
Claude Mythos Shows AI Shifting to Exploit Validation
MyPOV: .@Anthropic's Claude Mythos isn't just another security tool — it's a signal that #AI is moving beyond scanning into the harder work: validating exploitability, chaining vulnerabilities, and closing the loop from finding to fix. Get the scoop from @Chirag_Mehta: https://t.co/enMgibemwI

Beyond AI: Creative Solutions for the Vulnerability Apocalypse
So it looks like some of you only skimmed my recent #VulnMgt blog https://t.co/6Wu6ApVyN8 and did not make it to the "15 minute experiment" ... Sure, vuln apoc is fun (for some), but "what do we do" also needs creative...
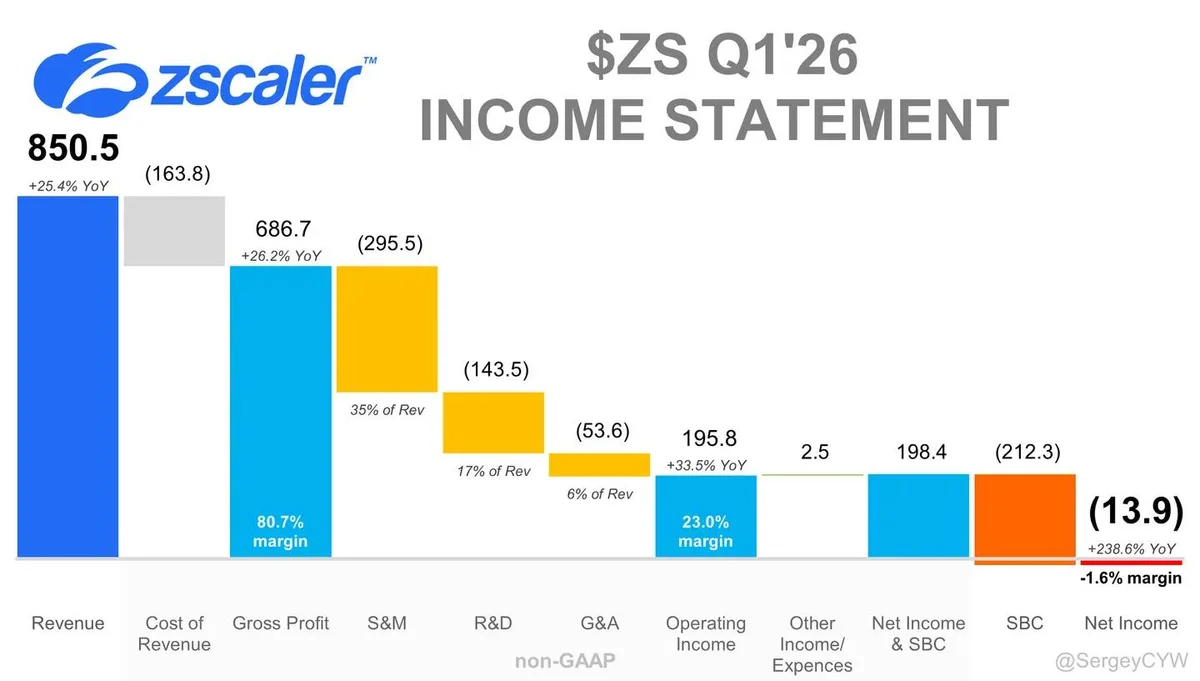
Zscaler Launches AI-Guardian for Zero Trust AI Agents
Zscaler is building Zero Trust security for the AI-agent era $ZS is expanding its AI security platform as enterprises move from traditional apps to autonomous AI systems. AI agents create a different security problem. They access data, trigger actions, inherit permissions, and...

Cisco and Splunk Turn Log Floods Into Threat Signals
From Log Flood to Threat Signal: Cisco and Splunk Bring Context to Modern Defense https://t.co/VaHbtpEhOU https://t.co/z8V0LCu07K

Breach Week Highlights: 7‑Eleven, Ameriprise, MyTheresa
Weekly update is up! Breach Week: 7-Eleven; Ameriprise; Mytheresa; Kemper; Charter; The Data Breach Disclosure Lag; Welcoming the Bhutanese Government https://www.troyhunt.com/weekly-update-506/
Balance AI Innovation with Governed System Access
Customer choice in AI tools connecting to core systems needs governed access. It's a line between responsible innovation and uncontrolled extraction. Encouraging innovation shouldn't cost security or governance. #AIChoice #DataGovernance https://t.co/qe11EuGL9P

CISA Flags Nx Console, GitHub Repos in Supply Chain Attacks
CISA warns that Nx Console and GitHub repositories abused in multiple supply chain compromises – tools across enterprise, cloud, and DevOps environments exploited https://t.co/AhpMs8oxpa

Company Knew of Carnival Leak, Gave No Notice
35 days ago, the Carnival data was published by ShinyHunters. Clearly, the company knew about it at the time (that’s how extortion works, plus the comment in the linked article) but at the time, I couldn’t find any disclosure notice,...

FBI Alerts: New Phishing Surge Hits Microsoft 365
The FBI warns Microsoft 365 services are being bombarded with new phishing emails – here are 3 steps you can take to stay safe https://t.co/4BlyWeYIpw
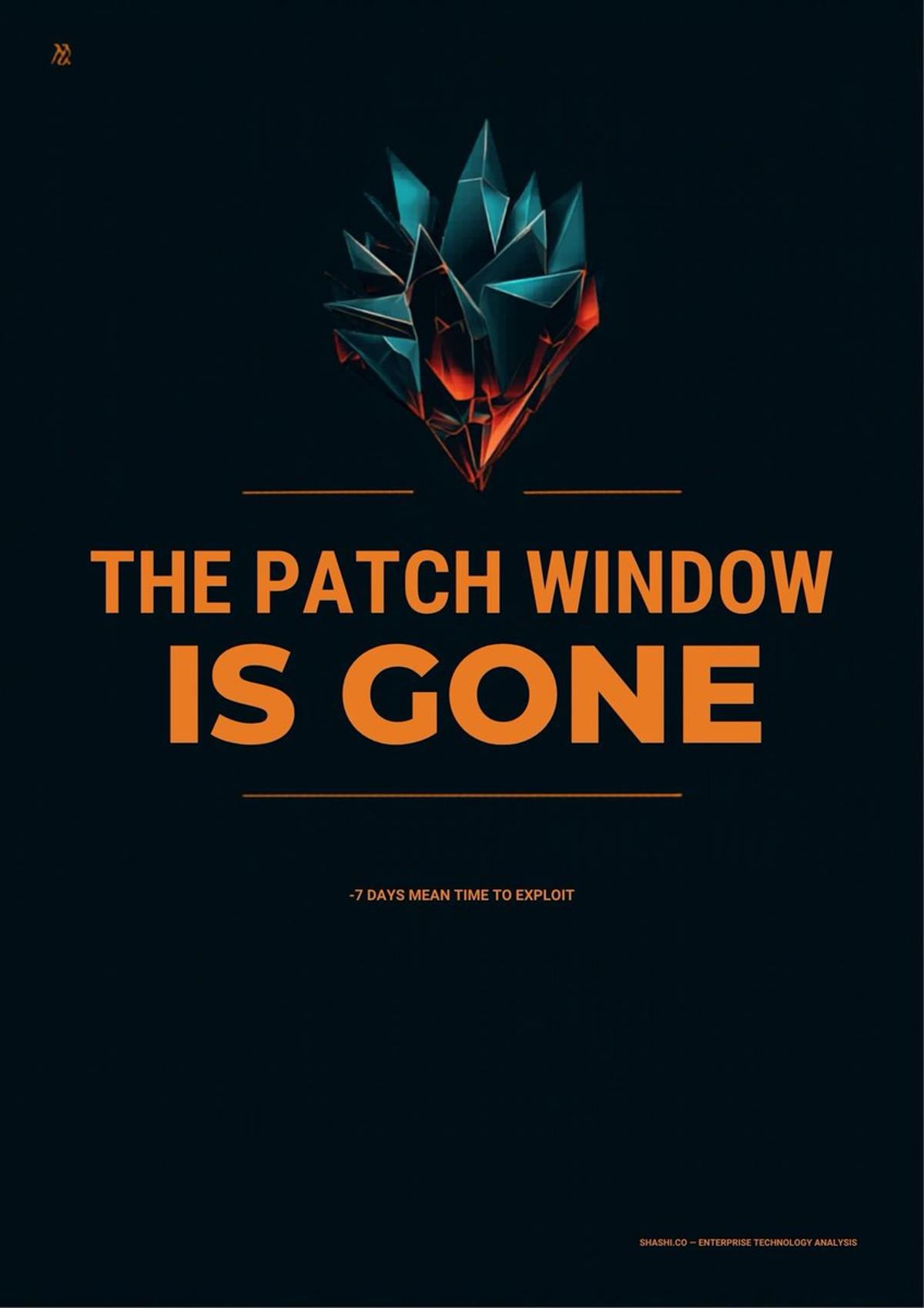
Exploits Arrive Before Patches: AI Defense Becomes Essential
The most important number in cybersecurity right now is negative seven. That's what Mandiant (part of Google Cloud)'s M-Trends 2026 report found: mean time to exploit is now an estimated -7 days. Exploitation is routinely happening before a patch is even...

48‑Hour SLA vs 48‑Minute Threats: Rethink Vulnerability Response
How do you manage when your SLA is 48 hours to remediate a critical vulnerability but the bad guys are finding it in 48 minutes? Mythos and AI-driven attacks have changed the math. Most vulnerability management programs were built for a...
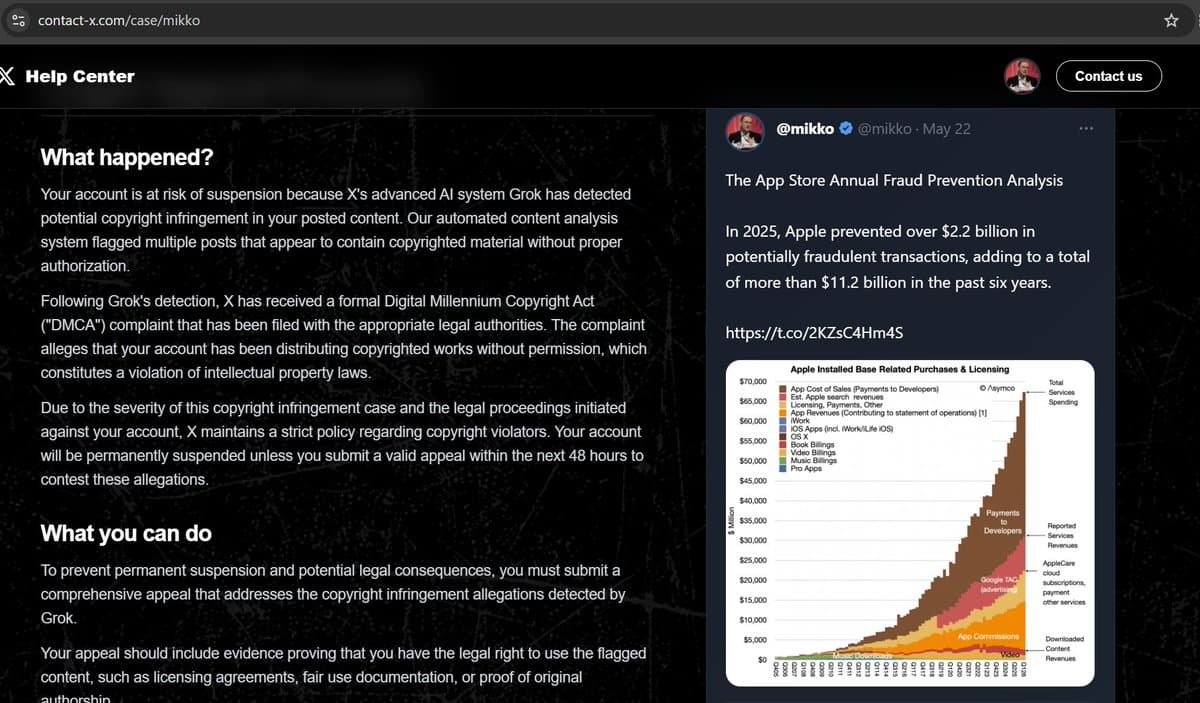
Beware: Fake AI Copyright Threat Emails Targeting Users
Scammers are sending emails pointing to "contact﹣x dot com", which hosts a fairly convinging site claiming that "Your account is at risk of suspension because X's advanced AI system Grok has detected potential copyright infringement in your posted content". Don't...

Cloud Atlas APT Leverages Hidden SSH Tunnels, Tor, PowerCloud
Today we’re having a look at both old and new tools from the Cloud Atlas APT group. The attackers actively use hidden SSH tunnels, Tor, RevSocks, the PowerCloud utility, and much more besides. A breakdown of the techniques and the...
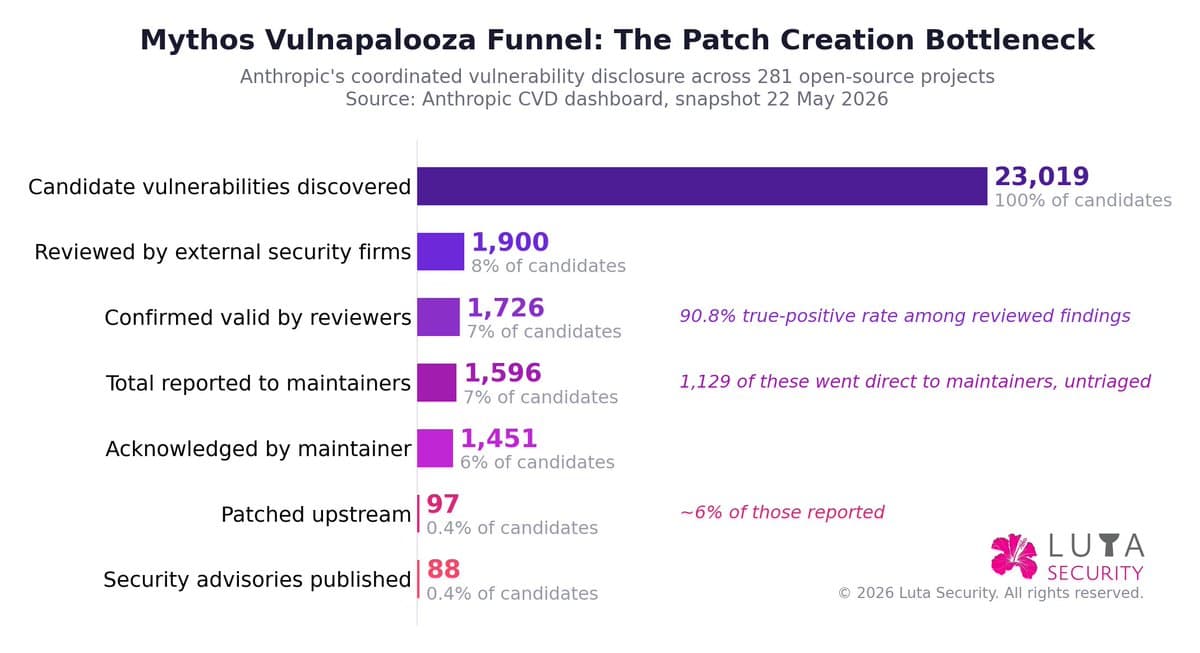
Systemic Approach to AI Vulnerability Coordination Reveals Patch Bottlenecks
New @LutaSecurity blog: AI Vulnerability Coordination at Vulnapalooza — First ##Mythos Encore. @AnthropicAI 's 1st Glasswing update surfaces bottlenecks in patch creation & deployment. Read about a systemic maturity approach to vulnerability coordination https://t.co/aNLoFCPNWH https://t.co/Tj4S0PeFX8

AI Shifts Cybersecurity Toward Autonomous Defense, Not Alerts
AI is moving cybersecurity from detection to autonomous defense. If OpenAI and Anthropic can identify, fix and prevent vulnerabilities directly, many classic cybersecurity tools will face pressure. The survivors will be those that own trust, workflows and real-world security outcomes, not just...