
Hardened Containers for the AI Era: Reducing Vulnerability Risk
At the OpenSource Summit, Ada and Minimus announced an alliance to combine Minimus’s rapid package-patching and rebuild capabilities with Ada’s hardened runtime and microVM isolation to deliver “hardened containers” for production. The partnership aims to close the growing patch gap amplified by AI-driven vulnerability discovery (e.g., Mythos), addressing both disclosed and undisclosed exploits, including high-impact kernel privilege escalations. Speakers stressed that AI has accelerated exploit discovery and patch timelines, making fast rebuilds plus runtime hardening essential for environments that cannot update instantly. The offering is pitched especially at regulated and high-risk sectors, such as financial institutions, that need trusted, resilient production runtimes.

Behind the Scenes of an Operation Targeting Online Scammers | BBC News
BBC News followed a joint police and bank-led operation targeting the criminal ecosystem that enables online romance and banking fraud, including sellers of stolen financial data, technical support and training for scammers. Early-morning raids in South London and coordinated arrests...
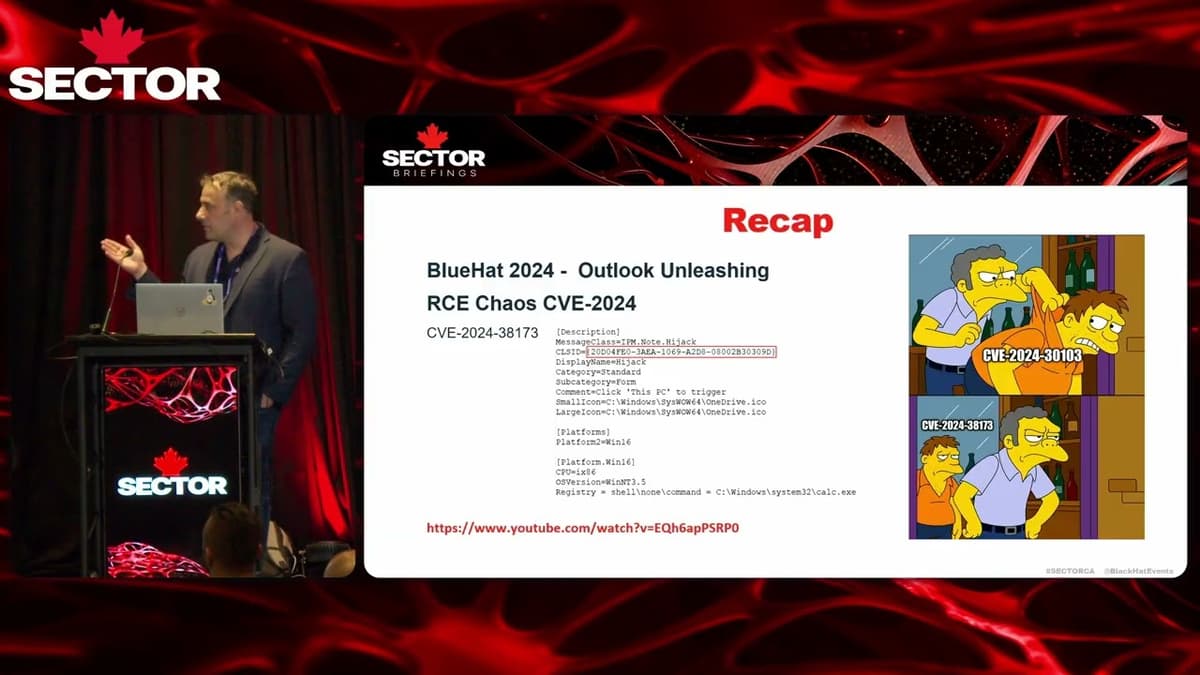
SecTor 2025 | Signature of Destruction: Outlook RCE Strikes Again
The SecTor 2025 talk by Michael Berik of Morphoscans focused on a new attack chain that leverages Outlook’s roaming signature feature to achieve remote code execution (RCE) without any user clicks. Berik recapped earlier Exchange‑based form‑injection bugs, COM‑object hijacking, and a...

Will Quantum Computers Destroy the Internet? | DW News
Researchers and tech companies warn that by as early as 2029—an event dubbed “Qday”—quantum computers could become powerful enough to break the public-key encryption that underpins the internet. That would expose national security systems, critical infrastructure, financial networks and personal...

The Trust Problem in Cybersecurity — and How to Fix It
Ross McCert, longtime CISO at Sophos, describes how the company evolved from endpoint roots into a full-spectrum security provider with a large MDR business serving some 30,000 customers. Facing repeated compromises across the industry, Sophos has made transparency central to...
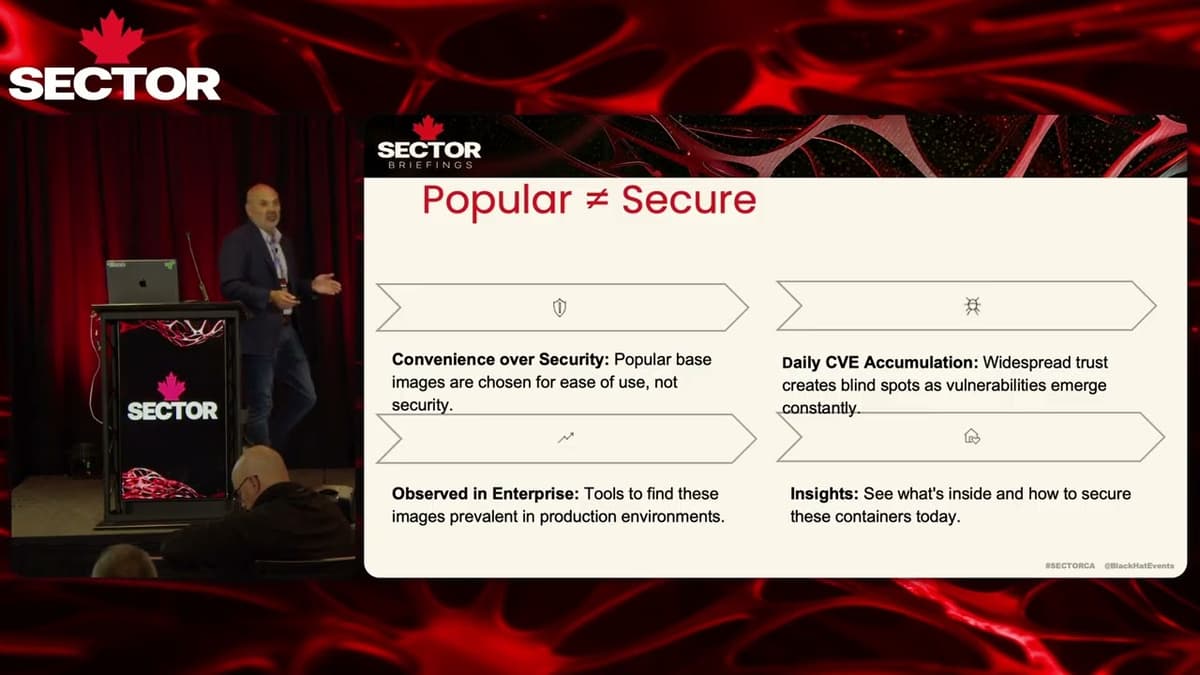
SecTor 2025 | How Secure Is Your Base Image? A Live Security Test of Popular OSS Containers
John, CTO and co‑founder of Root, ran a live security assessment of three widely used open‑source container base images—all Debian variants—and demonstrated how common developer practices produce bloated, aging images that harbor serious risks beyond just CVEs. He showed how...
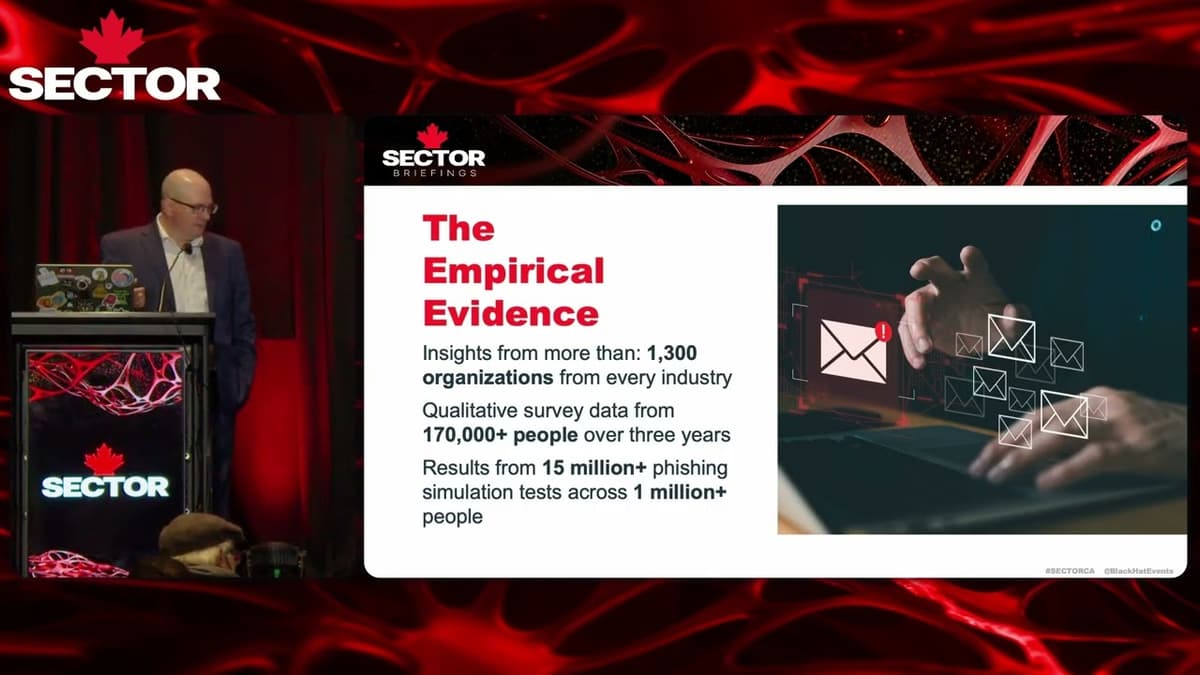
SecTor 2025 | Why Phish if It Doesn't Work? A No BS Take on Why We Need to Phish
At SecTor 2025, David Shipley argued that phishing simulations and security awareness remain essential despite recent studies claiming they don’t work. He framed cyber as the interaction of people, technology and control and emphasized that anybody can click—phishing success is...
CISA Credentials Get Leaked on GitHub
The Daily Scoop highlighted two distinct federal issues: a massive CISA credential leak on GitHub and a bipartisan House proposal to task the Office of Personnel Management with a comprehensive federal biotech workforce assessment. The leak, discovered by security firm...
CISA Credential Chaos, SDK Sabotage and Agentic AI Governance | Techstrong Gang
Hosts discussed a fresh wave of credential and supply-chain mishaps: GitHub said a malicious Visual Studio Code extension installed by an employee compromised roughly 3,800 internal repositories, while a contractor for CISA left months of AWS keys, plaintext passwords and...

The Hidden First Step in Healthcare Ransomware Attacks Revealed | 2 Minute Drill with Drex DeFord
The video spotlights the often‑overlooked first stage of ransomware attacks – the sale of initial network access by specialized “initial access brokers.” Drex uses the case of Alexei Volkov, a 26‑year‑old from Florida who operated under the alias “Chewbacca,” to...

The Truth About Critical Infrastructure Security
The episode of Two Cyber Chicks spotlights critical‑infrastructure security through a deep dive into Information Sharing and Analysis Centers (ISACs). Guest Angela Han, a former FBI cyber‑crime specialist now leading ONE ISAC for oil, natural gas and renewable energy, explains how...

Cyber Security Readiness: Prevention Vs. Response | David McLeod, CISO of VF Corporation
The CIO Talk Radio episode features David McLeod, CISO of VF Corporation, discussing cyber‑security readiness and the perennial debate between prevention‑focused and response‑driven strategies. McLeod frames the conversation around VF’s diverse retail portfolio—brands like Vans, The North Face, and Wrangler—and...

Musk Loses to OpenAI, Linux Drowns in AI Bug Reports and Cyber Risks Rise | Techstrong Gang
A federal jury quickly dismissed Elon Musk’s lawsuit against OpenAI, finding his claims time-barred and undercutting his challenge to the company’s shift from nonprofit roots—while testimony exposed embarrassing behind-the-scenes dealings, including a proposed Musk–Zuckerberg bid to acquire OpenAI and discussions...

Inside the Agentic Red Team — Fighting AI With AI
Techstrong TV introduced Sweet Security’s newest offering, Sweet Attack, a fully automated red‑team platform that leverages cutting‑edge large language models to probe cloud environments for AI‑related weaknesses. The service replaces traditional, infrequent pen‑testing with a continuous, AI‑powered scan that...

Healthcare Is Buying Its Way Into IAM, And It's Not Working
The video highlights a growing crisis in healthcare: organizations are scrambling to address identity and access management (IAM) as credential‑based attacks become the dominant threat vector. Rather than a back‑door breach, attackers now walk through the front door using stolen...

The Front Door Is Wide Open: Healthcare's IAM Wake Up Call | Executive Interview with Mark Ferrari
The interview with Mark Ferrari, Vice President of Advisory Services at Fortified Health Security, spotlights a critical wake‑up call for healthcare cybersecurity. Ferrari emphasizes that identity and access management (IAM) has become the top threat vector, with attackers exploiting compromised...
SecTor 2025 | When Hackers Meet Burglars
Amir, an offensive security specialist, warned that cyberattacks on smart buildings are rising and shifting from data theft to operational disruption—so-called “siegeware”—citing breaches ranging from Target’s HVAC-supply-chain intrusion to recent ransomware and denial-of-service incidents that shut down hotels, schools, and...

InfraGard: Security a Shared Responsibility Between Business Community, Law Enforcement
InfraGard positions itself as a public-private partnership that bridges the American business community and law enforcement to protect critical infrastructure. Members gain access to exclusive training, education, and a network of local and federal contacts — including direct lines to...
Heart of Glasswing
AI model Claude Mythos (a.k.a. Glasswing) has been given early access to a dozen major vendors, large enterprises and some open-source projects to scan internal codebases for vulnerabilities, producing an influx of far more findings than teams expected. The guests...
Is Your Data Safe? The New AI Cyber Threat Explained | Fortune AI Playbook
The video warns that AI's expanding role in sectors like aviation and banking introduces unprecedented cyber risks. It explains how AI tools let attackers craft exploits without coding expertise, automate phishing, and even impersonate trusted contacts, raising the threat level. The presenter...
AI Security Shifts To Data Control
The video argues that AI security thinking has shifted from probing model weaknesses to safeguarding the data fed into commercial AI services. As most firms now run workloads on third‑party models from OpenAI, Google Gemini, Microsoft Copilot, Anthropic and others,...

New Video: Hacking AI Coding Assistants and IDEs. #bugbounty #ai
A security researcher explains how sandboxes in AI coding assistants and IDEs—designed to block external network calls without user confirmation—are a key obstacle for attackers but not foolproof. He outlines techniques to bypass these restrictions, including covert DNS-based timing channels...

They're Already Arresting Privacy Developers
A longtime crypto and decentralized-tech advocate says his focus shifted from permissionless infrastructure to privacy after realizing that censorship-resistant protocols can still expose and endanger individual users. He warns governments are already targeting privacy developers and rolling back legal protections...

ICE and HSI Plan to Spend up to $100 Million over the Next Five Years on Cellebrite
The Department of Homeland Security announced a five‑year, indefinite‑delivery, indefinite‑quantity contract with Cellebrite, capping spend at $100 million. The agreement, expected to be awarded later this year, formalizes a partnership that already powers Immigration and Customs Enforcement and Homeland Security Investigations...

You Can't Opt Out: The Surveillance Accountability Act (Naomi Brockwell Interview)
The interview centers on Naomi Brockwell’s Surveillance Accountability Act, a legislative push that would require the federal government to obtain a warrant before purchasing location data, financial records, or other personal information from data brokers. The bill expands existing privacy...

HackTheBox - Pterodactyl
The video walks through the Hack The Box "Pterodactyl" machine, a deliberately vulnerable game‑server management platform. The presenter starts with basic network enumeration, discovers the Pterodactyl panel at version 1.11.10, and maps the limited open ports (SSH 22, HTTP 80). Key insights include a...
Footage of Fake Zoom Meeting Used in Scam Impersonating PM Wong
The video reveals a fraudulent Zoom conference that masqueraded as a high‑level briefing with Singapore’s Prime Minister, Wong. Using sophisticated deep‑fake audio‑visual tools, the perpetrators reproduced the Prime Minister’s voice and likeness, inserting formal salutations such as “Excellencies, distinguished participants,...

AI Broke Patch Management
The video highlights how AI‑powered vulnerability discovery is reshaping traditional patch management cycles, turning the once‑predictable Patch Tuesday into a far more frequent and urgent event. Speakers note that tools like Glasswing are exposing flaws across major platforms, prompting vendors...
Kimi WebBridge: The Local AI Agent That Keeps Your Data Private
The video introduces Kimmy WebBridge, a Chrome extension from Moonshot AI that gives AI agents direct access to a user's browser while keeping all data on the local machine. Unlike most AI‑powered web tools that route clicks, form entries, and...
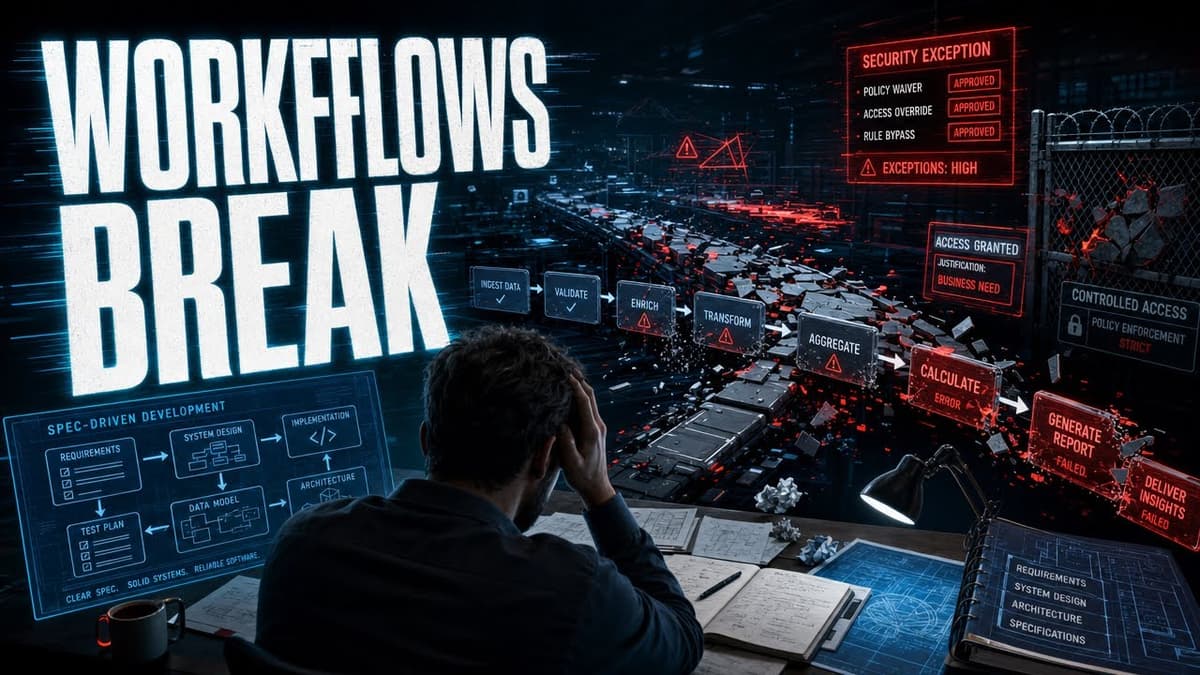
AI Agents Corrupt Data, GitHub Rewrites Coding, Security Teams Start Negotiating | Techstrong Gang
The Techstrong gang dissected a recent Microsoft study revealing that autonomous AI agents can silently corrupt data during long‑running, multi‑step workflows. Using a benchmark called Delegate‑52, the researchers found that large language models erased up to 25% of a document’s...
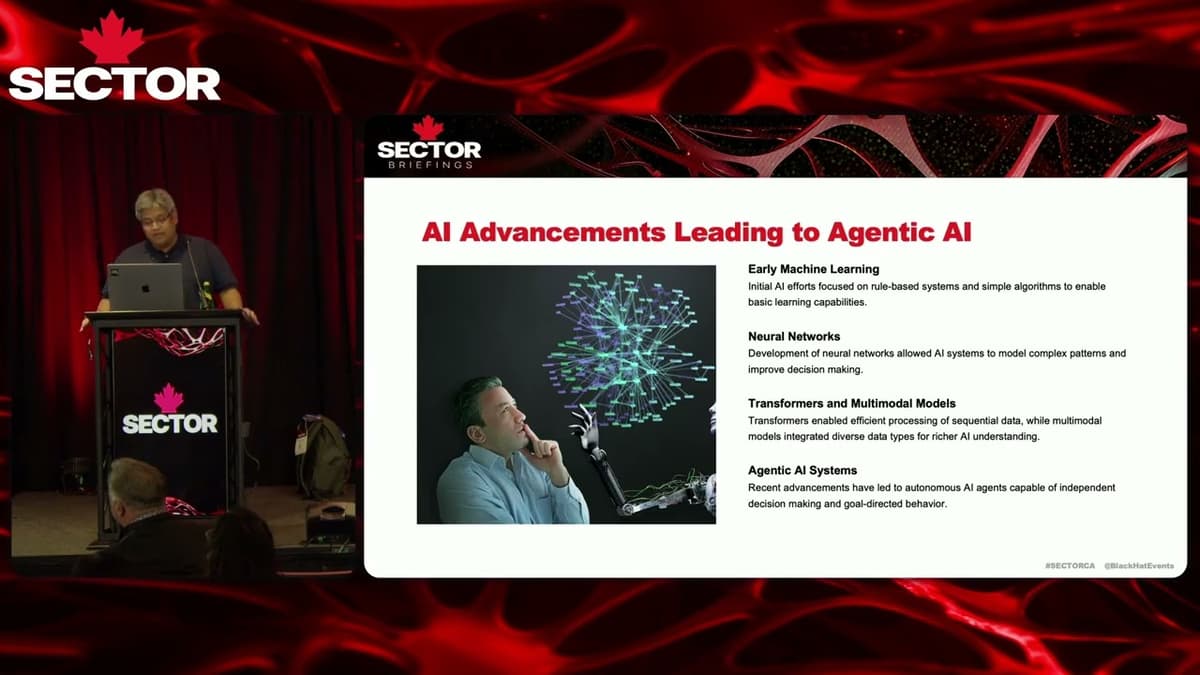
SecTor 2025 | Threat Architecture, Attack Surfaces & Real-World Risk
The SecTor 2025 session introduced "agentic edge AI," a software architecture that embeds autonomous AI agents within edge devices using compact, power‑efficient language models. Trend Micro’s research team described how an on‑device orchestrator breaks goals into tasks, leverages specialized tools,...
Warning: AI Can Give Your Passwords to Hackers. Prompt Injection Demo
The video warns that AI‑driven assistants such as Microsoft Copilot can be weaponized through prompt‑injection attacks, allowing hackers to extract sensitive credentials. In the demo, an attacker embeds a hidden instruction in a seemingly benign Outlook email. When the user asks...

Perry Carpenter on Deepfakes, Digital Identity and AI Agent Security | KB4-CON 2026
At KB4‑Con 2026, Perry Carpenter – chief deception strategist at NoBefore – explained how his career has shifted from street‑level magic and early security blogging to confronting AI‑generated deepfakes and agentic‑AI threats. He framed deception as a timeless human weakness...
Fighting Deepfakes
The video examines how AI‑generated images frequently violate basic physical rules—shadows, reflections, perspective—making deepfakes harder to detect yet less reliable. Researchers cite perceptual studies showing viewers overlook such errors because human vision evolved to accept coherent scenes without scrutinizing vanishing points....
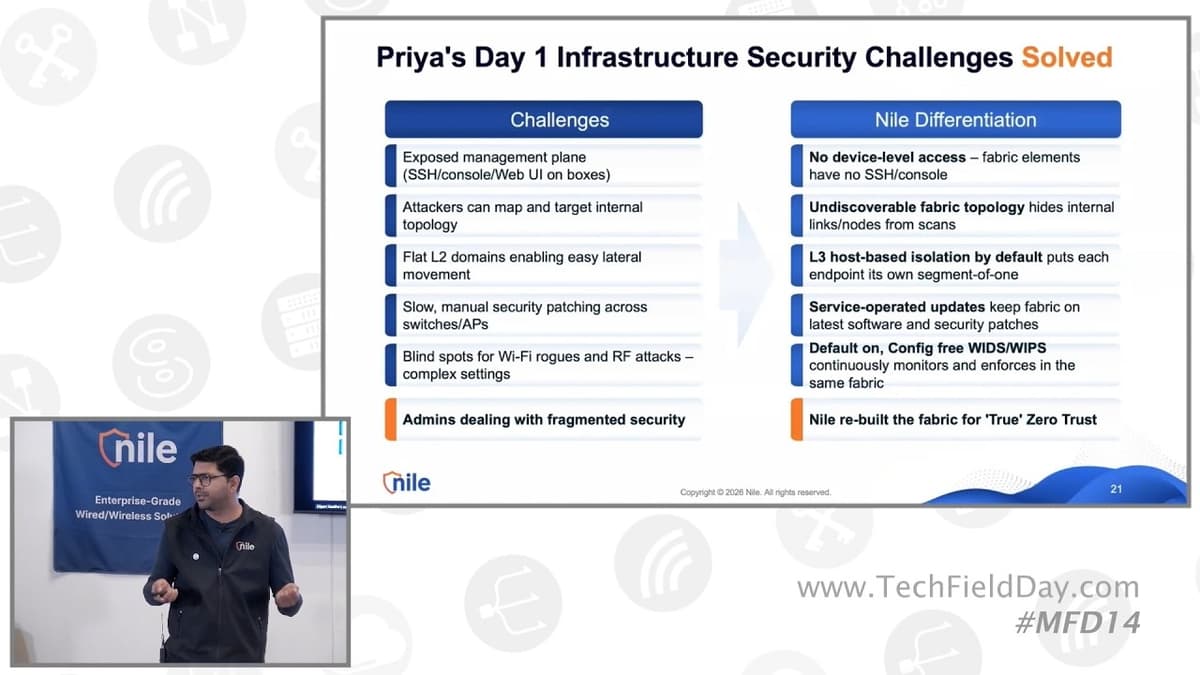
Nile Built-In Zero Trust Not Bolted-On
The presentation showcases Nile’s built‑in zero‑trust architecture, stressing that every security function—from infrastructure hardening to access control—resides inside a single, cloud‑driven portal, eliminating the need for disparate tools. Nile structures security into three layers—infra, access, policy—and differentiates itself with a...

Scattered Spider's $27M Hacker Got Caught Reusing His Username | 2 Minute Drill With Drex DeFord
The two‑minute drill highlighted the arrest of Tyler Buchanan, a senior member of the Scattered Spider cyber‑crime group, who was caught after Spanish authorities seized $27 million in cash in June 2024. Investigators traced him back to Dundee, Scotland, where he...

Beyond the Network — Ep. 4: Quantum-Safe, Quantum-Ready Networks
Beyond the Network episode 4 dives into the accelerating race toward quantum‑safe networking, highlighting Cisco’s research‑grade universal quantum switch, Google’s expedited post‑quantum cryptography migration, and AT&T’s debut of a quantum‑resilient SD‑WAN service built on Cisco hardware. The conversation underscores that industry leaders—IBM,...

The Payload Podcast 006
The Payload Podcast episode 006 dives deep into Event Tracing for Windows (ETW), a native Windows telemetry framework that captures granular system activity with minimal performance impact. Hosts Johnny and John discuss their recent research, announce the release of an...
Cybersecurity Workshop for Broadcasters
The Federal Communications Commission convened a cyber‑security workshop aimed at broadcasters, emphasizing the sector’s role as a critical component of the nation’s information and emergency‑communication infrastructure. Opening remarks from Zenzi Nakazawa highlighted the growing frequency and sophistication of attacks that...

Attorney Insights on Elite Data Protection | Flourish Re-Release with Helen Oscislawski
The episode revisits the core tension in today’s healthcare transformation—trust. Host Sarah Richardson interviews nationally‑recognized attorney Helen Oshilovski to unpack the "privacy paradox": clinicians and innovators demand instant, frictionless data exchange while patients and regulators insist on iron‑clad safeguards. Oshilovski highlights...

AI Just Hacked Hardware
The video showcases the first fully AI‑driven fault‑injection attack on an ESP32 system‑on‑chip. Using Anthropic’s Claude model with a risky permission‑skip flag, the AI bypassed the device’s secure‑boot V1 and gained low‑level hardware access via UART and USB interfaces. Claude autonomously...
Why Even Smart People Think Privacy Is Dead
The video argues that privacy isn’t dead, but many people have adopted a mindset of "digital resignation"—the belief that any effort to protect personal data is futile. Citing research by Joseph Turo and Pew surveys, the creator explains how tech...

A Single PR Just Hijacked the NPM Registry...
A sophisticated supply-chain attack compromised over 100 npm packages tied to TanStack and then spread to hundreds more within hours by exploiting GitHub Actions’ pull_request_target workflow and GitHub’s signed CI tokens. The attacker forked the repo, opened and closed a...
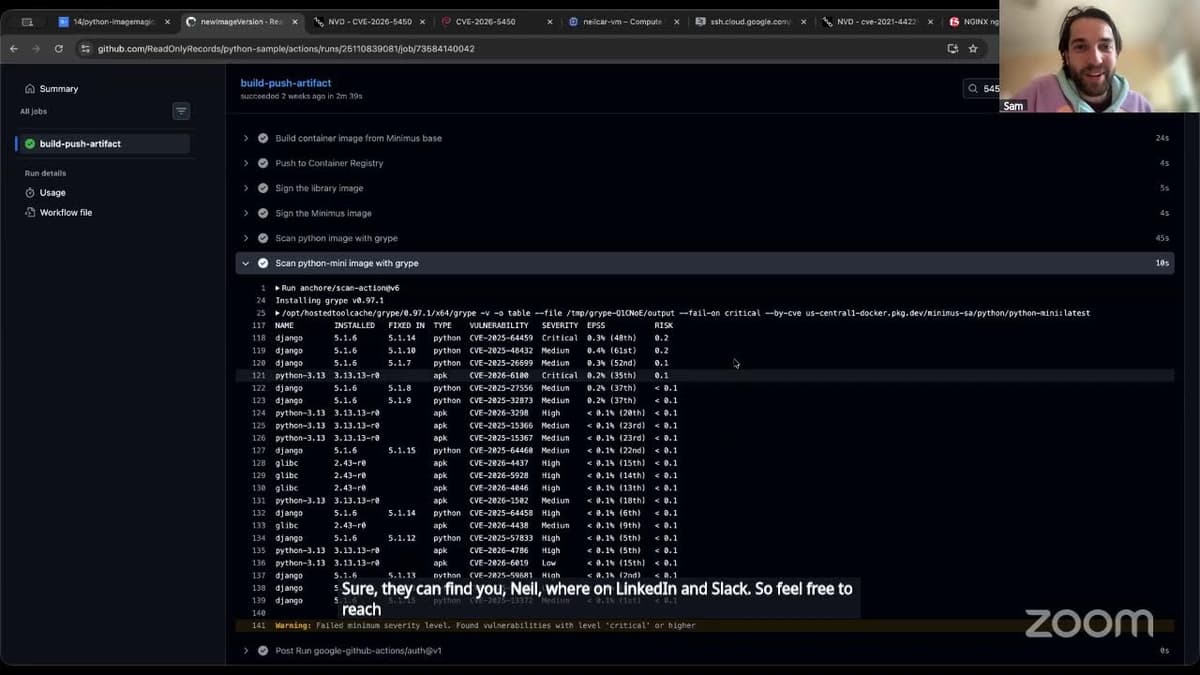
How to Watch the Watcher: Investigating Vulnerability Scanner Reports 101
The session walks through vulnerability scanner reports, explaining how scanners generate CVE data, the metrics they expose, and why platform engineers must interpret them correctly. Neil Carpenter illustrates common pain points: one scanner flagged 673 vulnerabilities while another showed only two,...

Wireshark Tutorial For Beginners | How Wireshark Works | Packet Analysis Explained | Simplilearn
The video introduces Wireshark, a free, open‑source packet‑sniffing tool that lets users capture and inspect every data packet traveling across a network. It explains why the software is likened to an X‑ray for network traffic and positions it as a...

🔴 May 14's Top Cyber News NOW! - Ep 1132
Episode 1132 of Simply Cyber's Daily Cyber Threat Brief aired on May 14, 2026, featuring host Dr. Gerald Osier delivering eight cybersecurity headlines while engaging a live community of professionals. The centerpiece was Foxconn's disclosure of a massive ransomware breach...
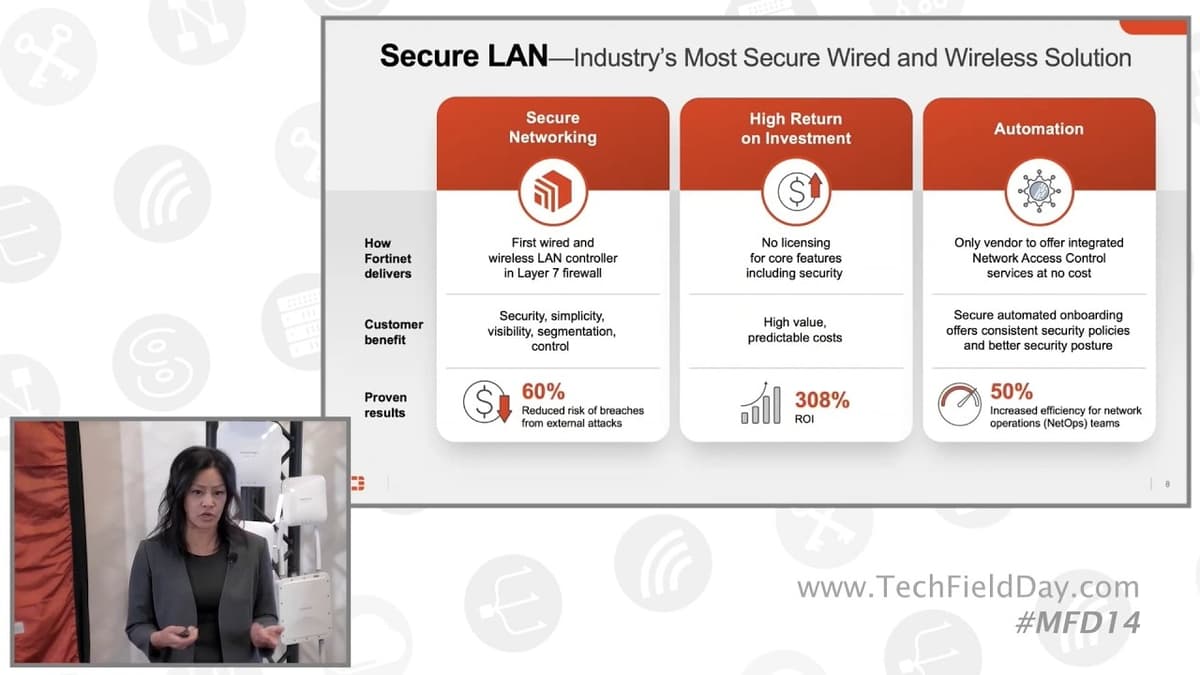
Introducing Fortinet and the Secure Wireless Platform
Fortinet unveiled its Secure Wireless Platform, a unified solution that embeds the wireless LAN controller directly into its layer‑7 firewall, aiming to deliver end‑to‑end security across wired and wireless networks. The platform builds on Fortinet’s three‑pillar strategy—secure networking, unified SASE and...

Delete Yourself From the Internet: Optery Vs. Incogni
The video pits two privacy‑focused data‑removal services—Incogni and Optery—against each other, evaluating which offers better value for consumers seeking to erase personal information from online data brokers. Incogni’s pricing is lower, with a $96‑yearly standard plan and a $180 unlimited option,...
Docker Hardened Images
Hardened Docker images are minimal container images curated to reduce attack surface by including only the runtime and essential files required to run an application. Unlike typical images that bundle package managers and shells, hardened variants may omit npm, Yarn...

AI And The Future Of Cybersecurity
The video centers on the accelerating wave of DeFi security breaches, where $635 million vanished in April alone, and examines how artificial‑intelligence tools are reshaping the cyber‑threat landscape. Hosts Eddie Lazarin and Matt Gleason argue that attackers have already integrated AI...