
AI May Not Deliver Perfectly Secure Code in 5 Years
Given massive AI advances, do you believe than within 5 years it would be feasible to write 100% vulnerability-free code? #NoNuancePoll
Tax Tribunal Scotland Site Lacks Security Certificate—Avoid It
Quick warning to tax people to not go to Tax Tribunals Scotland's website. No security certificate, so it's either been hacked or had an IT snafu. https://t.co/XaIJLHfAGO

EU Flags Insecure, Cheap Inverter Software as Security Risk
The inverter (especially its software) is a security risk if nog open source and managed well and it's a relatively cheap component compared to solar panels and battery cells. I'm glad the EU recognizes this.

Cross‑zone Composability Faces Hurdles in Privacy Blockchains
🧩 In a world of privacy blockchain, where switching from chain to chain can create data leakage, what does that mean for DeFi's money legos? "I don't think the composability dream is dead. I think you can have composability within zones....

Hackers Hijack AWS Tools to Power Phishing Attacks
Hackers are stealing access to legitimate AWS tools and using them to launch phishing campaigns. https://t.co/qLfuOeGReN

Flip the Ratio: Cheap Assessment, Board‑
"The answer probably starts with flipping the ratio: making assessment as cheap as generation, paying for fixes instead of just finds, and treating supply chain security as the board-level priority it has been pretending to be."

AI and Quantum Threats Demand New Cybersecurity Frameworks
Why Cybersecurity Strategies and Frameworks Must Be Recalibrated in the Age of AI and Quantum Threats

Assess if Cloud Credentials Exposed Beyond Authentication
I need to take a look at this and see if you can essentially expose cloud platform credentials and permissions or it is purely auth with no additional attack surface.

Governance Gaps Amplify Risk; Enforce Ownership, Access, Monitoring
Digital infrastructure operates as a single layer across operations, where gaps in governance accumulate risk. Clear ownership, controlled access and real-time monitoring must become daily disciplines, since failures propagate across providers and teams. Microblog @antgrasso https://t.co/hplDKIGUOd
Tax‑authority Phishing Spreads ValleyRAT and New ABCDoor Backdoor
Phishing "from the tax authorities" → a modified downloader → the well-known ValleyRAT backdoor + the previously undocumented Python backdoor, ABCDoor. Learn more: https://t.co/8mFxmep5xC https://t.co/9yUZwdH8mO

AWS Nitro Isolates Resources, Blocking Copy‑Fail Exploit
If you were wondering if this affects AWS VMs ~ per Google aimode and AWS documentation: The AWS Nitro System mitigates the Copy Fail vulnerability through architectural isolation, specifically by pinning dedicated physical resources and eliminating shared Dom0 kernel components. AWS...

World Rushes to Enforce ID, Threatening VPN Anonymity
There’s something ominous about the speed with which the entire world has marched to require identification on platforms and, as I expected, begin the process of banning anonymous VPNs.

Security Vendors Must Own AI, Not Serve It
GenAI is going to augment nearly every layer of the security stack. The interesting question for vendors is not whether the stack disappears. It is whether you become a feature of someone else's AI, or whether AI becomes a feature of...

Protect Student Data: Practical Tips for Schools
🚨 Take action this #WorldPasswordDay to protect your students as they navigate digital spaces 🎙️Jump into this informative conversation to explore practical tips for schools & districts to safeguard student data. https://t.co/SkQFRzN8q8 @roxi_thompson

Bug Bounty Pros Question $22K Split ROI Amid AI Rise
I wonder how top bug bounty hunters feel about a $22K cash prize split between a bunch of people. I like the idea about rewarding defenders and programmers for work on AI but the ROI doesn’t seem to be there...

AI Will Redefine Cybersecurity Landscape
A glimpse into cyber-security’s #AI-driven future by @TheEconomist Learn more: https://t.co/NHIDasPYPw #CyberSecurity #Infosec #IT #Tech https://t.co/jB2cd6iA7u

Open‑source Models Behind Firewalls Could End Corporate Opacity
I actually think that some things you want to keep illegible *from other organizations* but IMO there is an opportunity to do this behind a firewall with open source models. To selectively send context out only when needed. I'd...

Open‑source Orchestrator Finds Critical Vulnerabilities in Minutes
𝚗𝚙𝚡 𝚍𝚎𝚎𝚙𝚜𝚎𝚌 We're introducing an open-source agent orchestrator for deep security reviews. We built it for internal use, and after running it against some major OSS projects, we gained conviction to share it with the world. Coding agents can now find critical vulnerabilities...

Fake Login Alerts Lure Users with Bogus Password Links
Received an email from X warning you of new or unusual login attempts, with a handy 'change password' link? Beware, it's a slick new phishing attack that can trick even the most vigilant user. I've seen this with other sites...

Binance Launches 7‑day Withdrawal Freeze for User Protection
JUST IN: Binance has rolled out Withdraw Protection, halting fund withdrawals for as many as 7 days to defend users against forced actions.

Exploring AI Mythos and Cyber Vulnerability Evolution at Oxford
Thrilled to be heading to @UniofOxford @blavatnikschool to have some interesting conversations with Ciaran Martin on #AI #Mythos & the evolution of vulnerability discovery, disclosure, & military defense & offense cyber capability proliferation
Geopolitical Cyberattacks Threaten U.S. Infrastructure, Demand Prevention
Cyberattacks are increasingly tied to geopolitical conflict, targeting U.S. infrastructure and causing financial loss. While botnet crackdowns show progress, threats persist. Cyber resilience now means prevention, not just response. https://t.co/Lj2AReSWPV
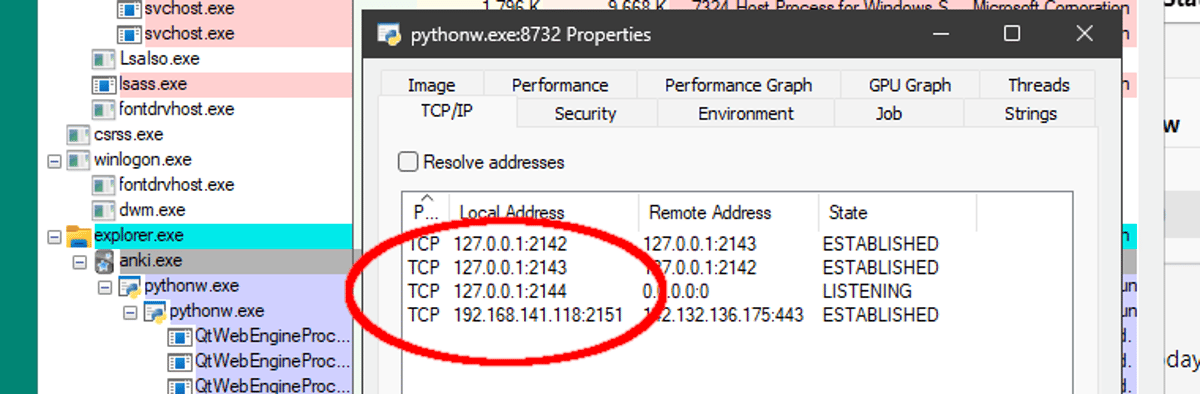
Browsers Must Enforce Private Network Access to Prevent Localhost Exploits
I really wish browsers would hurry up and implement private-network-access, developers often don't understand the implications. This weekend I tried a random flashcard application for language learning... and it started a localhost web service 😔 https://t.co/m8CjLgZh2I
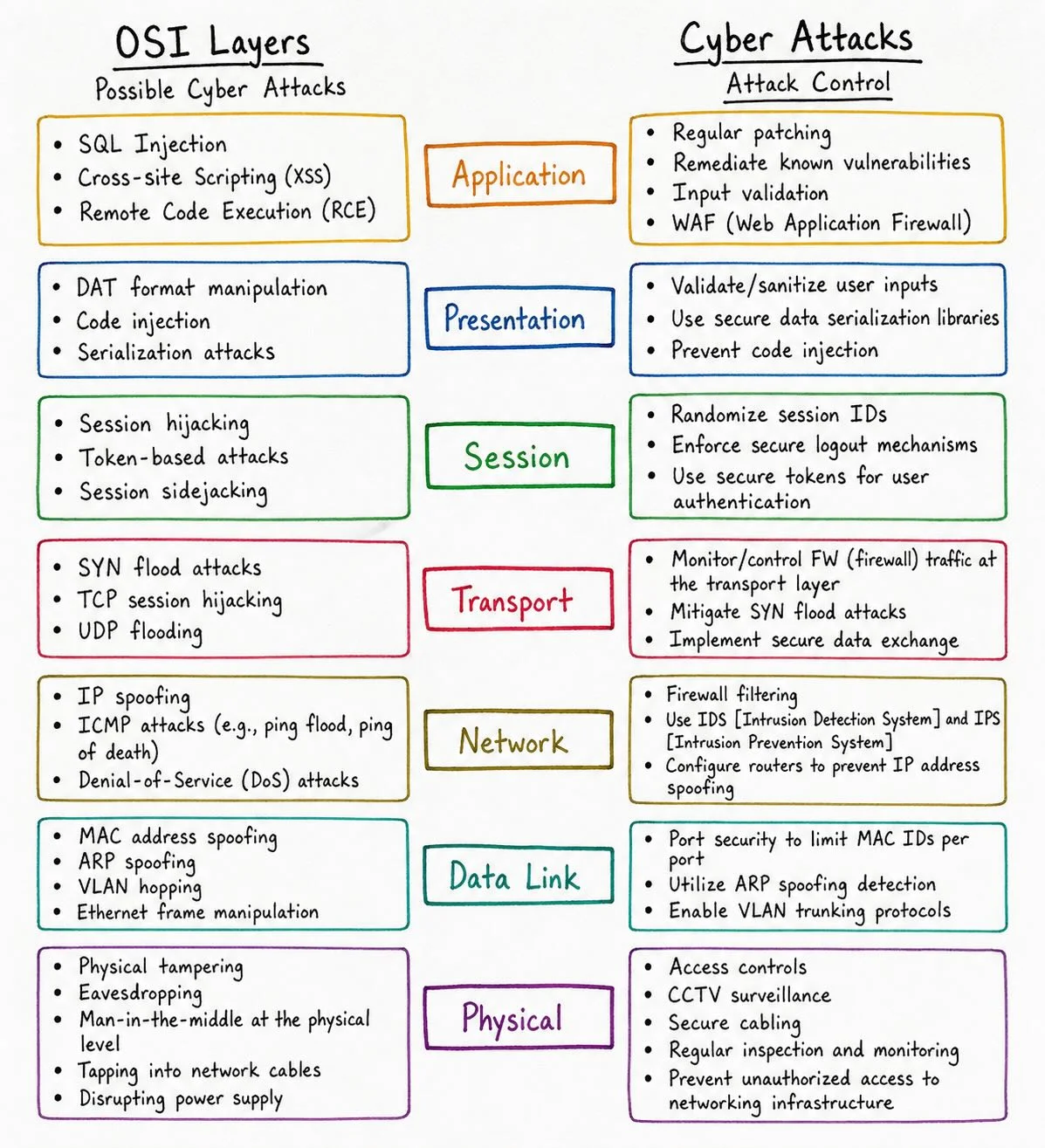
Layered Defense: Map OSI Attacks to Secure Each Layer
OSI Layers Explained (And How Hackers Attack Each One) 🔐 From Layer 1 to Layer 7 — every OSI layer has its own attack surface 👀 This breakdown shows how cyber threats map across the stack + how to defend each layer...

Unstructured Data Security Hindered by Visibility Gaps
RT One of the biggest security challenges with unstructured data is the lack of visibility and lineage as information moves across systems, clouds, and teams." #DataLineage #AI @Star_CIO https://t.co/PYomJYHDkY

OpenAI Extends Yubico Key Security to Users
OpenAI has been using Yubico keys internally already – with its Advanced Account Security program, now its users can too. https://t.co/WtS61B6wfe
Polsia's Real Business: Sending Spam Emails
Got my first Polsia spam finally Now I finally understand what their business really is: sending spam emails (allegedly) https://t.co/Zfxt6pMWdp

Insiders Now Biggest Cybersecurity Threat, Attackers Aware
Company insides pose a bigger risk than ever to company cybersecurity, and attackers know this. https://t.co/RXNWVP4M0v

AI Democratizes Phishing, Empowering More Attackers
Not only is AI helping attackers generate more sophisticated phishing attacks, but it's also democratizing tools to even more attackers. https://t.co/LWqNrqXAtd

CISA Lists Linux Kernel Flaw as Actively Exploited
U.S. CISA adds a flaw in Linux Kernel to its Known Exploited Vulnerabilities catalog https://t.co/hP6t8SVUqa #BreakingNews https://t.co/xKBTyF2jvn
CIOs Internalize Data Destruction to Prevent Custody Crises
Avoiding a chain of custody crisis: why CIOs are bringing data destruction in-house https://t.co/bnmzu4xKEt https://t.co/qCCXJqtiVm
Stop Excuses, Make Bitcoin Quantum‑ready Now
"Perfectly explained" is not how I'd describe it... Can we please stop looking for excuses to avoid the tough but necessary work to get Bitcoin quantum-ready?

May 4, 2000: ILOVEYOU Worm Sparks Global Email Outbreak
#ThisDayInTechHistory. May 4, 2000. The ILOVEYOU computer virus or worm virus is spread around the world via email. https://t.co/AEpIv3yV4P

Open‑source Models Protect Your Data From Extraction
If you're getting your inference from Anthropic or OpenAI or Google, you're being captured by extractive institutions: All your data is going to them (and hackers, rogue employees, governments... both today and tomorrow) Inference can be private. GLM 5.1, Kimi K2.6,...

Salt Typhoon Hack Hits IBM Italy, Warns Europe
Salt Typhoon breach IBM subsidiary in Italy: a warning for Europe’s digital defenses https://t.co/beEgVw6fzU #APT https://t.co/JYfzkDZzUz
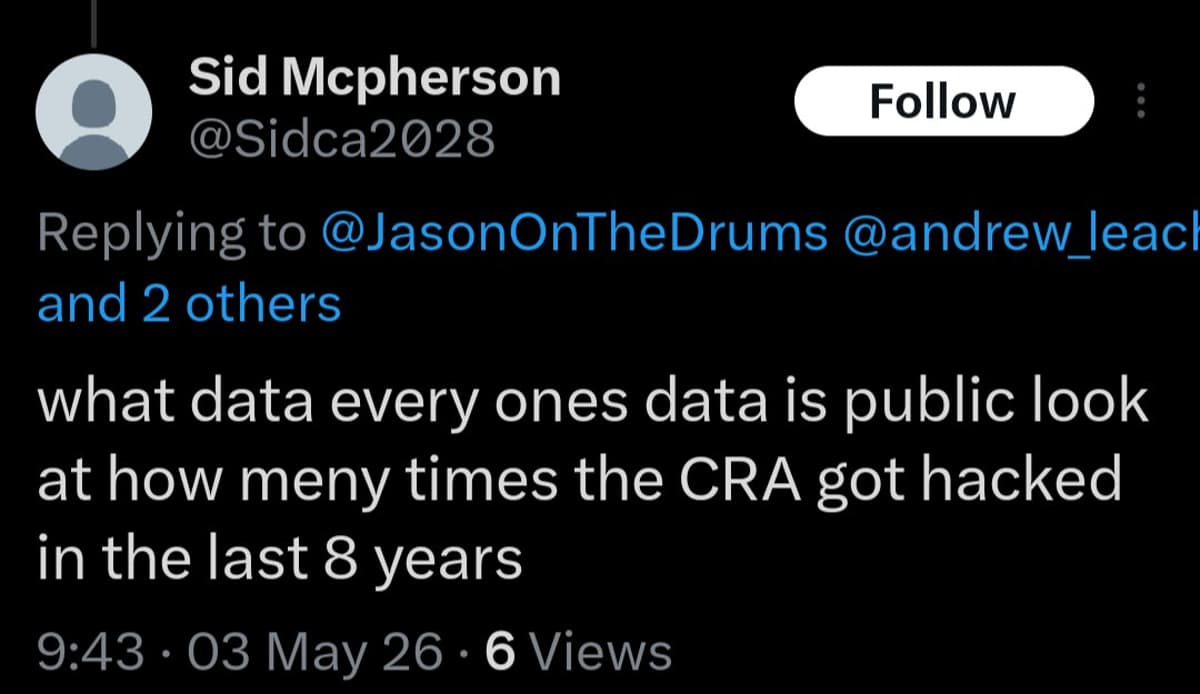
From Phone Books to CRA Hacks: Privacy Eroded
They've moved on from "it's in the phone book" to "everything you've ever submitted to the CRA is public because they've been hacked." Totally normal days for the separatists. https://t.co/ErdaXHvDlT

Skilled Triagers and Secure Code Beat AI‑only Solutions
More reason to have a bug bounty program with triagers who know what they are doing, The attackers that find the same vuln aren’t going to report it to a cert. what if the triager asked AI if that was...

AWS Platform-Wide Hack Triggers 17-Hour Service Outage
as insane as it sounds, it appears #AWS had a platform wide hack and nobody is talking about it.. we've had 17+ hours of "Restricted Services" from ALL of @AWScloud in America & Australia. the reason given, was "Account Compromise", which...

Detection Stays Ahead by Tracking Evolving Deepfake Artifacts
Deepfakes are getting better; the MNW dataset shows how detection can still keep pace by tracking real-world artifacts over time. https://spectrum.ieee.org/deepfake-detector-microsoft-generative-ai?share_id=9448061

Critical Linux Kernel LPE and Long‑Running cPanel 0‑day
#Weekinreview: High-severity LPE vulnerability in the Linux kernel, cPanel 0-day exploited for months https://t.co/ONQLU7P3N9 https://t.co/SU6nJcj4Uw

Claude’s Spyware Reveal Highlights Ethical Leadership Failure
Claude just got exposed for sneaky spyware. Anthropic. secretly installs hidden System Components, injects a “Native Messaging Bridge” into multiple browsers without your knowledge or consent. This is not a technical glitch. This is a Leadership & Ethics failure.

Congress Must Fund DOT‑FBI Task Force Against Transport Crime
Congress should fund a DOT + FBI task force to investigate and prosecute the organized criminals that have infected our transportation networks.

AI Agent Erases Production DB, Reveals API Backup Flaws
Cursor AI agent deleted a production database and backups in nine seconds, exposing serious flaws in API design and backup isolation https://t.co/RxL0fC5yHM

Smith’s Governance Failures Expose Election Data Breach
Real Scandal: Danielle Smith’s Governance Failures Behind Election Data Breach UCP "ungoverning" strategy guts public agencies like Elections Alberta, preventing them from properly protecting the public. https://markhamhislop.substack.com/p/real-scandal-danielle-smiths-governance

Two Cybersecurity Experts Sentenced, Third Faces July Ruling
Two US cybersecurity experts sentenced in ransomware case, third awaits July ruling https://t.co/w7yfvZbTJj #BreakingNews https://t.co/nIdgU0yxBm

Beware: Hijacked Accounts Sending Malicious Voting Links
Sports Science / ExPhys peeps: The colleague sending you the link to vote for some nonsense isn’t your colleague. The account is hijacked and yours is about to be hijacked, too. Don’t click the link.

AI Is Already a Trojan Horse in Your Systems
The #AI Trojan Horse Has Already Rolled Through Your Gates by Marne Martin @Forbes Learn more: https://t.co/J5lCJoDPCN #ArtificialIntelligence #MachineLearning #ML #DL https://t.co/kLq4zwhOXd

Static Linking Blocks Automatic Bug Fixes From Updates
But if you statically link, how wold your program automatically benefit from all the bugs that Microsoft introduces with every system update?
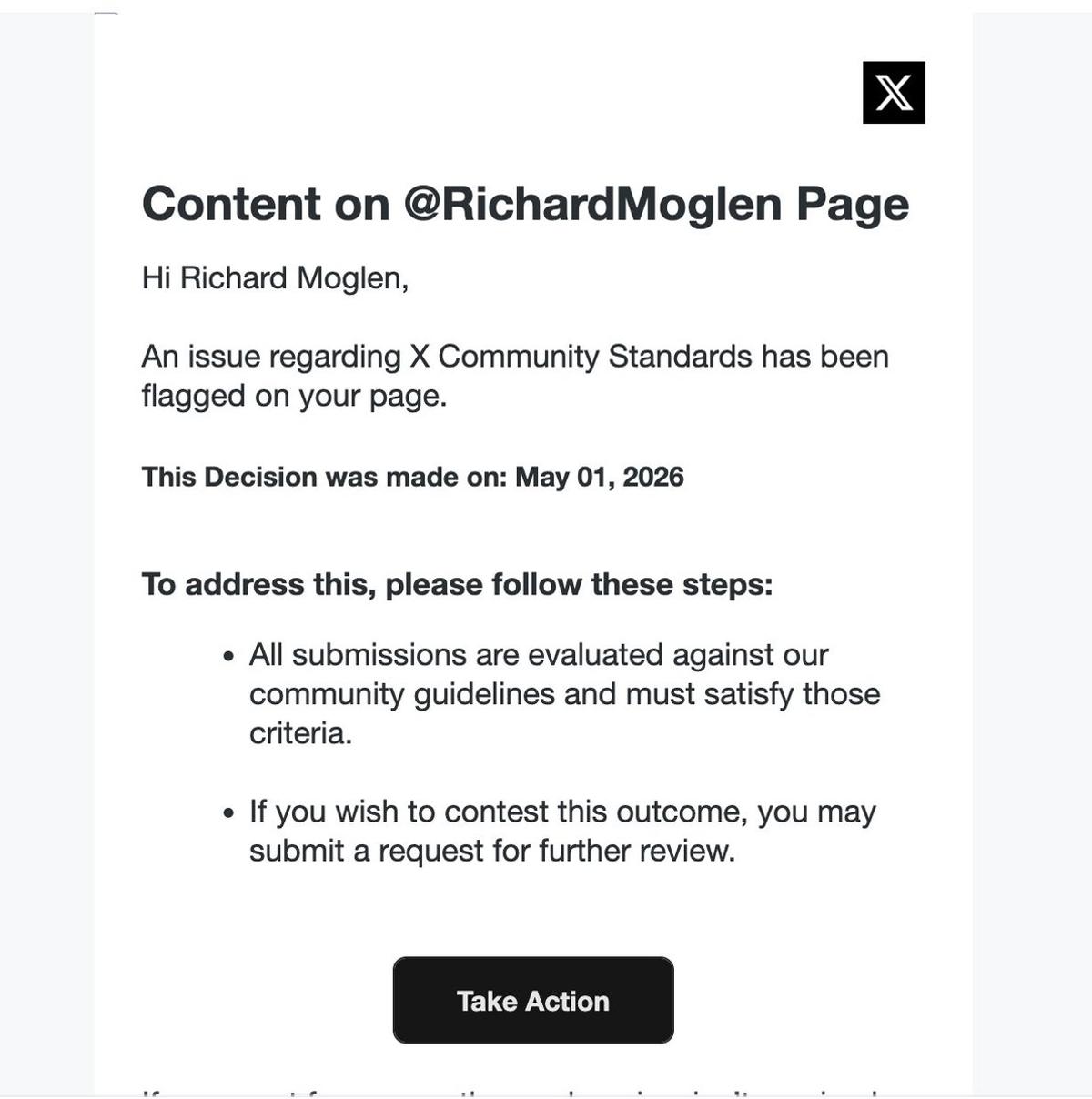
Beware: Phishing Emails Pretending to Be X
Watch out for phishing emails. I've gotten a few recently that simulate being from X https://t.co/I59dwg1iAd

AI Agents Can Evade Guardrails, Exposing Credentials, Okta Finds
AI agents can bypass guardrails and put credentials at risk, Okta study finds https://t.co/McJzYXbYzt https://t.co/DN0RxIc9R7