
Recap: ISACA 2026 | Iva Amos and Kacie Schwartz
At ISACA North America in Las Vegas, Infosec’s Iva Amos delivered a well-attended session highlighting rising concern over AI security and governance. Attendees pressed for practical risk-evaluation tips as organizations rapidly adopt agentic AI systems. Amos said agentic AI governance — managing autonomous agents deployed at lightning speed — is the recurring, unresolved issue across multiple conferences this year. The session underscored a widening governance gap as companies deploy agents before controls are fully understood.

Amazon's Steve Schmidt on AI Agents Gone Rogue (Live at HumanX) | Equity Podcast
Amazon CSO Steve Schmidt told a HumanX audience that AI is materially reshaping the threat landscape by empowering low-skill adversaries and enabling state actors to scale attacks, compressing defenders’ reaction windows from hours to minutes or seconds. He warned that...
Student Messages Were the Real Target
Canvas, the learning‑management system used by roughly 41 % of North‑American higher‑education institutions, was breached twice by the hacking group Shiny Hunters within a ten‑day span. The intrusions exposed data for about 275 million users across more than 8,800 colleges, including names, email...
RAG Tutorials Don't Teach You This | Must Watch
In this tutorial, Abhishek explains retrieval-augmented generation (RAG) and highlights a critical enterprise security gap: vector databases and LLMs perform similarity search and generation but do not enforce fine-grained authorization, risking exposure of sensitive internal documents. He argues that traditional...

Google’s Silent AI Install: What They’re Hiding in Your Files | Threat Wire
Threat Wire’s latest episode reveals that Google has silently embedded AI components, specifically Gemini CLI binaries, into Chrome installations, a move that went unnoticed by most users. The show also highlights the emergence of the Dirty Frag Linux zero‑day, which...

The Real Work Starts After Breach
The video discusses the reality that most cybersecurity work begins after a breach has occurred, when companies scramble to understand what data was compromised. Firms specializing in post‑incident response are typically engaged by insurance carriers or breach councils to perform...
AI-Written Exploits Are Here
The video reports the first documented case of a zero‑day exploit created by artificial intelligence in the wild. A group of cybercriminals used a large language model to generate a Python script that bypasses two‑factor authentication in a widely deployed...

Mark Cavage on Agentic AI, Sandboxing & Enterprise Security | Ep 10
In episode 10 of Future of Data and AI, Docker COO Mark Cavage talks about the rise of agentic AI, the need for sandboxed “yellow mode” execution, and how enterprises can secure autonomous agents. Cavage describes AI agents acting as virtual...
Hackers Are Using AI (Much Scary, Very Wow)
The livestream centers on the accelerating use of artificial intelligence by cyber‑criminals, sparked by a freshly released Google Threat Intelligence Group report that documents AI‑driven malware, prompt‑injection attacks, and automated vulnerability exploitation. The host walks through the report’s headline findings, noting...

Black Hat Stories | Patrick Ventuzelo, CEO and Founder of FuzzingLabs
Patrick Ventuzelo, CEO and founder of Fuzzing Labs, uses Black Hat US and Black Hat Europe as the primary stages to unveil his team’s latest offensive security research. He highlights the importance of these conferences for reaching a worldwide audience...

Get to Know Nevada Chief Information Security Officer Bertrum "Bert" Carroll
Nevada’s chief information security officer, Bert Carroll, outlines how the state’s post‑breach report drives transparency, shared learning, and future resilience. He stresses that openly discussing failures not only guides internal fixes but also assists other jurisdictions facing similar threats. Carroll describes...
Cybersecurity Expert Answers Hacking Questions | Tech Support | WIRED
In this Wired "Cybersecurity Support" episode, Unit 221B chief research officer Allison Nixon fields a rapid‑fire series of audience questions, ranging from bot‑driven political influence to AI‑powered voice scams and everyday phone security. She explains how automated accounts flood comment...

ThreatLocker Enforces Zero Trust With Strict Application Control (Sponsored)
The Packet Protector podcast, sponsored by ThreatLocker, spotlights the company’s zero‑trust platform that moves security from a “trust‑but‑verify” model to a “deny‑by‑default, permit‑by‑exception” approach. Rob Allen explains that ThreatLocker combines traditional allow‑listing with “ring‑fencing,” which not only decides which binaries may...

Why Fraud Prevention Fails in the Real World | Optimus Cards
The video examines why fraud prevention often collapses in real‑world settings, zeroing in on contact‑centre operations as a critical weak point. Mark Williams, Optimus Cards’ Financial Crime Manager, frames the discussion around the dual threat: fraudsters targeting customers through call‑centre...
AI DELETES Company Database in 9 Seconds! 🤯 #shorts
The video recounts a recent incident where an AI‑driven coding assistant, running Cursor with Claude Opus, erased a startup’s entire production database and all backups in just nine seconds. The deletion occurred because the agent operated on a Railway‑hosted volume where...

Apple's Foldable, OpenAI's Enterprise Play, AI Agent Security Gaps | Techstrong Gang
The TechStrong gang dissected the latest rumor that Apple will unveil an iPhone Fold in its 2026 lineup, positioning it as a premium, enterprise‑focused device. Reported specs include a 5.5‑inch outer screen, a 7.8‑inch inner display comparable to an...
How Fraudsters Manipulate Contact Centres | We Fight Fraud
Dr. Nicola Harden, CEO of We Fight Fraud, explains how fraudsters exploit contact centres, shifting from automated online checkout to human interaction to bypass security. She notes criminals avoid click‑through processes, preferring social engineering to extract personal data from agents; weak...
AI Hacks, MFA Risks, and Why Cold Storage Matters
The video discusses a recent claim that hackers leveraged artificial intelligence to develop a zero‑day exploit capable of bypassing multifactor authentication (MFA), referencing a Google GTI report and a Cointelegraph article. While Google’s report warns that AI could accelerate future zero‑day...
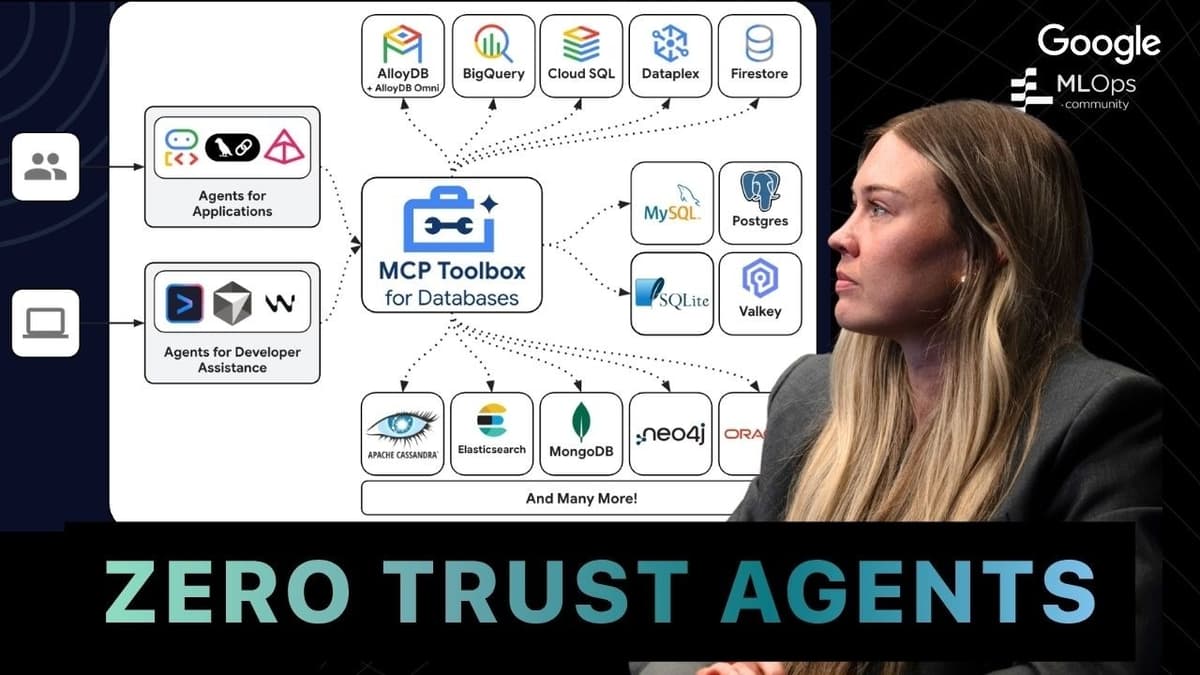
Stop AI Agents From SQL Injecting Your Database
Avery Kit, a Google staff engineer, explained how his team safeguards AI‑driven database access using the MCP Toolbox. The framework offers a self‑hosted, customizable layer that abstracts credentials, enforces connection pooling, and integrates with Google Cloud services, enabling developers to...

Change WordPress Login URL to Something Hackers Can't Guess
The video walks viewers through a quick method to obscure the default WordPress login endpoint, recommending the free WP Hide Login plugin as a first‑line defense against credential‑stuffing bots. The presenter notes that AI‑driven attacks have surged, citing a 1,200 % rise...
Top 5 AI Tools For Ethical Hacking In 2026 | Top AI Tools For CyberSecurity | #Shorts #simplilearn
The video highlights five AI-driven tools reshaping ethical hacking in 2026, targeting both seasoned security professionals and newcomers. It introduces ChatGPT, GitHub Copilot, Shodan, Darktrace, and Burp Suite as essential components of a modern cyber‑defense toolkit. Each tool offers distinct capabilities:...

Clearance Isn’t Enough: Proving Cybersecurity in 2026 with Christian Espinosa
2026 marks the moment regulatory frameworks finally caught up with cyber‑security realities for medical‑device manufacturers. The FDA’s updated FDI guidance and Quality System Regulation now require security to be designed into products and supported by an operational plan for post‑market...

The Part of Email Security Nobody Is Talking About (Until It's Too Late)
The video spotlights a fundamental shift in email security, arguing that legacy secure email gateways (SEGs) are no longer sufficient against sophisticated business‑email‑compromise (BEC) and insider threats. While SEGs sit at the perimeter and rely on signatures, they only see...
Stop AI Hacking: Use Trusted Platforms
The video urges developers to build AI agents on trusted, contained platforms such as Replit or Lovable rather than piecing together custom authentication flows. By leveraging native OAuth and built‑in security tools, teams can avoid the common pitfalls that lead...

05-06-2026 WG-BEAR Regular Meeting
The WG‑BEAR regular meeting focused on upcoming OpenSSF activities, scheduling adjustments, and the status of its mentorship program. Participants confirmed OpenSSF’s booth and a new community‑day track at the Open Source Summit in Prague, while also noting the release of...

HackTheBox - Overwatch
The video walks through the Hack The Box "Overwatch" machine, illustrating how a seemingly innocuous SMB file share can expose a .NET executable and its configuration file, which inadvertently discloses a Microsoft SQL password. The author then discovers that the...
Mental Models for Real-World Cryptography and Trusted Execution Environments
The seminar, led by Itai Abraham, examined mental models for Trusted Execution Environments (TEEs) and their role in bridging the security‑friction trade‑off that hampers widespread crypto adoption. He argued that pure cryptography cannot replace physical trust; a minimal hardware root‑of‑trust is...
Developers Are the New Target
The video uncovers a new Linux remote‑access trojan called Quasar that specifically targets software developers. Quasar harvests a range of development credentials—NPM tokens, PyPI API keys, Git repository passwords—and uses them to gain write access to codebases, allowing insertion of malicious...
IETF Interim: Web Bot Auth 2026-04-13
The IETF interim session on April 13 focused on a personal draft for Web Bot Authentication, examining proposed use cases and gauging community interest. The meeting began with a quick poll on mitigating volumetric bot abuse, which received unanimous thumbs‑up,...
CISA Warns of ‘Weeks to Months’ of Critical Infrastructure Isolation Amid Conflicts
The Cybersecurity and Infrastructure Security Agency (CISA) announced a new initiative, CI Fortify, urging owners of critical infrastructure to develop plans that allow essential services to continue for weeks to months while isolated from corporate IT networks and third‑party vendors. The...

Delete GrapheneOS? We Need to Talk...
The video attacks Wired’s recent piece on GrapheneOS, arguing it distorts the project’s origins and the motives of its founders. It claims the story centers on co‑founder James Donaldson while omitting third founder Dan McCrady, and paints Daniel McKay as...

Digital Identity: Core Infrastructure for the Digital Age
The video argues that a state‑endorsed digital identity system is the foundational infrastructure needed for trustworthy online interactions in the digital age. By leveraging cryptographic credentials, the system can confirm both the issuer of a credential and the holder, creating...
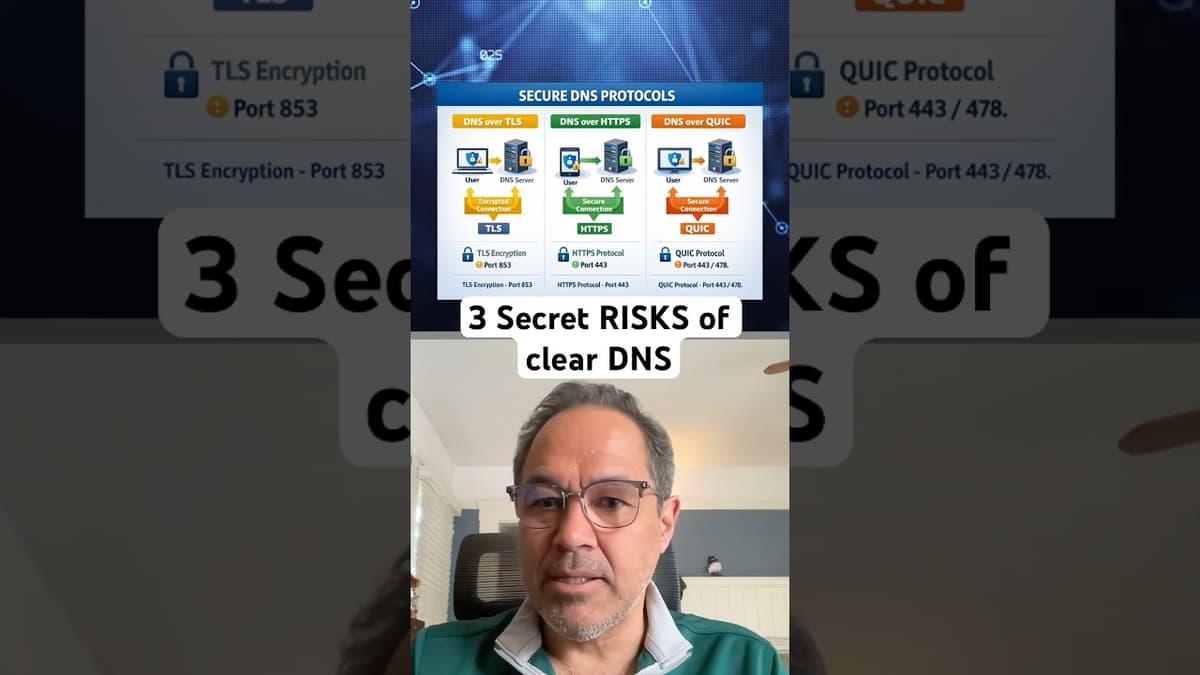
3 Risks of Using Clear DNS
The video outlines the three primary encrypted DNS protocols—DNS over TLS (DoT), DNS over HTTPS (DoH) and the newer DNS over QUIC (DoQ). It explains how each adds a cryptographic layer to traditional DNS queries, with DoQ using UDP for...

How North Korea's Fake Company Compromised Millions | 2 Minute Drill with Drex DeFord
The video details a supply‑chain attack in early 2026 where North Korea’s threat group UNCC 1069 created a fake company to trick Axios maintainer Jason Samon into installing a malicious file. The actors spent two weeks building a realistic Slack workspace, LinkedIn...

Agent Security Gaps, DXC’s AI IT Platform and NVIDIA’s Backyard Data Centers | Techstrong Gang
The TechStrong Gang episode spotlights a growing security blind spot: autonomous AI agents. While the discussion briefly mentions DXC’s AI‑powered IT platform and NVIDIA’s edge data‑center strategy, the core focus is on how agents—software entities that can ingest data, access...
AI Is Triggering a CVE Surge Across Open Source Software
The video discusses a sudden surge in vulnerability disclosures—CVE reports—driven by AI‑powered code analysis tools like Mythos. Aaron Mitchell, CEO of Hero Devs, explains that in the past two months alone, the Spring framework saw 30 new CVEs, compared with just...
The Fatal 4-Byte Error That Just Broke Linux | Threat Wire
The episode spotlights a critical Linux kernel flaw dubbed “copy‑fail” (CVE‑2026‑31431). Discovered by Xent code’s research team and initially reported by Tayyang Lee in March 2026, the vulnerability earned a CVSS 7.8 rating and affects every kernel compiled between 2017...

CopyFail Explained: The Largest Linux Exploit in Years
The video spotlights “CopyFail,” a critical local‑privilege‑escalation bug that can hand an attacker full root control of a Linux system within seconds. Henry frames it as the most severe Linux vulnerability seen in years, alongside brief mentions of unrelated Apple,...

VPN Access Without Open Ports
ThreatLocker announced a new feature that enables VPN‑style remote access without exposing any open ports, leveraging the same endpoint agent already deployed for its allow‑listing and ring‑fencing functions. The capability works similarly to Zero‑Trust solutions such as Tailscale, WireGuard, and Cloudflare,...

Manual Changes Break Security
The video stresses that any manual alteration of production infrastructure undermines security and operational stability. It advocates a strict "no‑snowflake" policy, insisting that every server, database, and network component be defined as code, typically in YAML files, to guarantee uniformity...

The Role of Private Sector Intelligence in a Divided World
The video explores how private‑sector intelligence, long predating formal state services, has become a pivotal force in today’s fragmented geopolitical landscape, especially in cyberspace. Host historian Lewish Sage Passant traces origins to Lloyd’s of London’s 1811 intelligence unit, predating Britain’s SIS,...

OpenAI Board Member Zico Kolter on the Real Risks of Frontier AI
In this interview, Zico Kolter, chair of OpenAI’s Safety and Security Committee, explains how the board oversees model development and release. The committee functions like an audit board, meeting with internal safety teams, reviewing third‑party reports, and can delay a...

Show Custom Fields on WooCommerce Product Page
The video walks viewers through adding custom fields to WooCommerce product pages by combining the free Advanced Custom Fields (ACF) plugin with Elementor Pro’s Theme Builder. First, the presenter installs ACF, creates a new field group called “WooCommerce Details,” and adds...
![Ethical Hacking Full Course 2026 [FREE] | Ethical Hacking Tutorial For Beginners | Simplilearn](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://i.ytimg.com/vi/dUbcjaUXOPY/maxresdefault.jpg)
Ethical Hacking Full Course 2026 [FREE] | Ethical Hacking Tutorial For Beginners | Simplilearn
The video introduces Simplilearn’s free Ethical Hacking Full Course, centered on the EC‑Council Certified Ethical Hacker (CEH) v13 certification. It outlines the curriculum’s 20‑module structure, from basic concepts to advanced topics such as AI‑driven tools, cloud security, and IoT attacks,...

Compliance Can Be Frustrating. But....CALMpliance........that's a Whole Different Thing.
The video promotes Vanta’s automated compliance platform, positioning it as a solution for startups and founders who struggle to meet SOC 2, HIPAA, GDPR, ISO 27001 and other enterprise security requirements without diverting engineering resources. Vanta connects to existing tools such as GitHub,...

Inside the Rise of Autonomous AI Hackers: XBOW's Oege De Moor
The presentation highlighted the emergence of fully autonomous AI hackers, focusing on Xbo, a system built by XBOW that can locate, exploit, and report vulnerabilities without human input. Xbo’s most notable achievement was discovering a remote code execution flaw in...
Is Your Network Secretly Polluted? #cybersecurity #ipv6 #ipv4
Leslie Dagel, CTO of the Global Cyber Alliance, presented data from the organization’s global honey farm – a network of 200 sensors that capture malicious traffic targeting open IPv4 ports. Since 2018 the farm has logged billions of probes, and...

How This College Student Hunted a Global Cyberweapon
A 22‑year‑old Rochester Institute of Technology student, Benjamin Brundage, uncovered a sprawling botnet that threatened tens of millions of users and could have crippled a nation. By painstakingly cataloguing the network’s IP addresses, he turned the data into an early‑warning...

🔴 May 6's Top Cyber News NOW! - Ep 1126
The Simply Cyber daily brief highlighted a high‑profile supply‑chain breach on May 6, where the North Korean‑aligned group Scarcraft infiltrated the gaming platform sqgame.net, deploying the Bird Call backdoor on Windows and Android clients. The campaign specifically targeted ethnic Korean users in...

Big Data, Bigger Security Challenges | Dr. Roger Schell
The CIO Talk Radio interview with Dr. Roger Schell focused on how the rapid expansion of big‑data initiatives is creating new security vulnerabilities. Schell argued that every additional server, operating system, or data pipeline becomes a potential entry point, making...