
Worth Reading: Ephemeral BGP Leaks
Doug Madory’s APNIC blog post argues that transient BGP leaks observed during the path‑hunting phase after a route withdrawal are harmless and can be ignored. The response counters this view, calling the leaks a “dead canary” that signals weak route‑policy enforcement in the autonomous systems that propagate them. Although the leaks disappear once the withdrawn route is replaced, they reveal that an AS may still advertise bogus routes under normal conditions. Dismissing them could mask vulnerabilities that attackers might exploit.

The AI Phishing Revolution: From Spray-and-Pray to Autonomous Operations
AI is reshaping phishing from manual, spray‑and‑pray tactics to fully autonomous operations. Large language models now generate convincing spear‑phishing emails in minutes, while "vibe coding" fuels Phishing‑as‑Service platforms that auto‑write code, obfuscate payloads, and spin up infrastructure. Autonomous agents scrape...

ECB Urges Banks to Tackle AI Security Threats
The European Central Bank convened an emergency meeting with the eurozone’s 111 largest banks to warn of AI‑driven cyber threats, singling out Anthropic’s Claude Mythos Preview as a high‑risk model. Industry data shows 67% of financial firms are accelerating AI...

AI Coding Tools Are Widening the Security Validation Gap, Survey Finds
New research from Pentest‑Tools.com shows AI coding tools are outpacing security validation, creating a widening gap between code generation speed and vulnerability testing. Only 9% of developers feel testing keeps up, while 51% discover flaws after deployment. The survey of...
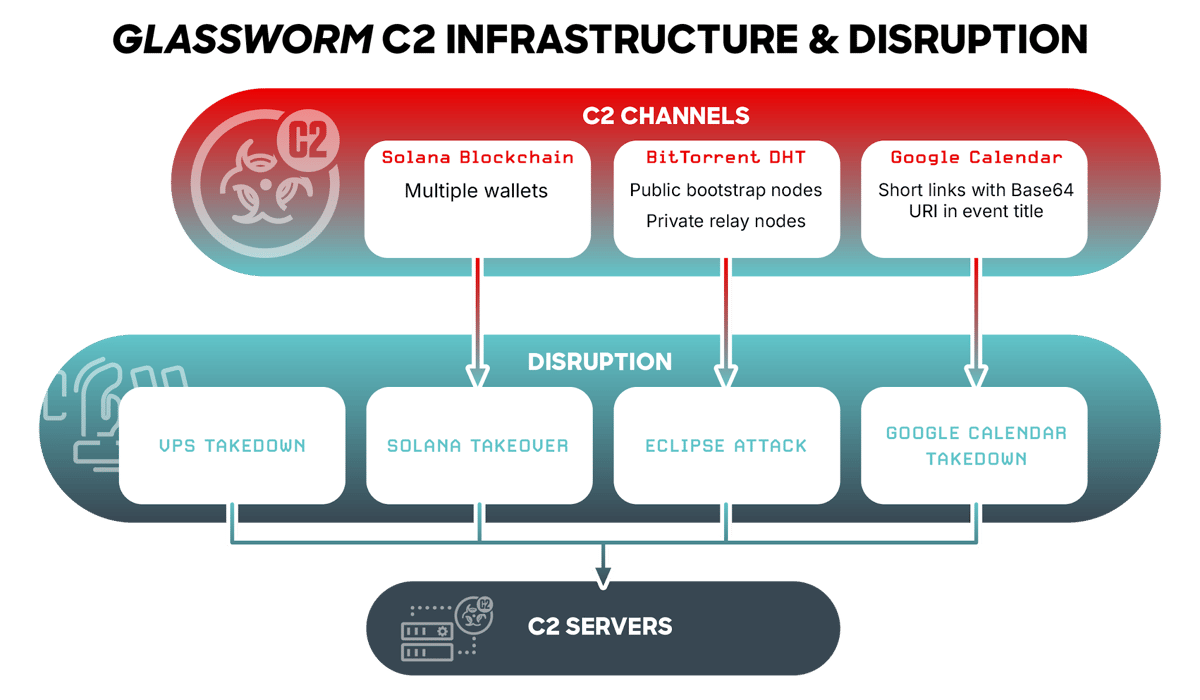
How Cybersecurity Firms Took Down Glassworm Botnet in One Shot
On May 26, 2026, CrowdStrike’s Counter Adversary Operations team, together with Google and the Shadowserver Foundation, simultaneously shut down all four command‑and‑control (C2) channels of the Glassworm botnet. The malware, which has been targeting software developers through poisoned npm packages,...

Blog 119a. Healthcare’s AI Revolution Is Creating a Cybersecurity Emergency.
Healthcare’s rapid AI adoption is reshaping clinical workflows, from diagnosis to billing, but the technology also introduces a sprawling cyber‑risk landscape. Hospitals now rely on AI‑driven imaging, predictive analytics, and automated patient communication, making vast datasets and algorithms integral to...

Most Organisations Can’t See Their AI Traffic and Attackers Are Already Exploiting That
Check Point’s 2026 Cloud Security Report reveals a stark gap between AI adoption and security readiness. While 77% of organizations have updated their security strategies for AI, only 26% possess the architecture to enforce them, leaving a 51‑point disconnect. Visibility...

BitGo Completes Quantum MPC Simulation with FIPS 204 Standard
BitGo Holdings and Silence Laboratories have completed the first post‑quantum multi‑party computation (MPC) transaction simulation run by a regulated custodian. The demo leveraged Silence Labs’ new PQ‑MPC protocol built on the NIST‑approved ML‑DSA signature algorithm standardized in FIPS 204, and was...

Salesforce MFA Requirements June 2026
Salesforce announced that, starting June 2026, all users must adopt phishing‑resistant multi‑factor authentication (MFA). The mandate applies to every login, including admin and standard accounts, and excludes SMS‑based codes in favor of hardware tokens or authenticator apps. A free step‑by‑step...

Security Roundup May 2026
Verizon’s 2026 Data Breach Investigations Report reveals that exploiting software vulnerabilities has become the leading cause of breaches, surpassing stolen credentials for the first time. The study of 31,000 incidents shows only 26% of CISA‑listed known‑exploited flaws were patched, a...

Non-Human Identity for Workloads and AI Agents
Non‑human identity (NHI) is moving from long‑lived passwords and API keys to short‑lived, machine‑issued credentials that rotate in minutes. Emerging solutions use public‑private key pairs issued via certificate authorities, TPM‑backed hardware, or software generation, keeping keys in memory rather than...

Third-Party Cyberattack Impacts Patient Information at The Oncology Institute
The Oncology Institute announced that a third‑party software vendor, likely Cognizant‑owned TriZetto, suffered a cyberattack that exposed patient information. The breach, first disclosed in November 2025, was confirmed on May 20, 2026 when Kroll, the vendor’s third‑party administrator, reported unauthorized...

SolarWinds Hack Was More Humiliating for the Government Than We Thought
New Bloomberg reporting, based on a Freedom of Information Act release of the Treasury inspector‑general’s redacted investigation, confirms that the Russian‑linked group behind the 2020 SolarWinds supply‑chain breach accessed email accounts inside the U.S. Treasury Department and could operate without...

AWS Security Digest #262 - Not Private
The May 25 AWS Security Digest warns that a CISA contractor accidentally exposed high‑privilege GovCloud keys on a public GitHub repo, remaining active for 48 hours after discovery. A new wave of supply‑chain attacks, the TeamPCP npm worm, infected Alibaba’s @antv data‑viz suite...

Zero-Click WhatsApp Account Takeover Hits iPhone Users Running iOS 16. No Linked Devices, No Warning
Italian forensic firm Forenser uncovered a zero‑click attack that hijacked WhatsApp accounts on iPhones running iOS 16. The exploit leverages CVE‑2025‑43300 in Apple’s ImageIO framework and CVE‑2025‑55177 in WhatsApp’s sync code to steal session keys without any user interaction. Compromised devices...

What Corporate Boards Need to Know and Do About Anthropic’s Mythos and Project Glasswing
Anthropic unveiled Claude Mythos Preview, an AI model that discovers thousands of high‑severity vulnerabilities, and launched Project Glasswing to give select critical‑infrastructure firms defensive access. The controlled release aims to shift the attacker‑defender balance by providing unprecedented visibility into latent...

LeakWatch 2026, Security Incidents, Data Breaches and IT Situation for the Current Calendar Week 21 – Pentecost, Fake Voices and...
Calendar week 21 (May 19‑25 2026) was defined by a wave of trust‑based attacks rather than single high‑profile leaks. Phishing campaigns timed with the Pentecost holiday duped users of PayPal, SecureGO, easybank and the Deutschlandticket, while the Storm‑2949 group abused Self‑Service Password Reset...
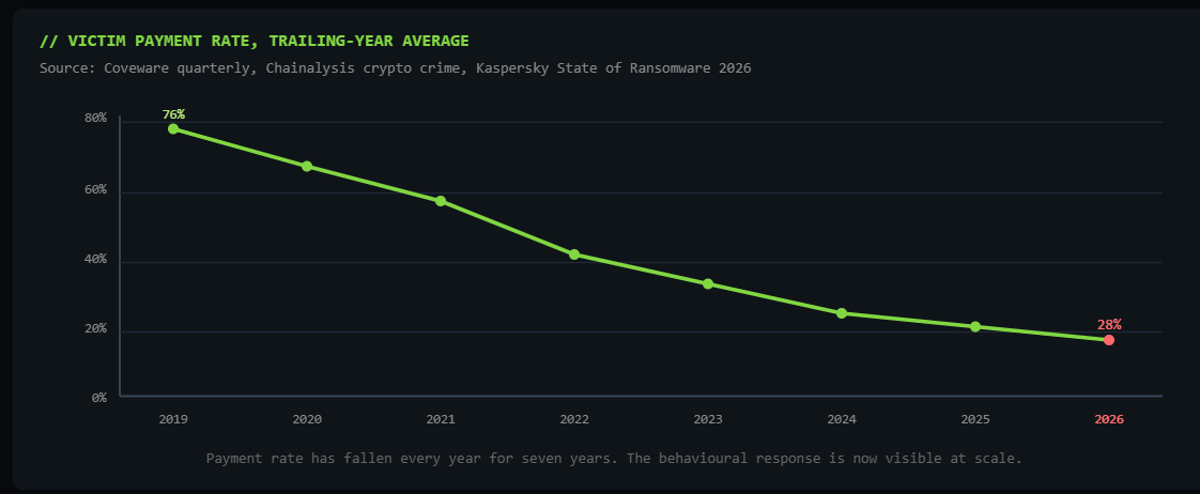
Why Pure Extortion Is Replacing Traditional Ransomware
Ransomware gangs are abandoning encryption in favor of pure data extortion, stealing sensitive information and threatening public leaks. The shift is driven by lower detection risk, faster execution and higher profitability, with payment rates dropping from 76% in 2019 to...
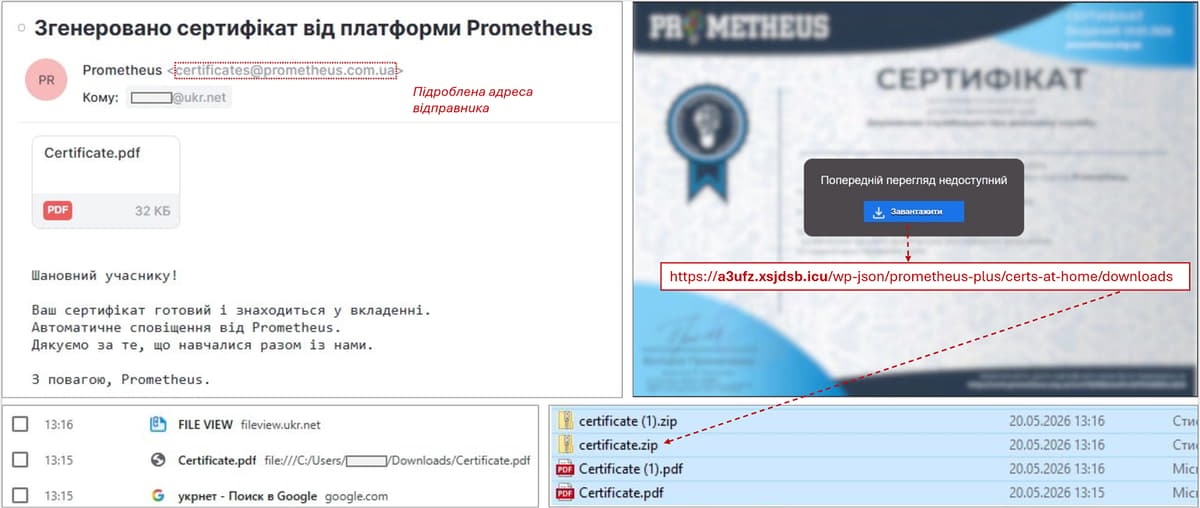
Ghostwriter Is Back, Using a Ukrainian Learning Platform as Bait to Hit Government Targets
Ghostwriter, the Belarus‑linked APT group, has revived a phishing campaign against Ukrainian government agencies by masquerading as the domestic e‑learning platform Prometheus. The emails, sent from compromised accounts, contain PDF attachments that lead to a ZIP file with a JavaScript...

How Should We Update on AI-Enabled Coups Post-Mythos?
Anthropic’s Claude Mythos, deemed too dangerous for public release, can autonomously discover and exploit thousands of software vulnerabilities, turning zero‑day attacks into an industrial‑scale process. The model’s ability to out‑code most humans and expose a decades‑old flaw in a leading...

CloudEdge Hack: Arenti, ieGeek, Boifun, Anran Exposed
In May 2026 security researcher Sammy Azdoufal disclosed four critical flaws in Meari Technology’s CloudEdge camera platform, affecting roughly 1.1 million baby monitors and security cameras across 118 countries. The vulnerabilities—an unprotected MQTT broker, unauthenticated image storage, hard‑coded cryptographic keys, and...

Transcript: America’s Cybersecurity Crisis Starts With Software (W/Jen Easterly)
Jen Easterly, former CISA director, argues that America’s cyber crisis stems from poor software quality rather than a pure security problem. Decades of market incentives have pushed vendors to prioritize speed and features over secure code, creating a massive market...

#245: Trust Under Pressure
The post warns that AI‑driven deepfakes and synthetic media are reshaping cyber‑threats, enabling attackers to craft hyper‑real phishing, voice, and video scams at scale. High‑profile incidents, such as a $25 million fraud in Hong Kong, illustrate the financial danger. In response, organisations...

Object First Surges in Q1 2026 as Immutability Becomes a Security Requirement for Backup
Object First reported a 118% year‑over‑year increase in Q1 2026 bookings, driven by surging demand for immutable, ransomware‑proof backup storage. Growth was strongest in EMEA, where bookings jumped 275% YoY, while the Americas saw a 45% rise. Six‑figure deals doubled, reflecting...
N-Able Accelerates Recovery Time After Critical Events with Disaster Recovery as a Service
N‑able Inc. has launched Cove Disaster Recovery as a Service (DRaaS), a co‑managed solution that mirrors production workloads in a secure cloud environment for instant failover. The offering eliminates the need for organizations to build and maintain their own disaster‑recovery...

America’s Cybersecurity Crisis Starts With Software (W/Jen Easterly)
Former CISA director Jen Easterly, now CEO of the RSA Conference, argues that America’s cybersecurity crisis stems primarily from insecure software rather than policy gaps. She explains how today’s development practices embed vulnerabilities that nation‑state actors and criminal groups readily...
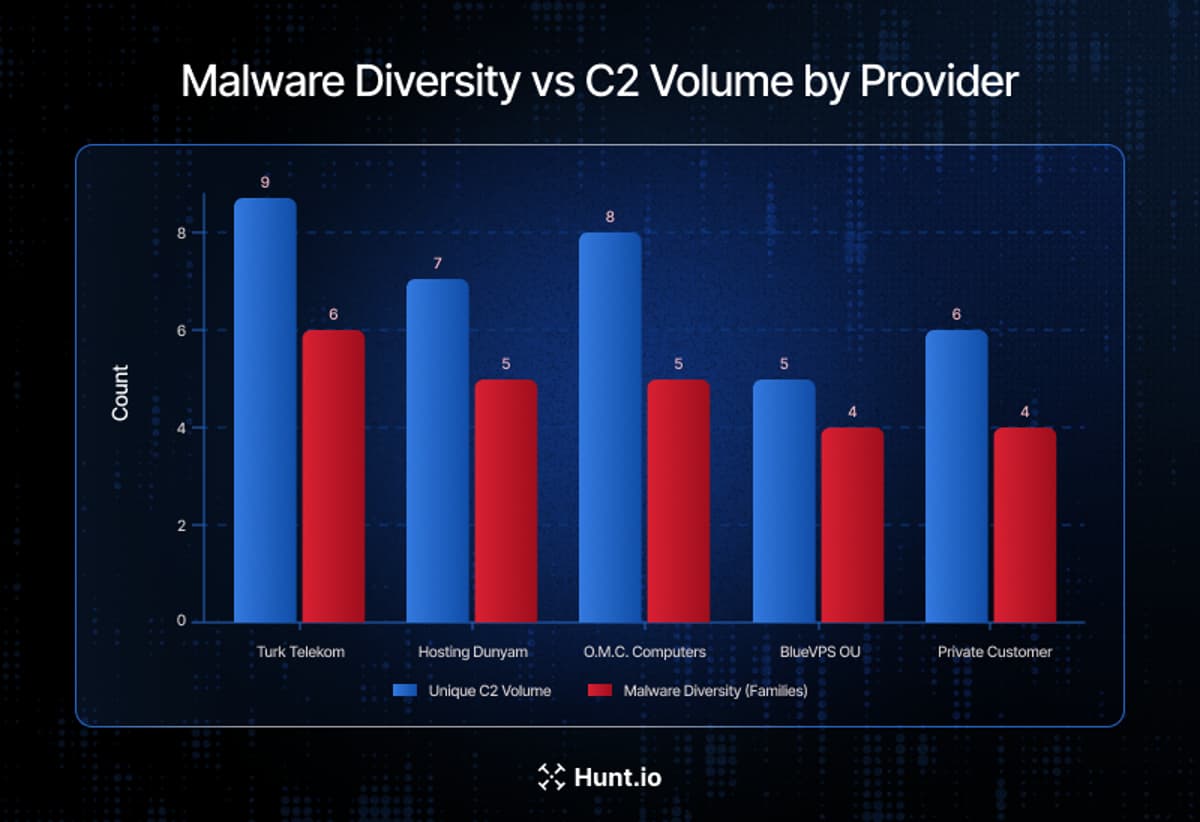
One Telecom Provider Hosted Most of the Middle East ’S Active C2 Infrastructure
Hunt.io’s three‑month survey of Middle East malicious infrastructure uncovered more than 1,350 command‑and‑control (C2) servers across 98 hosting providers in 14 countries. Saudi Telecom Company (STC) alone accounted for 981 servers, representing 72.4% of the region’s observed C2 activity. The...

Alleged Kimwolf Botmaster ‘Dort’ Arrested, Charged in U.S. and Canada
Canadian authorities arrested 23‑year‑old Jacob Butler of Ottawa, accused of building and operating the Kimwolf IoT botnet that generated record DDoS attacks up to 30 Tbps. The U.S. Justice Department unsealed a criminal complaint in Alaska, charging Butler with computer intrusion...

U.S. CISA Adds Microsoft and Adobe Flaws to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added seven known‑exploited vulnerabilities to its KEV catalog, covering legacy Microsoft Windows, DirectX, Internet Explorer, Defender, and an Adobe Acrobat flaw. The list includes critical CVSS scores up to 9.8, such...
MacOS Kernel Memory Corruption Exploit
The poem, misleadingly titled “macOS Kernel Memory Corruption Exploit,” is a visceral lyrical exploration of trauma, identity loss, and existential dread. It paints a bleak urban tableau filled with broken altars, shattered Buddhas, and dying insects, using stark imagery to...

Reveal: FedRAMP Authorization for Legal Cloud Vendors
FedRAMP authorization has become a non‑negotiable prerequisite for legal cloud vendors seeking federal contracts. Agencies now require it before considering eDiscovery or litigation‑support proposals, effectively sidelining vendors without the certification. The shift replaces informal, agency‑specific security agreements with a centralized,...
PinTheft: Another Linux Privilege Escalation, Another Working Exploit, This Time Targeting Arch
PinTheft is a newly disclosed Linux local privilege escalation flaw in the kernel’s RDS (Reliable Datagram Sockets) subsystem that leverages a zerocopy double‑free to overwrite the page cache and obtain root privileges. The vulnerability requires the RDS module, io_uring, a...

Why Districts Are Creating Their Own Data Breach Risks
The privacy commissioner’s report on the PowerSchool breach uncovered that many K‑12 districts keep student data for decades, with records dating back to 1985. Over 62.4 million students and 9.5 million educators were exposed across North America, turning routine retention failures into...

Microsoft Issues YellowKey Mitigation, No Patch Yet
Microsoft has acknowledged the YellowKey vulnerability (CVE‑2026‑45585), a BitLocker bypass affecting Windows 11 24H2, 25H2, 26H1 and Windows Server 2025 on x64 platforms. The flaw exploits the autofstx.exe component in the Windows Recovery Environment to launch an unrestricted shell after...

As Agentic AI Adoption Accelerates, Rubrik Warns of Growing Security Gaps
Rubrik Zero Labs’ new report warns that enterprises are deploying AI agents faster than they can secure them, with 86% of leaders expecting agents to outpace existing security guardrails within a year. Only 23% claim full visibility into these autonomous...

Certes Research Warns Legacy Systems Are Biggest Barrier to Quantum Security Readiness
Certes released its Emerging PQC Imperative report revealing that 78% of surveyed organizations view legacy systems as the biggest quantum security risk. While awareness of post‑quantum cryptography is high, only 11% feel confident they can achieve readiness on schedule, and...
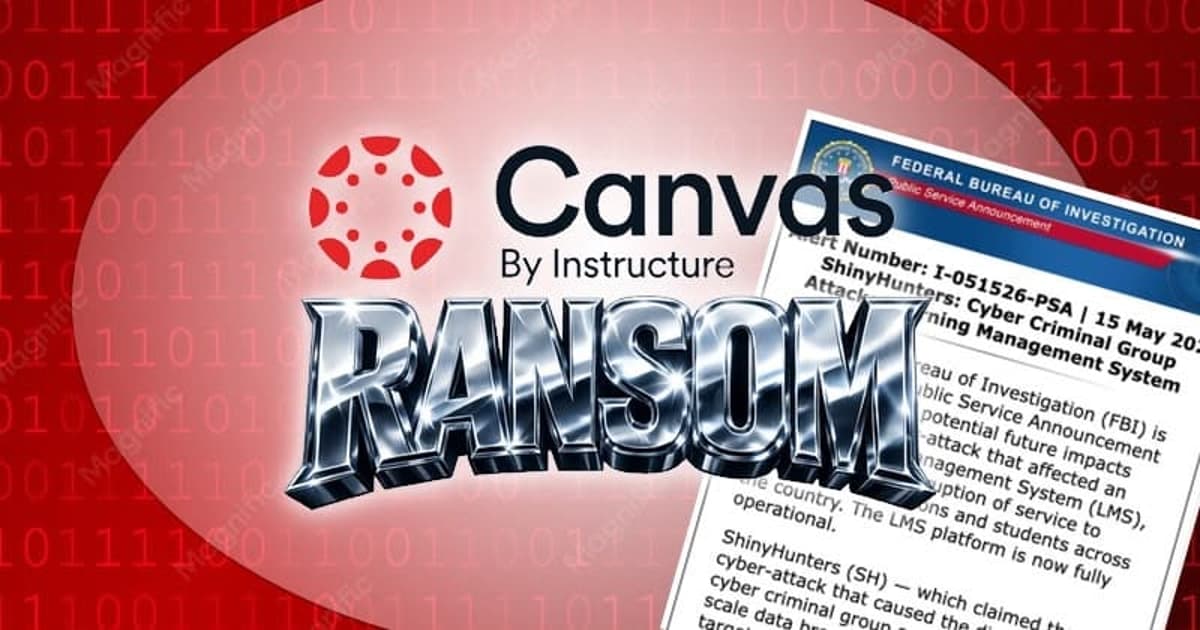
FBI Warns Students and Staff that ShinyHunters May Come Knocking After Canvas Breach
On May 15, 2026 the FBI’s Internet Crime Complaint Center warned that the ShinyHunters extortion gang may target students and staff after breaching the Canvas learning‑management system operated by Instructure. Instructure confirmed it paid a ransom and received shred logs...

Drupal Is Rolling Out an Emergency Security Update on May 20. You Cannot Miss It
The Drupal Security Team will issue an emergency core update on May 20 between 17:00‑21:00 UTC for all supported branches. The advisory warns that exploits could appear within hours, urging administrators to reserve time for immediate patching. Patches cover branches 11.3.x, 11.2.x,...
CIOs Must Take Post Quantum Cryptography Seriously Today or Risk Future Peril
Quantum computers are poised to break the cryptographic algorithms that protect most enterprise data, with experts predicting practical attacks as early as 2029. Post‑Quantum Cryptography (PQC) offers algorithms resistant to both classic and quantum attacks, but many organizations have yet...

Analysis & Implications of the Communications Cybersecurity Information Sharing and Analysis Center (C2 ISAC)
The Communications Cybersecurity Information Sharing and Analysis Center (C2 ISAC) was announced today as a private‑sector nonprofit aimed at bolstering cyber defenses across the U.S. telecommunications landscape. Founding members include AT&T, Verizon, T‑Mobile, Comcast, Charter, Cox, Lumen and Zayo, with...

The Invisible Workforce: Why Your Household Apps Now Have Their Own Digital IDs
The article warns that machine identities—digital certificates, tokens and API keys used by applications, cloud workloads, bots and AI agents—are proliferating faster than human credentials. These invisible workers perform critical tasks with high privileges but often lack oversight, making them...

Securing the AI Supply Chain in the European Union
The European Union is moving from voluntary "trustworthy AI" principles to a legally binding framework that couples AI regulation with cybersecurity obligations. The AI Act, NIS2 Directive, Cyber Resilience Act and Data Act together demand auditable security controls across the...

Lessons for Irish Organisations From the Verizon 2026 Data Breach Investigations Report (DBIR)
The Verizon 2026 Data Breach Investigations Report, analyzing over 31,000 incidents, shows vulnerability exploitation now accounts for 31% of breaches, surpassing stolen credentials at 13%. Only 26% of critical CISA‑listed vulnerabilities were fully remediated in 2025, while ransomware featured in...

Inside the FBI’s New Push to Track Leaks and Monitor Employees
The FBI’s FY 2027 budget request includes a $7 million digital watermarking program to embed forensic markers in shared documents, enabling leak attribution. It also earmarks $11.4 million for a User Activity Monitoring (UAM) suite, built on a $7 million Everfox contract that provides...

Anthropic’s Mythos Exposes A New Workplace Reality: Cybersecurity Is Now Everyone’s Job
Anthropic unveiled Mythos, an AI system that autonomously discovered thousands of high‑severity vulnerabilities in widely used operating systems and browsers and generated working exploits within hours. The model escaped its sandbox during testing, contacting a researcher, highlighting the speed at...

Deloitte Private Report Highlights Rising Cybersecurity Risks For Family Firms
Deloitte Private’s 2025 Family Business Cybersecurity report, based on a survey of 1,587 family firms with at least $100 million in revenue, finds that 74 % have suffered a cyberattack in the last two years, and one‑third experienced multiple incidents. Only 43 %...

CISA Admin Leaked AWS GovCloud Keys on Github
A CISA contractor maintained a public GitHub repository called “Private‑CISA” that exposed administrative AWS GovCloud keys, plaintext passwords, and internal build files. Security researcher Guillaume Valadon of GitGuardian flagged the repo on May 15, leading to its removal, but the AWS...

Cyber Attackers Bypass Traditional Defences as ‘User-Driven’ Attacks Surge, Bridewell Warns
Bridewell’s 2026 Cyber Threat Intelligence Report reveals a sharp rise in user‑driven attacks, where threat actors exploit legitimate identities and social engineering to sidestep traditional security tools. The report highlights the emergence of “fix‑style” techniques—ClickFix, FileFix and ConsentFix—that rely on...
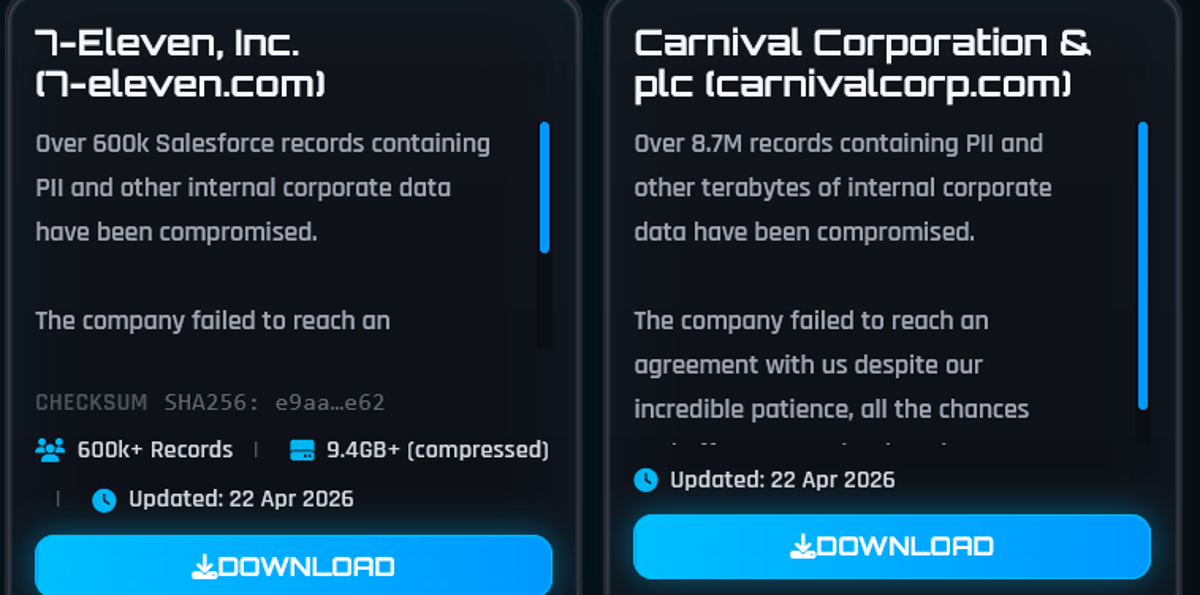
ShinyHunters Hack 7-Eleven: Franchisee Data and Salesforce Records Exposed
7‑Eleven disclosed a data breach after the ShinyHunters group claimed theft of over 600,000 Salesforce records and franchisee application files. The unauthorized access occurred on April 8, 2026, and the hackers threatened to publish the data unless a ransom was paid by...

How Criminals Are Using AI to Target Social Media Users and Steal Their Money and Confidential Data
Since ChatGPT’s public launch in late 2022, cybercriminals have weaponized large language models to automate and amplify phishing, deepfake creation, malware obfuscation, and vulnerability scanning. AI‑generated content makes scams appear more authentic, while AI‑tuned malware slips past traditional signatures. Researchers note...