Zero‑Day Threats Exist—Update Windows to Stay Safe
“Zero day exploit” sounds like a bad Hollywood techno-thriller, but it’s a very real security risk for Windows PCs. Here’s what it means, why software updates matter so much, and the easiest ways to stay safer online: https://t.co/fXA8h2VcJV #CyberSecurity #Windows #TechTips https://t.co/oae6c8Vnrf

Exploits Arrive Before Disclosure: Assume Exposure, Accelerate Detection
“Mean time to exploit” is now effectively negative. Attackers are exploiting vulnerabilities before disclosure. Modern defense means assuming exposure, investing in detection and response, and using AI to reduce dwell time faster. https://t.co/3pHSy0XEWm https://t.co/Cma1mjX3V1

Europol and Eurojust Shut Down First VPN Network
A joint operation led by Europol and Eurojust has dismantled 'First VPN,' taking 33 servers offline and seizing key domain names. https://t.co/K4asmKk77x

Collaboration and AI Needed to Bridge Cyber Inequity
Cyberattacks are increasingly targeting sectors with limited resources. Closing the growing cyber inequity gap will require collaboration, shared intelligence, and AI-enabled defense at scale. https://t.co/qcDAxmBp1E

Image Metadata Exploit Lets Attackers Hack Macs
We're covering CVE-2026-3102 in ExifTool, discovered by GReAT experts: how malicious... metadata (!) in image files can lead to Mac hacking. Learn more: https://t.co/2xP7Uzpwge https://t.co/btXdA79C49
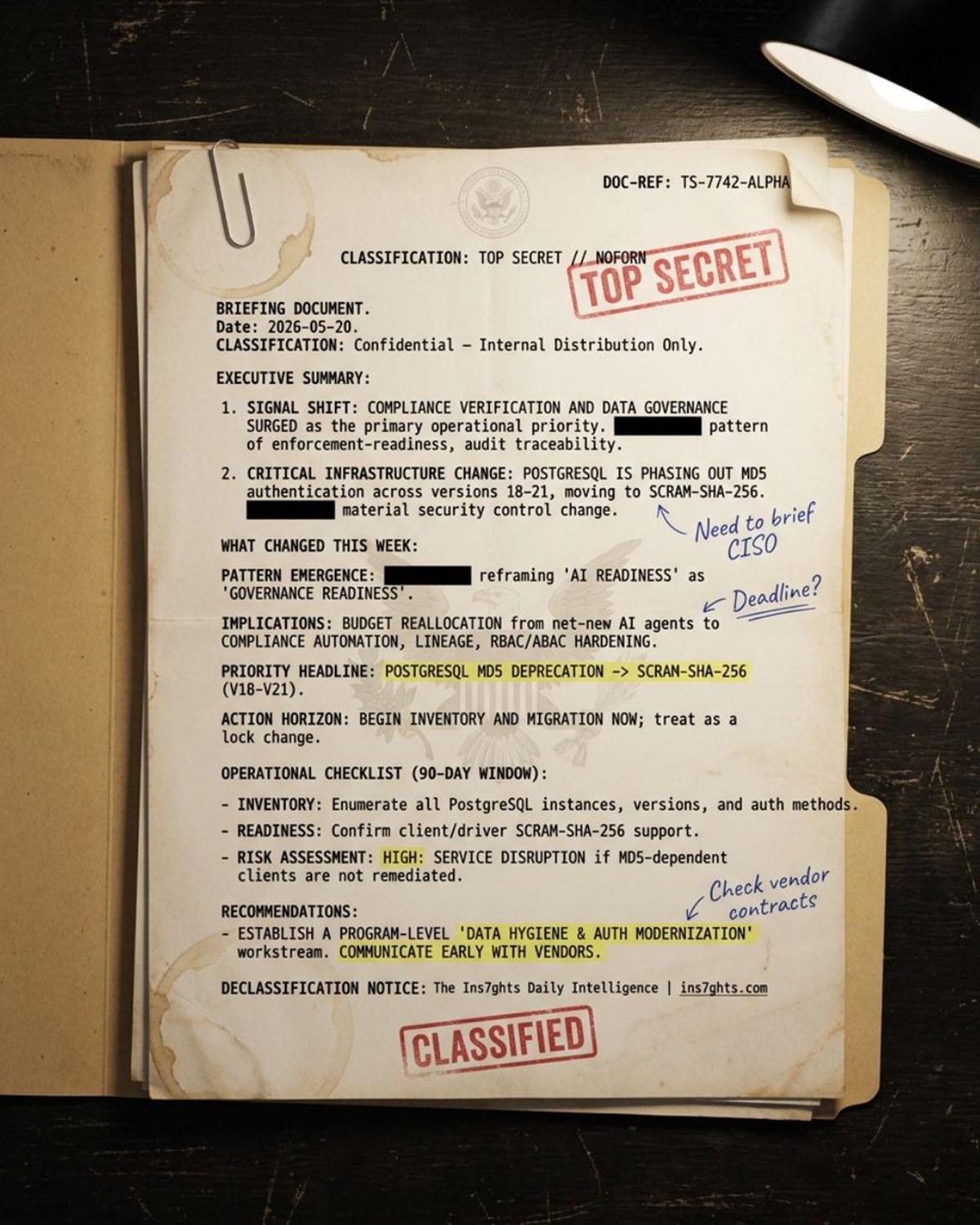
Database Security Now the Foundation of AI
PostgreSQL dropping MD5 auth. MongoBleed leaking server memory. SQL Server exposing vendor code on three clouds. Data governance broke out. Not because CDOs pushed. Because the attack surface got undeniable. The boring database work is now the load-bearing wall of your AI......

CIOs Must Act on Post‑quantum Cryptography Today.
CIOs must take post quantum cryptography seriously today or risk future peril. #CIO #CISO #Quantum #Cybersecurity https://t.co/vZgTOh99DD

AI Faces External and Internal Security Threats, Unprepared
AI Security Threats Coming From Outside And Inside, And Few Are Ready (My latest in @forbes) https://t.co/DzD1PKLGdd

Patch Fatigue Drives Surge in Vulnerability Exploitation
Verizon DBIR 2026: Vulnerability Exploitation Takes the Lead, and Patch Fatigue Is the Reason https://t.co/VqEwEEH8Qb
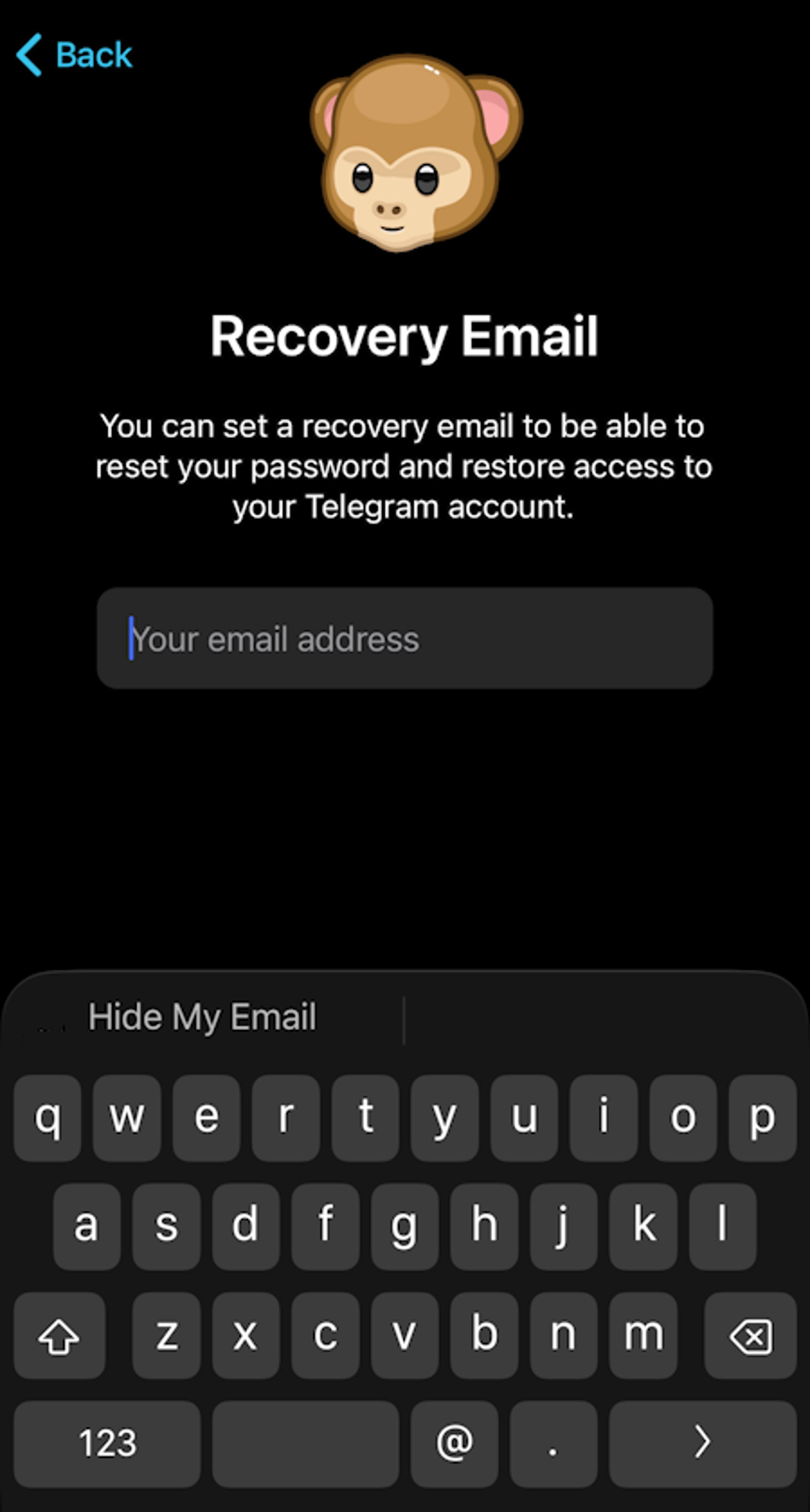
Secure Telegram: Update Weak Default Settings Now
Whether you're an old hand or just jumping into Telegram, it's important to set up your privacy and security settings, because the defaults just ain't that good. Here's what to update: https://t.co/hFFAXUo8ox #telegram #privacy #security @telegram https://t.co/tduEu7WOa2

Google Phone Adds Instant Hang‑up Button to Block Spoofed Calls
Someone pretending to be your contact during calls? Google Phone could soon fight back. Users will be provided with a direct, prominent option to "Hang up" the call immediately from the alert screen ✅ Details - https://t.co/LXBGAuI68K https://t.co/Wv91QDRa87

Federal Agencies Must Begin Post‑Quantum Crypto Transition Now
Transitioning to Post-Quantum Cryptography: What Federal Agencies Must Do Now - Intelligence Community News https://t.co/LAVSLjjCUB

Ransomware Attacks Dip, but Post‑quantum Threats Rise
Ransomware analytics and forecasts for 2026: the number of attacks is declining, but the risk remains high. We’re seeing new families based on post-quantum cryptography, a focus on RDWeb for initial access, and an increase in attacks involving data theft...

Hidden Audio Can Hijack AI Without User Awareness
New research reveals how nearly imperceptible audio in videos, calls, or music can trigger unauthorized AI actions without users noticing. https://spectrum.ieee.org/voice-ai-audio-attacks?share_id=9501042

Diversify Custody: Combine Cold Wallets, Exchanges, Anchorage
A hack at Anchorage cannot send your assets anywhere except your whitelisted cold wallet. Multi-sig process, 24 hour release SLA, and a verification call before anything moves. You are never a creditor of Anchorage. Assets sit in an FBO account...

Data Breaches Spawn Hidden Crimes, Even without Public Leaks
Data breaches have a long tail of secondary crimes… even when no data is released publicly

Five-Year Project Shattered in Five Days; Apple Scrambles
A product that took five years to build was broken into in five days, thanks to Mythos - and now Apple is working on a fix. https://t.co/ELqIjdHOVA

Never Feed AI Your Financial Documents or Bank Links
Just worked w/ @CNN on a piece about why I wouldn't upload full financial docs (tax docs, statements, etc) to AI tools due to leakage & hacking risk. I don't recommend connecting bank accounts to AI tools. It becomes a 1...

AI-Driven SBOMs Enforce Data Protection Obligations Post‑GDPR
'Where are companies' binding obligations to guard our data, our livelihoods, from misuse?' GDPR made that question expensive to ignore. AI is raising the stakes again. Cyber agencies already named it: AI-component SBOMs are the new supply-chain floor.

Incognito Doesn't Hide You From ISP Tracking
Going "Incognito" won't stop your internet provider from tracking, throttling, and selling your browsing history. Here is exactly how they see what you do online, and the best ways to shut them out. https://t.co/AoRYElRgkw

Never Trust Nondeterministic AI Responses as Deterministic
LLMRisks Archive - OWASP Gen AI Security Project ~ just saw this. My number one would have been: Treating non-deterministic AI responses as deterministic and trusting them. https://t.co/psehlnxxXq

Google Thwarts Massive Exploit by Securing Gemini APIs
On Google having disrupted a planned mass exploit: "In the last year, Google, Android, Chrome, etc., built Gemini in everywhere. "They found someone calling those APIs to say, 'Go find the attack surface and do exfiltration on the fly.'" 😱 --...

Chinese Laws Push BambuStudio to Breach Open‑Source License
BambuStudio has been violating PrusaSlicer AGPL license since their fork, with the same networking binary black box in question today. Why are they willing to burn the goodwill over it? There's something most have sensed but never seen it all in...

FBI Remotely Resets Compromised Routers, Evicts GRU
The FBI used court-authorization to remotely reset thousands of compromised home and small office routers, kicking the GRU out of sensitive networks. https://t.co/ap71RUhBGH

Mini Shai-Hulud Threat Targets Emerging AI Coding Workflows
the Mini Shai-Hulud attack is scary because it attacks new AI coding workflows like CI, editor hooks, agent configs, etc
AI Accelerates Cyberattacks, Demands Stronger Defenses
For our free newsletter this week, we discuss how AI-powered cyberattacks are a growing risk. And this morning a ton of hacks are being disclosed, as @emollick points out here. @IrenaCronin and I write this newsletter every week. AI-powered cyberattacks are a...

AI Supercharges Infrastructure Software and Cybersecurity Markets
AI isn’t disrupting infrastructure software and cybersecurity - it’s supercharging them. Here’s why:• • Inference and agentic AI are exploding data volumes and complexity. That demands next-gen infrastructure software: smarter databases, orchestration, observability, IaC and data pipelines. Hyperscalers are dropping ~$700...

Companies Face Lawsuits for Allegedly Addicting Users
Oh, FFS. These dolts will next sue Star Wars for addicting users. How about Dickens, folks? Not to mention Frito-Lay? Netflix sued by Texas for allegedly spying on children, addicting users https://t.co/qMiVieTu6o
Free Open‑Source Browser Beats $500 Anti‑Detect Solutions
I'm done paying $500 a month for anti-detect browsers after finding this. It's called CloakBrowser. A stealth Chromium that scores 0.9 on reCAPTCHA v3 (same as a real human) and passes 14 out of 14 bot detection tests. - Auto-resolves Cloudflare Turnstile -...

Binance AI Stops $10.5B Losses, Blocks 36K Threats
JUST IN: Binance's AI-powered security systems prevented $10.53B in user losses and blocked 36,000 malicious addresses since 2025.
Threats Hide in Plain Sight; Intelligence Beats Detection
As threats hide in plain sight, enterprises need intelligence and investigation, not just detection. https://t.co/KKOgpAAq5H

Hyperscalers May Lose Public‑Sector Data Contracts
US (and other global) hyperscalers could be pushed out of the running for contracts relating to sensitive public sector data. https://t.co/bzn1vgHBGg

AI Powers Real‑World Zero‑Day Cyberattacks, Accelerating Threats
AI-assisted cyberattacks are no longer theoretical. Google says hackers used AI to discover an unknown software vulnerability, a glimpse of how offensive cyber capabilities may rapidly evolve. This is likely just the beginning. AI is accelerating not only innovation, but also the...

Critical Xrdp Buffer Overflow Fixed in Latest Release
Our experts have discovered vulnerability CVE-2025-68670 in xrdp, a remote desktop server for Linux using the RDP protocol. A buffer overflow could lead to remote code execution without authentication. The issue has already been fixed in the latest versions. Details:...
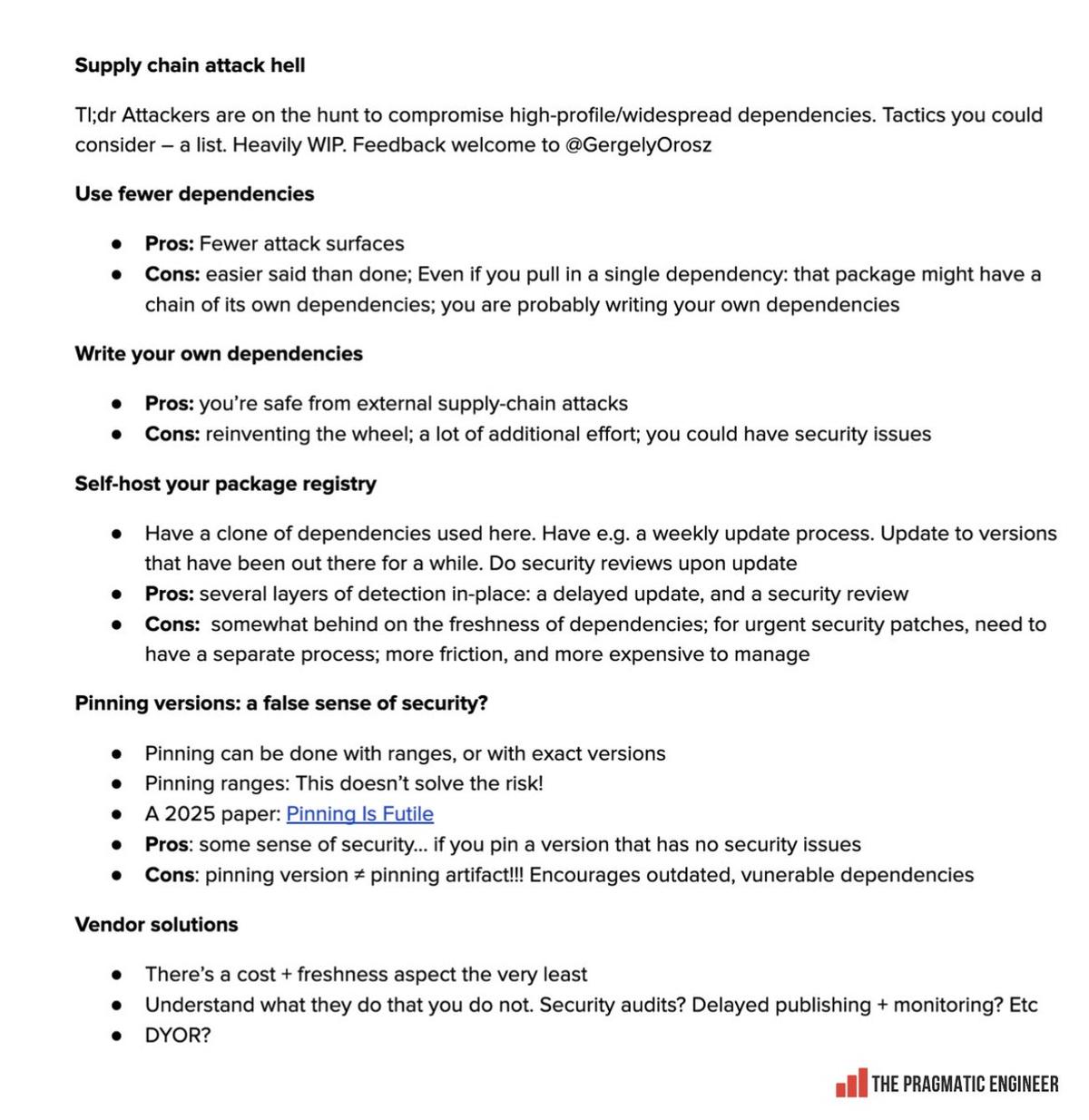
Supply Chain Attacks Surge; Explore Mitigation Strategies and Vendors
Supply chain attacks are happening left and right with npm, PyPI and so many other places. It seems to be getting worse, everyone agrees. But what can you do about it? Some thoughts on possible approaches (all have tradeoffs). What did I...
Mythos Finds Just One Real Curl Vulnerability Amid False Positives
The developer of curl tried using Anthropic’s Mythos to find security vulnerabilities. While it flagged 5 issues, 3 were false positives and 1 just a regular bug. So it only found 1 real security issue. That said curl already uses multiple...

DWP Won’t DM You—Ignore Telegram/WhatsApp Scams
If someone messages you claiming to be from DWP on Telegram or WhatsApp, it is a scam. Direct outreach on social media does not happen. Team members respond to messages but there is no personal outreach. If you are unsure,...

GeForce NOW Breach Affects Single Country, No Passwords Taken
The breach is limited to GeForce NOW users in just one country, and no passwords were stolen. https://t.co/6CZUppgiu8

OpenAI Launches Daybreak to Accelerate Continuous Cyber Defense
OpenAI is launching Daybreak, our effort to accelerate cyber defense and continuously secure software. AI is already good and about to get super good at cybersecurity; we'd like to start working with as many companies as possible now to help them...
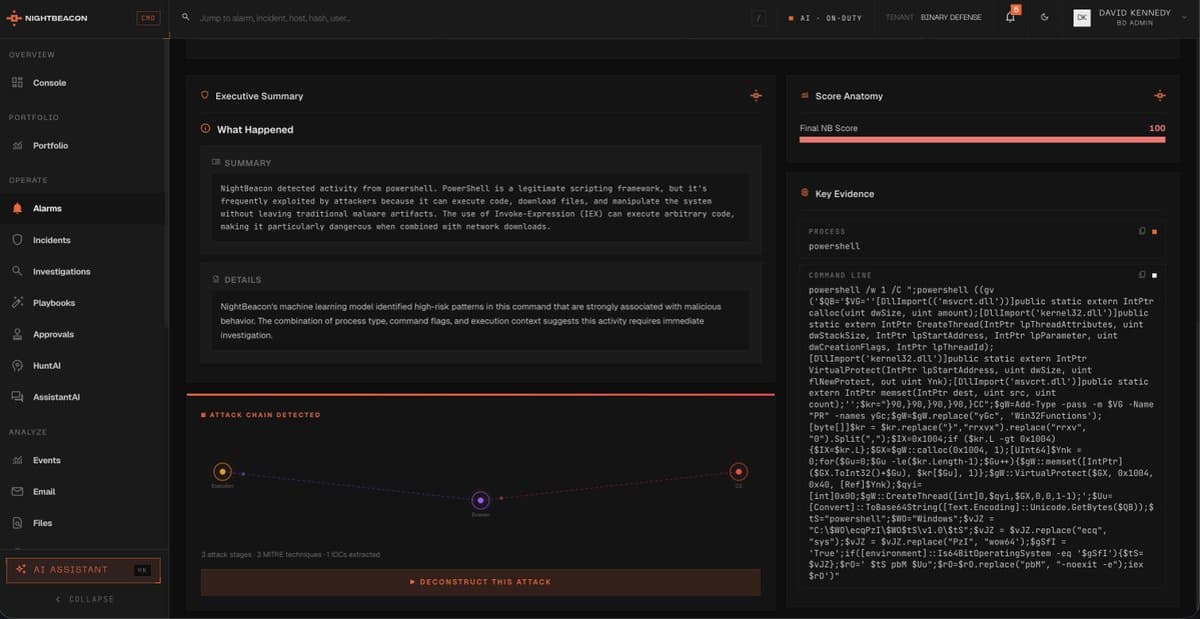
NightBeacon Slashes Detection to Seconds, Cuts False Positives 87%
NightBeacon is changing the game for us @Binary_Defense - we have this technology so dialed into every aspect of what we do. Our MTTD and MTTR has drastically been reduces to seconds and minutes, not multiple minutes or hours....

AI-Generated Scam Calls Now Mimic Real Voices
Scary indeed. AI-powered scam calls are getting more convincing—and more common: 'It was her voice, I know her scared cry' https://t.co/lV7jJx5BFm #CIO #AI

Unified Tech, Law, and Innovation Needed to Stop Live Piracy
Looking for an informed discussion navigating the intersection of 🔒 security technology stack, 🧑⚖️ legal frameworks and enforcement, as well as 📲 product innovation, here we go: In „Streaming Security at Scale: Protecting Live Sports Broadcasts,“ we are covering why an...

AI Could Expose Every Open‑source Vulnerability, Ending Its Safety
We've had Linus's Law for decades: "Given enough eyeballs, all bugs are shallow." #catb After last week's Canvas breach, perhaps we need Linus's Corollary: Given powerful enough AI, all bugs will be found and exploited. Will AI's superhuman ability to find...

Beware Spam: Don't Click Fake Alert Links
FOLLOWERS.......I have some spam dirt bags out there trying to trick you. Do NOT click on any links that say I am sending out alerts or a strategy.
LLM Agents Link Anonymized Data to Individuals at Scale
While gathering that data has become easier in the smartphone era, making use of it at scale has remained difficult. But researchers are beginning to show that LLM agents can connect anonymized data to real people quickly, cheaply, and at...

1 Billion IDs Exposed: America’s Data Security Crisis
Every day, in every way, it gets worse. Surely there’s no one left in America whose personal information isn’t already in the hands of crooks.. IDMerit exposes 1 billion identity records in unprotected database | Fox News

Canvas Hack Exposes Risks of Centralized EdTech Data
'The Biggest Student Data Privacy Disaster in History': Canvas Hack Shows the Danger of Centralized EdTech https://t.co/uYhtnaIe2g
Purple Teams Are Just Red and Blue Co‑Located
Your Purple Team Isn't Purple — It's Just Red and Blue in the Same Room https://t.co/SgiQ1iLO6J https://t.co/n2GviJHqgA

Curl Audit Finds Single Low‑severity CVE, Others False Positives
Mythos on Curl: Once my curl security team fellows and I had poked on the this short list for a number of hours and dug into the details, we had trimmed the list down and were left with one confirmed...

HIBP Adds Costa Rica as 42nd Government Partner
HIBP’s free gov program keeps growing, helping governments get ahead of data breaches before attackers do. Today, we welcome our 42nd government: Costa Rica, protecting departments, public resources and the people behind them. https://t.co/GD14TAF6sU