Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Fake App Drains Filipino Retiree’s Life Savings via ‘Malware-as-a-Service’
A fraudulent mobile app, sold as a help‑desk tool, infected a 68‑year‑old Filipino retiree's phone with malware‑as‑a‑service, allowing criminals to siphon his life‑savings. The attack illustrates a broader shift in Southeast Asian cybercrime, where organized groups in Cambodia are moving from low‑tech "pig‑butchering" scams to industrial‑scale, high‑speed digital heists. The malware gains real‑time control, harvests biometric data, and can execute unauthorized transactions without the victim’s knowledge. Authorities warn that the service model lets even low‑skill actors launch sophisticated attacks at scale.
AI Will Empower, Not Undermine, Security Teams
Somebody asked me here at the conference: given AI advances, are we fucked in D&R and SOCs? I said “no, AI will help a lot here, this is fine, defenders will be fine.” (1/2)

Cyber Techniques Being Used to ‘Support the Repression of British Individuals on Our Streets’, NCSC Head Warns
The UK’s National Cyber Security Centre (NCSC) warned that Russia and Iran are extending battlefield‑grade cyber techniques to target British interests. Richard Horne said Russia is applying lessons from the Ukraine war to attacks across the UK and Europe, while...

Unstructured Data Security Hindered by Visibility Gaps
One of the biggest security challenges with unstructured data is the lack of visibility and lineage as information moves across systems, clouds, and teams." #DataLineage #AI https://t.co/PYomJYHDkY

Chinese APT Abuses Multiple Cloud Tools to Spy on Mongolia
A newly identified Chinese APT group called GopherWhisper has been spying on Mongolia’s government, deploying at least five custom backdoors that each exploit a different mainstream cloud service for command‑and‑control. ESET researchers uncovered 12 compromised systems within a single agency...

Tropic Trooper APT Takes Aim at Home Routers, Japanese Targets
Tropic Trooper, a China‑linked APT active since 2011, has shifted to compromising home Wi‑Fi routers, hijacking DNS to deliver a watermarked Cobalt Strike beacon via a malicious dictionary‑app update. The group deployed new open‑source malware families—including DaveShell, Donut loader, Merlin and...

CrowdStrike Unveils Project QuiltWorks Coalition to Tackle AI‑Driven Vulnerabilities
CrowdStrike announced Project QuiltWorks, a cross‑industry coalition that includes Accenture, EY, IBM Consulting, Kroll and AI model providers OpenAI and Anthropic. The initiative will deliver continuous AI‑vulnerability assessments, board‑level risk reporting and guided remediation for enterprises facing a surge in...

SUSE and NVIDIA Unveil AI Factory: GitOps‑Driven Stack for Sovereign Enterprises
SUSE and NVIDIA announced the SUSE AI Factory at SUSECON in Prague, a GitOps‑driven software stack that combines SUSE AI and NVIDIA AI Enterprise for secure, sovereign AI workloads. The solution targets regulated enterprises and is slated for general availability...

Compliance Startup Delve Tied to New Vercel Data Breach via Context AI Client
Compliance firm Delve, already under fire for alleged audit fraud, is now linked to Vercel's latest data breach after its former client Context AI was used as an entry point. The incident underscores how trusted certification vendors can become supply‑chain...

How Indirect Prompt Injection Attacks on AI Work - and 6 Ways to Shut Them Down
Indirect prompt injection attacks embed malicious instructions in web pages, emails or other external content that large language models (LLMs) automatically read. Unlike direct attacks, they require no user interaction, allowing threat actors to exfiltrate data, execute commands, or hijack...

From the Microsoft Dynamics 365 Business Central Blogs: Cloud Migration; External Storage; Better Reporting; Critical Security Practices
Microsoft’s Dynamics 365 Business Central blog series highlights four critical topics for ERP users: cloud migration, external storage for attachments, reporting evolution, and essential security practices. Author Stefano Demiliani warns partners not to reuse the same self‑hosted Azure Integration Runtime during...

AI Security Brief
The AI Security Brief episode introduces a new podcast aimed at cybersecurity leaders who need to stay ahead of rapidly evolving AI safety regulations and threats. Hosts Johnny Hand and Dustin Childs, both active practitioners, explain that each episode will...
Confidential Guest Reset on QEMU Hypervisor: Design Choices and Approach
QEMU 11.0 introduces a reset mechanism for AMD SEV‑SNP and Intel TDX confidential guests, a capability co‑developed by Red Hat. Previously, attempts to reboot such guests forced termination because the hypervisor could not access encrypted CPU registers. The new design performs...

Confidential Clusters for Red Hat OpenShift: Developer Preview Now Available on Microsoft Azure with AMD SEV-SNP
Red Hat announced a Developer Preview of confidential clusters for OpenShift, extending confidential computing from individual pods to the entire cluster. The preview runs on Microsoft Azure and leverages AMD’s SEV‑SNP hardware‑rooted trust. A new Kubernetes‑native confidential cluster operator automates...

Mullvad VPN Creates iOS Master Switch to Protect Users From Data Leaks
Mullvad VPN announced an optional iOS "master switch" that forces all app traffic through the VPN, eliminating the platform’s notorious data‑leak and LocalNet vulnerabilities. The new includeAllNetworks setting is disabled by default and a built‑in alert prompts users to turn...

Apple Stops Weirdly Storing Data That Let Cops Spy On Signal Chats
Apple released an iOS update that closes a logging flaw which unintentionally stored Signal push‑notification snippets on iPhones. The bug could keep fragments of encrypted messages for up to a month, even after the messages vanished or the app was...

FedNow Fortifies Security for Instant Payments
On April 28, the Federal Reserve’s Financial Services arm will roll out a network intelligence API for FedNow participants. The tool supplies receiver‑level account data and leverages historical FedNow transactions to generate instant risk insights before payments are executed. After...

NIST Cyber Center to Launch OT ‘Visibility’ Project
The National Institute of Standards and Technology’s Cybersecurity Center of Excellence is rolling out a new operational‑technology (OT) visibility project aimed at helping critical‑infrastructure owners inventory and monitor legacy assets. The initiative will demonstrate how to achieve OT asset visibility...

Government Experts Gather for Tech Event
Government Cybersecurity & AI 2026 will convene senior federal, state and local officials in Canberra on April 29‑30. The two‑day event brings together CISOs, CIOs, policy makers and cyber experts to discuss responsible AI adoption and emerging security threats. Presentations,...

Newly Deciphered Sabotage Malware May Have Targeted Iran’s Nuclear Program—And Predates Stuxnet
Researchers at SentinelOne have reverse‑engineered Fast16, a stealthy sabotage malware first compiled in 2005, making it the oldest known state‑sponsored code of its kind. The malware silently spreads across networks and subtly corrupts calculations in high‑precision simulation tools such as...

Privacy Vulnerability in Firefox and TOR Browsers
Security firm Fingerprint uncovered a privacy flaw in Firefox and the Tor browser that let sites track users even in private‑browsing mode. The bug stemmed from a deterministic ordering of IndexedDB metadata, creating a unique fingerprint for each system. Mozilla...

Hackers Exploit File Upload Bug in Breeze Cache WordPress Plugin
A critical file‑upload vulnerability (CVE‑2026‑3844) in the Breeze Cache WordPress plugin allows unauthenticated attackers to upload arbitrary files, potentially leading to remote code execution. The flaw, scored 9.8 out of 10, has triggered more than 170 exploitation attempts recorded by...

When Mythos Finds Thousands of Zero-Days, EU Regulators Won’t Wait for Your SOC to Catch Up
Mythos will disclose hundreds to thousands of zero‑day findings at once, instantly triggering reporting obligations under the EU’s NIS2, Cyber Resilience Act (CRA) and Digital Operational Resilience Act (DORA). A typical 10‑analyst SOC can process roughly 320 findings in 24 hours,...

States Deploy Desktop as a Service To Standardize Endpoints and Boost Security
State IT leaders in Kansas, Indiana and New Mexico are rolling out Desktop as a Service (DaaS) platforms to centralize device provisioning, patching and security across thousands of endpoints. Kansas is deploying Tanium Endpoint Management on Dell hardware, while Indiana...

In a First, a Ransomware Family Is Confirmed to Be Quantum-Safe
A new ransomware family called Kyber is the first confirmed malware to use post‑quantum cryptography, specifically the ML‑KEM1024 algorithm, to wrap an AES‑256 key. Security firms Rapid and Rapid7 reverse‑engineered the code and found the quantum‑safe key exchange, though a...
3 Practical Ways AI Threat Detection Improves Enterprise Cyber Resilience
Enterprises are overwhelmed by thousands of low‑value security alerts, prompting a shift to AI‑driven threat detection. By building behavioral baselines for users, devices, identities and cloud workloads, AI reduces noise and surfaces genuine threats faster. Cross‑telemetry correlation and automated triage...

Citizen Lab Uncovers Telecom Vendors Exploiting SS7 and Diameter to Track Users
Citizen Lab disclosed two spying campaigns that leveraged weaknesses in SS7 and Diameter protocols, using three telecom operators to locate individuals. The findings highlight persistent vulnerabilities in global phone networks and raise regulatory concerns for carriers worldwide.

Bitwarden CLI Compromised in Checkmarx Supply‑Chain Attack Affecting 10M Users
Socket security researchers disclosed that the Bitwarden command‑line interface (CLI) version 2026.4.0 was compromised through a hijacked GitHub Action, part of the broader Checkmarx supply‑chain campaign. The breach impacts more than 10 million users and 50 000 businesses, highlighting the growing risk...

ServiceNow Seals $7.75 B Armis Deal, Bolstering Cyber‑exposure Portfolio
ServiceNow closed a $7.75 billion cash acquisition of cyber‑exposure platform Armis, adding real‑time asset visibility to its workflow engine. The deal, the largest cyber‑security M&A this quarter, aims to triple ServiceNow's addressable market for security and risk products.

UK VPN Group Warns Child‑Safety Plan Could Heighten Online Risks
The VPN Trust Initiative (VTI) has warned that the UK government's "Growing Up in an Online World" consultation, which seeks mandatory age‑verification on social platforms, could backfire by restricting VPNs that protect young users. The industry coalition argues that limiting...

Former U.S. Cyber Director Sounds the Alarm on Anthropic’s ‘Too Powerful’ AI Model
Anthropic’s new AI model Mythos can autonomously discover and exploit software vulnerabilities, prompting former U.S. Cyber Director Kemba Walden to label it “too powerful” for public release. The model has already identified thousands of high‑severity bugs across major operating systems...

Vercel Expands Breach Disclosure, Confirms More Compromised Customer Accounts
Vercel announced that a "small number" of customer accounts were compromised before its early‑April breach and that more accounts are now known to be affected. The expanded disclosure highlights broader security risks for fast‑growing SaaS platforms.

Exec‑Impersonation Vishing Targets IT Helpdesks, Bypassing MFA
Cybercriminals are now calling corporate IT helpdesks, pretending to be senior executives, and coercing staff to reset multi‑factor authentication (MFA) or enroll new devices. The technique, dubbed Okta vishing, leverages publicly scraped personal data and the urgency of remote‑work environments...

DOJ Charges Two Chinese Nationals Over $700 Million Myanmar Crypto Scam
The Justice Department indicted Huang Xingshan and Jiang Wen Jie for operating a cryptocurrency fraud compound in Myanmar that trafficked workers and stole more than $700 million from Americans. The case marks a major step in a cross‑border crackdown on crypto‑related...

Google Launches AI‑Led Cyber‑Defense Agents at Cloud Next, Promising Minute‑Scale Threat Detection
At Cloud Next in Las Vegas, Google announced three new AI agents that automate threat hunting, detection engineering and third‑party context enrichment. The rollout expands an existing AI stack that already processes millions of alerts, shrinking manual analysis from half...

Dynamic Privilege: Balancing Access and Security
Enterprises are plagued by static permissions that linger as employees shift roles, inflating the attack surface especially in business applications. Dynamic privilege, also called Privilege Security Posture Management, replaces role‑based grants with continuous, context‑driven decisions based on identity, entitlement and...
Meta Turns Employees Into Data Source for AI Replacements
Meta is recording employee keystrokes, mouse movements, and screenshots across Gmail, LinkedIn, VSCode, Wikipedia. Stated purpose? training data for computer-use AI agents. Translation? the white collar workforce is now the dataset for its own replacements. Passwords, product roadmaps, immigration status, health info, all...
Dragos: Despite AI Use, New Malware Targeting Water Plants Is ‘Hype’
Industrial‑cybersecurity firm Dragos dismissed the newly reported ZionSiphon malware as hype, noting it contains numerous coding errors and AI‑generated hallucinations. Darktrace initially flagged the sample as a threat to Israeli water treatment and desalination plants, claiming it could manipulate chlorine...
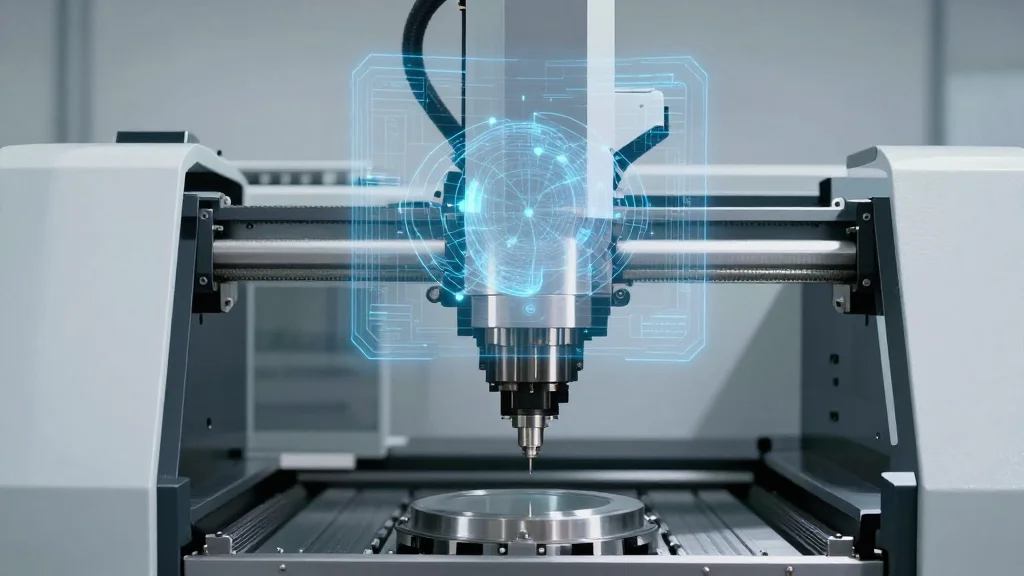
Digital Technologies and Cyber Security Are Changing Machine Tool Construction
Zimmermann, a German maker of high‑precision portal milling machines, is embedding cyber resilience, digital twins and artificial intelligence into its tool construction to satisfy the EU Cyber Resilience Act, Machinery Regulation and NIS 2 directives. The firm applies security‑by‑design, segmenting networks...

How to Add Security Layers to Your Agency Web Hosting Setup
Agencies face amplified risk because a single hosting breach can expose every client site in their portfolio. A layered, defense‑in‑depth strategy—starting with server‑level firewalls and extending through SSL, malware scanning, hardened access, automated backups, and continuous monitoring—provides comprehensive protection. Each...

Powerful AI Models Learn to Self‑Jailbreak Automatically
I mentioned this project in this week's AI Lab newsletter. It suggests a kind of flip side to the idea of self-improvement in AI models. As models become more powerful, it shows they can automate the process of figuring out...
Sony's 2011 Breach Exposed 77 Million PlayStation Accounts
#ThrowbackThursday. April 17, 2011. Sony began to notice its users about an attack that later disclosed to have compromised around 77 million of its PlayStation accounts. (CBS) https://t.co/iqjhF3SGSx

Compliance Is Broken. MSPs Are Fixing It.
Compliance has shifted from an occasional checklist to a continuous, resource‑intensive function, especially for mid‑market firms juggling HIPAA, SOC 2, state privacy laws and emerging AI governance. Internal IT teams often lack the authority, expertise, and bandwidth to keep pace with...

FCC Urges Court to Dismiss Hikvision Suit over Security Risk
.@FCC urges DC Circuit to reject Hikvision suit: "In any event, Hikvision’s arguments are meritless, particularly in view of the Secure Equipment Act, which ratifies and confirms the Commission’s authority to refuse equipment authorizations based on an unacceptable risk to...

Guard Your Credibility: Vet Every LinkedIn Connection
Friendly reminder that you shouldn't accept a connection from just anyone who asks to connect on LinkedIn. I see sham accounts that have legit people connected to them. They're obviously using these connections to lure others into connecting. Don't lend...

Bitwarden CLI Npm Package Compromised to Steal Developer Credentials
Bitwarden's command‑line interface npm package was compromised on April 22, 2026 when a malicious version (2026.4.0) was published to npm for roughly 1.5 hours. Attackers exploited a compromised GitHub Action in Bitwarden’s CI/CD pipeline to inject a loader that fetched the...

Payments Canada Strengthens Fraud Prevention Defenses and Broadens Membership Base
Payments Canada announced two strategic moves to strengthen Canada’s payment ecosystem. Patrick Boudreau, a veteran of fraud prevention at TransUnion and RBC, will join as Vice‑President of Fraud and Financial Crimes on April 30, 2026, overseeing the National Payment Fraud...

CISA: US Agency Breached Through Cisco Vulnerability, FIRESTARTER Backdoor Allowed Access Through March
The Cybersecurity and Infrastructure Security Agency (CISA) disclosed that a U.S. federal agency was compromised through a Cisco firewall vulnerability and later accessed via a persistent backdoor named FIRESTARTER. The malware allowed threat actors to regain control of the device...

Trigona Ransomware Attacks Use Custom Exfiltration Tool to Steal Data
Symantec reports that recent Trigona ransomware campaigns have switched to a bespoke command‑line exfiltration tool called uploader_client.exe. The utility accelerates data theft by opening five parallel connections per file and rotating TCP streams after 2 GB, while selectively skipping low‑value media....
Lowe’s Faces Pressure to Cut Ties with Flock Safety as AI Surveillance Data Raises Serious Privacy Concerns
Retail giant Lowe’s Home Improvement is under mounting pressure to end its contract with surveillance firm Flock Safety, which supplies AI‑driven cameras, drones and automated license‑plate readers at its stores. Recent reporting revealed that Flock’s data has been accessed by...