
Smart TVs Silently Siphon Classified Data to Foreign Adversaries
This is a massive and growing problem for American national security. Unbelievable amounts of sensitive and classified information is captured, scraped, and sent back to foreign nations. And users have no idea. Nobody expects that their TV or monitor is a surveillance tool. When I have joked that Smart TVs should be illegal, I am only half-joking.

Anthropic MCP Has Critical Flaw Enabling Full System Takeover
The Architectural Flaw at the Core of Anthropic's MCP according to OX allows complete system takeover in some cases. Of course they sell a tool to secure it but if using MCP you should understand how this works and how...

WordPress Plugin Flaw Lets Attackers Bypass Login, Seize Admin Control
A critical WordPress plugin flaw allows attackers to bypass authentication and gain full administrative control, exposing websites to data theft and malware attacks. https://t.co/lNfDVZAz0K

Google Archives Every Search, Location, and Video—Delete Now
Google has a recording of every search you've ever made. Every place you've ever been. Every YouTube video you've ever watched. Go to https://t.co/SsI3dVLQDL right now. You'll find searches from 2015. Voice recordings. GPS coordinates. All stored. All linked to your name. Here's how to...
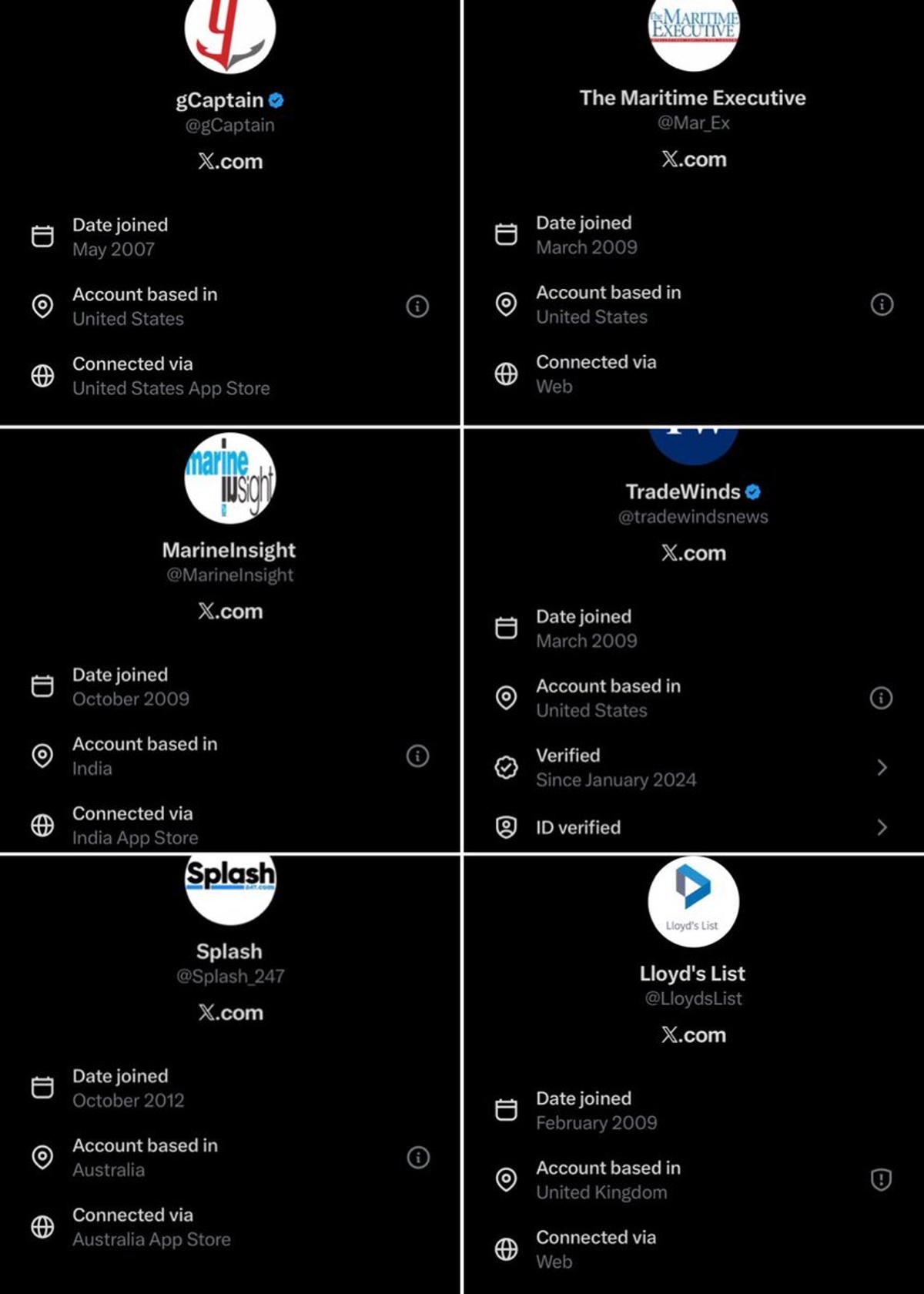
X Patches VPN Loophole, Reveals True Foreign Accounts
Looks like X finally fixed the VPN loophole that let our overseas competitors show up as 🇺🇸 This is accurate now except @splash_247 is registered in Singapore with an Australian office and @tradewindsnews is Norwegian. TW does employ a few American...

Five Teams Unite to Recover Funds and Boost NEAR Security
In trying times like this it was great to see collaboration between 5 different ecosystem teams and also global partners to track down what happened, responsible actor and recover funds. Security and resilience is going to be an ever more important...
Cross‑Disciplinary Maintenance Insights Boost Cybersecurity Programs
The Maintenance of Everything Studying how other fields think about maintenance and sustainment is extremely useful. These areas are rich in lessons to apply to cybersecurity. Stewart Brand’s Maintenance of Everything is a brilliant overview of many of these fields. It’s...

Passkeys: The Underrated Upgrade Securing Modern Web
passkeys don't get enough credit for how much they have shaped and secured the internet these past 2-3 years. when a site has it, it is usually a positive signal on how seriously they take security. going from a world of...

Avoid Eth_limo URLs After DNS Attack Warning
The kind people at @eth_limo have warned me that there has been an attack on their DNS registrar. So please do not visit https://t.co/BVfZIYrDKe or other https://t.co/OgoUF2qKUY pages until they confirm that things are back to normal. You can check my...
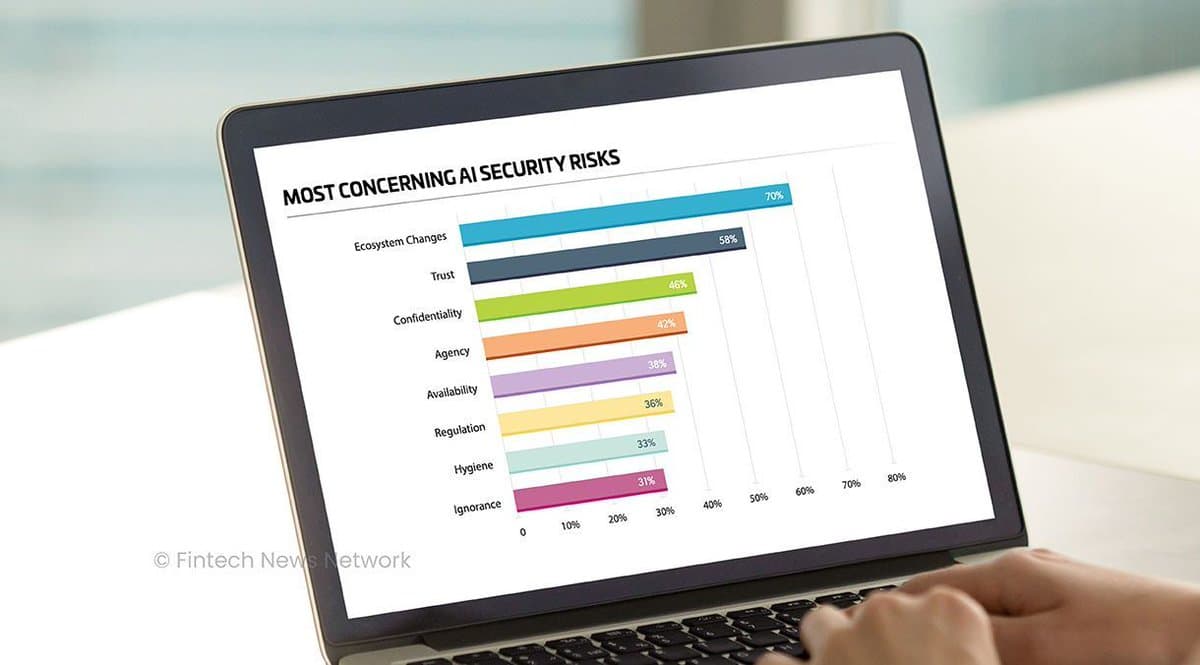
AI Emerges as Leading Data Security Threat
AI Becomes A Top Data Security Concern - Fintech Schweiz Digital Finance News - FintechNewsCH https://t.co/c4BCBKY7Qu https://t.co/5EUNVC4oiQ

Rust Tailscale Library Expands with C, Elixir, Python Bindings
tailscale-rs It is a work-in-progress Tailscale library written in Rust, with language bindings to C, Elixir, and Python. https://github.com/tailscale/tailscale-rs

Tools Are Easy; Business‑focused Risk Understanding Is Hard
The more time I spend in security, the more I believe tools are the easy part. Understanding risk in a way the business cares about and then acting on it is where most teams struggle.

Questioning Peston’s Access to Sensitive Email Traffic
Congratulations @Peston on getting access to such sensitive email traffic Obviously you’ve only got the important bits…& there’s obviously nothing further to see here btw who gave you access & why?

Third‑Party Risks Cause Over One‑Third of Breaches
Over 35% of data breaches are caused by vendors or partners, not internal failures. As threats spread globally, third-party risk is growing. Security is only as strong as the weakest link. https://t.co/e3kXTsRA5f
Mythos Could Exploit Vulnerabilities, Raising Skynet Concerns
Mythos, Anthropic’s not yet released model, allegedly can not only find security gaps but exploit them. How far from Skynet are we?
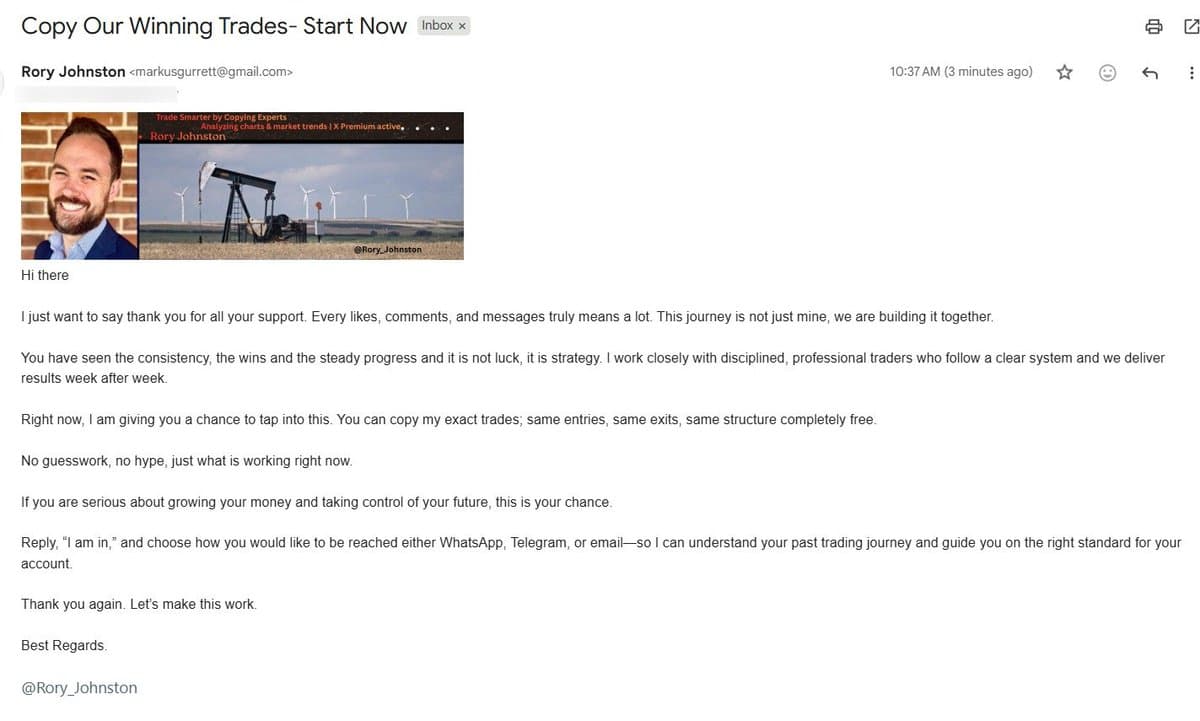
Unwanted Anonymous Email Sparks Creepy Concern
Few folks have reached out after having received this email, which is a new one for me. It's most certainly not me—it's weird and creepy and I'd really like it to stop. https://t.co/5ora12ynHG

Embrace Soft Forks Now to Prepare Bitcoin for Quantum Threat
The most important thing for Bitcoin community to get ready for addressing the quantum threat is taking head out of sand when it comes to soft forks and start embracing them. It'll be a big change to get post quantum, so...
Critical Permissions Should Never Be Auto‑Approved by LLMs
@boris_cherny Is there a way to get approve and auto accept edits back? I work on database systems my environment has very critical permissions that I just don't ever want an LLM to be able to use by itself regardless of...
Prepare for Quantum Threats Now, Not on Q-Day
Post-Quantum Readiness Starts Long Before Q-Day by Etay Maor @Forbes Learn more: https://t.co/7bXzGooAsr #EmergingTech #Innovation #Technology https://t.co/fk6CZ8LQRE

AI Overwhelms Volunteers, Echoing Past Cybersecurity Struggles
12 years ago I wrote how the internet is being protected by two guys named Steve. Today, the situation isn't all that different, except those handful of volunteers are being swamped by AI systems finding holes in our digital systems....

Never Share Passwords in DMs—Verify Sender First
Twitter or X is fun but just for house keeping and safety rules, never put your password into something other than to log into the platform you need to access. Any DM message that asks you to input password, even if...

AI Tools Empower New Wave of Bank Hackers
Forewarned is fore armed. New level of hacking of banks could come from these AI advances. 👉Cops & robbers when the robbers get a new tool. https://t.co/GKklqa2Kai
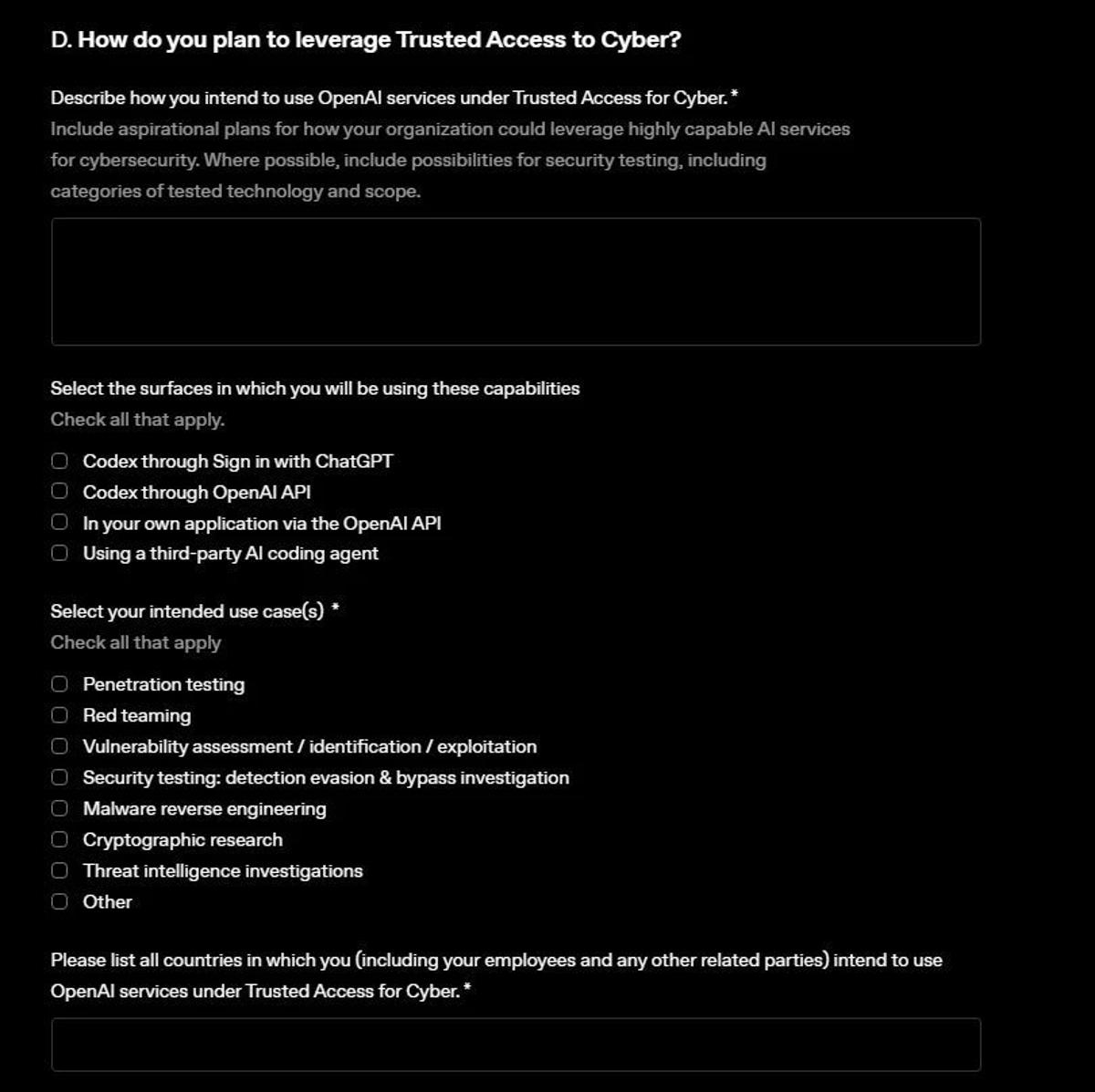
OpenAI Launches GPT‑5.4‑Cyber via Expanded Trusted Access
.@OpenAI releases GPT-5.4-Cyber, beefed-up Trusted Access for Cyber program https://t.co/Cqe6QG6I3Z OpenAI released GPT-5.4-Cyber, a model that will be released to select participants in a beefed-up Trusted Access for Cyber (TAC) program. https://t.co/pvHgkQtziD
Phishing Attacks Now Pivot to Crypto Scam Pitches
Not me. Phishing. Apparently next step is they will pitch you a crypto scheme https://t.co/L4QDjDF1BH

Phishing Tactics Shift From Freebies to Political Pitches
Evolution of phishing scams: -“Click here to redeem a free iPhone” -“This is USPS. We’re holding your package” -“Vote for me to co-host a podcast”

Bluesky Hit by Sophisticated DDoS, Fix Due Tomorrow
Bluesky has been wonky all day to due to a "sophisticated" DDoS attack. It sounds like they are still trying to get it under control w/ an update coming "no later than" 10am PT tomorrow

Open Source Will Outsecure Closed Source in Mythos Era
Open source software will be many times more secure than closed source software in the new Mythos era

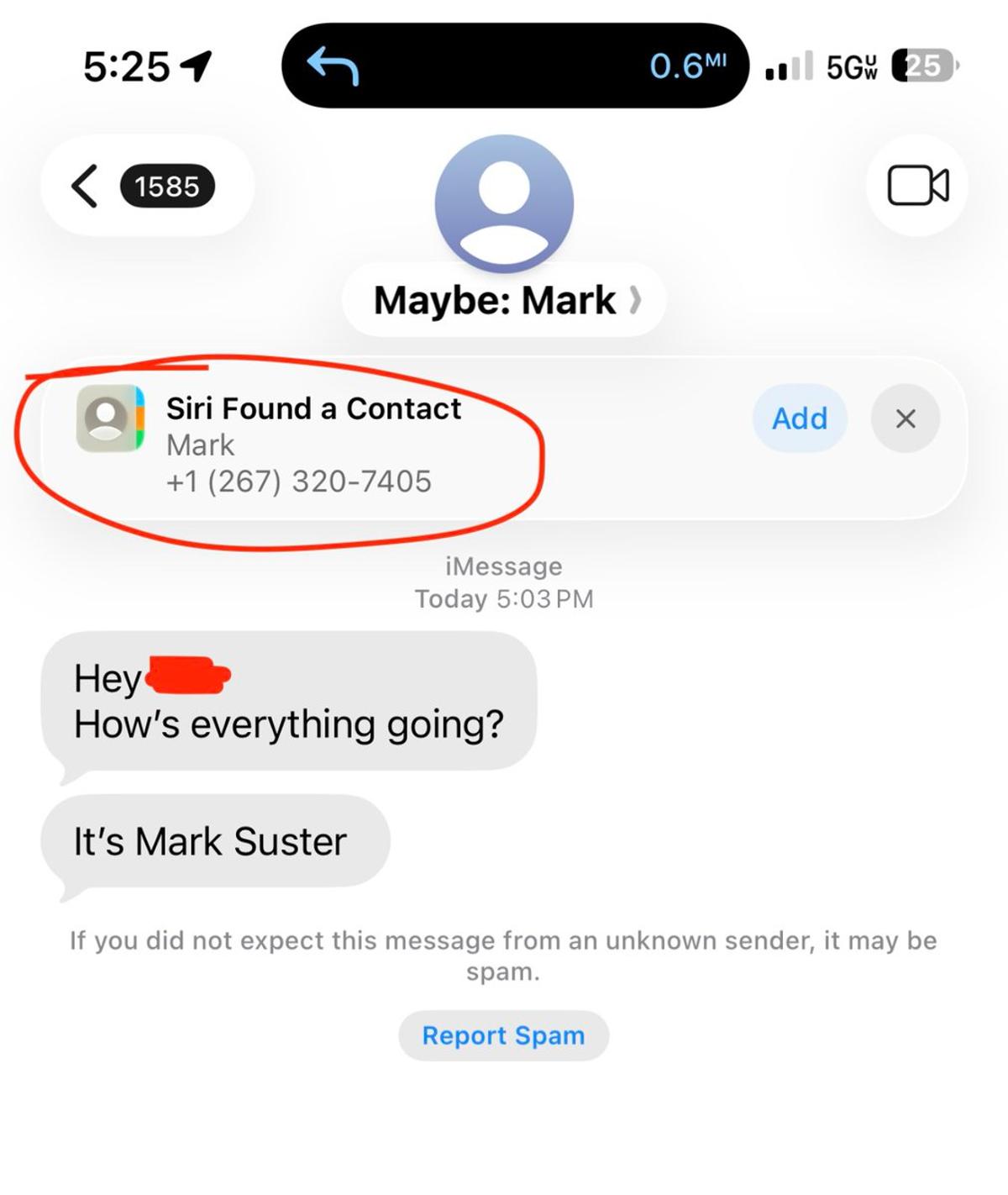
Beware: Unknown 267 Area Code Texts Are Phishing
No. I am not texting you asking to engage with me unless you already know my number. Yes. Somebody is doing this from a 267 area code and maybe others. Several people have now asked me. It's Phishing. Sadly. The world that...

AI Labs Purchase Defunct Startup Communications, Raising Privacy Concerns
AI labs are buying internal communications of defunct startups to train their agents. Emails, Slack archives, etc. Personally identifiable info is removed by data resellers. But how would you feel knowing your former board/CEO is selling your comms to recover...

Treat Dependencies as External Attack Surfaces, Upgrade Tooling
Your Dependencies Are Someone Else's Attack Surface https://t.co/zDbAITTE9f < good post with cause for optimism at the end. But we need to apply better skills/services to agent tooling to stay diligent when building

Simple Closure Launches Asset Hub to Sell Legacy Data
a company called @simple_closure that helps startups wind down is launching "asset hub", which is a marketplace to sell all the old slack/email data apparently they are working on hardening the PII removal tech for this

Agentic AI Security Needs Layered, Integrated Defenses
We keep asking how to solve agentic security as if there is a single answer, but most of the conversations I am having suggest it is a combination of least privilege, access controls, monitoring, and good architecture. The question might not...

New AI TUIs May Expand Attack Surface via React
I know there are some new TUIs coming out for AI development but I’m concerned about increasing the attack surface with web technologies like react. Securing AI is hard enough as it is.

World Cup Partners Neglect Strong DMARC Domain Protection
Some World Cup partners are not actively protecting their domain name with the strongest DMARC policy. https://t.co/Q4k3WpQ9hb

Russia Caps Bandwidth, Forcing VPN Filters or Price Hikes
Russia’s fight against digital privacy escalates as internet providers agree to freeze the expansion of cross-border channels into Europe. By capping international bandwidth, authorities aim to force telecom operators to either filter VPN traffic or hike prices, making it harder...

OpenAI Chooses CrowdStrike for Defender‑Focused AI Security
The top AI labs are building for defenders now. Today @OpenAI selected CrowdStrike for their Trusted Access for Cyber program. CrowdStrike continues to lead the market in secure AI adoption, trusted by AI leaders and organizations of all sizes to accelerate...

Mid‑Market Firms Must Close Compliance Gaps Now
Mid-market regulated firms are sitting on a compliance gap. PHI/PII pipelines built for speed, not governance. DLT expectations. Unity Catalog policies. On-call ownership. Most have one layer. Few have all five. Build it right once. Outrun the audit.
Small Businesses Need Post‑quantum Encryption Now
Even if you’re a small business, your data has long-term value. Cybercriminals are hoarding encrypted data, betting quantum computers will crack it. Post-quantum cryptography (PQC) and PQC-ready vendors are the defense today. https://t.co/JCn5eZDeii

AI Revives Early‑2000s 0‑Day Chaos
Has AI brought back the early 2000s? People can find and exploit 0days easily. Hackers angry at Microsoft are dropping 0day. Frosted tips are cool again (ok, that one would mean the apocalypse)

SMBs Know Basics; Prioritize What Truly Matters
For SMBs, cybersecurity is rarely a knowledge problem. Most teams know the basics. The challenge is figuring out what actually matters for their business and doing that well.

FSB Expands Control over Russia's Internet Landscape
A really excellent story from @thebell_io on how the FSB – the same unit behind Navalny's poisoning, no less – are taking over Russia's internet. The sort of depth and breadth you don't see too often these days. A must...

Hash Functions Power Your Daily Digital Interactions
Did you know you're using an algorithm called a hash function hundreds of times every single day without even realizing it? From logging into your favorite apps, to securing your passwords, hash functions are the invisible backbone of the modern...

Scammers Clone Slack Downloads to Distribute Silent Malware
Scammers are cloning Slack download pages almost perfectly. Same layout, same buttons, and the same Download experience. You have to install. But instead of Slack, you end up with malware running quietly in the background.
Telegram‑sold Tools Let Scammers Breach Bank Security
Cyberscammers are bypassing banks’ security with illicit tools sold on Telegram | MIT Technology Review https://t.co/6F7Bho2ZXd

Future‑Proof Chains Must Be Quantum‑Resistant, Regardless of Timeline
Whether you believe quantum computers will become reality as soon as 2029 or decades from now, it doesn't matter. The potential alone will scare people, and there will come a point when whatever you're building will have to be quantum...

If You Worry About Windows Privilege Escalation, Your Security Fails
Repeat after me: Your security program is not good enough to have to worry about escalation of privilege on Windows

Proactive Steps to Cut Cyber Risk Before Damage
How To Reduce Cyber Risk Before It Becomes Business Impact by @austingadient @Forbes Learn more: https://t.co/3n73qicnmw #CyberSecurity #Infosec #Technology https://t.co/WfQRH57gbm

Reddit 2026 Cybersecurity Talk Shifts From Phishing To AI Chaos
From Phishing to AI Chaos: What My Analysis of All Reddit CyberSecurity Discussions So Far in 2026 Revealed https://t.co/LF7w9E3mMR

Europe Launches First Kill‑switch‑proof Cloud Recovery Stack
Europe builds its first “kill-switch proof” cloud recovery stack https://t.co/QMZVcROJjW >> Congrats. Interesting pan EU collaboration - BUL / D / I and LUX. Good to see. Bow let's look for adoption.

AI Tool Adoption Leaves Companies With Zero Code Controls
In all seriousness though, companies that are investing in these tools have zero control over code quality, how to protect from prompt injection, what gets shoved and executed into the developers environment, what gets shoved into production. Zero. Controls. Death of...