Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

XRP Ledger Teams with Project Eleven to Guard Against Quantum Attacks
The XRP Ledger announced a partnership with post‑quantum security firm Project Eleven to audit its validator, wallet and custody layers and develop hybrid signature schemes. The move positions the blockchain to transition to quantum‑resistant cryptography before quantum computers become capable of breaking current encryption.

Sen. Rick Scott and Rep. Andy Ogles Push Stronger Defenses Against China-Backed Cyber Threats
Sen. Rick Scott and Rep. Andy Ogles called on Congress to fast‑track the Strengthening Cyber Resilience Against State‑Sponsored Threats Act, warning that Chinese groups like Volt Typhoon have already breached U.S. critical infrastructure. Their appeal underscores growing bipartisan concern over...

Coro Joins Leader’s Marketplace
Leader has added Coro’s AI‑driven cyber security platform to its Australian Cloud marketplace, giving MSPs and reseller partners a unified solution for endpoint, email, cloud, and network protection. The modular platform lets partners deploy only the capabilities their customers need,...

Beware of Financial Scammers Wielding Deepfake Tech
Deepfake-enabled fraud has shifted from a novelty to a persistent corporate risk, with synthetic audio and video remaining in circulation for an average of 3.5 years. A voice clone of a German energy‑company CEO persisted nearly six years, causing a...

Alleged Kimwolf Botmaster ‘Dort’ Arrested, Charged in U.S. and Canada
Canadian authorities arrested 23‑year‑old Jacob Butler of Ottawa, accused of building and operating the Kimwolf IoT botnet that generated record DDoS attacks up to 30 Tbps. The U.S. Justice Department unsealed a criminal complaint in Alaska, charging Butler with computer intrusion...

U.S. CISA Adds Microsoft and Adobe Flaws to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added seven known‑exploited vulnerabilities to its KEV catalog, covering legacy Microsoft Windows, DirectX, Internet Explorer, Defender, and an Adobe Acrobat flaw. The list includes critical CVSS scores up to 9.8, such...

Chinese State‑Sponsored Hackers Deploy Showboat and JMFBackdoor Malware Against Telecom Operators
China‑aligned Calypso (also known as Red Lamassu) has been actively compromising telecommunications providers with two new implants—Showboat for Linux and JMFBackdoor for Windows—since mid‑2022. The campaign, uncovered by Lumen’s Black Lotus Labs and PwC Threat Intelligence, leverages modular persistence, SOCKS5 proxying,...

Google API Keys Remain Active After Deletion
Researchers at Aikido Security discovered that Google Cloud Platform API keys remain usable after deletion, with a median revocation window of about 16 minutes and a maximum of 23 minutes. The study showed wide variability across regions—some tests saw a...

Verizon DBIR Finds Mobile Phishing Beats Email, Click‑Throughs Up 40%
Verizon’s 2026 Data Breach Investigations Report reveals mobile‑centric phishing now eclipses email, delivering a 40% higher click‑through rate. The shift, documented across 31,000 incidents in 145 countries, forces organizations to rethink awareness training and technical controls.

Satoshi’s 1.1 Million Bitcoin and Millions More Can Be Saved From Quantum Attack, Says Expert
AmericanFortress unveiled a patent‑pending post‑quantum signature scheme that would protect existing crypto assets, including dormant wallets, via a backward‑compatible soft fork. The protocol aims to freeze and secure pre‑BIP32 Bitcoin addresses—such as Satoshi’s 1.1 million BTC and roughly 5 million dormant coins—while...
Microsoft Plans Significant Update to Windows Secure Boot
Microsoft is rolling out its first Secure Boot certificate update in 15 years, with the 2011‑based certificates set to expire between June 27 and October 2026. For Windows desktops, the fix requires a standard Windows Update plus a UEFI firmware...

Announcing Claude Compliance API Support with Cloudflare CASB
Cloudflare announced that its Cloud Access Security Broker (CASB) now integrates with Anthropic’s Claude Compliance API, giving enterprises direct visibility into Claude Enterprise and Platform usage from the Cloudflare dashboard. The integration surfaces DLP‑related findings for projects, chat files, messages,...

Americans Can’t Spot a Deepfake, and That’s a Business Crisis, Not Just a Consumer Problem
A Veriff‑Kantar 2026 survey of 3,000 adults in the U.S., U.K. and Brazil found Americans score just 0.07 on deep‑fake detection – essentially random guessing. While 63% of U.S. adults recognize the term “deepfake,” half claim confidence in spotting them,...

MFA Verifies Who Logged In. It Has No Idea What They Do Next.
Enterprises relying solely on multi‑factor authentication are vulnerable because once a user logs in, the session token is trusted indefinitely, allowing attackers to move laterally without triggering alerts. NOV’s CIO Alex Philips discovered this architectural blind spot and implemented rapid...

Exploits Arrive Before Disclosure: Assume Exposure, Accelerate Detection
“Mean time to exploit” is now effectively negative. Attackers are exploiting vulnerabilities before disclosure. Modern defense means assuming exposure, investing in detection and response, and using AI to reduce dwell time faster. https://t.co/3pHSy0XEWm https://t.co/Cma1mjX3V1
MacOS Kernel Memory Corruption Exploit
The poem, misleadingly titled “macOS Kernel Memory Corruption Exploit,” is a visceral lyrical exploration of trauma, identity loss, and existential dread. It paints a bleak urban tableau filled with broken altars, shattered Buddhas, and dying insects, using stark imagery to...
Deleted Google API Keys Remain Active up to 23 Minutes, Study Finds
Aikido Security discovered that Google API keys remain functional for up to 23 minutes after deletion, with an average lag of 16 minutes. The delay stems from eventual consistency across Google’s global authentication servers, allowing attackers to continue accessing enabled...

AI-Generated Emails Make Business Email Compromise Nearly Undetectable
AI-powered generators are producing business‑email compromise (BEC) messages that mimic real executives and vendors, making detection almost impossible. The FBI reports over $20 billion in internet‑crime losses in 2025, with BEC as the second‑largest method, prompting urgent calls for cost‑free verification...

Tenable OPEN Expands the Partner Play for Exposure Management
Tenable announced the Tenable Open Partner Exchange Network (OPEN), a platform that links its Tenable One solution with more than 330 validated security integrations. The initiative enables bi‑directional data movement, allowing customers to import third‑party findings and push Tenable’s exposure...

Reveal: FedRAMP Authorization for Legal Cloud Vendors
FedRAMP authorization has become a non‑negotiable prerequisite for legal cloud vendors seeking federal contracts. Agencies now require it before considering eDiscovery or litigation‑support proposals, effectively sidelining vendors without the certification. The shift replaces informal, agency‑specific security agreements with a centralized,...

CISA Asks Cybersecurity Community to Alert It to Vulnerability Exploitation
The Cybersecurity and Infrastructure Security Agency (CISA) has introduced a public form that lets security researchers, vendors and other experts nominate vulnerabilities for inclusion in its Known Exploited Vulnerabilities (KEV) catalog. Submissions must include the CVE identifier, evidence of active...

Targeting Trust: Lessons From the Stryker Cyberattack for Healthcare
The March cyberattack on medical‑technology company Stryker exposed a new attack vector: the compromise of identity‑management and certificate‑issuance systems that establish digital trust. By infiltrating these trust layers, attackers could potentially weaponize entire fleets of connected medical devices rather than...

UK Plans for Cybercrime Law Reform Would Protect Almost No One, Experts Warn
The UK government plans to amend the 1990 Computer Misuse Act by introducing a statutory defence that would only protect security researchers conducting scans of internet‑facing systems. The defence would be limited to British nationals holding chartered accreditation from the...

GitHub Breach Traced to Malicious 'Nx Console' VS Code Extension
GitHub confirmed that a malicious version of the Nx Console VS Code extension compromised 3,800 internal repositories after an attacker uploaded the poisoned package to the Visual Studio Marketplace. The extension, which had 2.2 million installs, fetched an obfuscated payload that harvested...
Cranium AI Acquires Aiceberg to Strengthen Its End-to-End AI Security, Governance and Agentic AI Platform
Cranium AI announced the acquisition of Aiceberg, an agentic AI security specialist, to build the largest independent end‑to‑end platform for AI lifecycle protection, governance, and compliance. The deal integrates Aiceberg’s risk‑mapping technology with Cranium’s security framework, extending coverage from model...

Chinese APTs Share Linux Backdoor in Central Asia Telco Attacks
Chinese state‑aligned APT groups have been deploying a Linux post‑exploitation framework called Showboat, also known as kworker, against telecommunications providers in Central Asia and beyond. The tool, observed in Afghanistan, Ukraine’s Donbas region and other low‑maturity markets, is shared among...

Europol and Eurojust Shut Down First VPN Network
A joint operation led by Europol and Eurojust has dismantled 'First VPN,' taking 33 servers offline and seizing key domain names. https://t.co/K4asmKk77x

Content Delivery Exploit Opens Websites to Brand Hijacking
Researchers at ADAMnetworks have identified a new exploit called Underminr that lets attackers hijack brand‑trusted websites by manipulating DNS, SNI and Host fields, effectively bypassing CDN mitigations. The flaw affects roughly 42% of all domains worldwide and over half of...

Containing the Breach: Elisity and the Rise of Microsegmentation
A massive ransomware breach at Conduent exposed data of at least 25 million people, underscoring how lateral movement fuels cyber‑incidents. Traditional network segmentation often leaves broad zones that attackers can roam, while microsegmentation isolates each device, user and application by identity....

Visa Flags AI‑Driven Scams as Fastest‑Growing Consumer Payment Fraud
Visa’s Spring 2026 Biannual Threats Report warns that AI‑accelerated scams have become the fastest‑growing source of consumer payment fraud, with almost $1 billion in scam‑related activity detected between July and December 2025. The report says fraudsters are using AI‑generated content and...

Versa Applies Zero-Trust Controls to AI Agent Actions with New MCP Architecture
Versa Networks unveiled a zero‑trust architecture for its Model Context Protocol, embedding it in the AI‑powered operations co‑pilot Versa Verbo and the VersaONE Universal SASE Platform. The new layer validates every AI‑generated network action against user identity, role‑based access controls,...
Three-Quarters of Firms Knowingly Ship Vulnerable Code
A new Checkmarx study finds 75% of organizations still ship code they know contains vulnerabilities, a slight improvement from 81% last year but still alarming. AI‑generated code is dramatically accelerating exploit timelines, shrinking the average time‑to‑exploit from 840 days in...
Strategies, Expert Insights From the 2026 Verizon DBIR
The 2026 Verizon Data Breach Investigations Report analyzed 31,000 security events, including 22,000 confirmed breaches across 145 countries, marking its largest dataset ever. For the first time, software vulnerabilities eclipsed stolen credentials as the leading initial access vector, accounting for...
Nine-Year-Old Linux Kernel Flaw Leaks SSH Keys and Password Hashes
A nine‑year‑old logic flaw in the Linux kernel’s ptrace path (CVE‑2026‑46333) enables unprivileged local users to read sensitive files such as SSH host private keys and the /etc/shadow password hash on default Debian, Fedora and Ubuntu installations. The vulnerability resides...

Scammers Are Abusing an Internal Microsoft Account to Send Spam Links
Scammers have been exploiting a loophole in Microsoft’s internal email system to send spam from the legitimate notification address msonlineservicesteam@microsoftonline.com. By creating new Microsoft‑online accounts that appear as genuine customers, they can dispatch phishing messages that mimic official alerts. The...

When Identity Is the Attack Path
A cached AWS access key on a single Windows workstation gave an attacker potential access to 98% of the company’s cloud workloads, illustrating how a single credential can become a full‑scale attack path. The article argues that identity—whether AD groups,...

TeamPCP Hijacks 3,800 GitHub Repos in Massive Open‑Source Supply‑Chain Assault
TeamPCP, a prolific cybercrime group, breached GitHub on Tuesday night, compromising roughly 3,800 repositories and adding to a spree that has injected malicious code into more than 500 open‑source tools. The attack underscores a new, self‑perpetuating supply‑chain threat that could...
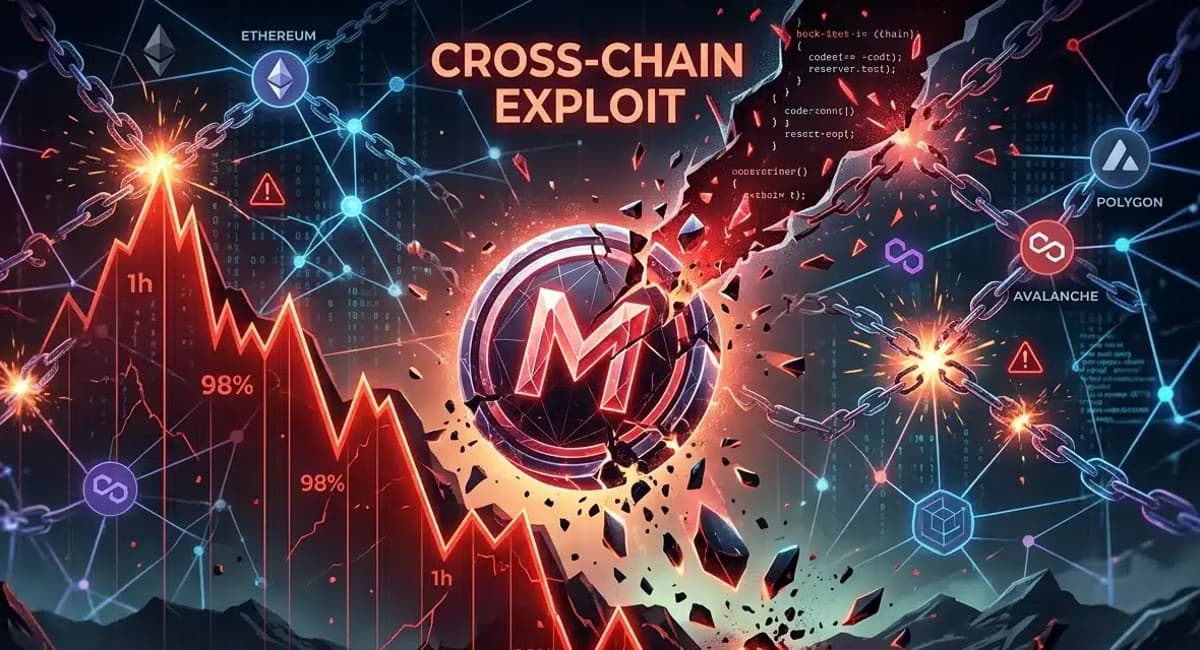
Hackers Exploit Butter Network Bridge to Mint Massive MAPO Supply
Hackers exploited a Solidity flaw in the Butter Network cross‑chain bridge, minting a quadrillion MAPO tokens and flooding the market. The attacker moved roughly one billion MAPO onto Uniswap, draining about 52 ETH (≈ $180,000) and driving the token price from $0.003...

Bluesky Says Kremlin Is Hacking Its Platform to Spread Propaganda
Bluesky disclosed that Russian actors have hijacked hundreds of real user accounts to post fabricated articles and AI‑generated videos, a tactic the platform says is unprecedented. The compromised accounts span journalists, academics, pollsters and creators, including a Colorado School of...
A Hacker Group Is Poisoning Open Source Code at an Unprecedented Scale
A cyber‑crime group known as TeamPCP has escalated software supply‑chain attacks to a near‑weekly cadence, compromising hundreds of open‑source tools and extorting victims. In the latest breach, GitHub disclosed that roughly 3,800 of its repositories were poisoned through a malicious...

Microsoft Warns of New Defender Zero-Days Exploited in Attacks
Microsoft began deploying patches on May 21 for two actively exploited Defender zero‑day flaws—CVE‑2026‑41091, a privilege‑escalation bug in the Malware Protection Engine, and CVE‑2026‑45498, a denial‑of‑service issue in the Antimalware Platform. The vulnerabilities affect older Defender versions and can grant SYSTEM...

Why Marks and Spencer Is Spending £140m on Digital and Technology This Year After Putting the Cyber-Crisis of 2025 Behind...
Marks & Spencer is committing roughly $179 million to a digital‑and‑technology overhaul after a 2025 cyber‑attack that cost the retailer about $168 million and drove online sales down 18.4%. CEO Stuart Machin says the spend will focus on AI, data capabilities, a...

AI Becoming an SOC Imperative for Curtailing Emerging Cyber Threats
At the DTX conference in Manchester, experts warned that AI is becoming a security operations centre (SOC) imperative for defending against autonomous cyber threats. While AI can automate log correlation, triage and reduce alert fatigue, panelists stressed that robust fundamentals—patching,...

Pardus Linux Vulnerability Chain Enables Complete System Takeover
A critical privilege‑escalation chain (CVE‑2026‑5140) in Pardus Linux lets any unprivileged user obtain full root access in seconds. The flaw combines a Polkit policy misconfiguration, a CRLF injection in SystemSettingsWrite.py, and an untrusted‑search‑path bug in AutoAptUpgrade.py. Scoring 9.3 on CVSS...

Ukraine Busts Massive Cybercrime Scheme Behind 28,000 Stolen Accounts
Ukrainian National Police uncovered an international cybercrime ring that stole nearly 30,000 customer accounts from a California‑based online retailer. The operation, driven by an 18‑year‑old Odessa resident, used infostealer malware to harvest login credentials and session cookies, enabling fraudulent purchases...

GitHub Confirms Cyberattack Targeting Thousands of Internal Repositories
GitHub disclosed that a threat group identified as TeamPCP breached thousands of its internal code repositories after compromising an employee’s machine with a malicious Visual Studio Code extension. The attackers attempted to monetize the stolen source by offering it for...

Ten AI Cyber Vulnerability Questions - NCSC
The UK National Cyber Security Centre (NCSC) released a checklist of ten questions for organisations that deploy AI models to discover cyber‑security flaws. It stresses that AI‑driven detection is only valuable if basic security hygiene—such as patching and access control—is...

GitHub Internal Repositories Breached via Malicious Nx Console VS Code Extension
GitHub confirmed that a compromised version of the Nx Console VS Code extension was used to breach its internal repositories, exposing roughly 3,800 codebases. The malicious extension was published on the Visual Studio Marketplace for only 18 minutes before being removed,...

Microsoft Is Working on a Patch for ‘YellowKey’ Attack on Bitlocker, Offers Temporary Fix
Microsoft disclosed a zero‑day vulnerability, CVE‑2026‑45585 (YellowKey), that lets attackers with physical access bypass BitLocker encryption and read or write files. A public proof‑of‑concept is already available, prompting an urgent advisory with interim mitigation steps. The company is evaluating a...

OpenAI Daybreak Launches Agentic AppSec Workflow with GPT‑5.5 and Codex Security
OpenAI introduced Daybreak, an AI‑driven application security workflow that pairs GPT‑5.5 models with its Codex Security harness. The platform, already used by hundreds of organizations and credited with more than 3,000 vulnerability fixes, aims to embed threat modeling, discovery and...