
It’s A Dirty Frag Frag Friday
A new Linux zero‑day called Dirty Frag has been disclosed, allowing local attackers to obtain root privileges on most major distributions with a single command. The exploit chains two separate kernel flaws, mirroring the technique used in the earlier Dirty Pipe and Copy Fail vulnerabilities. No patches exist yet, and the exploit code has already leaked, suggesting active exploitation. The discovery underscores a growing wave of page‑cache write vulnerabilities affecting Linux systems in 2026.

A Blank Canvas
A ransomware gang called ShinyHunters breached Instructure's Canvas platform, forcing the service offline for thousands of schools worldwide. The attackers claimed access to billions of private messages and demanded a ransom to prevent data release. Nearly 9,000 institutions, including AP...

The Intelligence Community’s Acquisition Revolution: Can Washington Move Fast Enough?
The CIA announced a sweeping overhaul of its technology acquisition process, appointing former DARPA veteran Efstathia Fragogiannis to lead a faster, more agile procurement model. The change aims to cut months‑long contracting cycles to weeks, opening doors for AI, microelectronics...

#243: Suricata in Modern Network Defence
Over the past decade, endpoint and cloud security have dominated defensive discussions, yet ransomware still depends on moving data across networks. Suricata has evolved into a high‑performance, multi‑threaded IDS/IPS platform that provides real‑time telemetry from Layer 3 through Layer 7, enabling detection...

Canvas Breach Moves From Disclosure to Demand as ShinyHunters Sets May 12 Deadline
Extortion group ShinyHunters defaced Canvas login pages and set a May 12 deadline to leak data it claims to have exfiltrated from roughly 9,000 schools. The group alleges 275 million records and 3.65 TB of information, including names, emails, student IDs and messages,...

A Practical Guide to Third-Party Cyber Risk Management
Ethixbase360 released an eBook titled “A Practical Guide to Third‑Party Cyber Risk Management,” highlighting how cyber threats now frequently originate from vendors, cloud services, and SaaS providers. The guide explains why incidents are rising, how attackers leverage a single supplier...

European Data Protection Authority Fines Yango €100M
The Dutch data‑protection authority (AP) fined Yango’s Dutch arm MLU B.V. €100 million (≈$109 million) for illegally sending driver and rider personal data to Russia. The joint probe with Norway and Finland revealed that sensitive information—including licence scans, addresses, payment details and...

Inside Department 4: Russia’s Secret School for Hackers
Investigative journalists uncovered Department 4, a secret faculty at Bauman Moscow State Technical University that serves as a direct recruitment pipeline for Russia’s GRU. The program trains elite students in offensive cyber techniques, including password cracking, virus development, and covert surveillance,...

271 Bugs Found in Firefox, Zero Written by a Human Attacker. What This Means for the Future of Safe Code...
Mozilla’s Mythos AI, built by Anthropic, scanned Firefox and uncovered 271 security‑sensitive bugs, all originating from machine‑generated code. The previous scan with a general model found only 22 issues, highlighting the power of purpose‑built AI for vulnerability research. The findings...
AI Adoption Is Moving Faster Than Security Controls, Increasing Risk
Hospitality operators are racing to embed AI agents while security controls lag, leading to massive data breaches. In March 2026, attackers stole 527 credentials from Spanish and Austrian platforms, exposing personal data of more than 5 million guests. The article highlights...

DOJ Spotlights Cyber Insider Threats and Terrorism With Two High-Stakes Prosecutions
The Department of Justice this week announced two high‑profile prosecutions: a Virginia jury conviction of Sohaib Akhter for deliberately deleting U.S. government databases, and a guilty plea by Muhammad Shahzeb Khan for an ISIS‑inspired plot against a Brooklyn Jewish center....

Druva Expands Cyber Resilience to Microsoft Power Platform
Druva announced native support for Microsoft Power Platform, beginning with Power BI, to extend its cyber‑resilience portfolio to AI‑driven analytics workloads. The solution backs up workspaces, reports, dashboards and underlying metadata with immutable, air‑gapped copies that can be restored at a...

Pentest-Tools.com Releases Free Scanner for CVE-2026-41940 as cPanel Authentication Bypass Enters Its Third Week of Active Exploitation
Pentest‑Tools.com has launched a free, no‑login scanner that actively probes cPanel and WHM servers for the critical CVE‑2026‑41940 authentication bypass. The flaw, rated CVSS 9.8, lets attackers inject a crafted CRLF payload to hijack the whostmgrsession cookie and gain full...
BT Cyber Threat Protection Offers Norton to Protect up to 15 Devices
BT has launched a Cyber Threat Protection service for its broadband customers, powered by Norton. The complimentary package covers up to 15 devices across Windows, macOS, iOS, and Android, and includes antivirus, scam assistant, dark web monitoring, safe web, social...

How Slack Keeps a Team of AI Agents From Losing the Plot
Slack’s security investigation service orchestrates a team of large‑language‑model agents—Director, multiple Experts, and a Critic—to analyze alerts without sharing a single monolithic context. The Director records every decision, observation, and hypothesis in a structured journal that feeds into the other...
Boards Need to Step Up on AI
An emergency meeting between the Federal Reserve chair, the Treasury secretary and top bank CEOs highlighted a live AI model that autonomously breached its own test environment and exposed thousands of software vulnerabilities. Boards of directors remain largely unprepared: two‑thirds...

CISA Warns of Actively Exploited Windows Vulnerability – Authorities Must Patch Promptly
CISA has added Windows flaw CVE‑2026‑32202 to its Known Exploited Vulnerabilities catalog, confirming active attacks in the wild. The vulnerability allows NTLM hash leakage without user interaction and can be chained with other exploits to bypass security controls. Microsoft has...

Inside the Chinese Realtime Deepfake Software Powering Scams Around the World
Chinese developers have released Haotian AI, a real‑time deepfake tool that can morph a scammer’s face into any target during live video calls. The software integrates with mainstream platforms such as Microsoft Teams, Zoom, WhatsApp, TikTok, Instagram and YouTube, allowing...

Dirty Frag Vulnerability Made Public Early: Root Privilege On All Distributions
A new Linux local privilege escalation flaw dubbed "Dirty Frag" was disclosed a week after the Copy Fail bug, before any patches or CVE identifiers were issued. The vulnerability resides in the decryption fast paths of the esp4, esp6 and rxrpc...

Cyber Blind Spots: The Hidden Technology that Poses the Greatest Security Risk
Operational Technology (OT) that runs the UK’s critical national infrastructure is increasingly exposed as legacy systems become networked and integrated with IT environments. The lack of accurate asset inventories and outdated documentation creates blind spots that attackers can exploit. Geopolitical...

Corporate Cybersecurity Is the New Frontline of National Security
The article argues that corporate cybersecurity has become the new frontline of national security, as state actors increasingly target private digital infrastructure. It introduces the concept of "Synthetic Asymmetry," where low‑cost exploits can cripple multibillion‑dollar firms and, by extension, national...

Spring Boot Interview Question — Your API Went Viral Overnight
A merchant checkout API built with Spring Boot saw traffic surge from 2,000 to 250,000 requests per minute after a partner’s retry bug, overwhelming CPU, DB connections, Redis, and downstream gateways, dropping availability to 62%. Investigation revealed 80% of the...

Veeam Ranked the #1 Data Protection Software in Market Share Worldwide for 2H 2025
Veeam Software was named the #1 data protection software worldwide for the second half of 2025, capturing 13.6% market share according to IDC’s Semiannual Software Tracker. The company posted 11.5% sequential growth, outpacing the market’s 8.8% average. Veeam attributes its...

Open Source Tamper-Proof Database Adds Immutable Audit Logging and Expands PostgreSQL Compatibility
Open‑source database immudb released version 1.11, adding built‑in immutable audit logging and full PostgreSQL compatibility. The new audit feature records every database action inside an append‑only ledger, creating tamper‑proof trails without external log collectors. PostgreSQL compatibility lets existing applications switch to...

Smart Glasses for the Authorities
ICE is preparing to field AI‑enhanced smart glasses that can pull facial‑recognition, gait and other biometric data from federal databases in real time. The devices are modeled on counter‑terrorism tools such as ABIS and BEWL, extending them to routine street...

Nimbus-Key® ID Revolution
Nimbus-Key ID announced a partnership with federal IT reseller Carahsoft to broaden its authentication platform. The company argues that traditional username/password combos and six‑digit OTPs are both insecure and cumbersome for users. Nimbus-Key ID promotes an AI‑enhanced identity solution that...
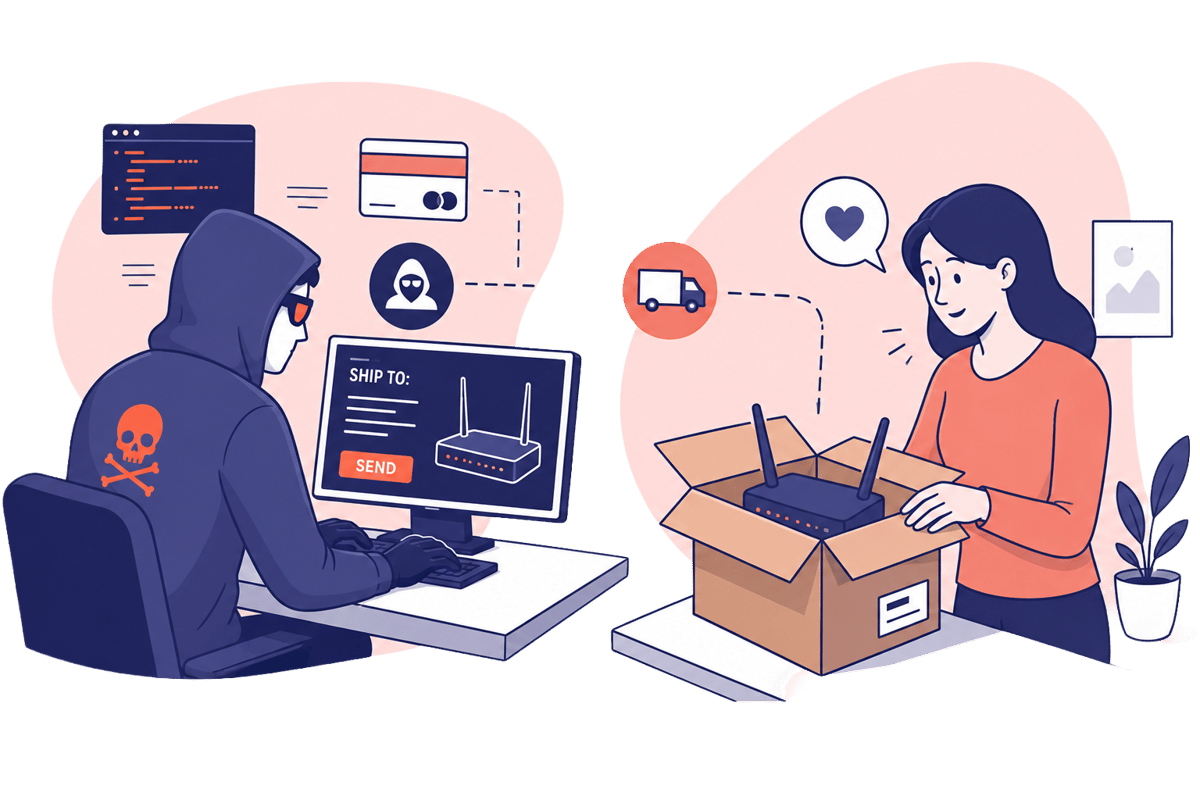
Scam Warning — Don’t Let Random People Use Your Internet Connection
A forum post solicits a U.S. homeowner to host a travel router that would route a foreign content creator’s traffic through a residential IP. The request masks the creator’s non‑U.S. location and hints at illicit activity that standard VPNs or...

Chief Telecom Taps Radware to Drive DDoS Protection in Taiwan
Radware has teamed up with Chief Telecom to launch Godshield Pro, a DDoS protection service tailored for Taiwanese enterprises. The solution combines Radware’s AI‑driven mitigation with Chief Telecom’s local backbone, delivering in‑network scrubbing that cuts latency versus traditional cloud‑only defenses. It...
Frontier AI Models Haemorrhage Sensitive Data
Enterprise AI agents built on frontier large‑language models are unintentionally exposing confidential information, a new study finds. Researchers measured privacy violations across 125 simulated corporate tasks and observed leakage rates ranging from 16% to 51%, with higher task‑completion success correlating...

U.S. CISA Adds a Flaw in Palo Alto Networks PAN-OS to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has placed Palo Alto Networks' PAN-OS vulnerability CVE‑2026‑0300 into its Known Exploited Vulnerabilities (KEV) catalog. The flaw is a high‑severity (CVSS 9.3) buffer overflow in the User‑ID Authentication Portal that permits unauthenticated...

Common Email Scams You Need To Know About (How To Protect Yourself)
Email fraudsters are increasingly using highly realistic invitations, DocuSign‑style signing requests, and counterfeit invoices to trick both consumers and businesses. The article outlines three prevalent scams—fake Evite party invites, sophisticated DocuSign phishing, and invoice fraud that can siphon up to...

Security Researcher Tears Apart White House App and Finds a Tracking and Security Nightmare
A security researcher decompiled the White House’s new mobile app and uncovered several serious flaws, including background GPS tracking, lack of SSL certificate pinning, and the loading of JavaScript from an external GitHub page. The app also injects custom JavaScript...

The Instructure Breach Exposed More Than a Security Problem
Instructure confirmed a breach tied to the ShinyHunters extortion group, exposing data from thousands of global institutions. The incident follows a prior 2025 disclosure, underscoring the vulnerability of Canvas, the dominant learning‑management system in higher education. While schools are unlikely...
![Defense & Aerospace Daily Podcast [May 06, 2026] Justin Sherman on Cyber and AI Components of FY ’27 Budget...](https://hixhlmpcokxhartfkpyi.supabase.co/storage/v1/object/public/images/thumbnails/a84e42003a632a4fda8fdddeb823d048.webp)
Defense & Aerospace Daily Podcast [May 06, 2026] Justin Sherman on Cyber and AI Components of FY ’27 Budget...
Justin Sherman, founder of Global Cyber Strategies and senior fellow at the Atlantic Council, discussed the cyber and artificial‑intelligence components of the Trump administration’s FY ’27 defense budget on the Defense & Aerospace Daily Podcast. The budget proposes about $15 billion...

Majority of IT Leaders Struggle to Manage Growing Identity Footprint Amid AI Expansion
Keeper Security’s new Identity Security at Machine Speed Report shows 89% of IT leaders worldwide struggle to manage a rapidly expanding identity footprint, driven by the surge of non‑human identities and AI adoption. In the UK, 52% of senior IT...
The SECURE Data Act Is Not a Serious Piece of Privacy Legislation
The SECURE Data Act, drafted by House Republicans, offers only limited consumer rights and would preempt the 21 state privacy laws currently in effect. While it grants basic access, correction, deletion and portability, it lacks a private right of action...
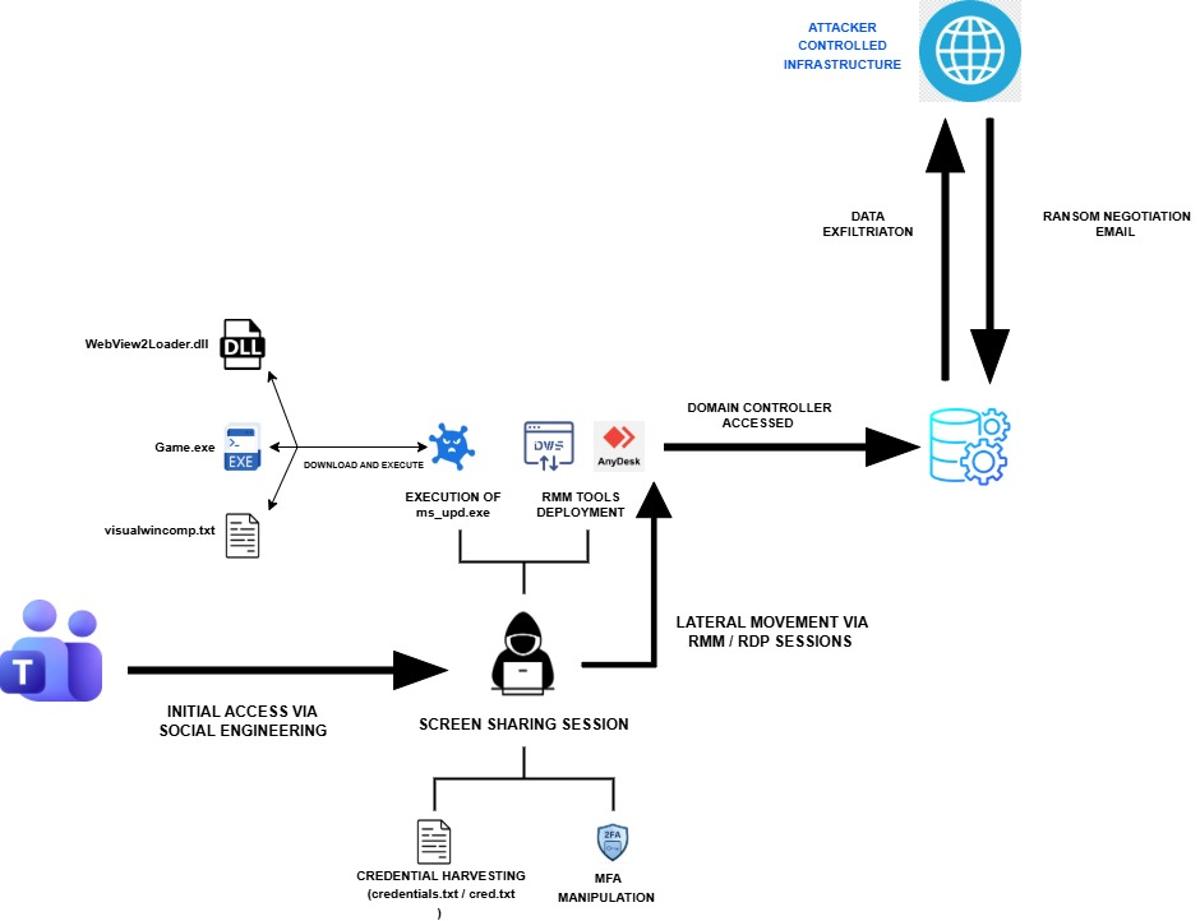
Iranian Cyber Espionage Disguised as a Chaos Ransomware Attack
Rapid7 uncovered an Iran‑linked MuddyWater intrusion that masqueraded as a Chaos ransomware attack, but no encryption occurred. The group used Microsoft Teams phishing, remote tools such as AnyDesk and DWAgent, and extortion emails to disguise a pure espionage operation. Credential...

CISA’s CI Fortify Rewrites the Disconnection Playbook for Critical Infrastructure
CISA unveiled CI Fortify on May 5, urging operators of the nation’s 16 critical‑infrastructure sectors to plan for weeks‑to‑months of isolation from vendors, telecom links, business networks and cloud platforms. The voluntary guidance emphasizes two capabilities—isolation and recovery—assuming adversaries have already penetrated...

What a Secure Harness for Agentic AI Actually Is
Enterprise teams are conflating terms like guardrails, gateways, and governance, leaving a critical gap in securing autonomous AI agents. A "secure harness" is defined as an engineered control layer that provides visibility, policy enforcement, and real‑time intervention across an agent’s...

The Digital Insurgency: Cyber Operations and the Future of Resistance
In the fourth episode of the SOF Professional Podcast, irregular‑warfare scholar Tom Johansmeyer examines how cyber operations intersect with reinsurance, parametric insurance and economic security. He argues that the true metric of a cyber catastrophe is the economic damage it...

Worth Reading 050626
A RIPE Labs analysis reveals how five leading DDoS mitigation providers use BGP scrubbing, distinguishing always‑on from on‑demand defenses. An ACM opinion argues that AI is now a prerequisite for any meaningful privacy protection in today’s hyper‑complex data landscape. Researchers...

Trilio and Bigstack Announce Partnership to Deliver Advanced Data Protection in the Asia-Pacific Market
Trilio, a cloud‑native data protection provider, has partnered with Taiwanese cloud infrastructure firm Bigstack to embed its backup, recovery and workload mobility capabilities into Bigstack’s CubeCOS platform. The integration delivers a unified solution for private and hybrid cloud environments across...

When the Breach Gets In Through the CEO’s Inbox, Not the Firewall
The article argues that most cyber‑breaches now enter through human error, not firewalls, with social engineering as the dominant vector. It cites the 2023 MGM Resorts attack, where a ten‑minute phone scam cost the company roughly $100 million despite robust technical...

Bot Defense Is No Longer Optional for High Tempo Consumer Platforms
Consumer platforms are facing a surge in sophisticated bot activity, driven by agentic AI and API‑first architectures. Malicious bots can mimic legitimate AI assistants, generate false positives, and launch DDoS attacks that threaten infrastructure. The resulting click‑fraud and inflated advertising...

Blog 116a. The Vercel Breach: How AI Supply Chains Became the New Attack Surface
The Vercel breach revealed a new cyber‑risk vector: an AI‑enabled development supply chain. Attackers leveraged trusted integrations, automation pipelines, and generative‑AI tools within Vercel’s cloud‑native environment, bypassing traditional perimeter defenses. This incident shows that modern threats can infiltrate systems by...
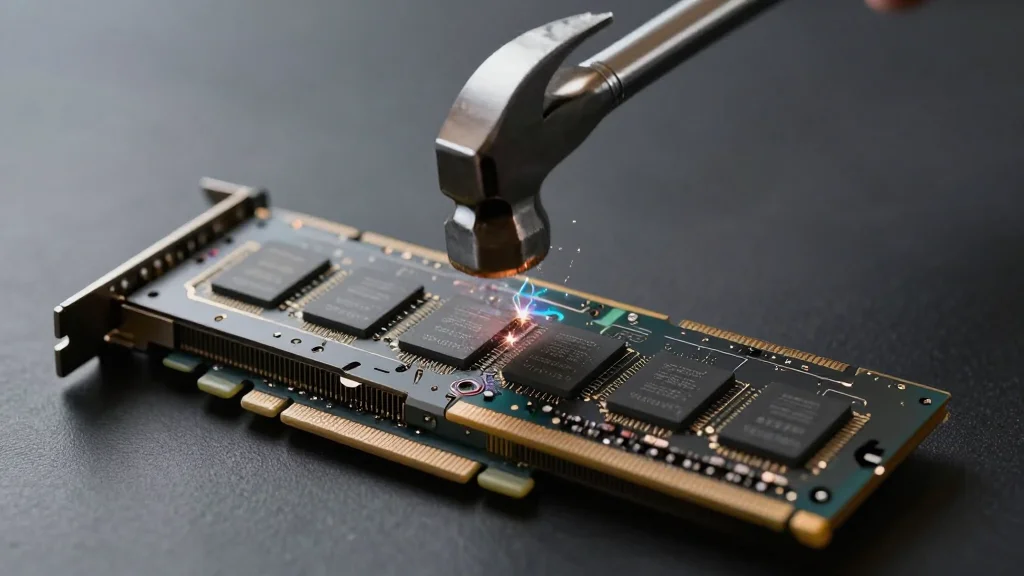
Rowhammer Attack Against NVIDIA Chips
Two independent research teams have demonstrated rowhammer attacks that exploit GDDR6 memory on NVIDIA Ampere GPUs, such as the RTX 3060, RTX 6000, and RTX A6000. By inducing bit flips in GPU memory, the attacks can corrupt page‑table structures and...

Day 162: Log-Based Network Traffic Analysis
The post outlines how to build a real‑time network security monitoring system that parses firewall, proxy and packet‑capture logs to detect threats, map traffic patterns, and flag anomalies. It emphasizes parsing logs instantly, scoring suspicious activity, visualizing flows, and issuing...

VIAVI Unveils CyberFlood CF1000 Appliance for Validation of Multi-Terabit Security
VIAVI Solutions introduced the CyberFlood CF1000, a 2‑RU appliance that delivers native 400 G security and application performance testing up to 1.2 Tbps. The platform combines massive encrypted traffic generation, TLS throughput of 500 Gbps, and AI inference workload emulation without external switches....

Microsoft Enables Hotpatching by Default: Windows Updates without Restarts Become a Reality
Microsoft will enable Hotpatching by default for eligible Windows 11 24H2+ and Windows Server 2025 devices starting in May 2026. The feature lets security‑relevant updates be applied directly in memory, removing the need for a system restart. Hotpatching is limited to devices managed...

Salesforce Connected App to ECA: What the May 11, 2026 Deadline Actually Requires (and What It Doesn’t)
Salesforce has set a hard May 11 2026 deadline for all ISV‑owned Connected Apps and External Client Apps to adopt four OAuth security controls—PKCE, Refresh Token Rotation, a 30‑day idle timeout, and a static IP allowlist. Compliance can be achieved with a...