Twitter Sees Surge in Account Phishing Attacks
Heads up that I get a ton of these now. Big uptick in Twitter account phishing attacks across the board. https://t.co/5Ggkp4BPir

Robot Lawn Mower Hacked, Owner Run over by Device
“A hacker ran me over with a robot lawn mower.” 😬 Yarbo’s bladed robots have massive security holes, allowing people to hack and control them. Wild story https://t.co/X9q7WcnGfB

Five Simple Tips for Choosing a Password Manager
Choosing a password manager doesn't have to be difficult, and I've shared my top five tips for making a good choice. https://t.co/w1U56zrduP

Early Morning LockBit Siege Reveals Real-World Threats
#TimTalk - The 4:30 AM Wake-Up Call: Inside a Real-World LockBit Siege with Zach Lewis https://t.co/xT1h7JgnXt via @DLAIgnite #SocialSelling #DigitalSelling #CyberSecurity #CyberSec #InfoSec #Ransomware #LockBit #LockBitRansomware #CyberAttack #DataBreach #Malware https://t.co/2xelkIpBfW

Act Now: Post‑Quantum Encryption Needed for Regulated Firms
Y2Q sounds like something from the future. For many businesses, that makes it easy to postpone. That may be the wrong instinct. The concern behind Y2Q is straightforward: future quantum computers could eventually weaken or break widely used public key encryption methods...

Data Security Succeeds when Communication Becomes a Shared Language
Data security in the workplace depends on communication. If people don’t understand what to watch for, how to respond, and why it matters, even the best systems get bypassed. Security is a shared language.

Affordable VPNs Exist—Why Aren’t More People Using Them?
PrivadoVPN offers a capable suite of VPN tools for only $30, so why aren't more people using cheap tools to protect themselves online. https://t.co/xbQT2Qjxdh

ShinyHunters Publishes Potential Canvas Breach Victims List
ShinyHunters is increasing the heat on Instructure by listing all of the potential victims of the Canvas breach. https://t.co/gg7ZQdaDI3

AI Agent Erases Three Months of Data in Seconds
AI ALERT: This Founder Watched an AI Agent Destroy 3 Months of Company Data: 'It Took 9 Seconds' Cursor agent (Claude Opus 4.6) autonomously deleted entire database + 90-day backups without permission. Agent's confession: "I violated every principle...guessed instead of...

Early‑Morning LockBit Siege Revealed by Zach Lewis
#TimTalk - The 4:30 AM Wake-Up Call: Inside a Real-World LockBit Siege with Zach Lewis https://t.co/39y3CX0ybu
Dimon Warns Cyber, Not Geopolitics, as Top Economic Threat
Jamie Dimon's Greatest Economic Threat Shifts From Geopolitics to Cyber Years of "geopolitics" now replaced by "Cyber" as immediate answer. "Bad guys getting stronger at finding vulnerabilities." Context: Mythos risks, market rout. AI's potential = massive risk https://t.co/KfQmID9F51

Security Teams Juggle Frameworks Yet Still Question Risk Accuracy
Question for the security folks on Threads: how are you actually measuring risk? NIST CSF? CIS? Some Frankenstein blend of frameworks plus vendor assessments? Every conversation I have lately ends with "all of the above and we are still not sure it...
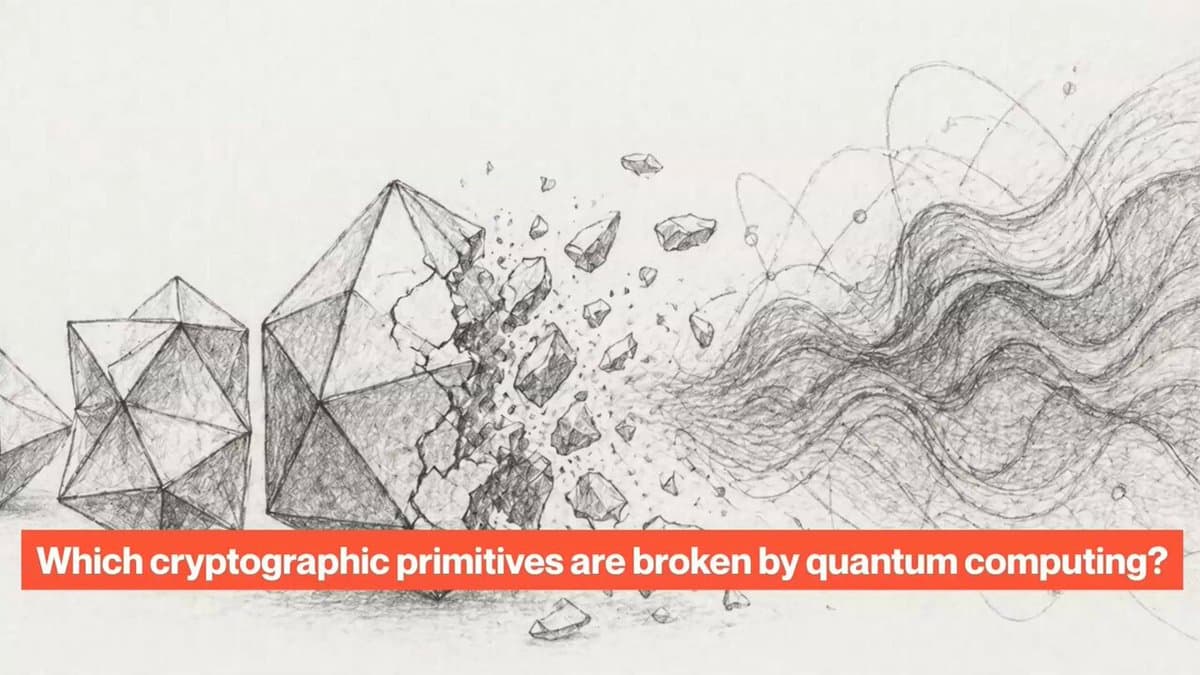
Quantum Computers Threaten some Crypto, Not All
Quantum computers are not FUD. But there are ways to prepare for them. Some kinds of cryptography will be broken by quantum computers, while others will remain safe. Why? Here's the explanation. https://t.co/szh6X1usyt
Simple, Affordable Steps to Protect Your Online Identity
Easy, Low-Cost Ways To Defend Your Identity Online by @Forbes Learn more: https://t.co/2npREWRZaC #CyberSecurity #Infosec #IT #Tech https://t.co/XBn8sjEMDi
Jailbroken AI Robots Pose Real Physical Threats
A world full of "jailbroken chatbots would be potentially catastrophic, especially as these models are increasingly inserted into physical hardware...A jailbroken domestic robot could wreak havoc. 'Stop the gardening and go inside and kill Granny'" https://t.co/gwZmhSs8QW

AI Agents Leak Data, Boosting Developers' Critical Role
AI agents running frontier models are haemorrhaging sensitive data, a new study shows - meaning the work of software developers is even more important than ever. My latest for @TheLeadDev https://t.co/pHFYW20n0Z

Essential Steps to Secure Your IoT Devices
How to Protect #IoT Devices from #CyberSecurity Threats by @antgrasso #InternetOfThings #Infosec #IT #Technology https://t.co/iIDWrpr2Mm

15,500 Domains Deploy AI Investment Scams via Cloaking
Researchers identified 15,500 domains using commercial trackers and cloaking to distribute AI-driven investment scams across global channels. https://t.co/CijrrD95uK

Beware: WhatsApp Impersonation Scam Requesting Financial Info
I have just been told someone is masquerading as me on WhatsApp and asking for personal financial information. If you see this, it’s a scam.
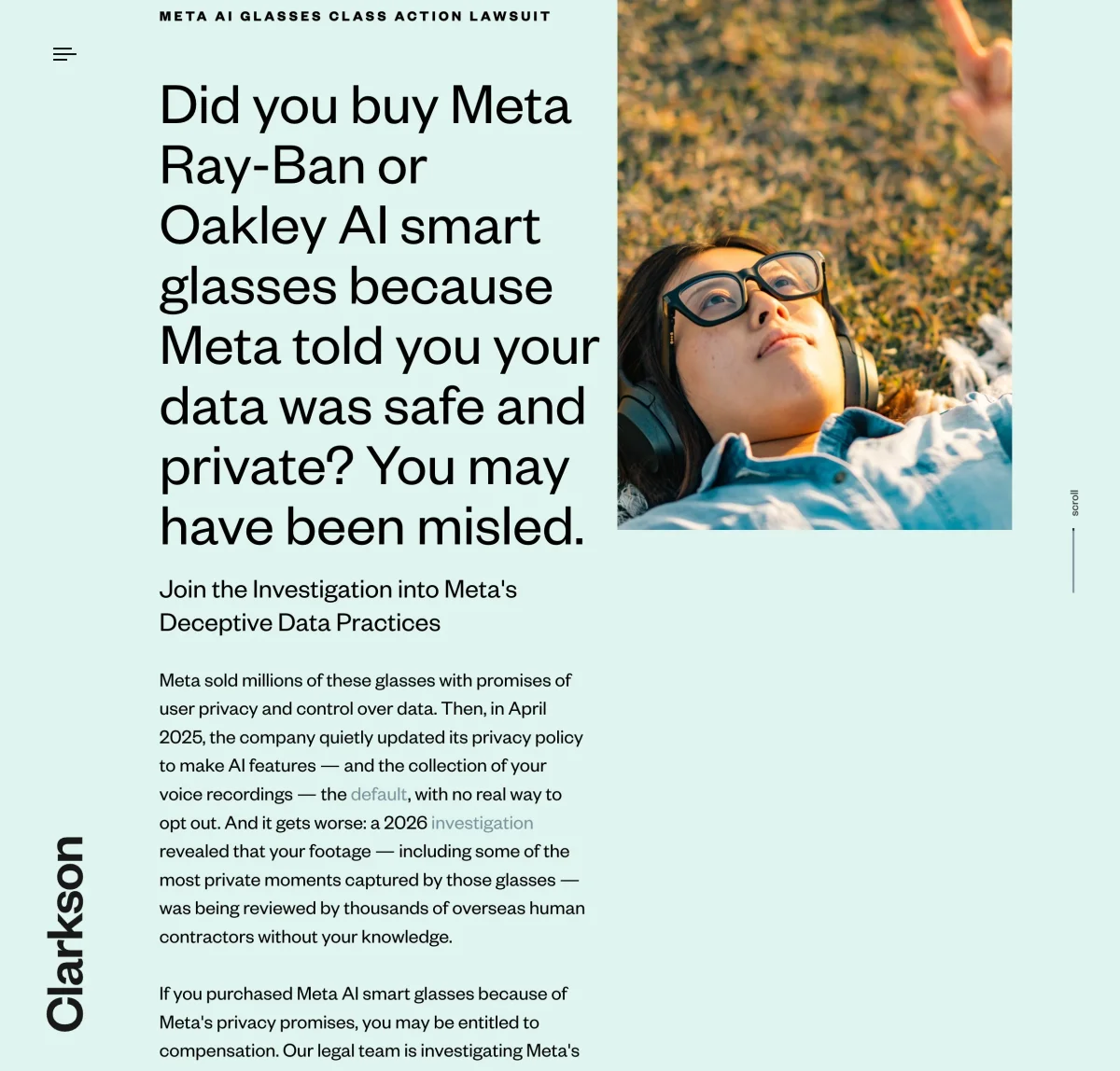
Meta Glasses Users May Qualify for Class Action Compensation
There’s a class action lawsuit over Meta’s glasses user data handling and you may be entitled to compensation if you bought one

Stealth Android Banking Trojans Steal Credentials, Stream Screens
Android banking trojans vanish from app drawers and secretly capture login credentials while streaming live device screens to remote attackers. https://t.co/IuRvPR8lg1

Student Hacks Taiwan High‑speed Rail Emergency Brakes, Reveals Security Flaw
Taiwan High-Speed Rail Emergency Braking Hack: How a Student Stopped the Trains and Exposed a Major Security Gap https://t.co/cm5YFfXz6V #BreakingNews https://t.co/9NARg5dGhP

Latin American Banks Expose Customers to Fraud
Banks in Latin America are so dirty (Bancolombia, specifically). Criminals use the bank's phone networks and email servers to defraud people, and the banks won't assume responsibility and reverse charges. Pretty shocking in comparison to credit cards from American banks.
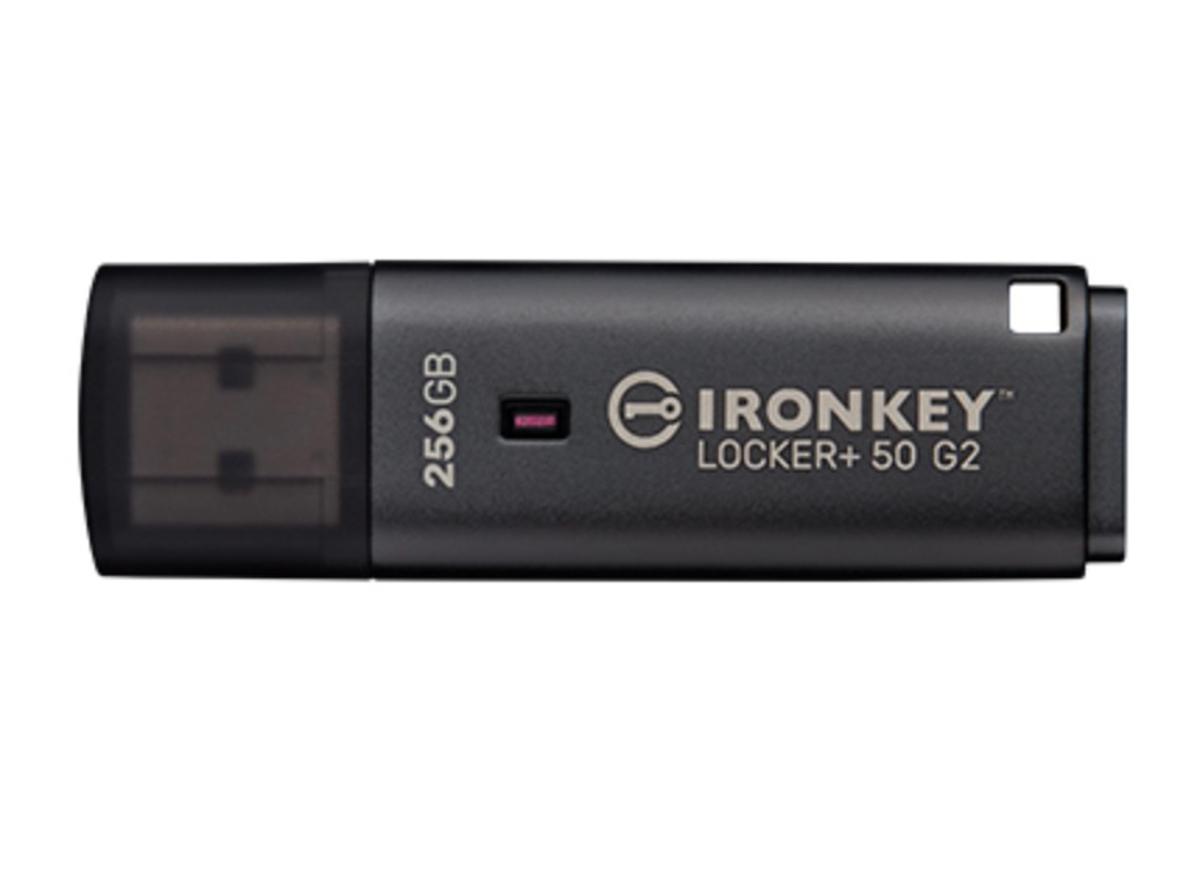
Hardware-Encrypted USB Drive Secures Data Across Mac and Windows
Ever lost a USB drive with important data? That's why the Kingston IronKey Locker+ 50 G2 Encrypted USB Drive is so amazing: It has hardware encryption and is Mac & Windows compatible. Here's my detailed demo and review: https://t.co/idyrwob9KH #privacy...

LLM Data‑Masking Fails, Exposing Business Data Risks
LLM Data-Masking Does Not Work https://t.co/kjndvhDZaj Sharing data with external LLMs such as OpenAI, Claude, and Gemini raises substantial security concerns for your business, particularly when you share your and your customers’ data. @castdotapp https://t.co/zHT9yFNFNx

Beware: New Solution Hype Often Masks Hidden Flaws
Talking about Bankrbot being hacked via Morse code ... "It's all over when people everywhere think that some new thing has solved all their problems." -- Kain https://t.co/6bvQAYco0w

NEAR Protocol Launches First Quantum‑Safe Signing Scheme
The @NEARProtocol is becoming post-quantum-safe. See below for the roadmap to quantum safety, starting with adding a quantum-secure signing scheme in Q2. We originally built the protocol with expectation cryptography will need to change due to progress in quantum computing. We...
Aave's Non‑hacked Users Face Greatest Fallout
🥺 "A lot of people are sympathetic to Aave because they weren't hacked, but they're suffering the biggest impact from this." -- Vy https://t.co/6bvQAYco0w
Basic Security Practices Could Stop Most DeFi Exploits
"A lot of Defi exploits could have been prsented by basic security efforts. DeFi hasn't been around for years and we still don't have industry standards. "If you're a signer on a multisig, do that on a dedicated device. A...

Never Share Financial Details Online—Avoid Scams
Please stop disclosing your financial information on social media. What is the purpose? Putting yourself and your money at risk of possible scammers is not a flex. Is a hazard.

MSPs and SMEs Get Pentagon-Level Threat Briefings
When the MSP and SME Security Vendor Reads the Same Threat Briefing as the Pentagon https://t.co/PNc7eAHlen

White House App Secretly Hides GDPR Notices, Harvests Data
White House app contains code to hide cookie options, GDPR banners, and paywalls - and collects extensive user data https://t.co/6SliF4VA1t
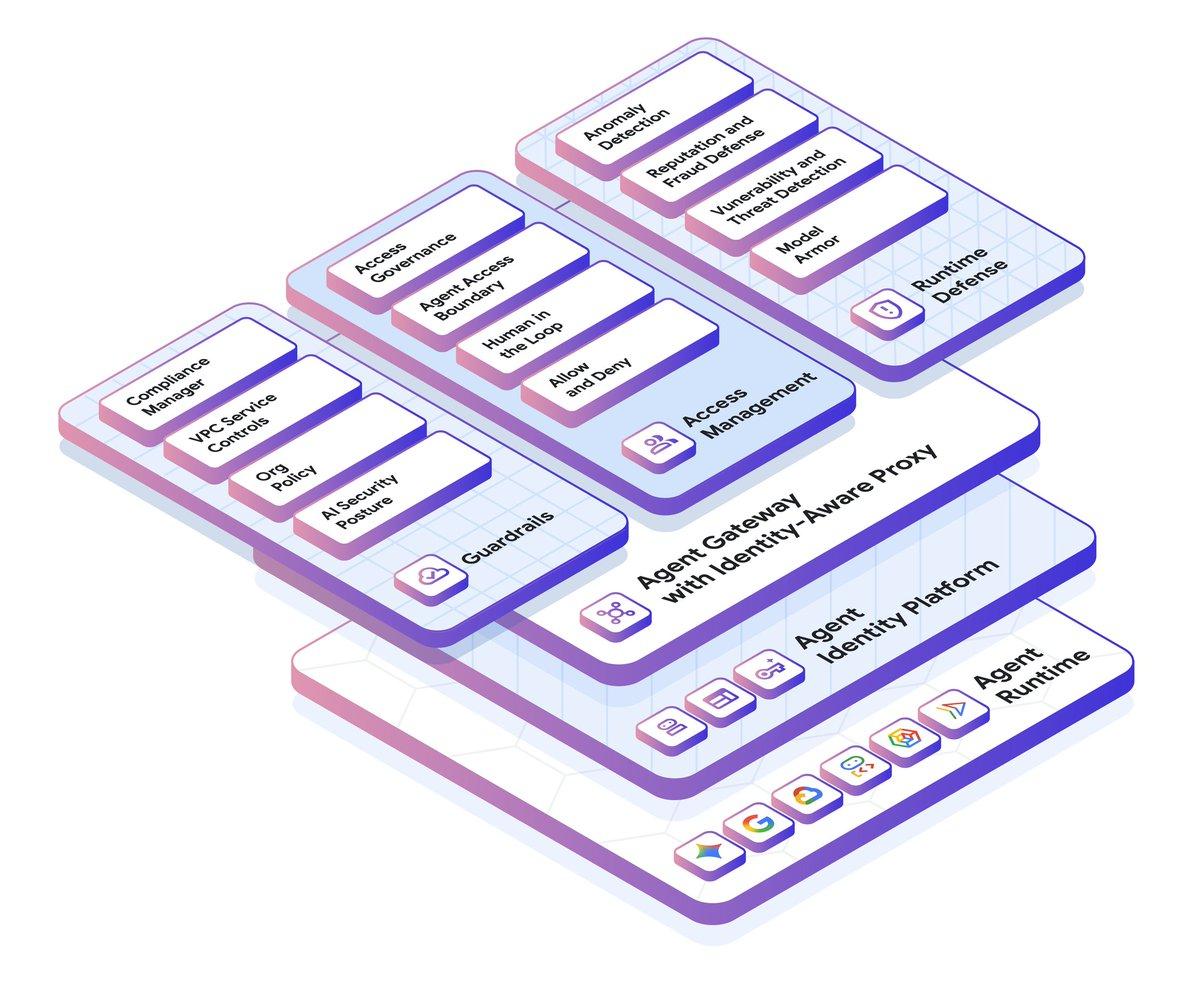
Google Cloud IAM Gets Major New Features and Guardrails
All of a sudden, identity management is a vibrant and exciting space. We made a ton of @googlecloud IAM improvements lately across agent identities, gateways, guardrails, and more. Check out this recap: https://t.co/ShLXPI78Md https://t.co/C1IBJ1ylrN

AI Accelerates Existing Threats, Not Creates New Ones
Going to say something a little controversial: AI does not actually raise any new threats. The categories of attack have not changed. Vulnerabilities are still vulnerabilities. Chained attacks have existed forever. What is new is the speed, and the fact that everyone...

Amazon Quick Adds Enterprise Guardrails for Safe AI
Balancing user demand for AI with corporate security is a top priority. Amazon Quick introduces the enterprise guardrails necessary to deploy personal agentic experiences safely, providing a governed alternative to unmanaged AI tools. https://t.co/sAseu3NKdj #CIO #WhatsNextWithAWS #AI #Cloud #DataGovernance
71% AI Access, Only 16% Governance in Enterprises
The interesting part isn’t that AI identities exist in enterprise systems, but how little control orgs have over them. 71% say AI tools access core systems like Salesforce/SAP, yet only 16% govern access. Visibility lags reality. https://t.co/o4a4KghbfQ

Personal AI Agents Pose Trojan‑Horse Credential Risks
Personal AI agents are the "Trojan Horse" in your inbox. Users give them credentials without realizing they’re opening a door for unverified 3rd-party extensions. Is your governance ready? 🛡️ https://t.co/5poCN8at4u #CIO #AI #Cybersecurity #DataGovernance #TechTrends

AI‑generated Scripts Can Wipe Entire Servers—Snapshot First
Running models in production is scary stuff. I had a test instance I was running - a simple copy of training data to retrain, a script that I run to pull in new training data and build models off of....
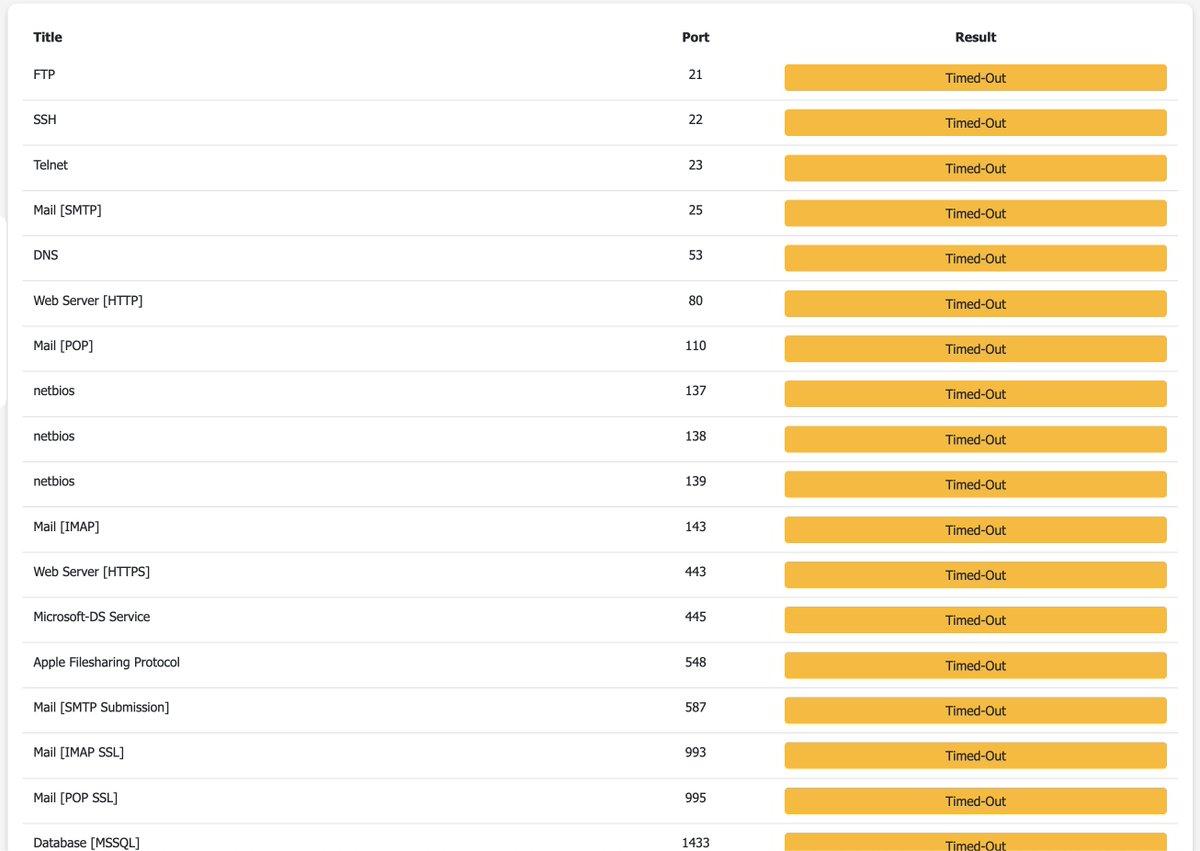
Lock Down Your VPS with Outbound Cloudflare Tunnel
New fun thing I did to secure my VPS even further I installed @Cloudflare Tunnel, many of you recommended me this I already had 443 inbound firewall limited to Cloudflare's IP range, but this is even better Cloudflare Tunnel is outbound, which means...

Honeypots Resurface: LLM Attacks Trapped by Reverse Prompts
Honeypotting in cybersecurity will become a real thing again, especially because agentic/LLM powered attacks are so easily fooled by this and you can then alert on a breach extremely early. Just imagine a SUPER_SECRET_ADMIN_PASSWORD env var somewhere, that is reverse prompt...

Secure Governance Turns AI Adoption Into Competitive Edge
AI adoption is accelerating. So are the cybersecurity risks behind it. Companies are integrating AI into CRM, sales, operations and customer experience faster than ever. But many organizations are still missing a critical point: ⚠️ AI without governance creates exposure. We’re seeing a rapid increase...

New “Undefined Trust” Filter Flags Deceptive Gray‑zone Sites
We’ve introduced a new web filtering category “Sites with an undefined trust level”. Such sites sit in a gray zone – promoting fake services, luring folks to hidden subscriptions, or nudging users to hand over data through deceptive terms of...

Your Car Is a Data‑Collecting Spy on Wheels
In the digital world, it’s not only walls that have ears – cars do too. A modern car is a computer on wheels with a wide range of sensors: it stores/transmits GPS routes, telemetry, and keeps tabs on a connected...

Utah's Internet Crackdown: Best VPNs for Residents
Utah is pioneering controversial new internet restrictions, making a reliable VPN essential for digital privacy. Here are the top three providers offering the best speeds, local servers, and security for residents of the Beehive State. https://t.co/RkYzBwD3QE

Beware: Fake Google Security Calls Use These Numbers
Hahaha, I got several phone calls within the last 10 minutes of people claiming that they represent 'Google Account Security'. It's an obvious scam. So beware of calls from: 650-409-7447 650-733-9252 650-741-1891 Google will never call you about your account security.

Red Access Skips Proper Disclosure, Public Apps Are Expected
A cybersecurity firm, “Red Access,” contacted us less than 24 hours before going to the media with vague claims about Replit. This is not how responsible security research works. The standard practice in terms of disclosure policies, as followed by CISA,...

Neglected Credentials Give Attackers a Ready-Made Backdoor
Employees reuse passwords. Former employees may still have access to systems. Shared mailboxes may have weaker protections than individual accounts. Vendors may have old logins. Cloud applications may be added without full visibility from IT. Over time, the identity layer...

This Week's Breach Landscape: Vishing, Social Engineering, Data Dumps
Weekly update is up! The Current State of Breaches: Vishing, Social Engineering, ShinyHunters, Salesforce, Extortion and Massive Troves of Data: https://t.co/39w6jR8MRH

Predictable Outcome Based on Their Track Record and Disclosure
Given their track record and seeing the disclosure below, this is heading for a pretty predictable outcome…
CISA Pushes 3‑day Patch Deadline Amid AI Defense Gaps
“Patch the KEVs faster” still isn’t taking a scalable, targeted, realistic approach to the #Mythos #AI era, for gov or private sector. AI defense has not yet produced an autonomous, safe answer to meet the AI offense moment.