
LeakWatch 2026, Security Incidents, Data Breaches and IT Status for the Current Calendar Week 20
During calendar week 20 (May 11‑17 2026) LeakWatch recorded a shift from isolated leaks to clustered risk vectors. Notable incidents included a material cyberattack on West Pharmaceutical Services that halted global production systems, a confirmed breach at Foxconn’s North American factories, and a multi‑stage intrusion of Instructure’s Canvas platform affecting student data. Phishing campaigns in German‑speaking markets escalated, employing QR codes, CAPTCHA stages and everyday service pretexts, while critical vulnerabilities in Microsoft Exchange, Cisco SD‑WAN and NGINX entered the CISA Known‑Exploited catalog. The week underscored the convergence of extortion, supply‑chain disruption, and advanced social engineering.

Researchers Use Anthropic’s Mythos AI to Find Two Bugs in MacOS, Cracking Apple’s Memory Integrity Enforcement in Just 5 Days
Researchers at Calif used Anthropic's Mythos AI to uncover two MacOS bugs that together bypass Apple’s Memory Integrity Enforcement (MIE). The team combined the AI‑generated insights with human expertise to craft a privilege‑escalation exploit in just five days. Apple’s MIE,...

CVE-2026-42897: Microsoft Confirms Active Exploitation of Exchange Server Zero-Day
Microsoft confirmed that attackers are actively exploiting a new Exchange Server zero‑day, CVE‑2026‑42897, with a CVSS rating of 8.1. The flaw is a cross‑site scripting issue affecting Outlook Web Access, allowing spoofing via malicious JavaScript embedded in crafted emails. Microsoft...
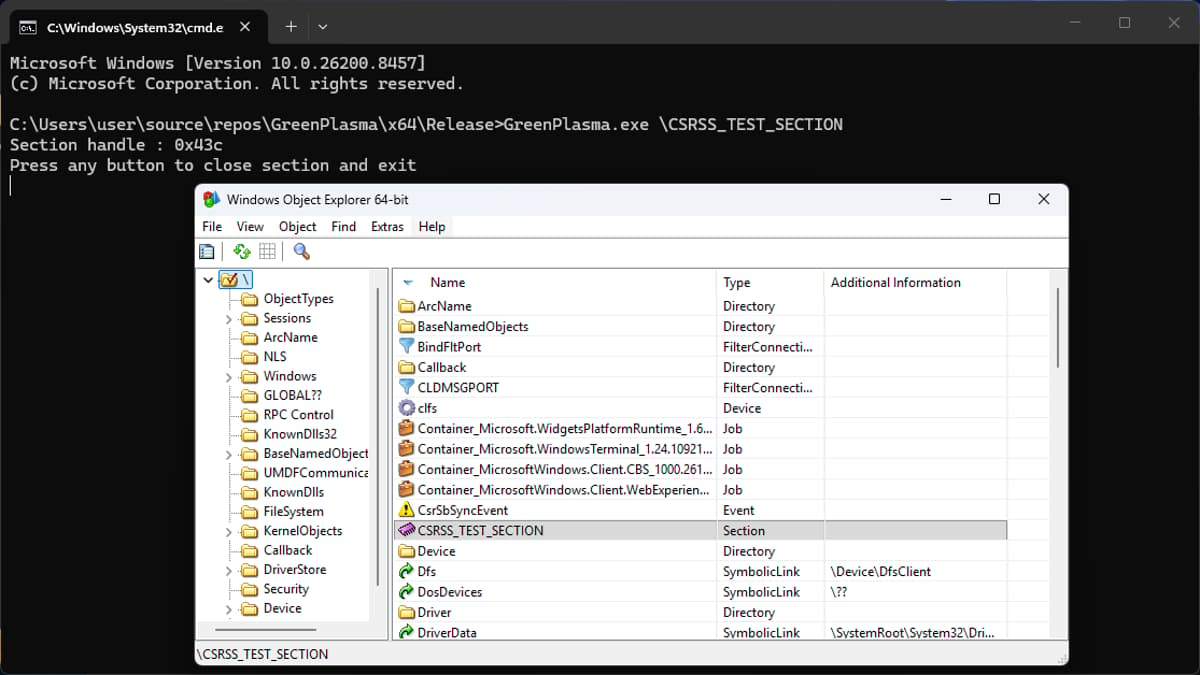
Researchers Uncover YellowKey and GreenPlasma Windows Zero-Days
Security researcher Chaotic Eclipse disclosed two fresh Windows zero‑days, YellowKey and GreenPlasma. YellowKey lets attackers with physical access bypass BitLocker on Windows 11 and Windows Server 2022/2025 by planting crafted files in the WinRE image. GreenPlasma targets the CTFMON framework, enabling privilege...

Security Researchers Use Anthropic’s Mythos AI Model to Crack Apple’s macOS
Security firm Calif leveraged Anthropic’s Mythos generative‑AI model to uncover two memory‑corruption bugs in Apple’s macOS, enabling a privilege‑escalation exploit that can seize control of a machine. The researchers demonstrated that Mythos not only identified the vulnerabilities but also assisted...

U.S. CISA Adds a Flaw in Cisco Catalyst SD-WAN to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added Cisco Catalyst SD‑WAN vulnerability CVE‑2026‑20182 to its Known Exploited Vulnerabilities (KEV) catalog. The flaw, rated a perfect 10.0 on the CVSS scale, lets an unauthenticated remote attacker bypass peering authentication,...
Broadcom Releases VMware Fusion Security Update for Root Access Bug
Broadcom has issued a security update for VMware Fusion that fixes a high‑severity TOCTOU flaw (CVE‑2026‑41702). The vulnerability allowed a local, non‑administrative user to elevate privileges to root on macOS systems running Fusion. The patch arrives as Broadcom participates in...

NGINX Rift: An 18-Year-Old Flaw in the World’s Most Deployed Web Server Just Came to Light
Security researchers at depthfirst disclosed NGINX Rift (CVE‑2026‑42945), a critical heap buffer overflow that has existed in the NGINX codebase for 18 years. The flaw lives in the ngx_http_rewrite_module and can be triggered by a common rewrite pattern that mixes...

How AI Is Silently Rewriting the Rules of Cyber Attacks
Artificial intelligence is reshaping cyber threats, allowing attackers to automate zero‑day discovery, craft polymorphic malware, and launch AI‑driven supply‑chain attacks such as the “Shy Hulud” worm. Nations like China, Russia and North Korea are integrating AI into espionage and infrastructure...
Quiet Warfare: Bending Data and Perceptions in the Defense Industrial Base
Artificial intelligence is reshaping the threat environment for the U.S. Defense Industrial Base (DIB), where adversaries now run hybrid campaigns that blend cyber intrusion, supply‑chain manipulation, and information operations. The World Economic Forum’s 2026 Global Cybersecurity Outlook flags AI‑related vulnerabilities...

Q&A: Why Vulnerability Scans Are Giving Businesses a False Sense of Security
In a recent interview, cybersecurity veteran Phillip Wylie warns that reliance on vulnerability scans and basic phishing tests gives organizations a false sense of security. He highlights how attackers now target overlooked assets such as security cameras, printers, and other...
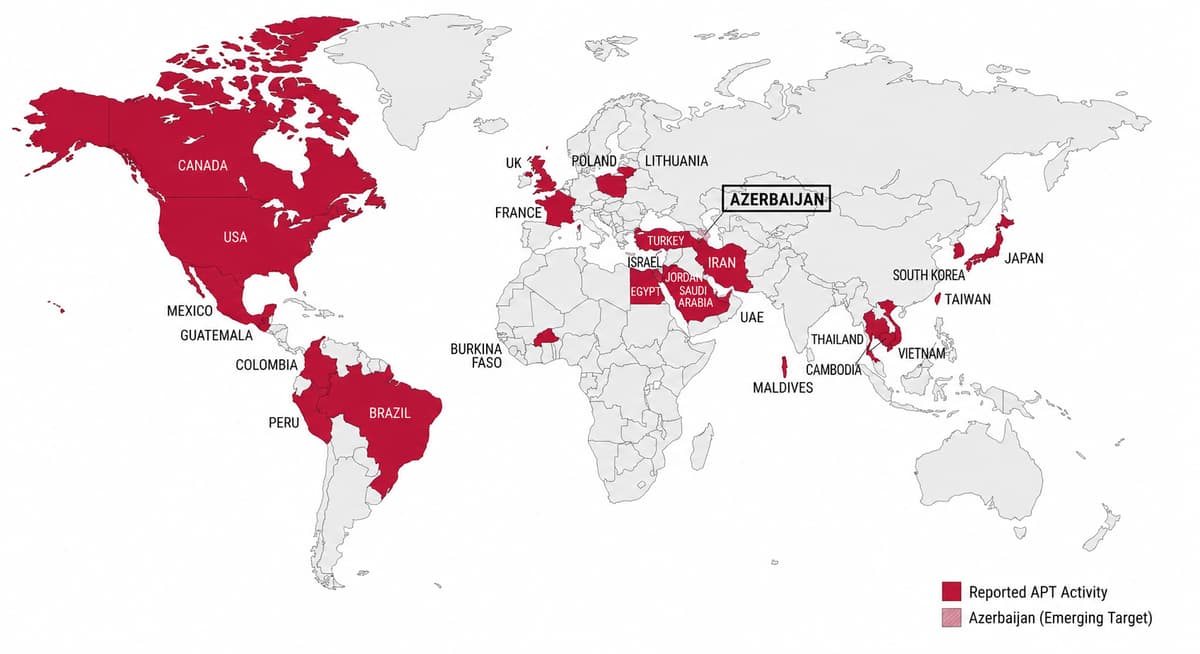
FamousSparrow Targets Azerbaijani Energy Sector in Multi-Wave Espionage Campaign
Chinese‑linked APT group FamousSparrow launched three intrusion waves against an Azerbaijani oil and gas firm from Dec 2025 to Feb 2026, repeatedly exploiting a vulnerable Microsoft Exchange server via the ProxyNotShell chain. The campaign deployed evolving payloads—Deed RAT, an attempted Terndoor backdoor,...

Pentagon Deploys Anthropic’s Mythos AI in “National Security Moment” Despite Blacklisting the Firm as a Supply-Chain Risk
The Pentagon has begun deploying Anthropic’s unreleased Mythos AI model to hunt for and patch software vulnerabilities across U.S. government systems. Mythos, part of the controlled Project Glasswing effort, can uncover decades‑old flaws in browsers, infrastructure and other code. The move...

OpenLoop Health Confirms January 2026 Data Breach Affecting 716,000
OpenLoop Health, a telehealth infrastructure provider, confirmed a cyberattack in early January 2026 that exposed personal information of 716,000 individuals. The intrusion lasted from January 7 to 8, during which threat actors exfiltrated data but did not access electronic health...

CIRCIA Is Coming: What Government Contractors Need to Know About the Upcoming Cyber Incident Reporting Rules
The Cyber Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA) is moving toward final rulemaking, obligating over 300,000 entities—including many government contractors—to report major cyber incidents within 72 hours and ransomware payments within 24 hours to CISA. The rule,...

Fragnesia Made Public As Latest Linux Local Privilege Escalation Vulnerability
The open‑source security community has disclosed Fragnesia, a new Linux local privilege escalation (LPE) vulnerability that mirrors last week’s Dirty Frag bug. Fragnesia resides in the ESP/XFRM subsystem and enables arbitrary byte writes to the kernel page cache of read‑only files....

Quest KACE SMA Flaw CVE-2025-32975: When One Unpatched Tool Opens the Door to 60 Organizations
Quest KACE Systems Management Appliance (SMA) suffers a critical authentication‑bypass flaw (CVE‑2025‑32975) rated CVSS 10.0. The vulnerability lets an unauthenticated attacker impersonate any user, including administrators, via the SSO module. Although a patch was issued in May 2025, more than 12,000...

The Next Wave of Healthcare Cyber Risk, From IoMT to AI-Enabled Attacks
Healthcare cyber risk is evolving beyond ransomware and data breaches as connected medical devices, remote telehealth services, and cloud platforms expand the attack surface. Legacy equipment lacking modern security controls now coexists with IoT and OT, creating vulnerable footholds for...

10 Crypto Heavyweights Explain the Quantum Risk to Bitcoin
Google’s recent research paper demonstrates that a quantum computer with roughly 500,000 qubits could extract a Bitcoin private key from an exposed public key in about nine minutes—close to Bitcoin’s 10‑minute block interval. This estimate is far lower than earlier...
How to Protect Your Identity From AI, Doxxers, and Scammers
Recent concerns about AI models like Anthropic's Claude Mythos, which can exploit software vulnerabilities, have heightened awareness of identity‑theft risks. The blog post outlines practical operational‑security measures for individuals seeking to keep personal data separate from their online presence, emphasizing...

Are You Using the Right Security Controls for Agent 365?
Agent 365 is Microsoft’s centralized platform for governing AI agents, integrating tightly with Microsoft Purview, Entra and Defender. It enforces least‑privilege access, flags unauthorized data requests, and provides real‑time monitoring, automated workflows, and DSPM to close policy gaps. Incident response and...

WorkNest Launches WorkNest Secure to Expand Cybersecurity and Compliance Services
WorkNestGroup has launched WorkNest Secure, a new cybersecurity and compliance division that consolidates the capabilities of Pentest People and Bulletproof under a single brand. The division offers services ranging from penetration testing and incident response to vCISO, GDPR, ISO 27001, PCI DSS,...
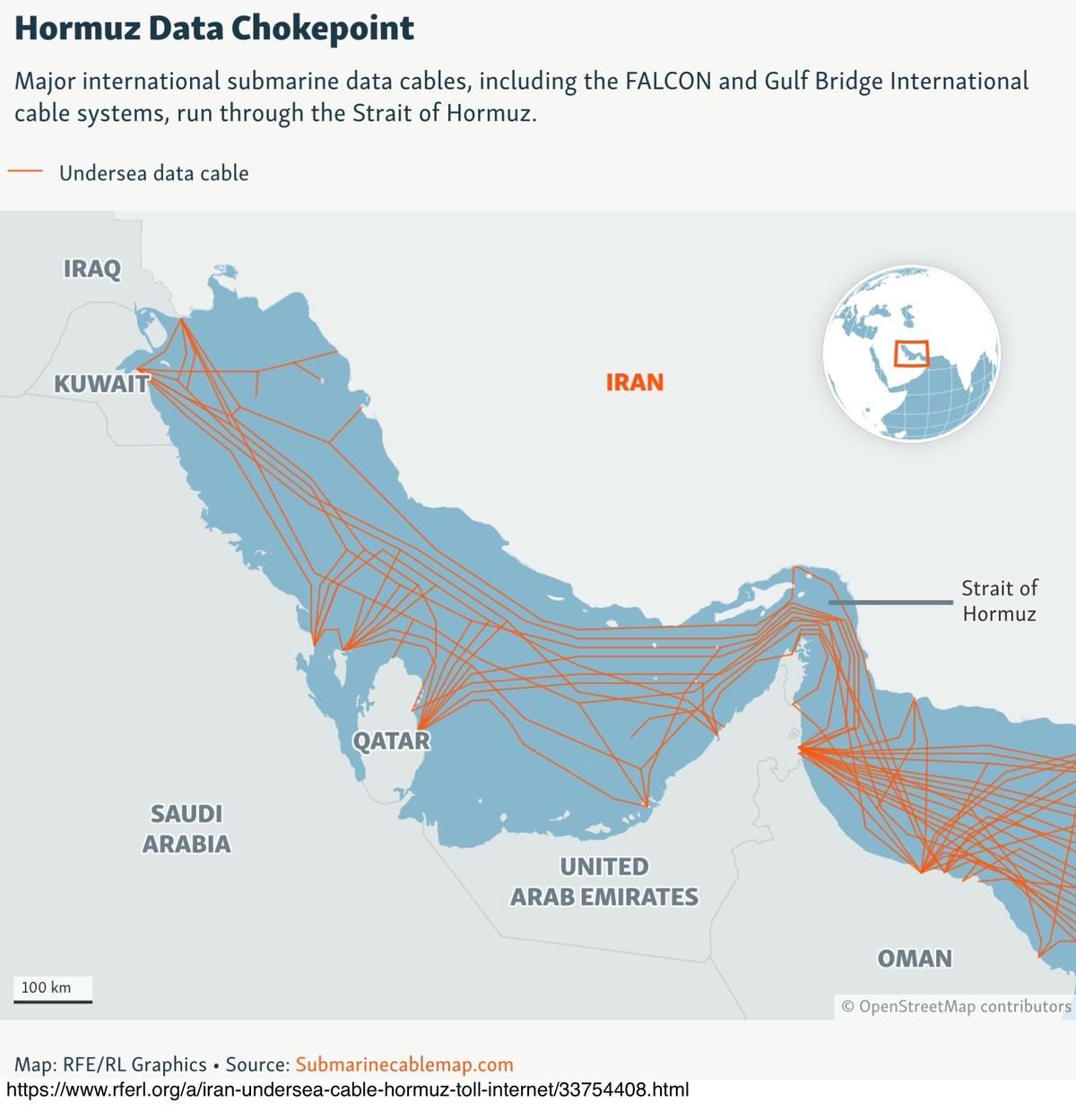
Hormuz Data Chokepoints and Iranian Threats Against Undersea Internet Cables
Iranian news agencies aligned with the IRGC have floated proposals to charge global tech firms for operating undersea fiber‑optic cables that cross the Strait of Hormuz. The plan leans on a selective reading of UNCLOS, arguing that the cables sit...

Pharmaceutical Cybersecurity and Risk Management: Q&A with Jamie Singer & Matt Flora
In a May 12, 2026 interview, FTI Consulting’s Jamie Singer and Matt Flora explain that pharmaceutical cyber threats have moved beyond ransomware to data extortion, supply‑chain attacks, and even executive harassment, while rapid AI adoption widens the attack surface. They identify recurring...
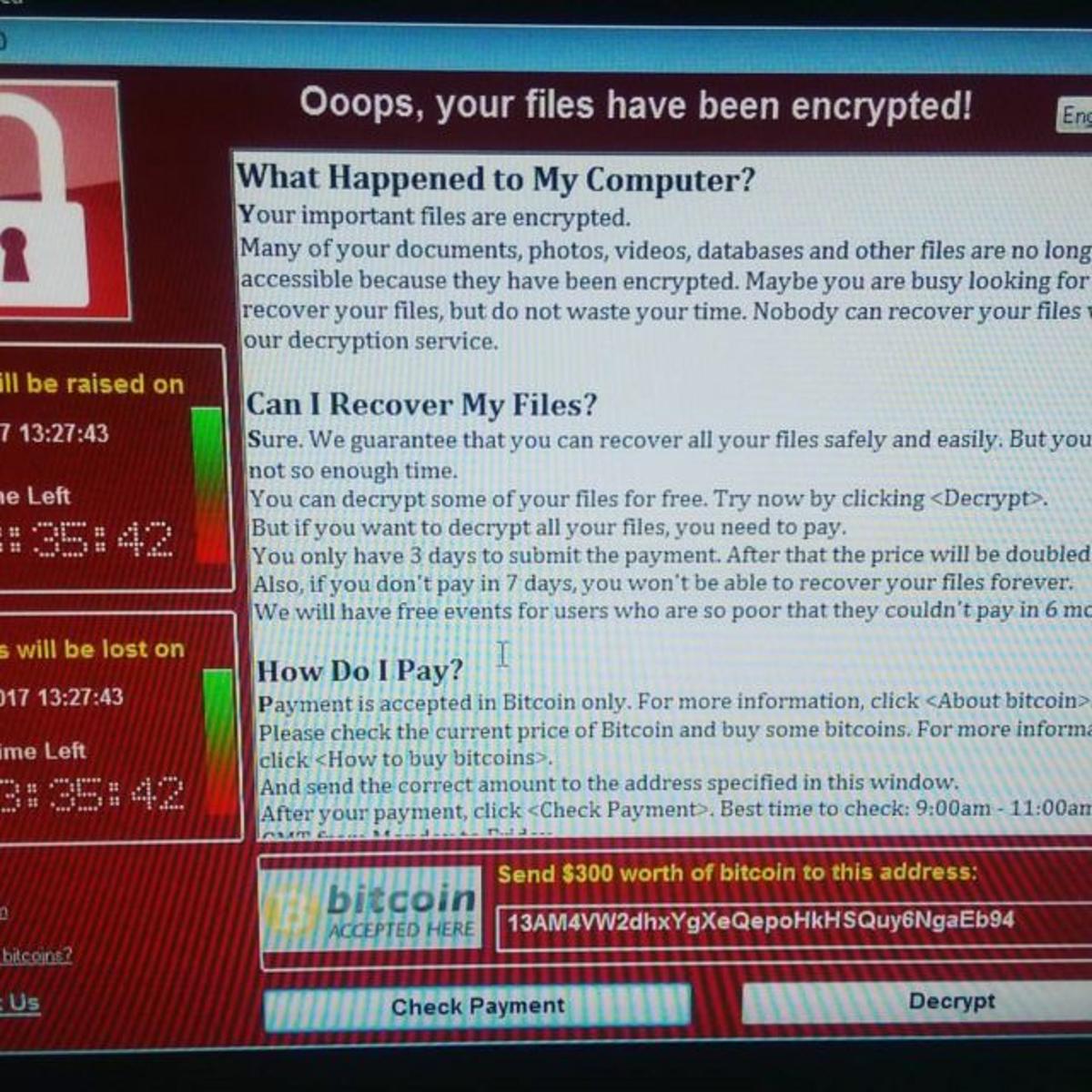
WannaCry, the Ransomware Attack that Changed the History of Cybersecurity
On May 12, 2017, the WannaCry ransomware leveraged the NSA‑derived EternalBlue exploit (CVE‑2017‑0144) to spread as a worm across Windows networks. Within hours it infected more than 200,000 computers in over 150 countries, crippling hospitals, telecoms and other critical infrastructure....
Lyrie.ai Deploys Real-Time Zero-Day Tracking Across Global Enterprise Infrastructure
Lyrie.ai, the cybersecurity platform from OTT Cybersecurity LLC, announced the deployment of a real‑time zero‑day tracking system that identifies and discloses active exploits to affected organizations within hours. The company also secured acceptance into Anthropic’s Cyber Verification Program, underscoring its...

Your iPhone-to-Android Texts Are Now Encrypted by Default
Google and Apple announced that end‑to‑end encrypted RCS messaging is now rolling out in beta for iPhone users on iOS 26.5 and Android users with the latest Google Messages. The encryption is enabled by default and displays a lock icon in the...
![[Sponsor] Drata](https://hixhlmpcokxhartfkpyi.supabase.co/storage/v1/object/public/images/thumbnails/53aafe558a60fe3a33da171d61fab781.webp)
[Sponsor] Drata
Drata is a compliance‑automation platform that connects to over 130 SaaS tools, enabling continuous evidence collection for more than 25 regulatory frameworks such as SOC 2, HIPAA, PCI and GDPR. The solution provides a library of 40+ auditor‑approved security policies that...

Repairing the RPKIViews H1 2026 Archives
RPKIViews repaired its H1 2026 archives after discovering a CCR ordering bug in older rpki‑client versions. Using a new rpkitouch repair feature, the team reprocessed 110 rpkispools, handling 190,601 CCRs and over 19 million RPKI objects. The effort compressed the dataset from...

Taken : This Is a Web Page that Shows How Much Data Your...
The new web tool Taken (sinceyouarrived.world/taken) reveals exactly what data a browser hands over the instant a page loads, without any cookies, logins, or prompts. By aggregating headers, canvas output, font lists, and hardware signals, the site demonstrates that a...
Canada’s Bill C-22 Is a Repackaged Version of Last Year’s Surveillance Nightmare
Canada’s Bill C-22, dubbed the Lawful Access Act, revives the failed Bill C‑2 by forcing digital services to retain a full year of metadata and expanding data‑sharing with foreign governments. The legislation authorises the Minister of Public Safety to demand...

OneLayer Unveils Certified Integrations to Strengthen Private Cellular Security Perimeter
OneLayer announced the Technology Alliance Program (TAP), a certified ecosystem that links its orchestration layer with third‑party private cellular routers, firewalls and other network components. Certified partners will appear in OneLayer’s affiliate directory and gain access to co‑marketing, workshop resources,...

GNOME's Help Viewer Updated Due To Flatpak Sandbox Escape Vulnerability
GNOME’s built‑in help viewer Yelp received a critical update (version 49.1) to close a Flatpak sandbox escape discovered during a security audit. The flaw let a malicious help file launch Yelp, using an SVG‑based CSS stylesheet to read arbitrary host files...

Google Warns Artificial Intelligence Is Accelerating Cyberattacks and Zero-Day Exploits
Google Cloud Threat Intelligence released a report warning that attackers are now leveraging artificial intelligence to accelerate cyber‑attacks, including the creation of AI‑generated zero‑day exploits. The research shows a clear shift from credential‑theft tactics to targeting software flaws, cloud APIs,...
Did the EU Parliament Really Vote Not to Protect Children Online?
In April 2026 the EU’s interim ePrivacy derogation – known as “Chat Control 1.0” – expired after the European Commission delayed its extension proposal and the Council refused Parliament’s privacy safeguards. The European Parliament voted to preserve its negotiating mandate...

Xinnor and the University of Utah’s SCI Institute Replace Aging PostgreSQL Backend with xiRAID
Xinnor’s xiRAID has replaced the University of Utah’s SCI Institute’s single‑drive PostgreSQL backend with a ten‑NVMe RAID10 solution, delivering a 2.65× boost in PostgreSQL 17 throughput and latency. The new system achieves 8.24 million read IOPS and 129 GB/s, roughly 39× more read...

AWS Security Digest #260 -
AWS released security bulletin 2026‑026 and five AL2023 live‑patches to address the Copy Fail kernel vulnerability (CVE‑2026‑31431), which can grant root on Linux instances from the past eight years. Live‑patches provide an immediate mitigation for customers who cannot reboot, while full kernel...

Crimenetwork Returns After Takedown, Dismantled Again by German Authorities
German police dismantled a revived version of the German‑language cybercrime marketplace Crimenetwork, which had amassed more than 22,000 users and over 100 sellers. The site generated over €3.6 million (≈$3.9 million) in revenue before being shut down, and authorities seized €194,000 (≈$210,000)...

U.S. CISA Adds a Flaw in BerriAI LiteLLM to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the critical LiteLLM flaw (CVE‑2026‑42208, CVSS 9.3) to its Known Exploited Vulnerabilities catalog. Attackers began exploiting the SQL‑injection bug within 36 hours of disclosure, targeting the proxy’s database tables that store API...

Cybersecurity: Briefing Your Board
The BCLP blog outlines a structured agenda for cybersecurity briefings to corporate boards, emphasizing the threat landscape, risk profile, AI implications, regulatory updates, and program status. It recommends private sessions between the board and the CISO to foster trust and...

Welcoming the Costa Rican Government to Have I Been Pwned
Have I Been Pwned (HIBP) has added Costa Rica as its 42nd government client for the free government‑focused breach‑monitoring service. The Costa Rican CSIRT now gains continuous visibility into compromised government email addresses, enabling faster identification of exposure and more...

LeakWatch 2026, Security Incidents, Data Breaches, and IT Situation for the Current Calendar Week 19
Calendar week 19 (4‑10 May 2026) saw a cascade of high‑profile security incidents spanning education, networking, mobile‑device management, software supply chains, cloud workloads, and critical‑infrastructure OT. Instructure’s Canvas platform suffered unauthorized access affecting student IDs and communications during exam season, while Palo Alto Networks...

Pete Recommends – Weekly Highlights on Cyber Security Issues, May 9, 2026
The UK Online Safety Act’s age‑verification tools are proving ineffective, with children easily bypassing checks, while the US government drafts policy to limit private‑sector AI contractors from dictating how their models are used in federal missions. In 2025, American consumers...

Meta Shuts Down End-to-End Encryption for Instagram DMs, Citing Low Opt-In Rates
Meta announced it will disable end‑to‑end encryption for Instagram direct messages on May 8, citing very low user opt‑in rates. The feature, which prevented anyone—including Meta, governments, and law‑enforcement—from reading messages, never gained traction. Users who still want encrypted chats are...
Microsoft Releases Azure Linux 3.0.20260506 With Many Security Fixes
Microsoft rolled out Azure Linux 3.0.20260506 on Saturday, bundling the latest security patches for a broad set of open‑source components. The update addresses vulnerabilities in Avahi, GNU Binutils, libssh, Node.js, Ruby, the Linux kernel, Rust and dozens of other packages. It...

Worth Reading 050926
The latest Worth Reading roundup highlights five pivotal tech developments. RPKI has matured into a core security layer, now protecting the majority of global IP routes. Amazon’s marketplace of third‑party sellers generated $117.7 billion in 2022, underscoring its economic weight. Additional...
![0.08% False Positive Rate That Masked a $4.2M Attack [Edition #8]](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://substackcdn.com/image/fetch/$s_!INXp!,w_256,c_limit,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F486d4b79-6177-4bf3-b025-c4abbc2aa8c4_944x944.png)
0.08% False Positive Rate That Masked a $4.2M Attack [Edition #8]
FinShield, a Series B fintech, expanded its cross‑border payment rails to 14 markets and now processes about 8 million transactions daily. Its real‑time anti‑abuse gateway uses an XGBoost‑NN ensemble retrained weekly on a 90‑day sliding window, delivering 45 ms P99 latency and 99.99%...

The Most Direct Social Engineering Propaganda You’ll EVER See
Channel 5’s new drama “The Teacher” features a classroom showdown where students demand immediate adoption of preferred pronouns and condemn Shakespeare as “triggering.” The scene, widely shared online, illustrates what the author calls overt social‑engineering through entertainment. The post links the...
Insider Trading Case Exposes Gaps in Law Firm Security | Reuters
A recent insider‑trading prosecution has revealed that law firms’ internal data controls are still vulnerable, despite heavy investment in cyber defenses. The case shows that a partner’s access to confidential client files can be leveraged for illicit market activity. Firms...

It’s A Dirty Frag Frag Friday
A new Linux zero‑day called Dirty Frag has been disclosed, allowing local attackers to obtain root privileges on most major distributions with a single command. The exploit chains two separate kernel flaws, mirroring the technique used in the earlier Dirty Pipe and...