
Curating Secure Software: The Art of Selecting Safe Dependencies - Kadi McKean, ReversingLabs
Kadi (Katie) McKean, open source manager at ReversingLabs, framed selecting third-party dependencies as a curatorial process — start with clear requirements, assess acquisition and UX (how the code will be used), and evaluate impact. She warned that modern software is overwhelmingly composed of borrowed code and highlighted recent supply‑chain incidents (notably the Light LLM compromise that traversed npm to PyPI and infected CI pipelines) as examples of how malicious packages can exfiltrate secrets and propagate across ecosystems. McKean urged practitioners to go beyond CVE checks to consider tampering, provenance, signatures, secret exposure, and the risks posed by deep transitive dependency chains. She compared reputational and cultural fallout from compromised projects to the historical Isabella Stewart Gardner art heist to stress long‑term trust implications for maintainers and organizations.
From SBOMs To Decisions: Prioritizing Supply Chain Risk in Time-Bound M&A... Prashanth Chandrasekar
The presentation by Prashanth Chandrasekar of Bitsight focuses on how software bill of materials (SBOMs) can be transformed from a static inventory into a decision‑making tool for mergers and acquisitions (M&A). He stresses that M&A due diligence operates under a...
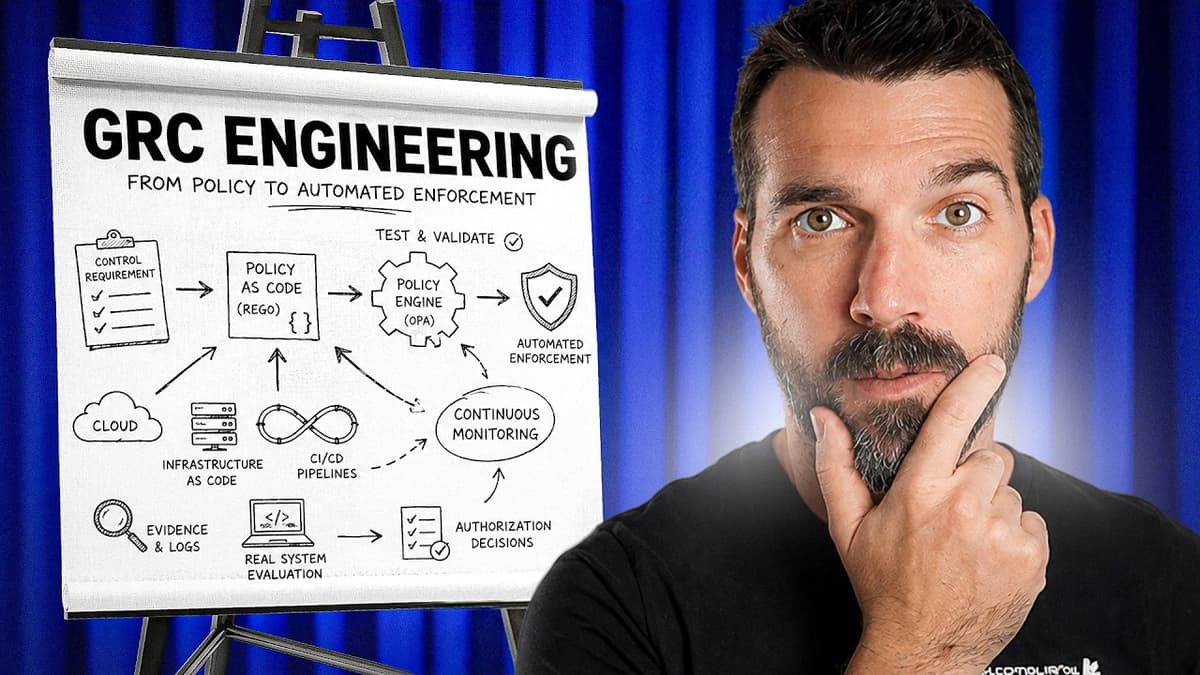
GRC Analysts Will Get Left Behind Without This Skill
The video introduces GRC engineering as an emerging discipline and highlights the free GRC Playground as a hands‑on, browser‑based learning platform for analysts seeking to acquire practical policy‑as‑code skills. It explains how traditional GRC relies on manual documentation, while GRC engineering...

CHINA CHALLENGE: Booz Allen CEO Sounds Alarm on AI Adoption Risks
The video features Booz Allen Hamilton CEO Horacio Rozanski warning that rapid AI adoption carries national‑security risks, especially when Chinese‑developed large language models (LLMs) are used in U.S. applications. Rozanski’s team found that Chinese LLMs produce significantly more vulnerable code...
Gemara: The GRC Architecture You Didn’t Know You Built - Hannah Braswell & Jennifer Power, Red Hat
Red Hat engineers Hannah Braswell and Jennifer Power outlined Jamara, an OpenSSF Orbit–stewarded sandbox for an OSI-inspired, seven-layer GRC engineering model that decouples compliance definitions from measurements to enable end-to-end automation. The model separates definition layers (guidance, technical controls, organizational...

Taking the Temperature of Tech Policy Debates in Brussels at CPDP
At the 19th CPDP conference in Brussels, policymakers, academics, industry and civil-society voices clashed over competing visions for Europe’s digital future, centering on the EU’s ‘digital omnibus’ simplification package, tech sovereignty, and child-safety rules. Debate focused on whether omnibus measures...
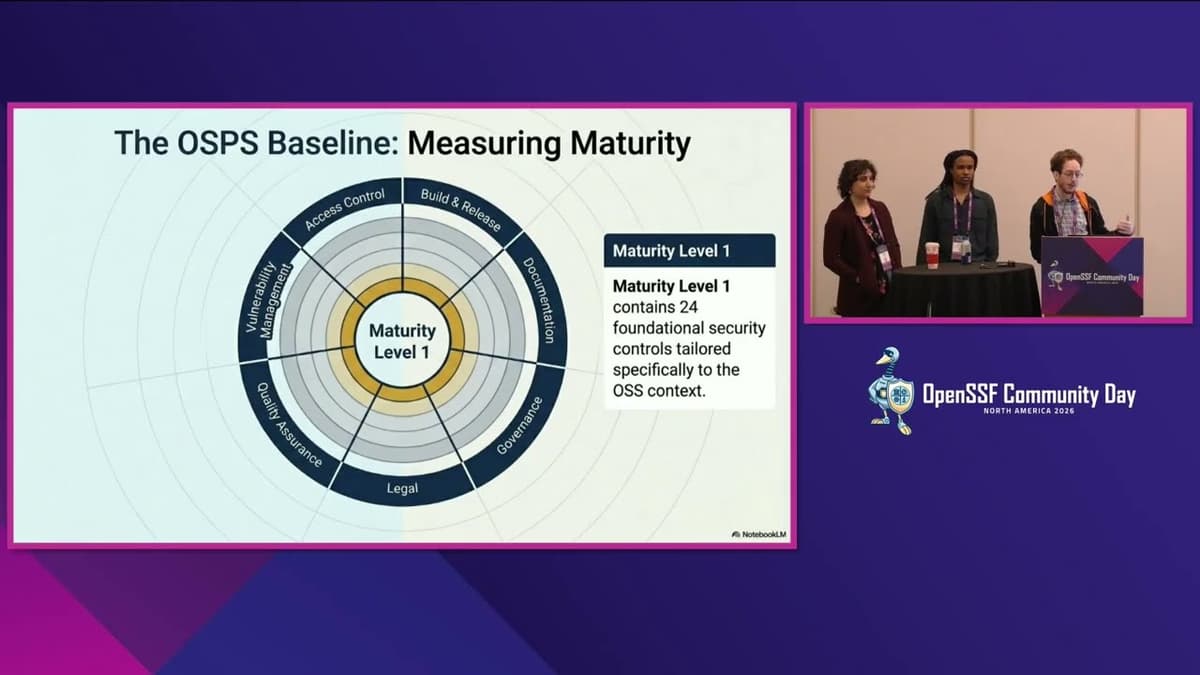
OpenSSF Baseline Alignment in Open Source Repos: Autom... Will Sergeant, Kiran Chana & Kavoi Mutisya
Researchers from Harvard developed a mixed-methods approach—an open-source Python tool plus maintainer questionnaires—to measure OpenSSF Baseline maturity level 1 alignment across 21 Linux Foundation repositories mirrored on GitHub. Automated, unauthenticated scans and follow-up surveys found high overall compliance with level‑1...
The Architecture of Accountability: Transparency in Software - Hayden Blauzvern, Google
Hayden Blauzvern, a Google software engineer, framed transparency in software around two core principles: discoverability and auditability. He introduced a claimant model—claimant, claim, verifier, arbiter, and believer—stressing falsifiability and signed statements as prerequisites for reliable transparency. Using examples such as...

HackTheBox - Interpreter
The video walks through the HackTheBox "Interpreter" machine, beginning with an nmap scan that reveals SSH, HTTP, and HTTPS services on a Debian host. By inspecting the web application’s JNLP file, the presenter identifies Mirth Connect 4.4.0 and locates CVE‑2023‑43208,...

Anatomy of a Phishing Campaign - Mike Fiedler, Python Software Foundation
Mike Fiedler of the Python Software Foundation walked the audience through a recent phishing campaign that targeted PyPI maintainers, illustrating how attackers spoofed official PyPI communications with a single‑character URL alteration and a man‑in‑the‑middle proxy to harvest credentials. The talk highlighted...

BOE's Bailey: UK Banks Still Don’t Have Access to Mythos
Bank of England Governor Andrew Bailey said UK banks currently do not have access to Anthropic’s Mythos, underlining concerns about reliance on US-owned AI providers and the cross-border spillovers of cyber and operational risk. Bailey stressed the need for a...

Securing the Agentic Future: How OpenSSF Is Leading AI Security
The Open Source Security Foundation (OpenSSF) announced a strategic push into AI security, reaffirming its core mission to protect open‑source software. The foundation operates around four pillars—programs and projects, community building, targeted education, and policy advocacy—and is now extending each...
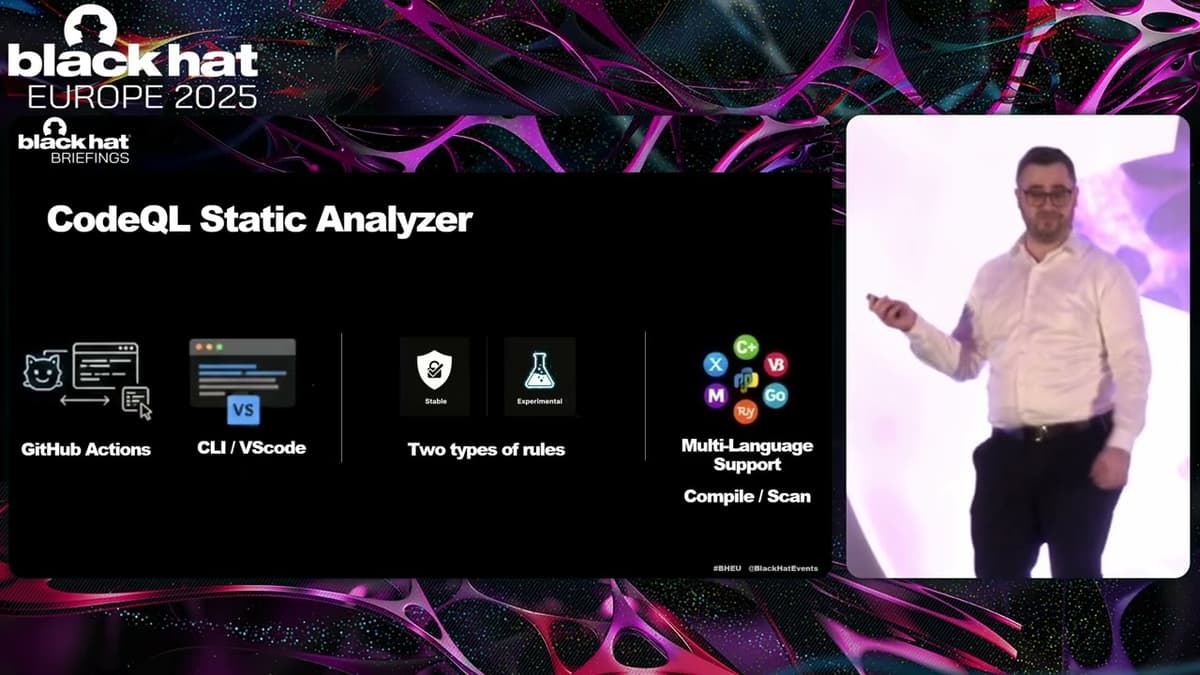
Black Hat Europe 2025 | Flaw And Order: Finding The Needle In The Haystack Of CodeQL Using LLMs
At Black Hat Europe 2025, Simha Cosman of CyberArk Labs presented a novel method for finding software flaws by pairing CodeQL static analysis with large language models (LLMs). He argued that the hype around LLM‑only vulnerability scans is misplaced, as...
New Warning on Fake Party Invites
Recipients across the U.S. are being targeted by phishing scams that mimic digital invitation services like Paperless Post, Evite and Punchbowl. Victims report clicking invites that prompt fake login or multi-factor authentication pages, then seeing the bogus invite propagate to...

A Former Spy Shares HR's Critical Role in Workplace Security
In this episode of People and Strategy, former Defense Intelligence Agency officer Shaunie Delaney explains why human‑resource functions are now the front line of workplace security. Drawing on her clandestine background and consulting work at firms like Uber, she argues...