Social Media Scams Surge 8‑Fold, Cost $2.1 B
Scams that *start on social media* have increased 8x since 2020, including: - Investment Scams (crypto scams, fraud investments) - Shopping Scams (bogus items via scam ads/listings) - Romance Scams (fake crisis to steal $, fraud investment reccs) Reported losses = $2.1 billion https://t.co/qyYjhuNEae
DeFi Hack Delays, Doesn’t Deter Traditional Finance
1/ A $293M DeFi exploit should’ve been the kind of event that sends TradFi running. Instead, Morpho CEO Paul Frambot [ @paulframbot ] says the reaction has been more revealing: Delayed? Yes. Deterred? Not quite. 👇

Digital Security Improves; Overall Damage Is Decreasing
Narrative violation: The digital world has, empirically, become more secure, not less. ~Every device can be hacked at some cost, to be clear. But total volume of damage has declined.
AI Era Amplifies Need for Personal Data Protection
#AI-Powered Future: Why Protecting Personal #Data Online Matters More Than Ever by @SecurityTrybe #CyberSecurity #InfoSec #IT #Tech #Technology https://t.co/ZvCjZmvVoW

Link Cyber Risk Directly to Financial Outcomes, Not Just Controls
How are you actually measuring cyber risk today? Frameworks are helpful, but they don’t always translate cleanly to business impact. Are you tying risk to financial outcomes or still working mostly in controls and maturity?

US Drops Probe Into WhatsApp‑Meta Chat Visibility Claims
The US has abruptly ended its investigation into claims that WhatsApp chats were visible to Meta. https://t.co/f1WXpQz58J

AI Uncovers Injection Flaw; Defenders Must Act First
The bad news is they got in; the good news is that they used an AI to find the security hole (an unsanitized injection) via decompiling the executable and got it quickly fixed. So the vulnerabilities can be found -...

Windows Silently Snapshots Screens for AI Training
Windows has over 1.4 billion active users. Almost none of them know their operating system is quietly taking snapshots of their screen to train Microsoft's AI. That is 1 of 18 hidden tracking mechanics Microsoft buried deep in the system settings. Here's all...

Unified Employee Data Makes SOC 2 Compliance Effortless
Hot take: compliance feels complex because of how it gets handled. SOC 2 turns painful when teams try to recreate reality inside a compliance tool using integrations, exports, and manual checks. That’s what turns it into a second job. @Rippling takes a different...

Recent Exploits Expose Infrastructure Gap Before Trillion‑Dollar On‑Chain Adoption
3 bridge incidents in 3 weeks sounds bad but i think the harder read is this, we have been asking the biggest institutions in the world to come onchain and trust us with trillions. How can we expect that while...

Join a No‑Pitch Virtual Roundtable on Transport Security
I'll be hosting a virtual roundtable tomorrow on securing transport systems. No pitches, just real discussion with cybersecurity leaders. Great way to network and learn. If you're interested, register now at: https://buff.ly/L7CxprA
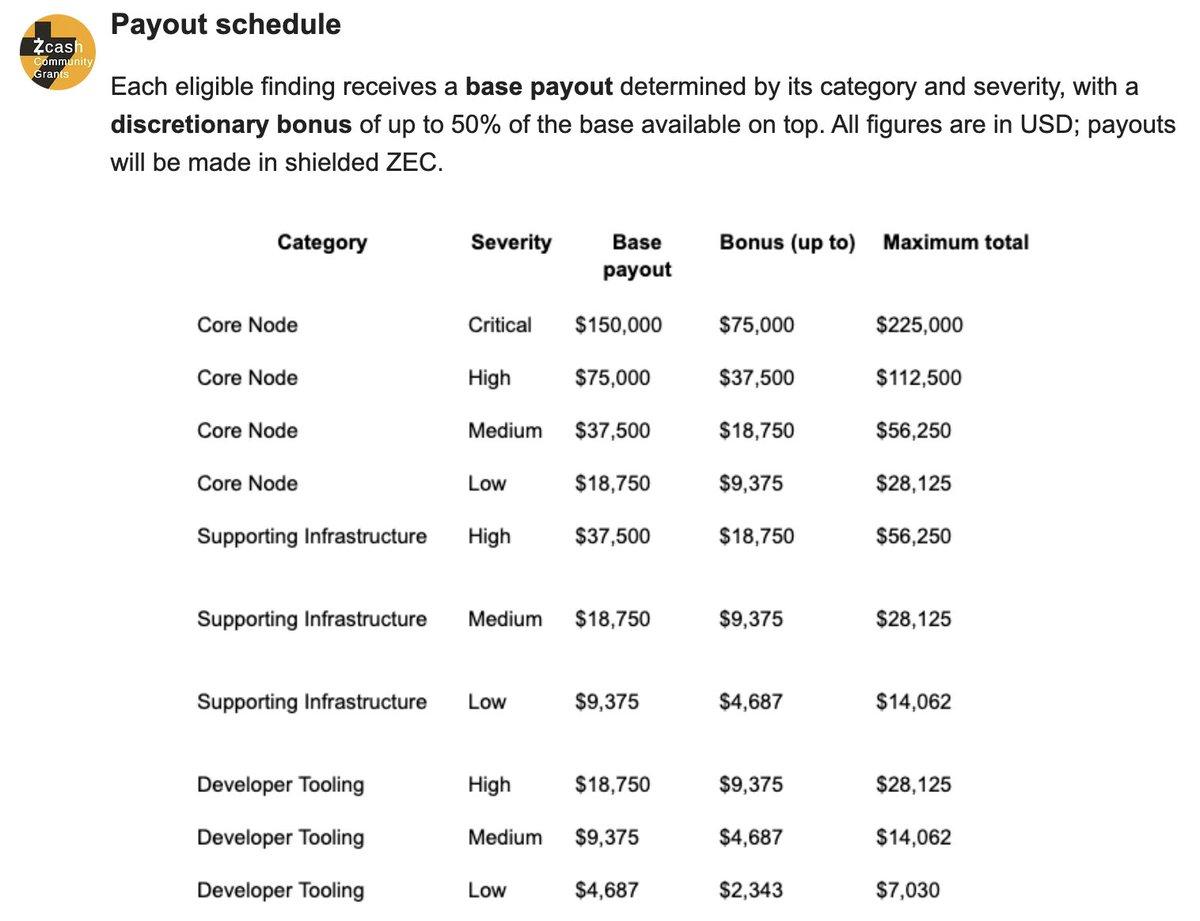
Zcash Allocates $1M in Bug Bounties for Security
Zcash cybersecurity defenders never sleep. Zcash Community Grants Committee announces $1,000,000 worth of bug bounties: https://t.co/zk60sAFmlJ https://t.co/JgomZhw33E

Coupang Breach Exposes Millions of Customer Accounts
On 29 November 2025, Korean e-commerce company Coupang reported a cybersecurity breach, with millions of customer accounts leaked to third parties https://t.co/FUXEOMmvwi

Legacy Apps Pose Security Risk, Mythos Offers Solution
Legacy apps are a security risk with Mythos - Matt Calkins, CEO @Appian #AppianWorld #AI https://t.co/tbJBn7Pw2l

Global Tax Scams Exploit AI and Fake Government Sites
*International Tax-Scam Roundup* Here's an overview of scam tactics being used around the world targeting taxpayers getting ready to file their returns. So, how are these cyber-crooks swindling folks? Well, the methods range from classic tricks to newer AI-powered schemes. For example: ❌...
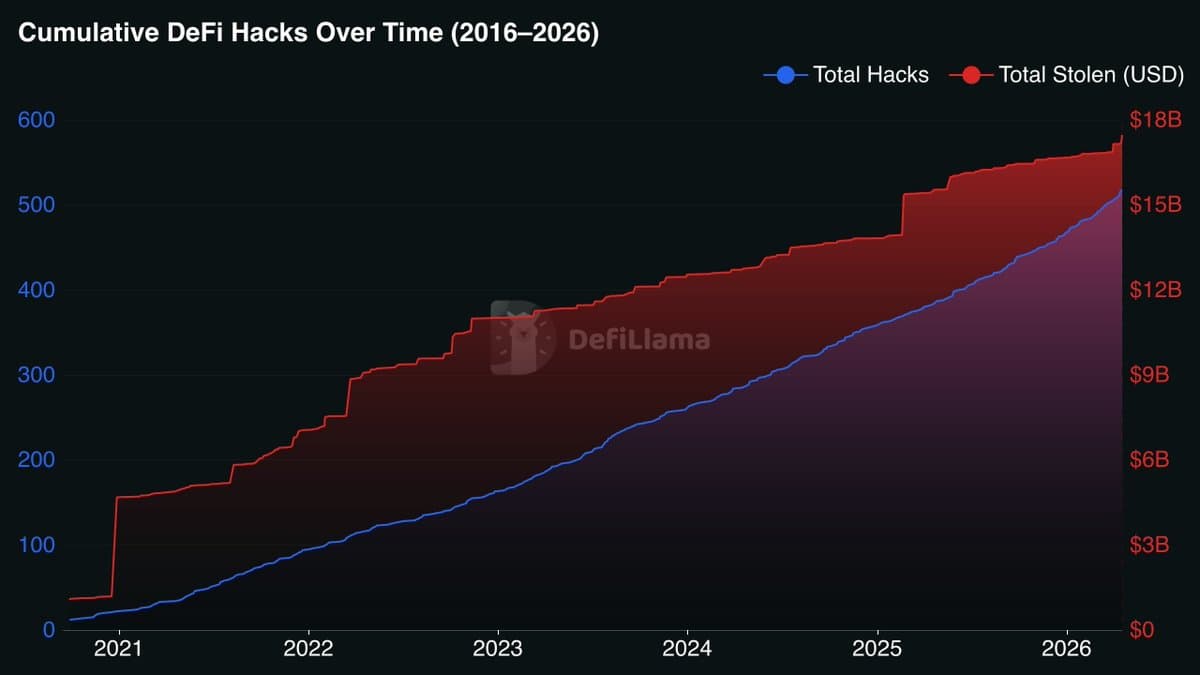
Hackers Stole $17B in Decade; Self‑custody Essential
🚨UPDATE Over the last 10 years, hackers have stolen more than $17 Billion across 518 different incidents. That’s an average of roughly $33M per hack and one major exploit every single week for a decade straight. Over $3.6B of that came from...

Everyone Claims They'd
.@griffgreen on @unchained_pod: after billions stolen by North Korea, "at least we got a little bit of a punch in." And almost everyone says they'd have signed the transaction. https://t.co/UkKnClTb9n
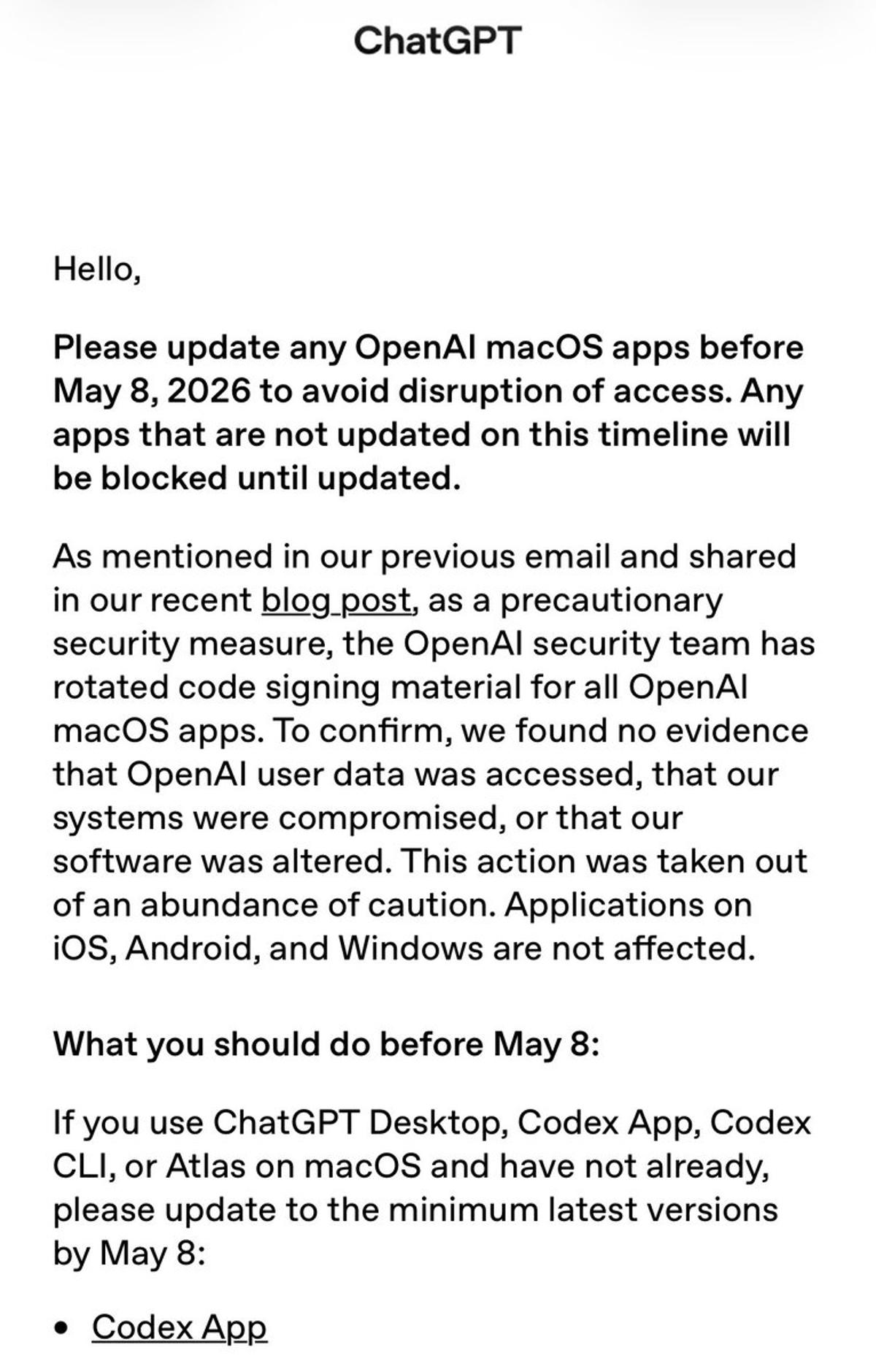
OpenAI Urges Mac Users to Update by May 8
Uh oh. OpenAI is warning users of its Mac apps to install the latest security update by May 8th to avoid being locked out https://t.co/TgQ2TCnxqm

Formal Verification: Math’s Shield Against AI-Driven DeFi Hacks
🤖 "The power has shifted way more toward the attackers ... but we have one tool: formal verification. AI can break a lot of things, but it can't break math." -- @PaulFrambot on all the hacks in DeFi https://t.co/o3h67jD0JH

Mether Pins Kelp Hack Blame on Kelp, LayerZero, Aave
.@0xMether's breakdown of fault in the Kelp hack is worth watching. He doesn't let Kelp, LayerZero, or Aave off easy. @bitsandbips https://t.co/5zLVFRyZo4

First OpenAI Spoof Spam Lands, They're Officially Big
Got my first @OpenAI related spoof spam attempt. They are now technically big time :)
One Password, No Storage: Secure, Easy Logins
Cryptographers created a browser extension password manager that only requires you to remember one #password and stores none of your passwords, allowing you to log in to as many sites as you require. People reported feeling more secure and found...

Secure Mobile Communications: T-Priority Bridges VPN Mobility Gap
Having served as a public safety director, first responder safety is always top of mind, including secure communications when units move. Tunnel-based VPNs were never built for movement. T-Priority with T-SIMsecure closes the gap. @T_Priority Partner https://t.co/CHTZbTwufN

SMS CAPTCHAs Are Scams that Can Cost You
CAPTCHAs asking you to send an SMS are actually a scam that can cost you big time. https://t.co/IhoxFfJzCH

SaaS Founders Battle Relentless Bot Scraping of Landing Pages
Something I hear from more and more SaaS founders is that they have to actively fight and mitigate massive bot fleets scraping their pSEO pages. Solo-founder-run businesses fighting billion-dollar companies. Cloudflare mitigates SOME stuff, but there's still a lot to handle. I'm...

RunZero Masterfully Secures Fragile OT and ICS Environments
...In which hdmoore and I go "full packet-rat" and dig into what runzero have been developing to support the complicated , fragile, often safety-critical OT and ICS world. If you've ever knocked over a dusty Solaris box with an nmap...

AI only Reports Real Bugs; Scaling Triage Is Temporary Fix
AI is not going to flood you with real vuln reports unless you have a ton of real vulns. Adding resources to a vuln disclosure process to keep up with triage & bug fixing is a temporary investment at the loud...

Red Teams Leverage LLM-Generated Exploits to Strengthen Security
LLMs can chain obscure bugs into full exploits; the interesting part is how red teams are using that same capability to harden real systems. https://spectrum.ieee.org/anthropic-claude-mythos-preview-code?share_id=9389166
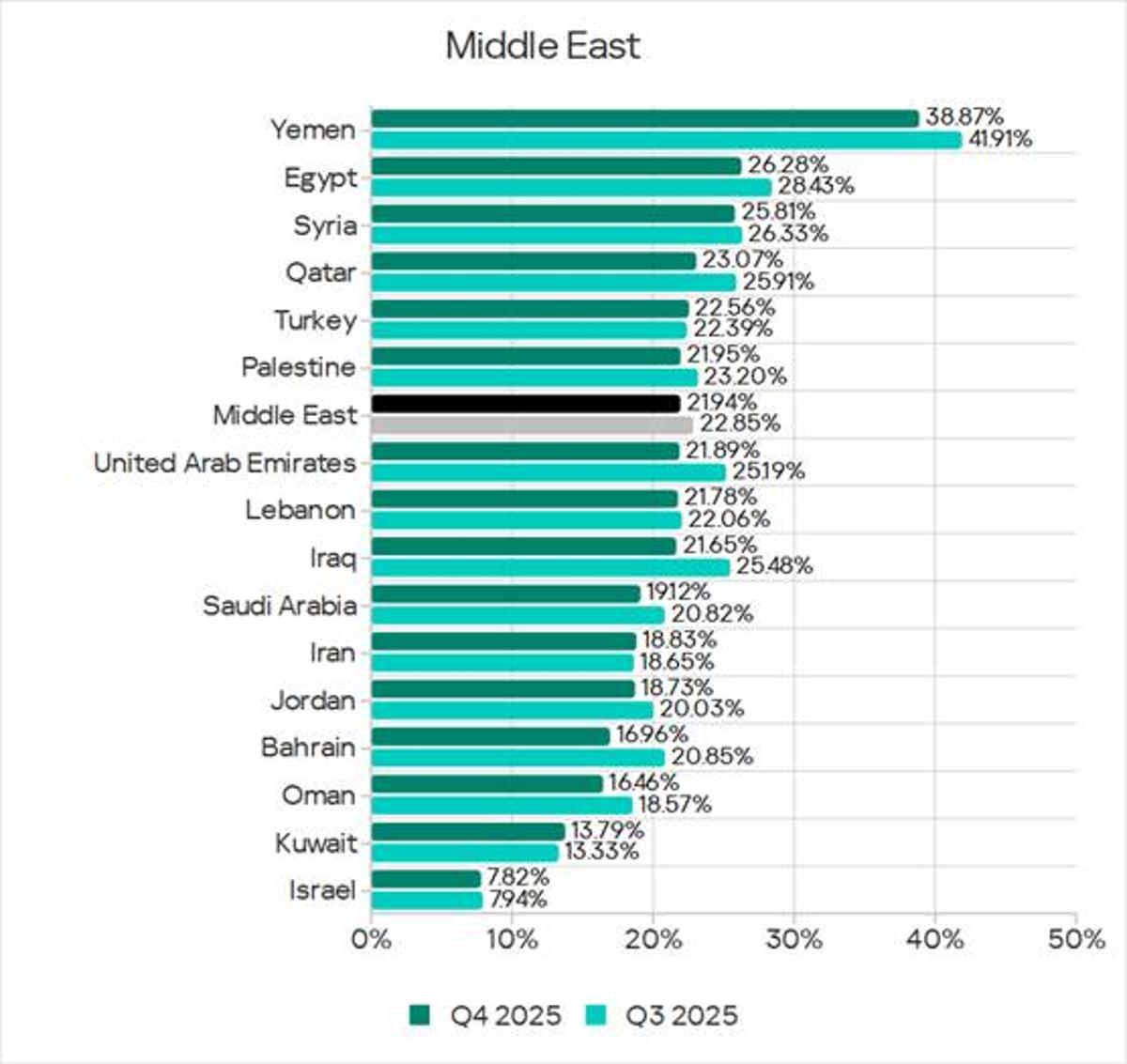
Yemen Ranks Second in ICS Attacks; Israel Among Safest
The threat landscape for industrial automation systems in the Middle East – Q4 2025: high risk of targeted attacks, network segmentation issues, and numerous espionage attacks. Yemen ranks second globally for the share of ICS computers attacked, while Israel is...

New Unpatched Windows RPC Privilege Escalation Disclosed
We reveal details of a previously unknown privilege escalation technique in Windows RPC. The vulnerability is due to an architectural flaw and is currently unpatched. We also discuss risk mitigation measures: https://t.co/TexY19gONO https://t.co/7zo8vuhtF1

Never Click Email Links—Phishers Exploit Gmail Quirks
Phishing emails getting smarter and smarter. Gmail ignores "." in address (and also "+xyz"). Simplest rule is to never click on any link in an email.

Regulators Target Hotel AI Use Over Data Privacy
Regulators turn attention to hotel AI governance “Hotels are increasingly deploying AI for functions such as … dynamic pricing, and personalised marketing. These systems rely on large volumes of behavioural and transactional data, raising questions about consent, storage, and secondary...
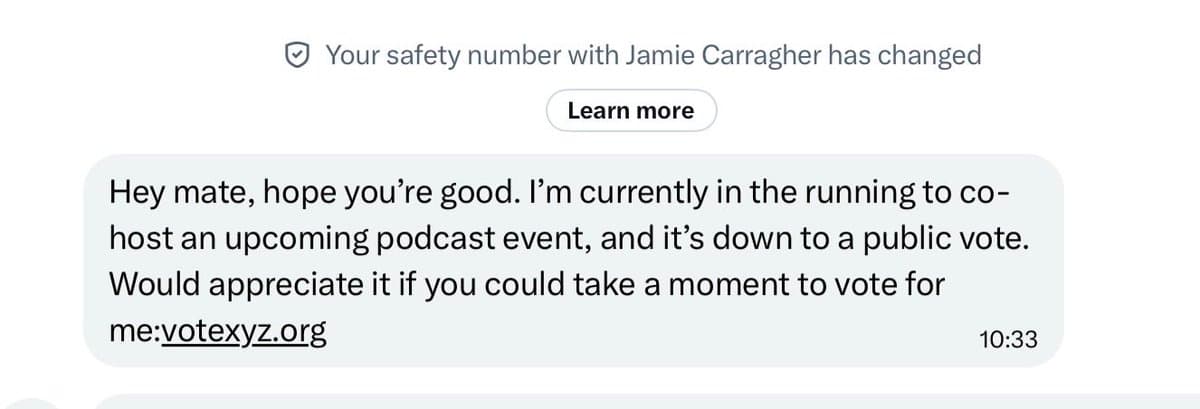
Jamie Carragher's Account Hacked—Avoid Suspicious DM Links
If you get a DM from Jamie Carragher asking to click on a link for a competition or see some unusual posts on his account do NOT engage. Someone has hacked his account and it’s a scam. Has happened to...

Hackers Fabricate Problems, Then Pose as IT Helpdesk
Hackers first create a problem then try to "solve it" by pretending to be IT helpdesk. https://t.co/UqeWuAgF4r

Data Breaches Expose Surprisingly Odd Email Address Patterns
Fascinating the sorts of email addresses that appear in some of these data breaches 🤣 https://t.co/grfbmi39Qf
Identity Theft Is Really Just Data Theft
#DigitalIdentity #HotTake 1/6 There is no such thing as identity theft; there is only data theft. Data breaches do not represent an “identity” problem but a data quality problem. More: https://t.co/0JJyam6o0T
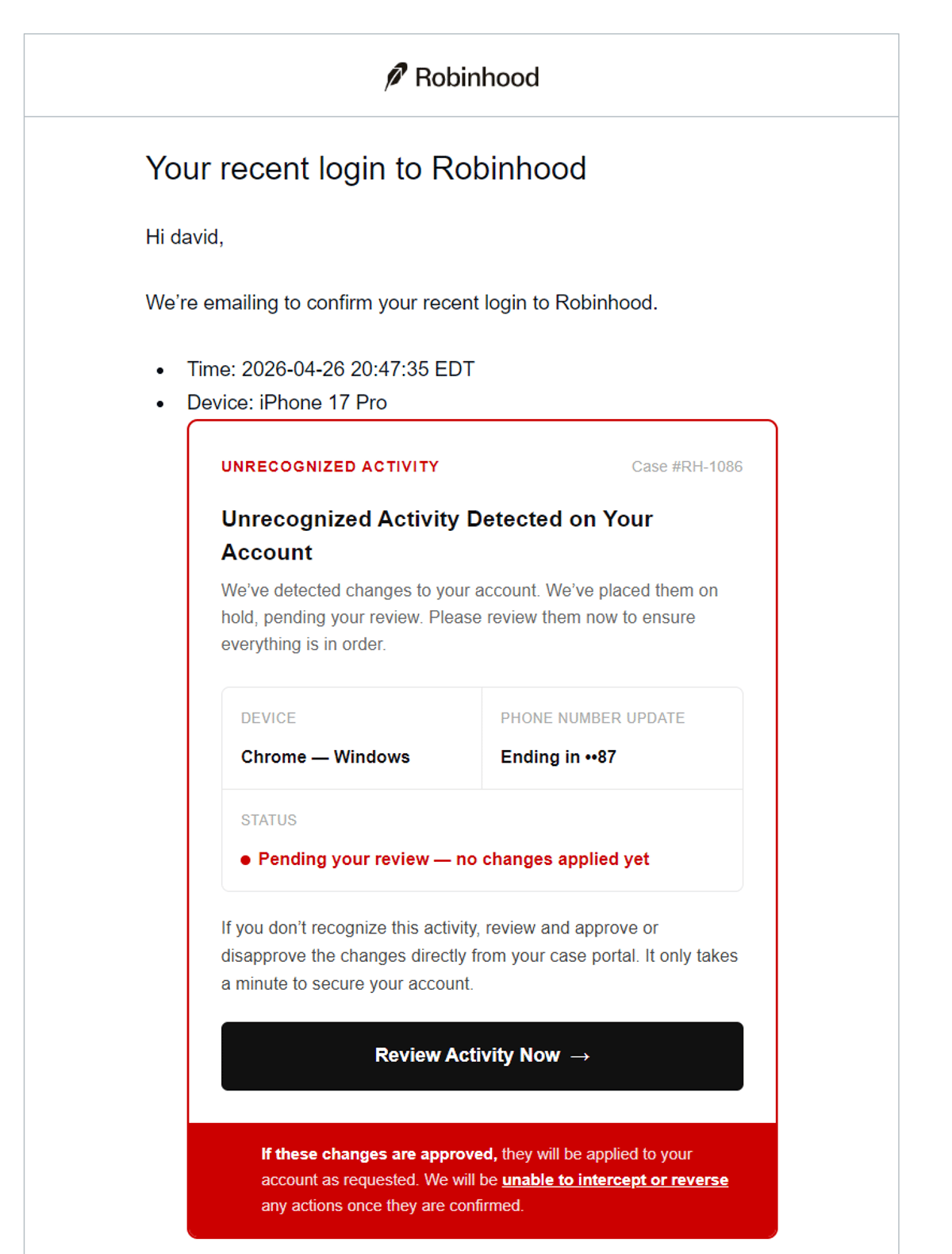
Robinhood Emails Are Phishing Attempts—Stay Vigilant
WARNING: Any emails you get that appear to be from Robinhood (and may actually be from their email system) are phishing attempts. Example: https://t.co/oJilpQqJdp

Aave’s Unified Pool Design Fuels $193M Bad Debt
Who Pays for the $193M Aave Bad Debt? 40% of LayerZero OFT deployments still run a 1-of_1 signer. @0xMether and @blockworksres break down how that choice, combined with Aave's unified pool design, produced $193M in bad debt. @bitsandbips Timestamps: ⚠️ 3:36 Dissecting the rsETH...
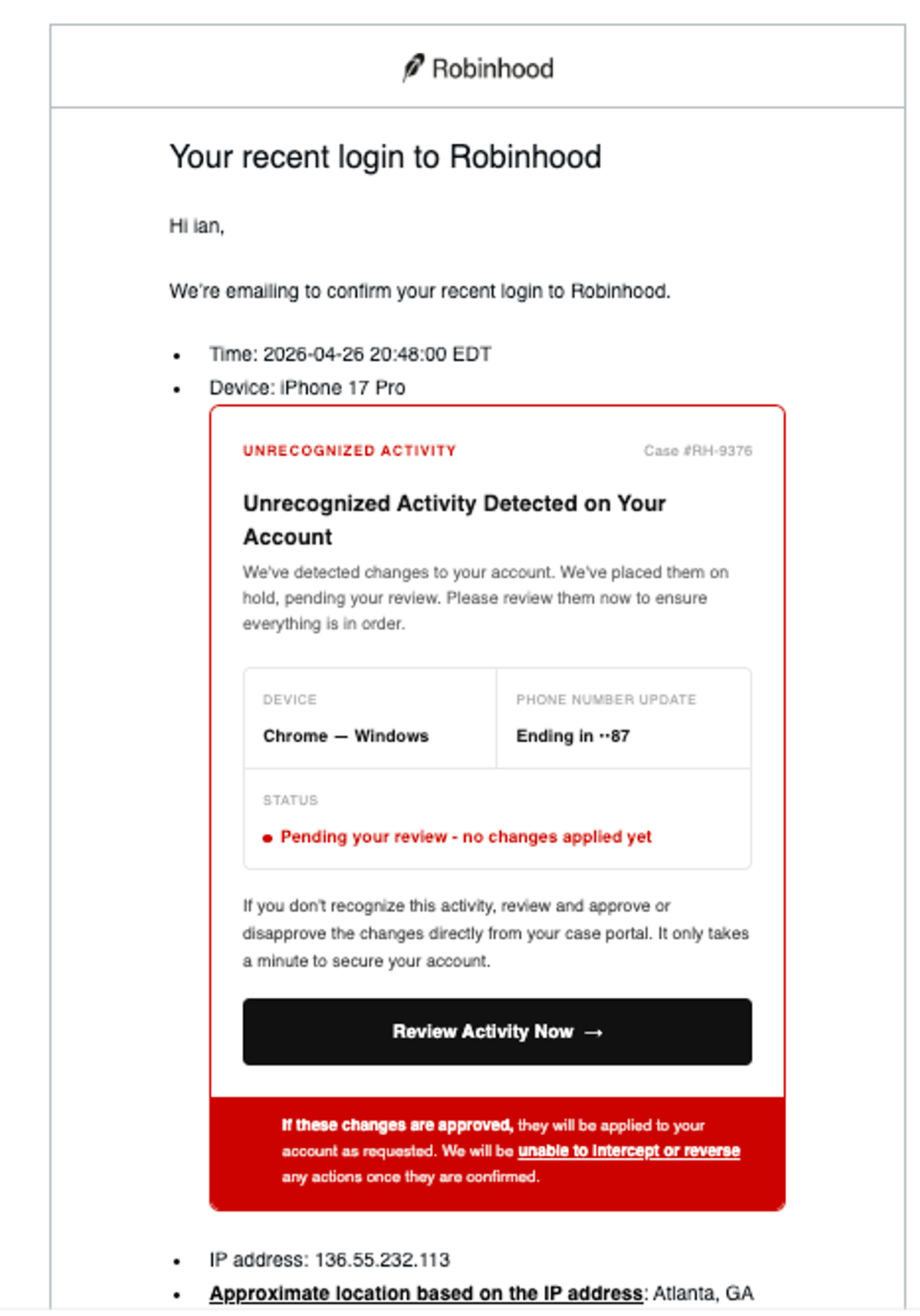
Sophisticated Robinhood Email Spoofing Threats Rise, Stay Vigilant
this looks like an extremely real @RobinhoodApp email but its fake. the email it was sent to was slightly off. most of the links except the big one to reset my account link to RH websites. email comes from noreply@robinhood.com....
Grant Williams at Risk—Enable 2FA Now
Grant Williams is the next account to be hacked. Turn on 2FA folks. Jeez. https://t.co/c6issUS2KE

Twitter's Chaos: Broken Polls, Hacks, and Phishing
Is it me or X starting to look like a vibe coded mess? Polls are broken. Accounts are getting hacked. My DMs are full of phishing scams. Basics that used to work no longer work.

Agentic AI Shatters Old Security Model; Cyera Offers Solution
Agentic AI Broke the Old Data Security Model. Cyera Is Betting It Can Build the New One. https://t.co/gAuASNYvDf
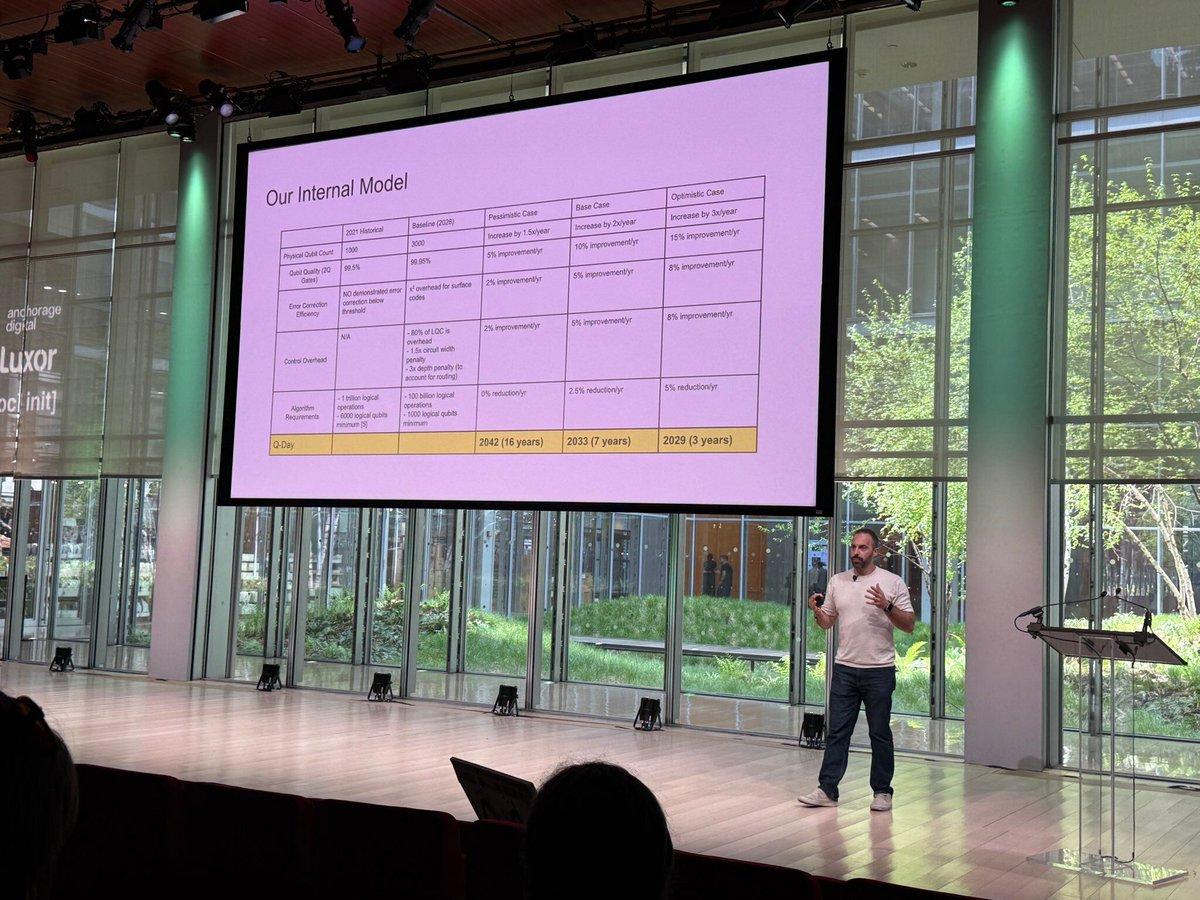
Q-Day Could Arrive Within 3‑7 Years, Not Decades
Everyone's asking when Q-Day is. That's not the right question. Everyone wants the Q-Day date so they can plan backwards. But can change your cryptography at all, and fast? Some data from a recent Project Eleven (@projecteleven, @apruden08) presentation on Q-Day modeling: -...

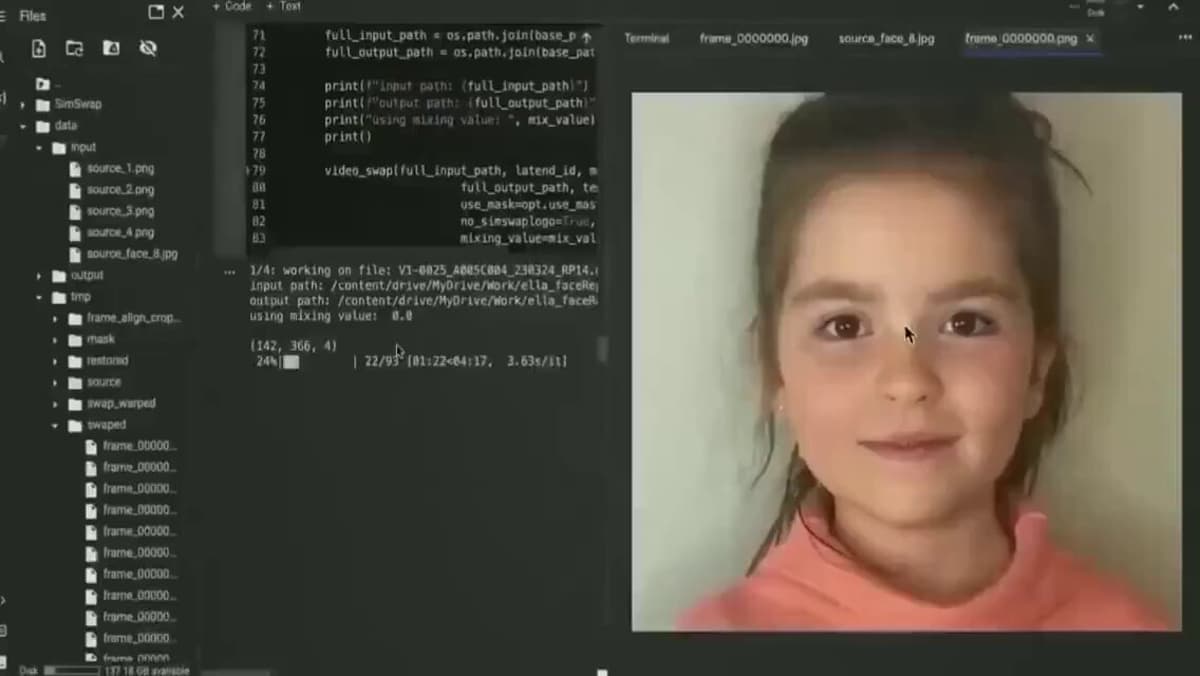
AI Scams Are Heading Into a Darker, Stranger Era
the AI scam era is going to be so much darker and weirder than people realize https://t.co/jqF5bwKmgY
Blockchain Enhances Data Security: Practical Guide
How to Apply #Blockchain #Technology to #Data Security by Zac Amos @_odsc Learn more: https://t.co/xNYYkp3Mf8 #CyberSecurity #Infosec #IT #Tech https://t.co/m6A6nCczW5

Spike in Phishing DMs Suggests X Account Breach
getting so much phishing email in my X DMs. either a lot of accounts have been hacked or someone has discovered a back door to posting DMs.

Spam Texts Masquerading as Friends Signal Platform's
Latest sign of the end of x: overwhelming number of spam private text messages supposedly from people I know, but in fact, pure spam/phishing
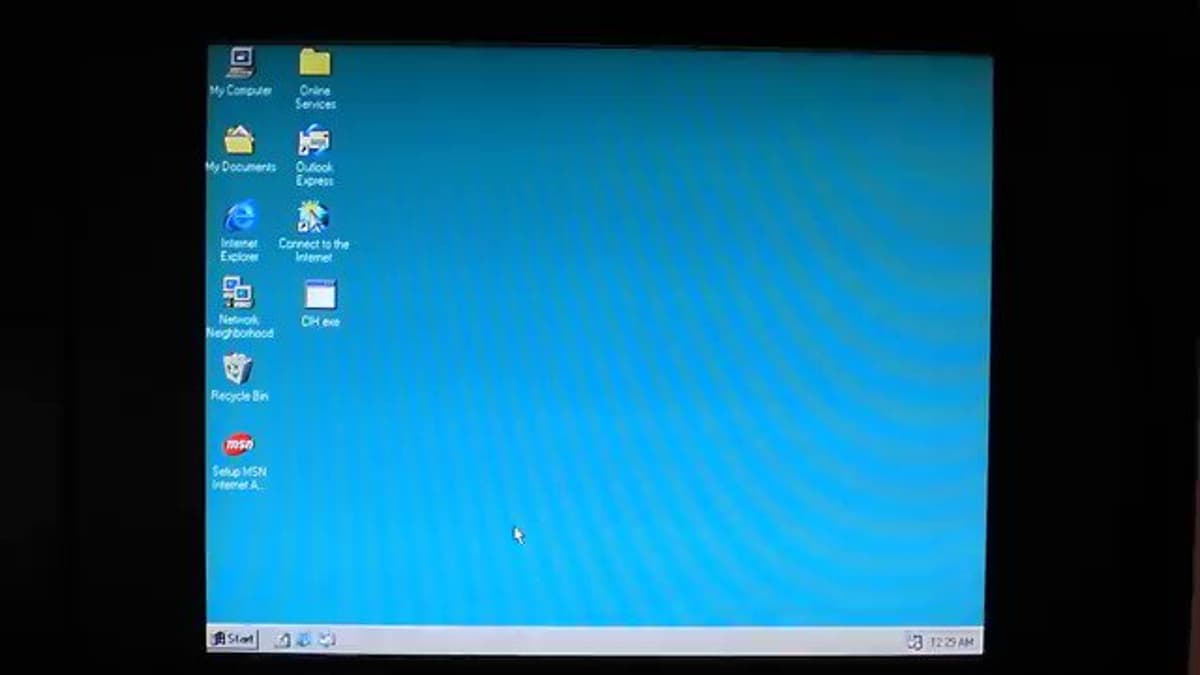
1999’s CIH Virus First to Attack PC BIOS
#ThisDayInTechHistory. April 26, 1999. The first known virus to target the flash BIOS of a PC, the CIH/Chernobyl Virus triggers its payload on this day, erasing hard drives and disabling PCs primarily in Asia and Europe. https://t.co/urNvbAJTbh

EU Demands Real‑time Google Search Feed, Privacy at Risk
tl;dr: the EU wants to force Google to make a real time feed of all searches done on Google, with bullshit privacy protections, available to any EU company or researcher who wants it. Complying is evil. A future EU government should...

Donation Pages Become Fraud Hotspots, Costing Nonprofits Thousands
A sustained attack on your donation page that generates hundreds of thousands of declined transactions can rack up thousands of dollars in authorization fees that were never legitimate: https://blog.clickandpledge.com/why-nonprofits-are-ground-zero-for-credit-card-fraud/ ✅