannot alone...

Russia’s FSB Says Foreign Spies Infected Officials’ Phones With Malware
On June 2, 2026 Russia’s Federal Security Service announced it had uncovered a large‑scale operation by foreign intelligence that implanted malware on the mobile phones of senior Russian officials. The alleged code could steal data, intercept calls and activate microphones...
China-Linked TA4922 Hackers Target UK, Europe With New SilentRunLoader Malware
China‑aligned cybercrime group TA4922, previously focused on East Asian victims, has broadened its campaign to the UK, Germany, Italy and South Africa. The group uses tax‑ and payroll‑themed phishing emails to lure employees into downloading malware hosted on services like...

Dashlane Breach: Hackers Steal Encrypted Vaults After Brute‑forcing 2FA, Affecting ~20 Users
Dashlane disclosed that attackers brute‑forced its two‑factor authentication system and downloaded encrypted password vaults from about 20 customer accounts. The stolen data remain unreadable without each user’s master password, but the breach highlights vulnerabilities in MFA implementations for consumer security...

Kirki, Burst Statistics WordPress Plugin Flaws in Attackers’ Crosshairs
Security firm Defiant has identified critical flaws in two popular WordPress plugins—Kirki (versions 6.0.0‑6.0.6) and Burst Statistics (versions 3.4.0‑3.4.1.1). The Kirki bug (CVE‑2026‑8206, CVSS 9.8) lets an unauthenticated attacker obtain a password‑reset link for any admin account, while the Burst Statistics...

Simplify Security Management with CIS SecureSuite Platform
The Center for Internet Security launched the CIS SecureSuite Platform, consolidating CIS CSAT Pro and CIS‑CAT Pro Dashboard into a single interface for members. The platform offers unified visibility, automated assessments against CIS Controls, ISO 27001, NIST CSF and now includes...
Listen up, England. The Health Secretary Is Going to Be Data Controller for Everyone's Single Patient Record
Health Secretary James Murray announced he will serve as data controller for England’s new Single Patient Record (SPR), a system that will pool NHS data from GP surgeries, trusts and other providers into a shared platform accessible via the NHS...

Hackers Target Global Stock Exchange in Espionage Operation
A senior executive’s Outlook mailbox at a major global stock exchange was compromised for roughly 150 days, from October 2025 to March 2026. Symantec and Carbon Black traced the intrusion to malware masquerading as Adobe and OneDrive, with command‑and‑control channels activated...

IMA Diligence Services Data Breach Impacts 525,000 People
IMA Diligence Services disclosed a data breach that compromised personal and financial records of 525,306 individuals. The intrusion, traced to a third‑party managed legacy server, occurred between Dec 8 and Dec 16, with attackers exfiltrating roughly 700 GB of data. The Genesis ransomware...

Acer Working to Patch Max Severity Zero-Days in Wave 7 Routers
Acer disclosed two critical zero‑day flaws in its Wave 7 mesh routers, affecting firmware up to version T7c_GBL_1.01.000055. CVE‑2026‑49200 lets unauthenticated attackers read clear‑text credentials from the acer_cgi.log file, while CVE‑2026‑49201 exploits a hard‑coded AES key in upload.cgi to inject persistent...

Microsoft Wants to Put AI Agents on a Short Leash
At Microsoft Build 2026, the company unveiled a suite of security controls aimed at containing autonomous AI agents used in software development. The centerpiece is Microsoft Execution Container (MXC), a policy‑driven sandbox that runs agent‑generated code on Windows, Linux and...