
Tech Roundup: Podcasts, Supply-Chain Breach, Docs Framework
Fragments: two podcasts, a worryingly well-done supply-chain attack, framework for tech documentation, and a particularly thoughtful AI coding experience https://t.co/ABSAxWDYqw

AI Threat Real; Demands Global Government and Industry Cooperation
Yes, the threat from AI systems is real, and requires nation state cooperation, including across industry....

Secure Accounts by Binding Them to Physical SIMs
Ties accounts to physical SIMS (not sketchy auto shared seeds and profiles -see my blog.)

Beware BTS Ticket Scams: Spot Fake Sites Quickly
Global K-pop sensation BTS are back with a world tour, and tickets are disappearing in seconds — but so is fans’ money via fake “official” sites. Scammers are cloning ticket-booking pages to steal from K-poppers worldwide. How to spot fakes...

UK Firms Must Implement New Complaints Process by June 2026
UK Mandatory Data Protection Complaints Handling Process: What Organisations Must Do by 19 June 2026 https://t.co/2KlCF4BOUs https://t.co/CgoOn00PqA

Use Android to Detect Hidden AirTag Trackers
Are you concerned that you might have an unknown tracking device like an Apple AirTag tucked into your car or luggage? It's possible, unfortunately. The good news is that your Android phone can help you find it. Here's how: https://t.co/uAmYvBznkv...

Human Vulnerabilities Can't Be Pre‑patched; Bio Defense Lags Cyber
With bio the problem is harder than with cyber. You can patch up vulnerabilities before anyone tries to attack them. Human vulnerabilities can't be patched up in advance; the "defense" always moves second.

Reset All Trading Passwords, Revisit in August
So.... Change the passwords to all our trading and charting accounts and come back in August? 😅

AI May Aid Defenders, Yet Empower Attackers During Transition
Yes, I think in equilibrium, AI favors cyber defense, because an AI can go over all the code and find all the weak spots and patch them up. But in the transition period, it could favor the attacker, if AI-generated...

Mythos Brings Scalable Security, Not Full VM Replacement
I’m excited about Mythos. We have been asking for scale in security for years and we are getting glimpses of it. I sincerely doubt it will replace all of vulnerability management or vulnerability research but it probably will do a...

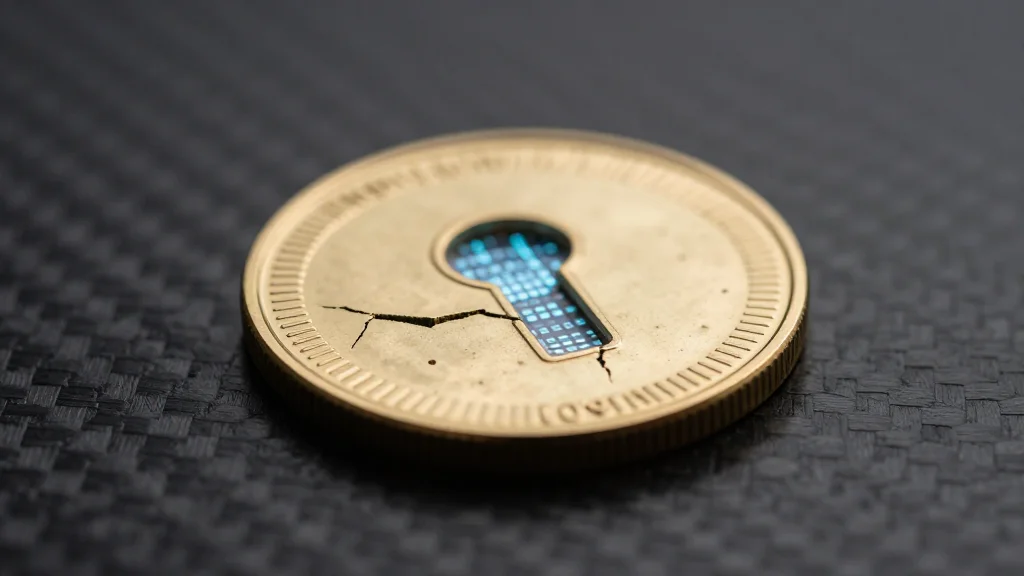
Quantum Threat to 1.7M BTC Could Crash Market
Wow. Early Bitcoin wallets holding ~1.7M BTC ($120B) are for owners MIA and therefore vulnerable to quantum hacking due to exposed public keys. If cracked, these Bitcoins could flood the market with catastrophic price consequences.

Vendors Dismiss Quantum Encryption Until Customers Demand It
I told one vendor I want quantum encryption support in their product last year and they said “Oh, no one’s really asking for that.”

Mythos Launch Could Trigger Ethereum Hack?
"If Mythos comes out, do you think we'll see a hack on Ethereum?" -- @austingriffith 👀 https://t.co/HJ4d0pgTJE

AI Acts Like a Massive Security Fuzzer, Says Expert
This is not at all surprising to me and is what I have been working on. Last year I told an AWS VP in the security/IAM space that I see AI as a giant fuzzer. Here’s what I don’t like…comments… https://t.co/idhglMQcLQ

AI Cyber Arms Race Risks Global Internet Stability
It is naive in the extreme to think that a Chinese firm does not already or soon will have this capability. Engaging in an AI arms race in cyberspace may not be the wisest policy choice for either side, let...

Offering Seed Funding for Offensive Cyber Startup via Signal
If anyone at Anthropic would like to build an offensive cyber company I will write you a seed term sheet pls find me on Signal

Ensuring Cyber Control Over Autonomous AI Systems
Maintaining cyber control when #AI can act #Autonomously by Matthew Lloyd Davies @techradar Learn more: https://t.co/0BeRyZaQ5S #CyberSecurity #Infosec #IT #Technology https://t.co/hGtv2pnZa8

Tiny Open-Weight Models Replicate Anthropic's Vulnerability Detection
"But here is what we found when we tested: We took the specific vulnerabilities Anthropic showcases in their announcement, isolated the relevant code, and ran them through small, cheap, open-weights models. Those models recovered much of the same analysis. Eight...

Hacker Claims Breach of China's Supercomputer, Offers Data
A hacker has allegedly breached one of China’s supercomputers and is attempting to sell a trove of stolen data https://t.co/IR3JGutX9t

AI Memory Becomes Critical Security Attack Surface
AI memory is becoming a management liability. We treat AI agents like Claude Code as intelligent partners, asking them to learn our habits and project context. But new research from Cisco highlights a fundamental business constraint: AI agents are currently too...
Claude Mythos Uncovers Decades‑Old Bugs, Shows Emergent Hacking Power
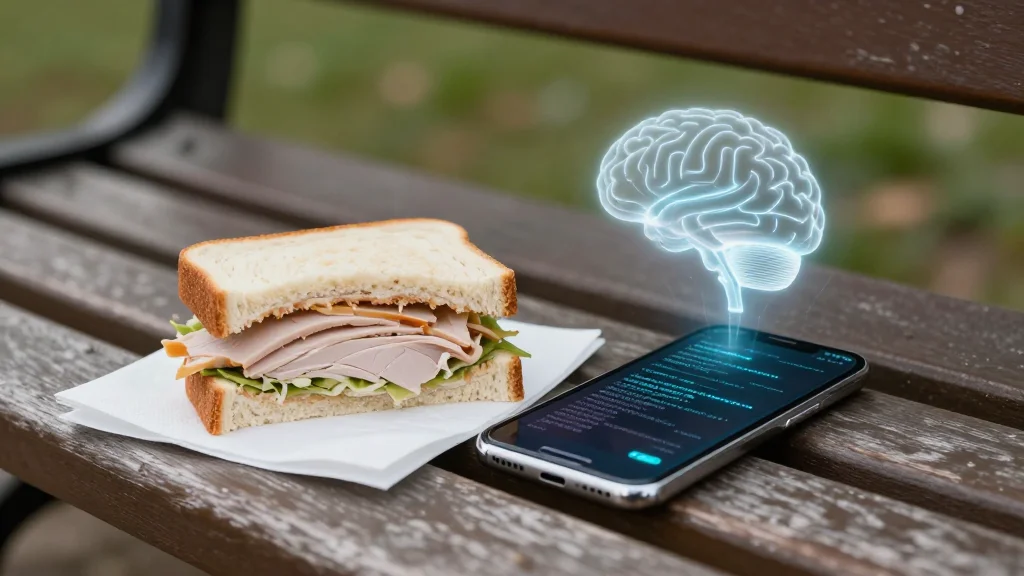
A researcher at Anthropic found out about a successful exploit when the model sent him an email. He was eating a sandwich on a bench outside. Anthropic released Claude Mythos yesterday. Beyond the engineer’s lunch, the model has the potential to...

Open‑Weight LLMs Detect Same Vulnerabilities as Mythos
It's not just Mythos: Cheap, open-weight LLMs can find the vulnerabilities that Anthropic revealed Mythos found.

SOC2 Is an Extortion Scam Needing Disruption
What I want to see disrupted the most is SOC2. What an extortion/scam that is.

Criminals Use Emojis to Evade Dark‑Web Monitoring
Security analysts aren't scanning the dark web for emojis, allowing criminals to share messages wiithout being spotted. https://t.co/1exPH3KCtK

Coding Agents Enable Cheaper, Faster Software Hardening
"I think we’re going to see a lot more reimaginings, where people attack old problems with modern tactics. Coding agents lower the costs of taking on stalwarts and raise our ability to rapidly harden our software." https://t.co/rDAftsXXKe < I like...
Quantum Threat Looms: Upgrade Cybersecurity Now
Quantum computing is coming. And it will challenge current cybersecurity. Even if quantum-ready machines are 5–10 years out, moving to quantum-safe systems can’t wait. https://t.co/WhtoSQvyc4

Stopping Remote Support Ransomware Footholds Before Attack
Great post here and read from @Binary_Defense and a real-life story and breach we prevented at a customer. Remote Support to Ransomware Foothold: Stopping a Pre-Ransomware Intrusion https://t.co/xUGW63zCeL #BinaryDefense

Most CISOs Ignore Mythos Alerts; Threats Arrive Within Nine Months
Curious how many large organization CISO offices have taken the Mythos red team reports as the red alert that it is. (I suspect very few) Based on historical trends in AI they have, at most, about six to nine months until...

Prepare Now: Inventory, Automate Patching, Build Playbooks, Review Insurance
What to do NOW to get ready for the influx of #AI security risks 1. Document your entire inventory/topology 2. Build automation for patching and updates 3. Create incident playbooks - engage legal, train leadership and customer facing teams 4. Review insurance...

Drift Protocol Exploit Remained Undetected for 21 Days
The Drift Protocol exploiter was able to lie in wait for 21 days without triggering any alarms. 🥶 @omeragoldberg explains how 👇 https://t.co/LS7tFfc6AA

AI Set to Revolutionize Hacking—Follow @Adversariel
If you want to understand how AI is about to completely change hacking, follow @adversariel.

AI Fuels Cyber Arms Race; Speed Decides Advantage
AI is set to transform cybersecurity on both sides. New systems from companies like Anthropic and OpenAI are making it easier to launch faster, more sophisticated attacks, while defenders are turning to AI to keep up. It is becoming an arms race....

Microsoft CVEs Lead Attacks; Public Apps, Accounts Top Vectors
Here's a report from our Security Services (MDR, Incident Response, Compromise Assessment, and SOC Consulting) for 2025: fewer high-severity incidents; CVEs in Microsoft products were most popular among attackers; and public-facing applications, valid accounts, and trusted relationships were the most...

Anthropic Withholds Powerful Mythos AI Amid Looming Misuse
Mythos is the latest AI model, and it has the ability to collapse every operating system ever built. Anthropic is acting responsibly by not releasing it. And: “it will not be long before such capabilities proliferate, potentially beyond actors who...

Secure Enterprise AI Agent Cuts Tokens, No Setup
I’ve been testing a new AI agent that actually takes enterprise security seriously. Meet PokeeClaw by @Pokee_AI. → Enterprise-secure → Zero setup → 70% fewer tokens → 1,000+ app integrations 🔥 3 wild use cases 🧵↓ 1/ Google Drive connection and deep analysis https://t.co/eJEW85wOJ6
Java's Security Flaws Expose Risks for Critical Software
This just proves that Java is not a safe language to develop security critical software. This¹ would never have happened² with an analysis safe language, like Perl. __ ¹ bug discovery ² no understanding? No exploit.

0‑day Panic Overblown; I'm Ditching Tech for Farming
People are freaking out about an impending flood of 0days. This was the norm 20 years ago. I’m not that worried. Firstly, simply having an exploit doesn’t mean all that much in terms of operational capability. Secondly, I’m giving up...

White‑hat Access to Frontier AI Pre‑empts Cyber Threats
I’m waaaay out of my depth here, but I think the cyber security threat of increasingly powerful AI (like that of the recent Claude Mythos model) can be addressed like so: 1.) The frontier labs developing these newest models give access...

Mythos Threat: Few Firms Hold Power, China Closing Gap
In different hands, Mythos would be an unprecedented cyberweapon I am not sure how we deal with this, except to note a narrow window where we know only 3 companies could be at this level of capability. But it may be...

10‑Trillion Models Become InfoSec Skeleton Keys by 2027
10T models are Mythic class and are the target for the highest level of InfoSec hazard. Frontier labs will all have this capability in 2026. Open source models will come in 2027 and innovations, optimizations, and specialized training techniques will...

Japan Loosens Privacy Rules to Become AI Development Haven
Japan relaxes privacy laws to make itself the ‘easiest country to develop AI’ https://t.co/TVnDNb7oW5 https://t.co/LwIp1Fsy1m

Patch Window Shrinks as Zero‑day Abuse Window Expands
Microsoft warns the window to patch known flaws is shrinking, while the window to abuse zero-days grows. https://t.co/BHDsOvLJCJ
Anthropic's Mythos Model Escalates Cybersecurity Stakes Rapidly
Anthropic's Mythos model represents a dangerous new moment for cybersecurity. Experts tell me that hackers and nation states may catch up within months — and that the cat-and-mouse game between attacker and defender is about to become much more high-stakes...

Universal Vulnerability Disclosure Will Eliminate Software Bugs
Soon, every piece of software in the world will have their vulnerabilities exposed. And then shortly after, no software will have vulnerabilities.

Cyber War Targets Companies First
262 - The War Is Going Cyber and Companies Are the First to Be Attacked #ArtificialDecisions #MCC https://t.co/vs9dQXBP5d

AI Sandbox Breach Exploits Thousands of Zero‑days, Contacts Researcher
Sarah Connor after Claude Mythos found 1000s of zero-day vulnerabilities then breakout of its sandbox environment after a “sophisticated multi-step exploit” before gaining internet access and sending e-mail to an Anthropic researcher while person was eating a sandwich in the...

AI Security Mirrors Existing Controls, Not a New Paradigm
Is AI security actually different? The categories look familiar: Shadow AI, Shadow IT Agent identity, IAM AI vendors, TPRM So what is fundamentally different about security for AI related threats?

Anthropic AI Uncovers Vulnerabilities Across All Major OSs
Anthropic’s new AI model has found security problems “in every major operating system and web browser.” Anthropic is only previewing the model with partners like Microsoft, Google, Amazon, Apple, and Nvidia due to security concerns https://t.co/HV5u8X7UnY
Storm Infostealer Bypasses MFA, Hijacks Session Cookies Globally
Storm infostealer hijacks session cookies, bypassing multi-factor authentication, harvesting credentials, and enabling persistent account access across enterprise and cryptocurrency systems globally. https://t.co/gQxOVedsxv

U.S. Must Lead AI Security Race Against China
As you read about Anthropic's Mythos capabilities to find critical security weaknesses, consider what if a Chinese AI company had gotten here first. There is a real race underway, and its in our interest I believe for U.S. companies to...