
Cohesity and CISA Announce Cybersecurity Information Sharing Partnership
Cohesity announced a partnership with the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to create a voluntary framework for sharing cybersecurity information. The collaboration will enable direct exchanges of threat alerts, malware analysis, and indicator bulletins, as well as participation in CISA‑convened forums with other public‑private stakeholders. By linking Cohesity’s AI‑powered data security platform with federal threat intelligence, the partnership aims to improve detection, prevention, and mitigation of cyber risks affecting critical infrastructure and the broader digital ecosystem. The agreement does not constitute an endorsement of Cohesity products by CISA.

Frontnode Achieves ISO/IEC 27001 Certification Amid Growing Institutional Focus on Digital Asset Governance
Frontnode, the Estonia‑based Bitcoin exchange, custody and transfer platform, announced it has achieved ISO/IEC 27001 certification, the global benchmark for information security management. The fintech now serves more than 100,000 customers across Europe and beyond, reinforcing its operational controls as...

The Future of Cybersecurity: What CISOs Must Do Differently in 2026
The 2026 cybersecurity outlook warns CISOs that AI‑powered attackers, ransomware‑as‑a‑service, and deepfake fraud are outpacing traditional defenses. Signature‑based tools and manual patching are obsolete, while real‑time behavioral analytics, dynamic allowlisting, and automated containment become essential. Boards now demand concrete metrics—dwell...

KATE ROBERTSON: Bill C-22 and Carney's Return to Giving over Data Sovereignty and Civil Liberties to Trump's USA
Canada’s Liberal government, led by Prime Minister Mark Carney, is pushing Bill C-22, a streamlined law titled “An act respecting lawful access.” The bill seeks to embed the U.S. CLOUD Act’s extraterritorial data‑request powers into Canadian legislation, effectively allowing American...

Acumen Cyber and AttackIQ Partner to Strengthen Cyber Defense Validation
Acumen Cyber and AttackIQ announced a strategic partnership to deliver continuous validation of cyber defenses. The collaboration merges Acumen Cyber’s engineering‑led security operations with AttackIQ’s Continuous Threat Exposure Management (CTEM) platform. Together they will emulate MITRE ATT&CK techniques, expose exploitable...

Designing for Data Compliance — Automated PII Redaction in Logs and Backups
Engineers frequently expose personally identifiable information (PII) when logs or backups capture raw objects, leading to GDPR, PCI‑DSS, and trust violations. Automated redaction pipelines—both inline and asynchronous—scan logs, trace spans, ORM queries, backup streams, and third‑party SDK payloads to strip...

Hackers Don’t Need Your Passwords. They Just Need Your HVAC Contractor.
Building automation systems (BAS) have shifted from isolated controllers to cloud‑connected ecosystems, expanding a $124 billion market to an estimated $204 billion by 2030 and creating a massive attack surface. Legacy protocols like BACnet and Modbus lack encryption, while remote‑access paths for...

Red Hat MicroShift 4.16.63: Important Security Update for Kubernetes at the Edge of the Infrastructure
Red Hat issued Security Advisory RHSA‑2026:20436 on May 28, 2026, classifying the MicroShift 4.16.63 update as “Important.” The patch addresses CVE‑2026‑33186, a gRPC‑Go authorization bypass affecting HTTP/2 path validation. It covers multiple architectures—including x86_64, ARM64, IBM Z, LinuxONE, and Power—used in single‑node edge Kubernetes deployments....

Perplexity Launches Open-Source Bumblebee Scanner to Check Developer Laptops for Malicious Packages, Extensions, and AI Tool Configs
Perplexity has released Bumblebee, an open‑source, read‑only scanner that inspects developer laptops for malicious packages, editor extensions, browser add‑ons, and AI tool configurations. The Go‑based utility runs on macOS and Linux under an Apache 2.0 license and requires no subscription. It...

Resecurity Supports Microsoft DCU in Disrupting Fox Tempest ’S Cybercriminal Code-Signing Ecosystem
Microsoft’s Digital Crimes Unit, with Resecurity’s assistance, dismantled Fox Tempest—a malware‑signing‑as‑a‑service that leveraged counterfeit Microsoft code‑signing certificates. On May 19, 2026, the agency seized the signspace.cloud site, shut down hundreds of virtual machines, and revoked more than 1,000 fraudulent certificates....

Check Point Launches AI Agents That Think Like Attackers as Autonomous Exploitation Reaches Critical Threat Level
Check Point introduced Agentic Exposure Validation (AEV), an AI‑driven module in its Exposure Management platform that deploys autonomous agents to reason like attackers and prove which vulnerabilities are truly exploitable. The launch arrives as frontier AI models have accelerated exploit...

Microsoft’s Stance on Zero Day Exploits Is a Dumpster Fire of Their Own Making
Microsoft’s recent blog declares publishing zero‑day proof‑of‑concept exploits as criminal activity, a stance that sparked backlash after researcher Nightmare Eclipse was banned from GitHub, GitLab, and Microsoft’s vulnerability portal. The author highlights the inconsistency of Microsoft’s policy, noting the company...

How Deno’s New Firewall Stops AI Agents From Leaking Passwords
Deno has open‑sourced Claw Patrol, a firewall that sits between AI agents and external systems to protect credentials, control actions, and monitor activity in real time. The framework uses HashiCorp Configuration Language for flexible rule definition and supports secure tunnels...
Bad Vibes: AI-Generated Code Is Vulnerable, Researchers Warn
Georgia Tech researchers have unveiled the Vibe Security Radar, a tool that scans public vulnerability databases to identify security flaws introduced by AI‑generated code. The radar has already flagged 74 vulnerabilities, including 14 critical and 25 high‑severity issues such as...
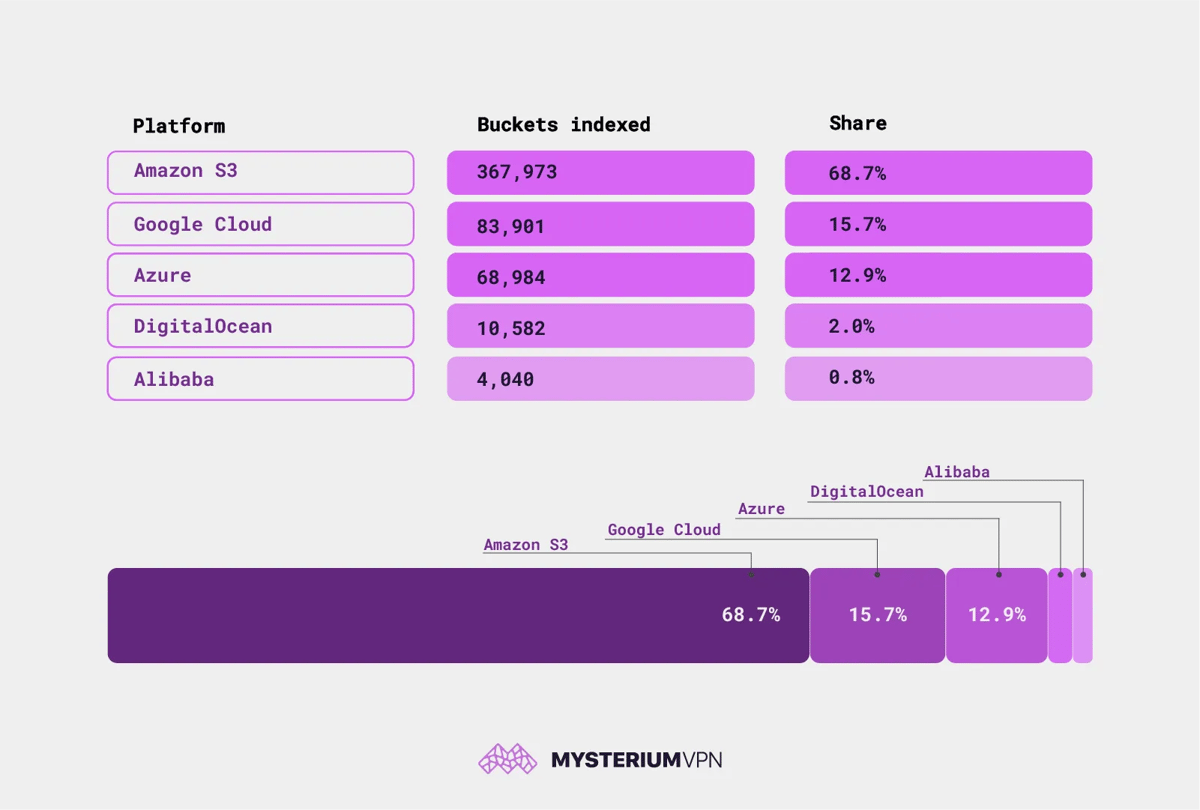
19.6 Billion Files Are Sitting Open on the Internet. No Password Required
Researchers at Mysterium VPN identified 19.6 billion publicly accessible files across 535,480 cloud storage buckets on AWS, Google Cloud, Azure, DigitalOcean and Alibaba. Among them are 685,000 credential files and nearly 1 million database dumps, exposing passwords, API keys and customer data....