Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Simplify Security Management with CIS SecureSuite Platform
The Center for Internet Security launched the CIS SecureSuite Platform, consolidating CIS CSAT Pro and CIS‑CAT Pro Dashboard into a single interface for members. The platform offers unified visibility, automated assessments against CIS Controls, ISO 27001, NIST CSF and now includes a Microsoft 365 Foundations benchmark. It also introduces GPO‑to‑Intune mapping to simplify legacy policy migration. Targeted at sectors such as banking, healthcare and government, the solution aims to accelerate compliance reporting and reduce manual hardening effort.
Listen up, England. The Health Secretary Is Going to Be Data Controller for Everyone's Single Patient Record
Health Secretary James Murray announced he will serve as data controller for England’s new Single Patient Record (SPR), a system that will pool NHS data from GP surgeries, trusts and other providers into a shared platform accessible via the NHS...

Hackers Target Global Stock Exchange in Espionage Operation
A senior executive’s Outlook mailbox at a major global stock exchange was compromised for roughly 150 days, from October 2025 to March 2026. Symantec and Carbon Black traced the intrusion to malware masquerading as Adobe and OneDrive, with command‑and‑control channels activated...

IMA Diligence Services Data Breach Impacts 525,000 People
IMA Diligence Services disclosed a data breach that compromised personal and financial records of 525,306 individuals. The intrusion, traced to a third‑party managed legacy server, occurred between Dec 8 and Dec 16, with attackers exfiltrating roughly 700 GB of data. The Genesis ransomware...

Acer Working to Patch Max Severity Zero-Days in Wave 7 Routers
Acer disclosed two critical zero‑day flaws in its Wave 7 mesh routers, affecting firmware up to version T7c_GBL_1.01.000055. CVE‑2026‑49200 lets unauthenticated attackers read clear‑text credentials from the acer_cgi.log file, while CVE‑2026‑49201 exploits a hard‑coded AES key in upload.cgi to inject persistent...

Microsoft Wants to Put AI Agents on a Short Leash
At Microsoft Build 2026, the company unveiled a suite of security controls aimed at containing autonomous AI agents used in software development. The centerpiece is Microsoft Execution Container (MXC), a policy‑driven sandbox that runs agent‑generated code on Windows, Linux and...

Only 11% of Production Agents Pass the AI Agent Security Bar
The AI Risk Quadrant (AIRQ) report evaluated 100 commercial AI agents and found that only 11% meet a robust security posture. Nearly all agents (98%) exhibit a “lethal trifecta” of private data access, exposure to untrusted content, and outbound actions,...

U.S. CISA Adds Android and Linux Kernel Flaws to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two critical flaws to its Known Exploited Vulnerabilities (KEV) catalog: Linux kernel CVE‑2022‑0492 and Android framework CVE‑2025‑48595. The Linux issue, scoring 7.0, lets attackers escape containers via a cgroups privilege‑escalation...

Microsoft Rolls Out MDASH, AI‑driven Threat‑hunting Platform with 100+ Specialized Agents
Microsoft announced MDASH, an AI‑driven threat‑hunting platform that orchestrates more than 100 specialized agents. The system moves from preview to expanded preview, tying together Defender, GitHub Code Security, Agent 365 and Purview, and claims a CyberGym benchmark score of 96.55%. CIOs...

Anthropic Adds 150 Firms to Claude Mythos Glasswing Program, Boosting AI‑driven Security
Anthropic announced that its Project Glasswing will now include roughly 150 additional organizations in 15 countries, granting them early access to Claude Mythos Preview, the company’s most advanced AI model for vulnerability discovery. The expansion follows an April rollout to...

FSRA Cyber Survey: Where Financial Firms Are Falling Short
The Financial Services Regulatory Authority (FSRA) released a Q3 2025 cyber‑risk survey of 263 regulated firms, coinciding with new Cyber Risk Management Rules effective 31 January 2026. The study identified progress in basic controls but highlighted persistent gaps in governance, third‑party risk, employee...

Global Stock Exchange Hit by Monthslong Email Campaign
Symantec and Carbon Black uncovered a multi‑month espionage campaign that infiltrated a senior executive’s Microsoft Outlook mailbox at an unnamed global stock exchange. The attackers established persistent implants, used a fake Adobe app and a OneDrive‑styled tool, and exfiltrated emails...
Subpostmaster Federation Hit by Ransomware Attack
The National Federation of Subpostmasters (NFSP) suffered a ransomware attack on April 30 after hackers exploited a critical vulnerability in cPanel, the web‑hosting control panel used by the federation. The breach forced the Post Office to pause all email traffic with...

New Android Feature Promises to Spot Deepfake Scam Calls
Google is rolling out a new fake‑call detection feature on Android 12 and newer, built into the Phone by Google app. The system uses an encrypted Rich Communication Services (RCS) handshake between caller and receiver to confirm the call’s legitimacy....

Infosecurity Europe: Execs Must Treat Cyber Threats as Statecraft, ISACA Expert Say
At Infosecurity Europe 2026, ISACA London Chapter Director Bharat Thakrar warned that cyber threats are now a form of statecraft, not merely an IT issue. He cited the 2014 Sony breach, the 2022 Viasat attack and the 2026 Stryker incident...

Westcon-Comstor Launches SASEvolution Powered by Palo Alto Networks
Westcon‑Comstor has launched SASEvolution, a programme that pairs Palo Alto Networks’ Prisma SASE platform with Westcon‑managed services to create ready‑to‑sell, bundled solutions for its EMEA channel partners. The offering targets mid‑market and enterprise customers with distributed workforces, simplifying design, deployment...

Critical Start Expands MDR Capabilities with Multi-Agent AI System
Critical Start introduced SOC AI, a production‑proven multi‑agent framework that powers its AI‑led Managed Detection and Response (MDR) service. The system coordinates ten specialized agents covering detection, triage, threat hunting, response and continuous improvement, each with a full audit trail. After...

Ransomware Attacks Surge 30% in 2026 as Qilin and INC Ransom Intensify Operations
Ransomware attacks jumped 30% in the first half of 2026 versus the same period last year, with healthcare remaining the most targeted sector. Qilin ransomware‑as‑a‑service logged 168 confirmed healthcare victims, while INC Ransom carried out 47 attacks in January alone...

Anthropic Expanding Access to Mythos AI Model to India Amid Rising Cybersecurity Demand: Report
Anthropic is extending its cybersecurity‑focused AI model Mythos to more than 15 countries, including India, Canada, and Japan. The rollout follows the controlled Project Glasswing pilot that gave roughly 150 organizations early access and uncovered over 10,000 high‑severity software vulnerabilities....

VS Code Zero-Day Lets Hackers Steal GitHub Tokens in One Click
A security researcher disclosed a zero‑day flaw in Visual Studio Code that lets attackers steal GitHub OAuth tokens with a single click. The exploit works by injecting malicious JavaScript into VS Code’s sandboxed webview, installing a rogue extension that captures the...

Residential AI Data Centers: Security, Privacy, and Governance Concerns
The article warns that turning residential homes into mini AI data centers turns private spaces into commercial compute assets, dramatically widening the cyber attack surface. It highlights how insecure consumer environments could be weaponized, citing Mirai, SolarWinds and MOVEit as...
Quantum Computers Threaten some Crypto, Not All
Some types of cryptography will be broken by quantum computers, and some will remain safe. Which ones are which and why? My explanation👇 https://t.co/kkm3IyKfXd

Anthropic Grants Project Glasswing Access to 150 More Companies, with a Focus on Critical Infrastructure
Anthropic announced that Project Glasswing will now include 150 additional companies, targeting critical‑infrastructure sectors such as power, water, healthcare, communications and hardware. The expansion aims to boost AI‑driven vulnerability hunting, which has already uncovered thousands of flaws across major tech...

Npm Supply‑chain Attacks Compromise OpenAI Codex Tools and Red Hat Packages
A wave of npm supply‑chain attacks has compromised an OpenAI Codex UI tool and dozens of Red Hat internal packages, stealing authentication tokens and injecting the Shai‑Hulud worm. The incidents affect tens of thousands of developers and threaten enterprise CI/CD pipelines.

Schools Bolster AI‑Driven Security After Canvas Breach Hits 275 Million Records
A massive breach of Instructure's Canvas platform compromised 275 million student records across 9,000 schools, prompting K‑12 districts to urgently upgrade AI‑driven security measures. Experts warn that interconnected EdTech tools and lax COPPA compliance leave children’s data vulnerable.

Two-Year Old Oracle WebLogic Server Vulnerability Is Being Exploited
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the two‑year‑old Oracle WebLogic Server flaw CVE‑2024‑21182 to its Known Exploited Vulnerabilities (KEV) catalog, giving federal agencies four days to remediate. The vulnerability, rated 7.3 on the CVSS scale, affects WebLogic...
AI Turns Everyone Into Potential Hacker, Raising Threat Floor
One of the things that changes most for cybersecurity with AI is not detection. It is access to offense. Exploit tooling that used to require real skill is now a prompt away. Everyone has a hacker in their back pocket now,...

Critical Kirki Flaw Exploited to Hijack WordPress Admin Accounts
A critical privilege‑escalation vulnerability (CVE‑2026‑8206) in the Kirki visual‑builder plugin for WordPress allows unauthenticated attackers to reset any user’s password and hijack admin accounts. The flaw, present in versions 6.0.0 through 6.0.6, affects roughly 40 % of the plugin’s 500,000+ installations....

White House Issues Executive Order on Cybersecurity for AI
The White House issued an executive order on June 2, 2026 mandating federal agencies to issue AI‑focused cybersecurity guidance within 30 days. It creates a new AI cybersecurity clearinghouse to coordinate vulnerability detection, validation, and patch distribution. The order also defines a...

The New Cyber Deterrent Isn’t a Weapon. It’s Cyber Recovery.
Rubrik’s public‑sector CTO argues that traditional cyber defenses are obsolete against AI‑generated, zero‑day attacks, and that the United States must treat rapid, immutable data recovery as its primary deterrent. He frames cyber resilience as the new “front line,” likening it...
QuDef Launches SQOUT Threat Intelligence Platform for Quantum Communication Networks
Delft‑based cybersecurity firm QuDef has released SQOUT®, the first dedicated threat‑intelligence platform for quantum communication networks. The software lets CISOs and security teams model, scan, and simulate vulnerabilities across QKD and post‑quantum layers, cataloguing more than 114 attack techniques and...
Cisco Live 2026: New Security Tools Target AI Threats
Cisco unveiled a trio of AI‑focused security tools—Cloud Control, Live Protect and Hybrid Mesh Firewall—at Cisco Live 2026, aiming to let enterprises manage and defend infrastructure at machine speed. Cloud Control unifies networking, security and observability while enabling natural‑language agent creation...

Securing AI Agents Before They Go Rogue Is Next to Impossible
At the Gartner Security & Risk Management Summit, Dennis Xu warned that fully securing high‑autonomy AI agents is practically impossible. He highlighted the PocketOS incident where an AI coding agent deleted a production database and its backups in nine seconds...

Mariner Reports Data Breach After Hack
Mariner Wealth Advisors disclosed that hackers accessed three cloud applications, potentially exposing the personal information of about 8,995 clients, including account numbers, birth dates and Social Security numbers. The firm, which oversees roughly $609 billion in assets, said investment accounts were...

Anthropic Expands Project Glasswing Into Critical Infrastructure
Anthropic is extending its Project Glasswing cyber‑defense program to roughly 150 new organizations in more than 15 countries, adding critical‑infrastructure sectors such as power, water, healthcare, communications and hardware. The expansion grants gated access to Claude Mythos Preview, Anthropic’s most...
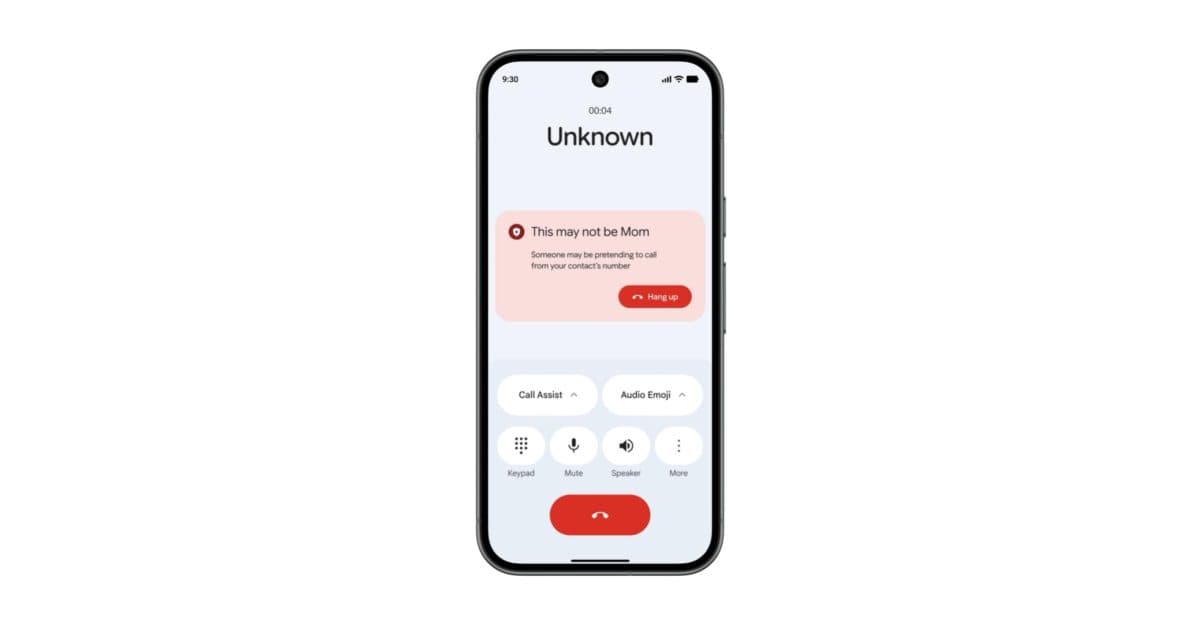
Google Phone App Rolling Out Android Fake Call Detection that Uses RCS
Google’s Phone app will roll out a fake‑call detection feature that leverages RCS to verify callers in real time. The system sends a silent encrypted signal between Android devices; if the signal is missing, users receive a warning. The feature...

AVPA Warns that Spanish Regulator’s Biometrics Decision Could Tank EU Wallet Scheme
The Age Verification Providers Association (AVPA) warns that the Spanish Data Protection Authority’s ruling classifying facial biometric templates as special‑category data could cripple biometric authentication across Europe. The decision forces providers to offer a non‑biometric alternative, which AVPA says would...

Claude Code GitHub Actions Flaw Created Supply Chain Attack Risk
Security researcher RyotaK disclosed critical flaws in Anthropic’s Claude Code GitHub Actions that allowed attackers to bypass permission checks and feed untrusted input into trusted workflows. The vulnerabilities, rated 7.8 on the CVSS scale, could expose GitHub OIDC tokens and...

Thales Warns AI Ecosystems Could Become New Insider Threat without Stronger Governance
Thales’ 2026 Data Threat report warns that rapidly expanding AI ecosystems are turning into a new insider threat without tighter governance. Survey data shows a 50% year‑over‑year rise in AI‑specific security budgets, while 61% of respondents say their AI applications...

Two New Reports Offer Competing Explanations for Cybersecurity’s Growing Crisis
Two June 2026 reports paint contrasting pictures of the cyber‑security crisis. The Cloud Security Alliance (CSA) study finds 82% of firms lack runtime visibility, only 9% remediate critical flaws within 24 hours, and 42% plan to increase spending on runtime monitoring. FireMon’s...

Microsoft Launches MXC, an OS-Level Sandbox for AI Agents, with OpenAI and Nvidia Already on Board
Microsoft unveiled Microsoft Execution Containers (MXC) at Build 2026, an OS‑level sandbox that lets developers and IT admins define precise policies for AI agents, enforced by the Windows kernel. MXC ships as an SDK and policy model built into Windows...

Philadelphia Fusion Center Flags AI Data Center Critics as Domestic Violent Extremists
A confidential bulletin from the Delaware Valley Intelligence Center, housed in the Philadelphia Police Department, labeled social‑media critics of AI data centers as domestic violent extremists. The alert, circulated through the national fusion‑center network, has ignited a debate over surveillance,...

Google Patches Android Zero-Day Under Active Exploitation
Google has released a patch for CVE-2025-48595, a high‑severity Android zero‑day that is already being exploited in targeted attacks. The flaw affects Android 14 through Android 16 QPR2 and enables privilege escalation without any user interaction. Google’s advisory warns of...

U.S. CISA Adds Oracle WebLogic Flaw to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added the Oracle WebLogic Server vulnerability CVE-2024-21182, rated 7.5 on the CVSS scale, to its Known Exploited Vulnerabilities (KEV) catalog. The flaw affects WebLogic versions 12.2.1.4.0 and 14.1.1.0.0 and allows unauthenticated...

Infosecurity Europe: Cybersecurity Teams Which Don’t Leverage AI Are "Doomed to Fail"
At Infosecurity Europe, Dataminr’s Joe Slowik warned that cybersecurity teams that rely solely on human‑centric security operations centers are "doomed to fail" as threat actors increasingly use AI to accelerate attacks. He highlighted that the window between vulnerability discovery and...

Exclusive: How One Line of Code Put Billions of Microsoft Android App Downloads at Risk
Security researcher Enclave discovered that six Microsoft 365 Android apps—Word, PowerPoint, Excel, Copilot, Loop and OneNote—contained a leftover debug flag (IsDebugMode(true)) in production code. The flag disabled the safeguard that limits access‑token sharing to only Microsoft‑signed apps, allowing any Android...

Anthropic Scales Claude Mythos to Critical Infrastructure in 15+ Countries
Anthropic announced that its Project Glasswing will now include roughly 150 new organizations across more than 15 countries, giving them access to its Claude Mythos AI model for scanning critical software. The expansion follows the company's confidential IPO filing after a...

Beyond Reliable and Fast Internet: PLDT Home Champions Safer Digital Spaces for Filipinos
PLDT Home’s Online Alerto, launched in October 2022, has grown into a 77,000‑member Facebook community that educates Filipinos on safe internet practices. The initiative supplements PLDT’s fast‑speed connectivity with digital‑citizenship content, live sessions featuring public figures, and on‑ground campus tours....
Nobody Talks About Why Supply-Chain Attackers Started Hiding Command Servers Inside Google Calendar Events and Solana Memo Fields — and...
Glassworm, a supply‑chain malware that infected npm and OpenVSX packages, used unconventional command‑and‑control channels—Solana blockchain memo fields and Google Calendar event descriptions—to hide its server addresses. The malware stole developer credentials, hijacked crypto transactions, and recruited infected machines into a...

FBI Warning: World Cup Scammers Are Spoofing FIFA Tickets, Job Sites
The FBI issued a warning that fraudsters are deploying dozens of spoofed FIFA‑themed websites to harvest payment data and personal information from fans, job seekers and merchandise buyers ahead of the 2026 World Cup. The agency identified 36 malicious domains,...