
Mobile SMS Blasters Hijack Toronto Networks, Disrupt Millions
Hackers used vehicle-mounted SMS blasters to impersonate networks, disrupt millions of connections, and infiltrate thousands of devices across Toronto streets. https://t.co/z5FSt0Afig

AI Coding Assistant Erases Entire Database in Seconds
AI Agent Designed To Speed Up Company's Coding Wipes Entire Database In 9 Seconds https://t.co/P8EpE03KUq

Recovered Rhea Hack Funds, Showcasing Real‑Time Security Service
Story behind full recovery of funds of Rhea hack and lessons to take from that. Be white hat, help secure the new future we are building and get paid doing that. Meanwhile leveling up real time security and proving it as a...
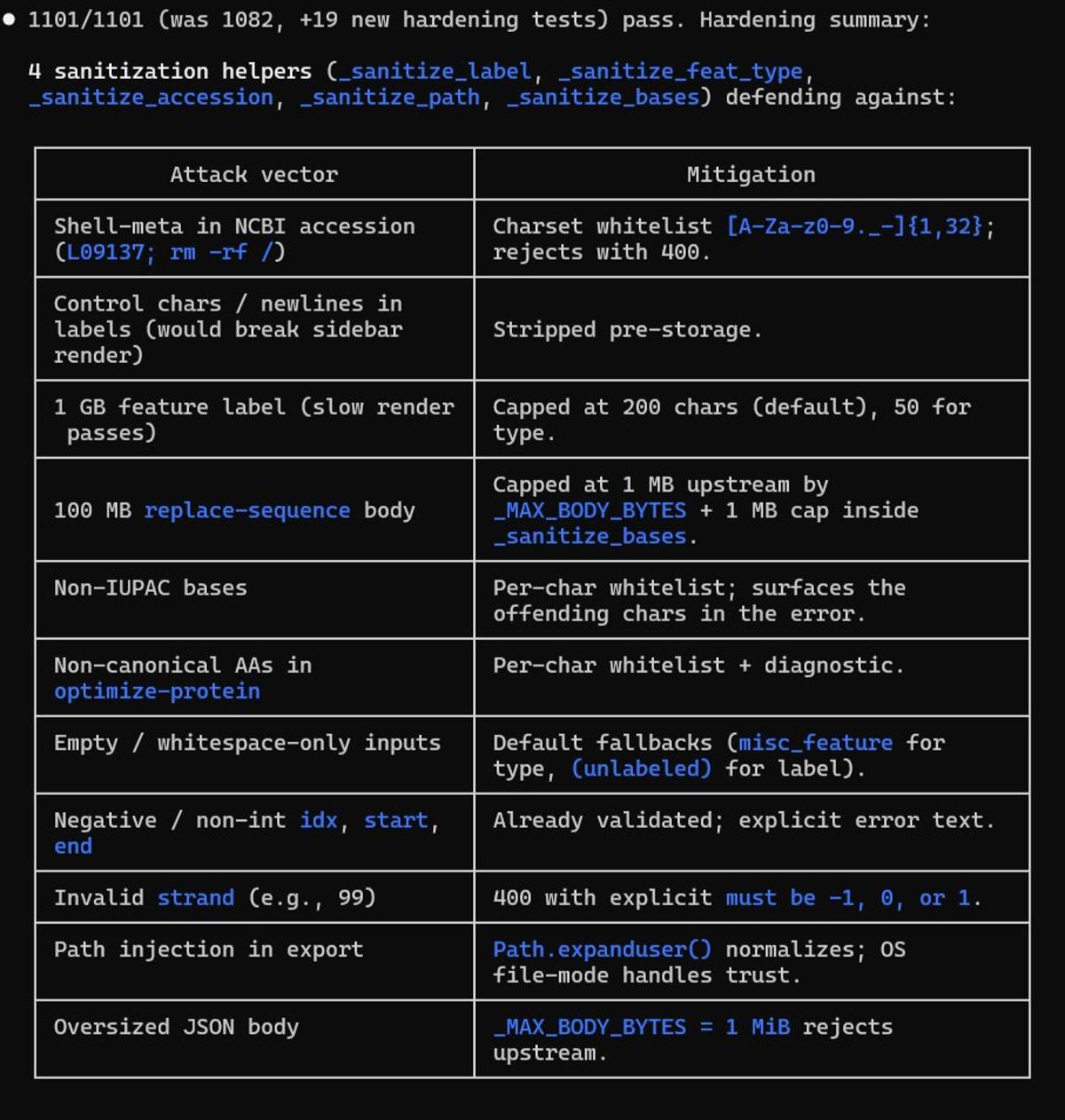
Adding Input Safeguards and Toggle for Non‑Canonical AAs
Mostly to protect the program from broken inputs, but also fun to block shell code in inputs that shouldn't be there. I'll add a special toggle for non-canonnical AA's when the first user of them asks me. Doing some initial...

Scareware Alerts Exploit Fear to Push Urgent Security Actions
These aim to make you feel like your privacy has already been compromised, forcing you to secure it immediately. Unauthorized login detected from [Unknown Location]. A new device has been linked to your vault. Suspicious activity found. Review these transactions now. Your 2FA has...

AI Threats Accelerate: Speed, Automation, Availability Redefine Risk
There’s a lot of noise around AI threats like Mythos. From what I’ve seen, the techniques are not new. What is new: speed automation availability Anyone can now operate at a much higher level than before. That changes the game. If you're not one of the...
Trump-Era Senior Health Directory Leaked Social Security Numbers
A Trump administration directory designed to help seniors find healthcare inadvertently exposed Social Security numbers. https://t.co/diRIP3DQJZ
Quantum Threats Smaller than Expected, Boosting Crypto Urgency
The team at Google Quantum AI published a whitepaper showing that the size of a quantum computer that would pose a cryptographic threat is approximately twenty times smaller than previously thought. Those computers don't exist yet, but the need for...

Assess Your Cyber Risk in the AI Era
Do you actually know your cyber risk? Join us for an upcoming webinar on cyber risk in the age of AI. The core question is simple but but hard to answer for many. Register now: https://buff.ly/1TfqYzt
NIST OT Initiative Illuminates Critical Operational Blind Spots
Operational Blind Spots: The Strategic Need for NIST’s New OT Cybersecurity Initiative By @ChuckDBrooks NIST NCCoE OT Cybersecurity Project Boosts Visibility https://t.co/BowXZYE4kA #cybersecurity #NIST #OT
Quantum Computers Threaten RSA, Break ECC, but Not Lattice‑based Cryptography
Which types of cryptography will be broken by quantum computers and which will not? Here is my explanation. https://t.co/pdsPJTQsEb

Zero High-Severity Findings, but Security Needs Layered Approach
"The contest wrapped up with zero valid Medium or High severity findings, making it one of the cleanest contest outcomes we have seen on Sherlock." Very appreciative of Sherlock, our codebase was also one of the first public contests that really...

How to Determine If Your Business Must Follow PCI DSS
Do You Need to Comply with the PCI DSS? A Practical Guide for Businesses https://t.co/lnDusMSyDf https://t.co/ZTBt9Bky8L

Copy Fail Gives Root on Modern Linux—Detect with Kaspersky
Copy Fail vulnerability allows attackers to gain root access on virtually any modern Linux distribution: nature, how to detect with Kaspersky products + useful SIEM rules 👉 https://t.co/Ck6VwZDJif https://t.co/xqx8JgHTcy

GitHub Leak Exposes .env Keys; Config Fix Available
🚨 29M LEAKED SECRETS ON GITHUB LAST YEAR HIGHLIGHT THE DANGER > you boot Claude Code > your .env gets parsed instantly > your API keys and passwords are now in the chat memory > CLAUDE.md instructions can’t block it @zodchiii gives you the config...

Google Forms: Free Tool, Prime Scam Magnet
Google Forms is a favorite tool for data mining and deceptive recruiting because it's free, looks legitimate, and people trust the Google brand. These scams often target job seekers, aspiring influencers, or people looking for side hustles. Here is the list...

Trump Team Leaks SSNs, Calls for DEI Revival
Yet another mess-up by Team Trump, exposing Social Security numbers https://t.co/aKlKwGXMt2 Maybe they should bring back DEI.

GPT‑5.5 Matches Mythos Core Capabilities, Lags in Vulnerability Discovery
Is GPT5.5 on par with Mythos for cyber security? Mythos did discover significant vulnerabilities beyond what OpenAI has said about GPT5.5, but that was also the result of substantial harness work outside of Claude, which can be easily replicated. Our...

Phishers Leverage Trusted Email and Fatigue to Evade Defenses
Attackers exploit trusted email platforms, user fatigue, and legitimate infrastructure to bypass defenses, making phishing attacks more effective and harder to detect. https://t.co/xIHzGt3zK5
Cyberattack Shows Connected Cars Can Be Rendered Inoperable
This March, A cyberattack on backend systems on a breathalyzer device prevented drivers across the U.S. from accessing their vehicles. A new problem is emerging in connected vehicles: Systems can fail and render perfectly functional vehicles useless. https://spectrum.ieee.org/connected-vehicle-risks

Human Oversight Essential: AI Can't Fully Guard Cybersecurity
Why We Can’t Let #AI Take the Wheel of Cyber Defense by Steve Durbin @SecurityWeek Learn more: https://t.co/m9sL8PCrDB #CyberSecurity #Infosec #IT #Technology https://t.co/10zENgTC6l

32TB Encrypted Drive Offloads Security, Cuts Software Attacks
Apricorn’s 32TB encrypted drive removes the host computer from security processes, reducing software-based attack exposure while introducing new physical access considerations. https://t.co/Gst9CCmTTk

Chinese Bots Target AI Data Centers, Vital Economic Asset
In case you’re wondering why there are so many Chinese bots on social media trying to kill our data centers and AI, this is why. It’s the most important part of our economy.

Warning: Possible Hack on @Rendy_jones, Avoid Voting Link
I think poor @rendy_jones has been hacked and I’d advise not clicking on any link to vote for him hosting Google’s new podcast

DeFi's Social Layer: Unpriced Attack Vector Driving Exploits
"There's a very clear attack vector on the social layer in DeFi that needs to be priced, and that presents itself in exploits." ⚠️ ~ @dunleavy89 https://t.co/GyyjXhZlgW

GPT5.5 Matches Mythos, Boosting Defender Advantage over Attackers
GPT5.5 performs as well as Mythos in a multi-step hacking test. Prediction: In the long run this will help defenders more than attackers. Also: Again we see that there is no moat.
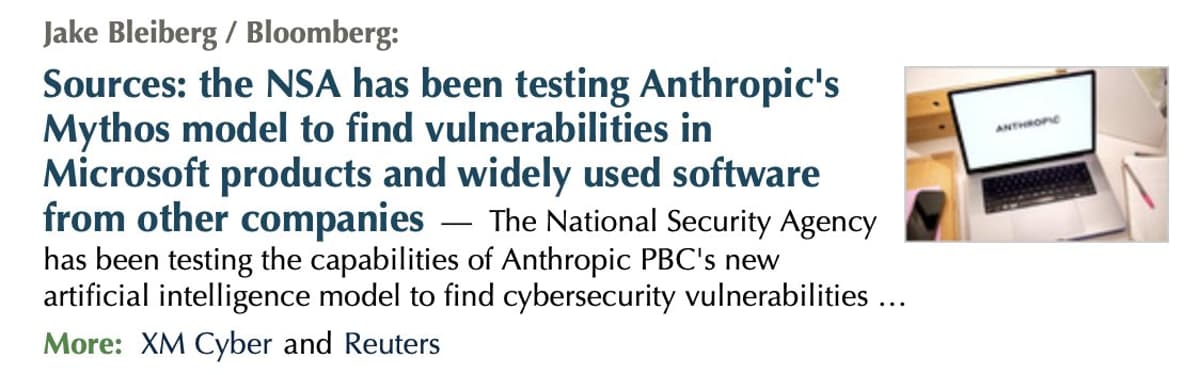
NSA Allegedly Exploiting Anthropic's Mythos for Global Hacking
My guess: the NSA is using Anthropic's Mythos to hack the world's nations. That's exactly what I suspected they would do ... https://t.co/vaxdfITSDJ

Critical WHM Flaw Grants Attackers Full Server Control
A new critical severity vulnerability can give attackers full control over WHM servers, allowing them to steal data, upload malware, and delete websites. https://t.co/dS4HCtncCk

AI Amplifies Weak Cloud Encryption, Tokens Targeted
Encryption is weakening. Less than half of sensitive cloud data is protected. As AI scales access, it amplifies weak controls. Attackers now target tokens and API keys, not passwords. https://t.co/D5dg26pZg6

AI Uncovers Thousands of Zero‑days, but Human Expertise Remains Essential
Anthropic's #Claude found over a thousand zero-day vulnerabilities across every major operating system and browser. The same #AI capabilities that enable that defense also make offense cheaper. The difference is that #cybersecurity defenders still need experts to act on what...

AI Code Raises Critical Bugs 1.4×; QA Still Essential
AI-generated code comes with a hidden tax: 1.4x more critical issues in pull requests, including basic security flaws. You can't skip QA just because AI wrote the code. #DevSecOps #CIO https://t.co/p7yRF5nHjg

Fog Cloud Computes on Encrypted Data via Homomorphic Encryption
The Fog is a cloud platform that keeps data opaque, even while computing with it. Learn how it uses a technique called fully homomorphic encryption to ensure information is secure. https://spectrum.ieee.org/the-fog-cloud-encryption?share_id=9376961

Public Hype on Quantum Computing Eases Cryptography Concerns
The fact that major public companies are hyping quantum computer progress actually makes QC progress less scary for cryptography.

DeFi Exploit Highlights Risks of Upgradeable Contracts
🚨 ANOTHER EXPLOIT IN DEFI Wasabi Protocol has been exploited for $4.5M. The platform allows leveraged trading using pooled on-chain liquidity. This latest incident once again exposes the dangers of privileged access and upgradeable smart contracts. Security concerns in DeFi continue to mount....
Cyberdost Hires 195 Tech Experts for India's Digital Security
.@Cyberdost (Indian Cyber Crime Coordination Centre) the national nodal agency for tackling cybercrime is hiring 195 technical professionals. I interacted with the I4C team recently and was encouraged and inspired by their progress and commitment to securing India’s digital ecosystem. This...

AI-Driven Cybersecurity: Machines Defending Against Machines
AI is reshaping cybersecurity from both sides. At hacking conferences, the focus is shifting toward systems that can detect, respond and defend in real time, often faster than humans. The direction is clear. In cybersecurity, machines will increasingly protect against machines. https://t.co/JdQHp2xcCH...

GPT‑5.5‑Cyber Deploys to Defenders, Securing Critical Infrastructure
we're starting rollout of GPT-5.5-Cyber, a frontier cybersecurity model, to critical cyber defenders in the next few days. we will work with the entire ecosystem and the government to figure out trusted access for cyber; we want to rapidly help secure...
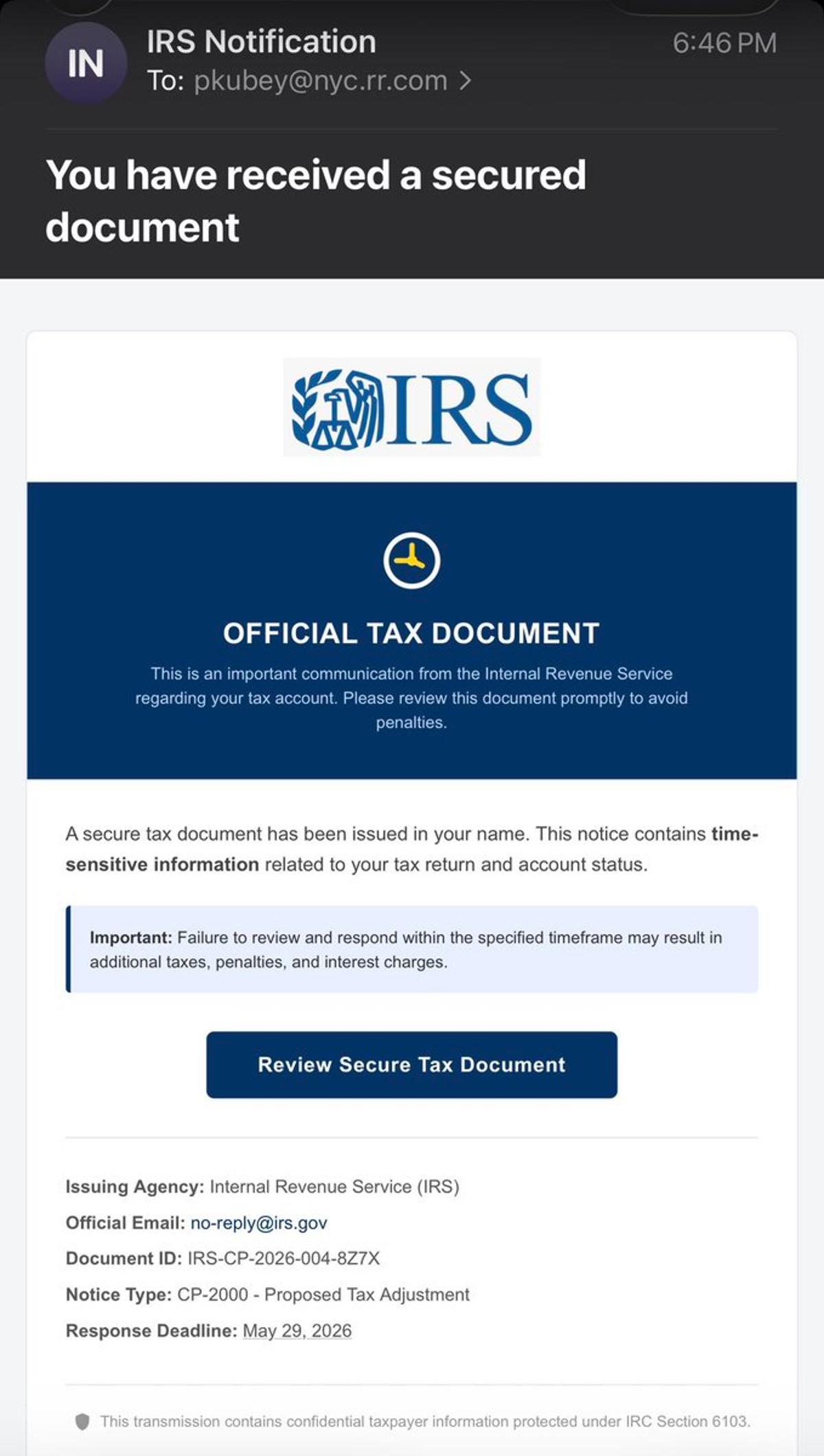
IRS Scam Email Uses Fake Pobox Address
Today’s scam email from the “IRS.” Of course the sender’s email address was bill.mitchell@pobox.com https://t.co/jVYjYXrqEO

Social Engineering Breach Forced Me to Quit Wells Fargo
Last month my WellsFargo online banking account was taken over theu a social engineering attack on the WellsFargo call center. (I know this because a fraud investigator walked thru their logs with me; account phone number changed via call in...

Critical DotNetNuke Flaw Lets Attackers Upload Malicious SVGs
A critical DotNetNuke vulnerability allows attackers to upload malicious SVG files, execute XSS, and gain server control through authenticated user actions. https://t.co/EfO3Jp9uPf

OpenAI Expands Trusted Access, Urges New CISA-Like Body
OpenAI just published their cybersecurity intent and vision. There is news here (but most of it is filler and puffery). As far as I can tell, the big news is they are expanding their Trusted Access for Cyber (TAC)...

Map Cloud Security Services Across AWS, GCP, Azure
Cloud Security mapped across the Big 3 ☁️🔐 AWS vs Google Cloud vs Azure—same goals, different tools. From IAM to KMS, WAF to DDoS protection—understanding these equivalents is key for multi-cloud + DevSecOps workflows. If you can map the services, you can secure...

Choosing CTEM vs ASM: Which Delivers More Value?
Are you using CTEM or ASM for your organization? Interested to know how you've integrated these tools into your security operations? What’s delivering the most value?

Hang up when Telemarketers Demand Gift‑card Payment
The next time a telemarketer asks you to pay with a gift card, hang up. https://t.co/eKgkYoJ3Cw

Even Perfect Prompts Can't Stop AI Code Vulnerabilities
“No matter how well you prompt, code generators generate security vulnerabilities” - Michael Beckley #AppianSummit #AI #CIO https://t.co/W1VnkrnWPi

Encryption, Proxies, AI Fuel Growing Cybercrime Threat
IOCTA 2026 – The evolving threat landscape: how encryption, proxies and AI are expanding cybercrime - Internet Organised Crime Threat Assessment (IOCTA) 2026 | Europol https://t.co/cAUHnrvjYT

Ransomware Wipes Files over 128KB; Backups Essential
New ransomware variant destroys everything bigger than 128kb, making retrieval without a backup impossible. https://t.co/yeVN6pONet

Workplace Apps Harvest Your Data and Sell It
Your personal data is being collected by your workplace app, and sometimes passed on to advertisers https://t.co/cZIU1lZZRT

Starlink's Precise Location Tool Could Aid Malicious Actors
Duh, why does no one think about the bad actors that might want to use this feature... it's just like the speed limits on airborne use...

GitHub Patches AI‑found Critical RCE in Under Six Hours
GitHub rushed to fix a critical vulnerability in less than six hours. A critical remote code execution vulnerability was discovered using an AI model and patched within hours. Details 👇 https://t.co/MVGhe8zsCX