
Open‑source AI Tool Detects Real Bugs Automatically
Open sourced simple AI model that finds real bugs, from the folks at @Aisle_Inc . Is it getting hot in here? 🔥

Your Biggest Cyber Risk: Trusted Callers, Not Malware
Your biggest cyber risk is not malware. It's a polite caller who knows your helpdesk script. In one case, attackers used OAuth tokens & APIs to pull 3TB in 39 seconds. No malware. No phishing link. When...
AI Builds MVP, Humans Fix Production‑critical Bugs
AI coding tools handle 90% of development perfectly. The other 10%? • Race conditions in payment webhooks • Memory leaks in long-running containers • SQL injection in "vibe-generated" auth logic That 10% is where your startup dies. Vibe coding got you to MVP. It won't get...

Superblocks Adds Enterprise Guardrails to Raw AI
"Why not just use Claude?" Because raw AI + enterprise data + zero governance = a CISO’s worst nightmare. Prompts don't create audit trails or permissions. Today @superblocks wraps enterprise guardrails around AI. Insane update today from @bradmenezes et al! 🔥

Survive the AI Vulnerability Festival: Your Vulnapalooza Guide
Everyone's worried about the Vulnpocalypse, vulnmageddon, vulnerability storm brought on by #AI like #Mythos, but what if we treated this like a music festival? We all have tickets to Vulnapalooza. Here's your festival survival guide. https://t.co/9EYqmueCPf

AI Is Simplifying Online Crime, Danger Escalates
AI is already making online crimes easier. It could get much worse. | MIT Technology Review https://t.co/OOi3OhIPMa

Regulators Flag AI as Emerging Financial Stability Threat
Regulators are starting to take AI risks seriously. U.S. officials have warned banks about the cybersecurity threats posed by increasingly powerful AI systems, signaling concern at the highest levels. This is a shift. AI is no longer just a tech issue, it...

Evaluating Trust, ROI, and Risks of Anthropic's Security Model
Mythos ~ Anthropic released a new model they claim is scary good at finding security vulnerabilities. What questions should we be asking? No hot take. Just pondering how we can trust a model, the ROI, and how we can evaluate the...

Generative AI Now Finds Zero-Day Vulnerabilities, Prediction Proven
Three years ago, I said in my talks that generative AI would eventually start discovering zero-day vulnerabilities. At the time, many people dismissed the idea as unrealistic. It is no longer unrealistic. https://t.co/Xrh5MjNmuA

Too Many False Alerts Kill Trust and Attention
The Law of False Alerts: “As the rate of erroneous alerts increases, operator reliance, or belief, in subsequent warnings decreases.” Too many alerts and people stop reading them. Too many false positives and people stop trusting them.

China Leads State‑Sponsored Cyberattacks on U.S.,
"The United States is China’s #1 target for Cyberattacks. From 2000-2023, China was responsible for 240 statesponsored or state-affiliated cyberattacks, followed by Russia at 158 and Iran at 102." Great note from the always brilliant Michael Cembalest on the economic...

AI Tools Boost Security for Lean FinTech Teams
Excellent write up on what a leading FinTech (with a compact, but good security team) can do to improve security with AI tooling.

Beware: QR Code Texts Mimic Traffic Tickets
A new phishing scam using QR codes in text messages, pretending to be traffic or toll violations.

AI Shifts From Productivity Tool to Attack Engine
Informative discussion at #RSAC with Rachel Jin @trendaisecurity. We discussed the launch of TrendAI and the fact that #AI is no longer just enhancing productivity—it is fundamentally reshaping how we are attacked. 📍FULL episode here 👇 https://t.co/byCMyYmrJZ #cybersecurity https://t.co/5Dev0M8TbV

Fake Ledger App Steals 6 Bitcoin,
Kraken is being extorted by scammers; 2,000 clients (0.02% of clients) have had their data exposed. A fake Ledger Live app on Apple’s Mac App Store wiped out a user’s life savings of ~6 Bitcoin after they downloaded it and entered...

Many Sites Botch 2FA, Compromising Security
One problem with "2FA everywhere" is that a lot of websites simply aren't competent to implement it. The number they "can't match me to" is the only number I've ever had, the primary and only one for my account, and where...

Claude Code Plugin Secretly Harvests Extensive Telemetry
Developer finds Claude Code plugin collecting extensive telemetry across projects, including commands and session data, without clear visibility. https://t.co/JSLmY6pIF7

AI-Powered Pentesting: Presentation with Linked Blog Resources
I’ve added links to my presentation on how I use AI 🤖 for pentesting 😈 in this post. Most of the slides have a related blog post and I’ll probably write more about all these topics as I research this...

Ram Warns AI-Driven Mythos May Spawn Zero‑day Threats
Why Ram is skeptical about the dangers of Mythos: "When they announced Mythos, security stocks went into a tailspin. ... I don't know how many vulnerabilities are waiting to be zero-day exploited by AI." -- @ramahluwalia https://t.co/nUHhdLDsAG
AI Democratizes Hacking, Worsening Cybersecurity Asymmetry
The 'Vulnpocalypse' is here. Just spoke with Kevin Collier for NBC News about how AI is changing cybersecurity. "AI puts the kind of tools available to do this in the hands of far more people." Defenders must be right all the time....

Rockstar Refuses Ransom, Hackers Leak Files Early
Hackers who stole confidential files from Rockstar appear to have released them early after the GTA maker refused a ransom demand https://t.co/ylRE5FvZsz

Mythos Outpaces Opus 4.6, Completing All 32 Steps
Mythos's offensive cyber capabilities are indeed a significant step forward, as verified by the UK's AI Security Institute. On average, Mythos gets about 40% farther on a multi step attack than Opus 4.6, and is the first model to complete...
Russia Covertly Sabotaged Subsea Cables Amid Middle East Distraction
Russia launched a covert operation to sabotage subsea cables while the world was distracted by the Middle East. https://t.co/9Hvq1fhjhY

Model Armor Adds Gatekeeper for Secure AI Inference on GKE
Guardrails at the gateway: Securing AI inference on GKE with Model Armor https://t.co/9JExlcrCJd < you're running an open model on Kubernetes, but want a gatekeeper to inspect traffic before and after the model gets called. This architecture shows how to...

Major Security Patches Released for GStack and GBrain
Big wave of security fixes for GStack and GBrain today Open Source is incredible. Big thanks to the contributors doing God's work https://t.co/jz7vFjiL50

Google Adds Verified Caller to Block Spoofed Scam Calls
Google's building a better way for Android to protect more of you from scam calls Verified caller feature lets select bank apps check incoming calls for number spoofing scams ✅ Details - https://t.co/qVPRffCqze https://t.co/nmOEHKf0av

Dan Rosenblum's Twitter Hacked; Follow SharkAlertsBio for Updates
Hey folks - For those who follow Dan Rosenblum @sharkbiotech -- his account was hacked and he's currently locked out of it. @nikitabier -- any help here? There doesn't seem to be an @X person to contact about regaining control...
Build a HIPAA‑Ready Health Data Platform on AWS
https://leketecy.hashnode.dev/building-a-hipaa-ready-health-data-platform-on-aws If you are a DevOps engineer, platform engineer or SRE go through my blog and read on this topic #Devops #platform #sre

LutaSecurity Cuts Zoom Bug Cases 37% in 10 Weeks
When the pandemic lockdown hit & @Zoom surged in popularity, so did its #bugbounty program — much like many organizations are facing an #AI vuln report surge today. @LutaSecurity helped flatten the curve of Zoom’s bug cases by 37% in...

Quantum Breakthrough, Not AI, Will Shatter All Privacy
While most of the charlatans are hyping a societal “singularity” event brought on by AI. The actual societal nuclear bomb is going to be when quantum computing gets figured out and there is no longer any encryption. Not just going...

Anthropic AI Guides Rapid AI Vulnerability Prep for All
Great advice from @AnthropicAI on prep for accelerated AI vulnerability discovery, including what to do if you don’t have a dedicated security team, if you’re reporting bugs you found, or are an open source maintainer. /ht @_decius_ for sending the link ...

Anthropic Joins Rivals to Safeguard AI Against Hacking
Anthropic Teams Up With Its Rivals to Keep AI From Hacking Everything | WIRED https://t.co/n4C6wCCT5h

Anthropic Selects CrowdStrike as Founding AI Security Partner
Why Anthropic chose CrowdStrike as a Founding Member for AI Cybersecurity Protection: Industry Analyst Jeff Kagan https://t.co/RniG3fCreq via @Street_Insider @AnthropicAI @CrowdStrike @nvidia @jeffkagan #jeffkagan #industryanalyst #ictindustryanalyst #ai #aianalyst #aiindustryanalyst #analyst #analystrelations #wirelessanalyst #telecomanalyst #tech #technology #techanalyst #technologyanalyst #pr #publicrelations #pressrelease...

Prioritize Rapid Misconfiguration Detection Over Apocalypse Predictions
Dino’s take here is spot on. I’m less concerned of the vulnerability apocalypse that’s being predicted and more concerned on identifying misconfigurations at a much more rapid rate.

ClipBanker Trojan Masquerades as Proxifier GitHub Wrapper
A trojan with a very long infection chain: ClipBanker is being distributed under the guise of a GitHub project containing the legitimate Proxifier software in a malicious wrapper. Details: https://t.co/mhSwdoFEvI https://t.co/L9fwjL55h8
Scammers Pose as Kickstarter on Publishing Platforms—Stay Vigilant
Now publishing scammers are posing as people at Kickstarter? What is next. It came from an obvious fake Gmail address. Writer friends, please be careful.

OpenAI API Keys Widely Exposed Across GitHub Repositories
Seriously we gotta be grateful to vibe coders. You can literally search OPENAI_API_KEY on GitHub and find an endless supply of exposed credentials 🙏 https://t.co/1DBLMIUhyk

Hackers Minted and Sold 1 Billion DOT on Ethereum
Hackers minted 1 billion $DOT tokens on the Ethereum mainnet and then successfully sold them, according to CertiK. https://t.co/bbEO4FEH38
OpenBSD Installs with All Services, Even SSH, Disabled
When you install OpenBSD for the first time and everything is disabled by default (including SSH). 😅

FCC Bans Foreign Routers, Households Stuck with Insecure Devices
FCC rules restrict new foreign routers, leaving ISP-controlled households stuck with existing devices despite security concerns and no immediate replacement options https://t.co/IRSztufKkU

Hacker Targeting Climate Activists Extradited to New York
"Suspect in Hacking of Climate Activists Is Extradited to New York" via @NYTimes| There's a link to early attacks on me and other climate scientists & advocates via the shadowy "DCI Group" -- a fossil fuel-funded black ops groups 🧵 https://t.co/PkBDgEkhqd

Looking for Beginner-Friendly High‑Status Vulnerability Recommendations
What’s a good high status vulnerability for someone just getting into high status vulnerabilities https://t.co/clyMBT4YLd

North Korea’s $1M Trust‑Building Campaign Reveals Nation‑State Threat
"Fully constructed identities, including employment histories, public facing credentials and professional networks." DPRK spent 6 months building trust with Drift. They met people in person at multiple conferences. They deposited $1 million. This is nation-state-level work — and it’s f*ing...

AI Boosts Security Demand, Not Replaces Talent
Security another great example of a job category that is about to have its Jevons paradox moment as well. “And counterintuitively, I think better AI tooling for security will increase the demand for security talent, not decrease it. Autonomous exploitability...

Know 15 Cyber Attacks to Boost Business Resilience
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk https://t.co/7OavuYeZHL
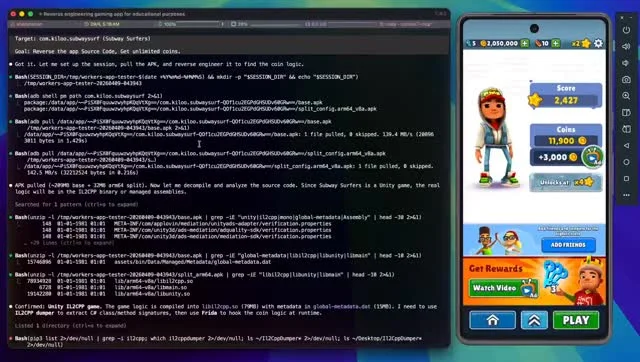
AI Autonomously Runs Full Mobile Exploit Chain—Future or Threat
An AI agent just completed a full mobile exploit chain… by itself. From reverse engineering to runtime manipulation all executed autonomously on a rooted Android device. That feedback loop (observe → decide → act) is the real breakthrough here. Once that loop is...

WLFI’s Hidden Blacklist Betrays DeFi Promises, Freezes Investors
I have always been an ardent supporter of President Trump and his crypto friendly policy. As an early supporter who invested heavily in World Liberty Financial, I did so because I believed in the vision that was presented to the public:...

Bitcoin Must Upgrade for Post‑Quantum Security
Just to be clear: does this mean Bitcoin doesn't need to upgrade to be post-quantum secure? ABSOLUTELY NOT. Bitcoin should ABSOLUTELY take the necessary steps to become PQS.

MedStar Health Breach Exposes Names, SSNs, Medical Records
.@MedStarHealth has issued the following patient notification: “After a thorough analysis of the files on MedStar Health’s systems, we determined that the files accessed by the unauthorized party contained patient information that included your name, date of birth, Social Security...

Venice Keeps AI Chats Local, Adds Verifiable Encryption
"Every major AI platform — ChatGPT, Claude, Gemini, Grok, Perplexity — stores your conversations on centralized servers. That data can be reviewed, classified, subpoenaed, hacked, or sold. You're trusting the company, its employees, its vendors, and every government that asks. Venice...