
Startup Accidentally Exposes Personal Info via Public Roadmap
A startup just CCed me its roadmap because a) its roadmap is on Github and b) minor notes on that roadmap named my Twitter account which c) lexically equivalent to my Github account. Had never thought of that route for information disclosure, and hence, this polite heads up.

Ethereum Offers Upgradeable, Limit‑enforced Contracts; Canton Lacks Protection
What's possible on Ethereum that's not possible on Canton? "You can set limits, you can make it upgradeable with keys in cold storage by Circle in a multisig, and this smart contract. enforces limits. "You cannot do this on Canton. Your...

Voluntary Security Attestations Boost Open‑Source Supply‑Chain Safety
Our colleagues at Open Regulatory Compliance have released statement on article 25 of the EU's CRA. Voluntary security attestations can help sustain open source and improve supply chain security. We support the joint ORC statement. 👇 https://t.co/3iGhnJ58RT
DeFi Must Rethink Trust After Lazarus Breaks Eight Protocols
"If Lazarus can break 8 different protocols in 8 different ways, then DeFi has to stop working from the framework of assuming that all transactions are legitimate." 👀 -- @austincampbell https://t.co/xtIdxNvnOf
Your Crypto Stays Safe with Multi‑sig, Advisor‑approved Transfers
A compromised Google account wiped out someone's XRP. Assets at Digital Wealth Partners are not tied to your Apple ID or Google account. Separate login, multi-sig verification, whitelisted addresses only. Nothing moves without a wealth advisor signing off. Some partners...

Permission Overhaul Unintentionally Exposed Public Project Chats
Crazy. “We also retroactively patched our API so public project chats couldn't be accessed, no matter what. Unfortunately, in February, while unifying permissions in our backend, we accidentally re-enabled access to chats on public projects.”
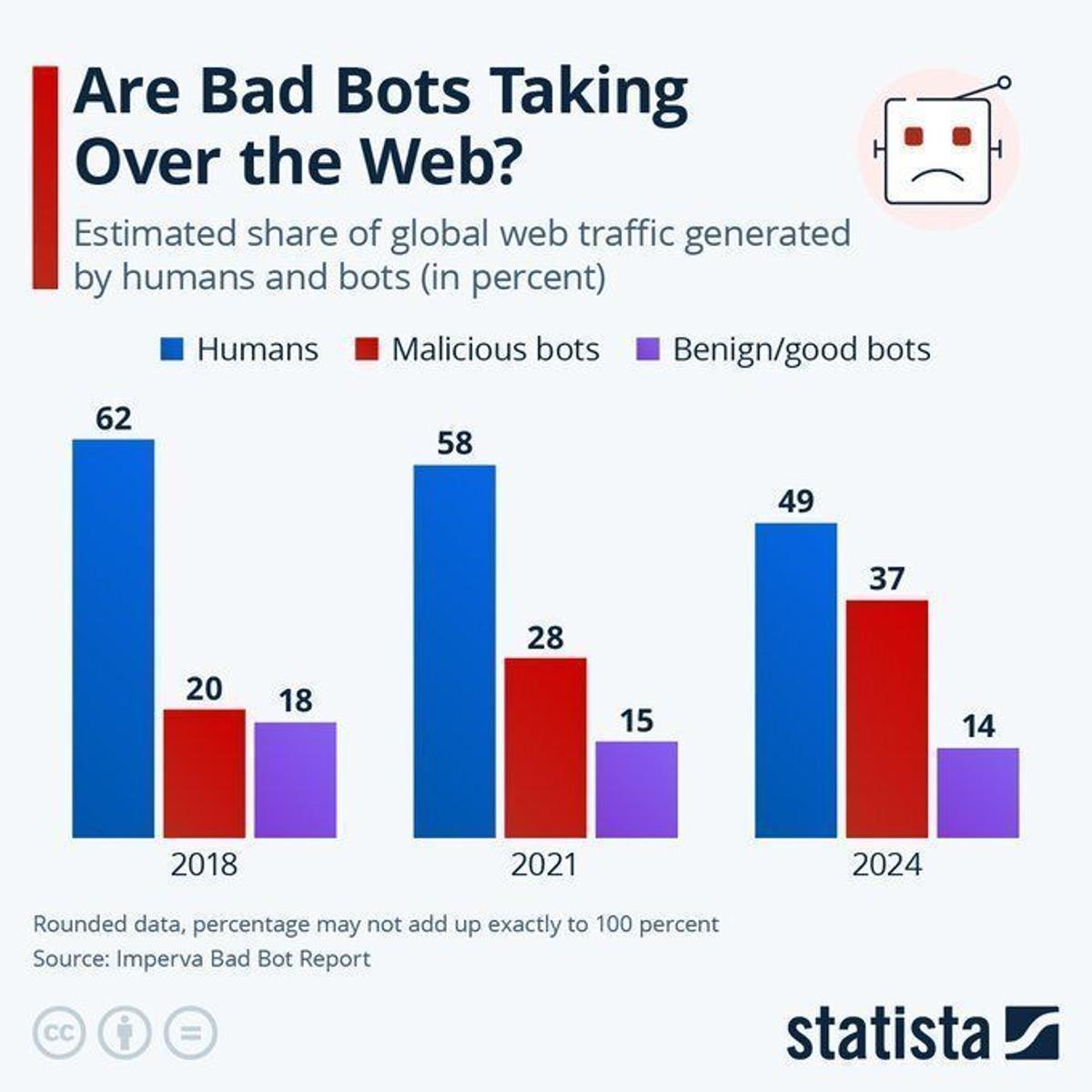
Bots Account for 37% of Web Traffic, Redefine Analytics
Web traffic metrics increasingly hide a structural distortion. Malicious bots generate 37% of activity, so marketing analytics, ad spend and cybersecurity baselines must be recalibrated because a growing share of “users” is no longer human. Source @StatistaCharts via @antgrasso https://t.co/kfAwyiqWYw

Security Alerts Steal Your Entire Workday
Ok great. Now I have to spend all day figuring out who is trying to access my systems and network. Thanks.

Prioritize PQ‑safe Outputs and Signatures Now, Defer Other Fixes
Follow up on Bitcoin and Quantum: A proposed roadmap. https://t.co/QoOrvnxeOe tl;dr: we should work towards activating a PQ-safe output type with PQ signatures now. everything else (including escape hatches, zk proofs, commit/reveal, to freeze or not) can, and should, wait.

20i Hosting Range Flagged for Malware Activity
The malware report below is interesting for those who want to get into reverse engineering malware, but the IP range would immediately stand out on my network if you are trying to block such things. I looked into who owns the...

AI Security Shifts to Governance, Data Control, Real Risk
Great roundtable in NY last week with Zscaler on securing the next wave of AI in financial services. The conversation has changed. Less hype, more focus on governance, data control, and real risk.
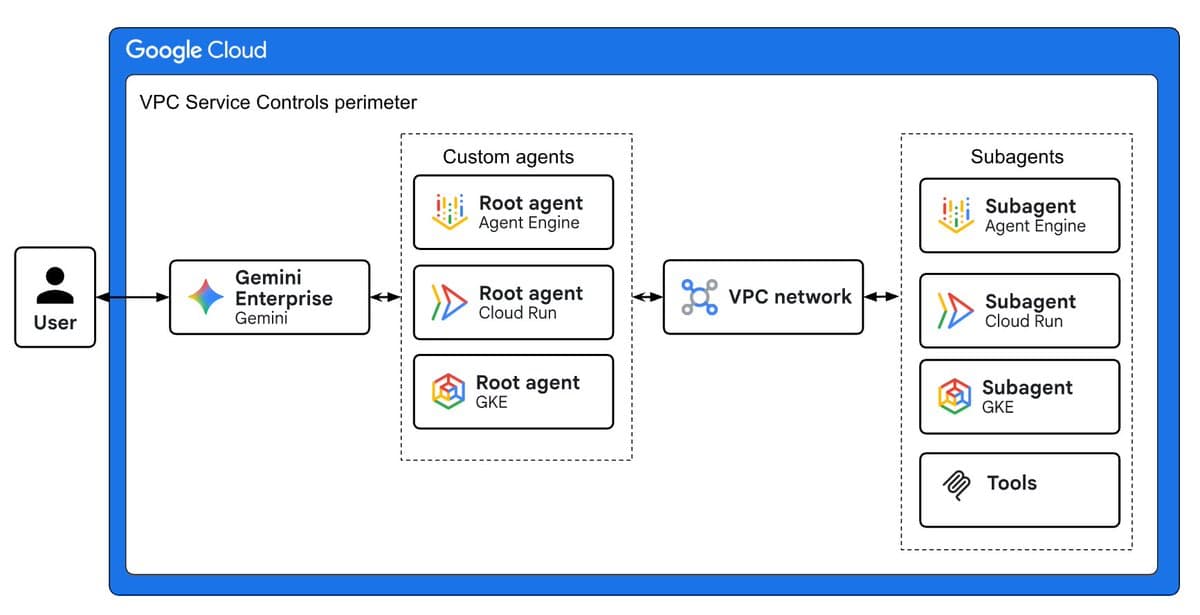
New Guide Shows Secure Multi‑Agent Networking Patterns
If you don't need more than one agent, keep it simple. But when you do, it's important to know the patterns and tech for secure networking. We just shipped a terrific new architecture guide that you can study, or give to an...
SignalShot: AI-Driven Proof of Signal’s Full Security
Today is the launch of SignalShot: An AI-powered moonshot launched to prove that Signal Messenger is bug-free and secure – and turbocharge the AI-powered quest to secure all critical software.The spectacular power of new AI tools such as Mythos to find...

Secure Your Crypto: Essential Practices for Maximum Protection
Crypto Security Checklist - High Security Email for important accounts (Protonmail) - Always use 2FA (never mobile 2fa) - Level 1 Data (Seed phrases, passwords high security emails): paper or metal in fireproof safe, never digital. - Level 2 Data (account passwords): unique and...

Context.ai’s SOC2 Audit Traced Back to Delve
I’ve confirmed that Context .ai was “audited” by Delve for SOC2 Redirects now deleted but https://t.co/o3dRukNdBn used to redirect to Delve themselves You cannot make this up…

AI Security Fundamentals Unchanged, Just Faster and Messier
I keep hearing “AI security is different.” Not sure I buy that. Most of what teams are dealing with looks very familiar, just faster and messier. Shadow AI, identity, third parties. We’ve seen all of this before. The tooling changed. The fundamentals didn’t.
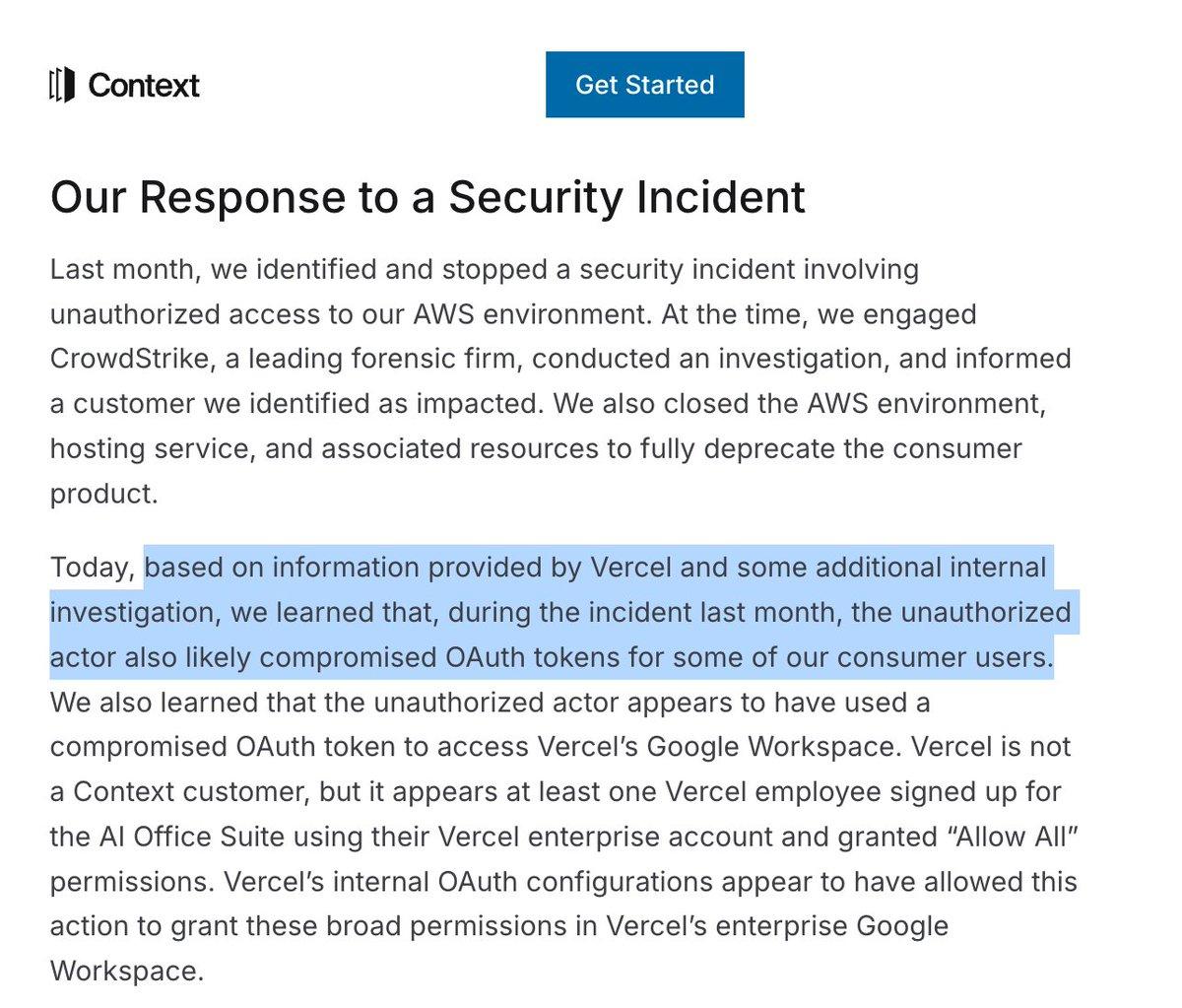
Breach Discovered by Customer Undermines Trust
Few things are more embarrassing for any company than to only learn from your customer that you have been breached. It's what happened with Context ai. Vercel acted as their security team. This could well be a business-ending event, as it shows the...

Tech Firms Shield Datacenter Metrics, Thwart EU Transparency Push
So, the EU commission wanted to oblige datacentre operators to report data on key performance indicators. But then tech companies successfully "pushed to classify all individual information on datacentres as confidential, citing commercial interests" https://t.co/qmPgzunR0w

Over 20 iOS Crypto Wallets Hijacked by FakeWallet
More than 20 malicious crypto-wallets for iOS: how the FakeWallet crypto-stealer is spreading through the App Store: https://t.co/SSkqda8UH5 https://t.co/efDIdCmpRh

Rushing AI Deployment Sacrifices Security for Speed
The push to deploy AI creates security gaps, as speed is prioritized over proper testing. https://t.co/yz4Sdmq27H

Cloud Platform Admits Non‑sensitive Data Breach, Customers Notified
Cloud development platform confirms theft of "non-sensitive data" and says customers were already notified. https://t.co/H2ODt6Fsuz

Rethinking Cybersecurity Acronyms for Modern Success
Cyber security has many acronyms to measure success but are these still fit for purpose today? https://t.co/OweXT5eLQr

Proof‑based Protocols and Diversity Essential for Long‑term Security
This is the kind of attack that many people in blockchain security had long expected. This is why proof based protocols, multiple, operator diversity etc matter. The challenge with security is that it’s a super long game and it’s hard to convince...

Base Security Lies in RPC/DNS, Not Consensus
If the stack above consensus won’t pay for trust-minimization, then base-layer security is irrelevant. Users touch RPCs and DNS, not validators and that’s the layer that’s exposed

Are Smarter AI Models Fueling Recent DeFi Hacks?
Is there any reason to believe recent DeFi hacks are directly a result of smarter models?
Sophisticated Attack Exploits KelpDAO Laxity on LayerZero
The attack was way more sophisticated than I expected and aimed at LayerZero infrastructure taking advantage of KelpDAO laziness.

Single-Validator Bridge Breach Highlights Need for Decentralization
tldr KelpDAO made the decision to use a 1 of 1 validator for the entire bridge and their 1 got breached. How could this have been avoided?

Urgent Request: Need Figment Contact for Phishing Victim
Hey can someone connect me to someone at @Figment_io ? An emergency about a friends wallet that got phished

Cybersecurity Becomes Critical for Decentralized Energy Systems
Managing cyber risks in the era of decentralized energy #energysky -- via pv magazine global: https://t.co/DN7O7RH2jq

Avoid Vote Links in DMs—They're Likely Scams
PSA: don't click those vote links in the direct messages (looks like a bunch of compromised accounts are DM-ing people asking them to vote for podcasts)

Mythos AI Exposes Legacy Systems—Act Now
JUST IN: Anthropic's Mythos model gives hackers access to long-secured systems, and Nic Nguyen details the cybersecurity steps you must take immediately.
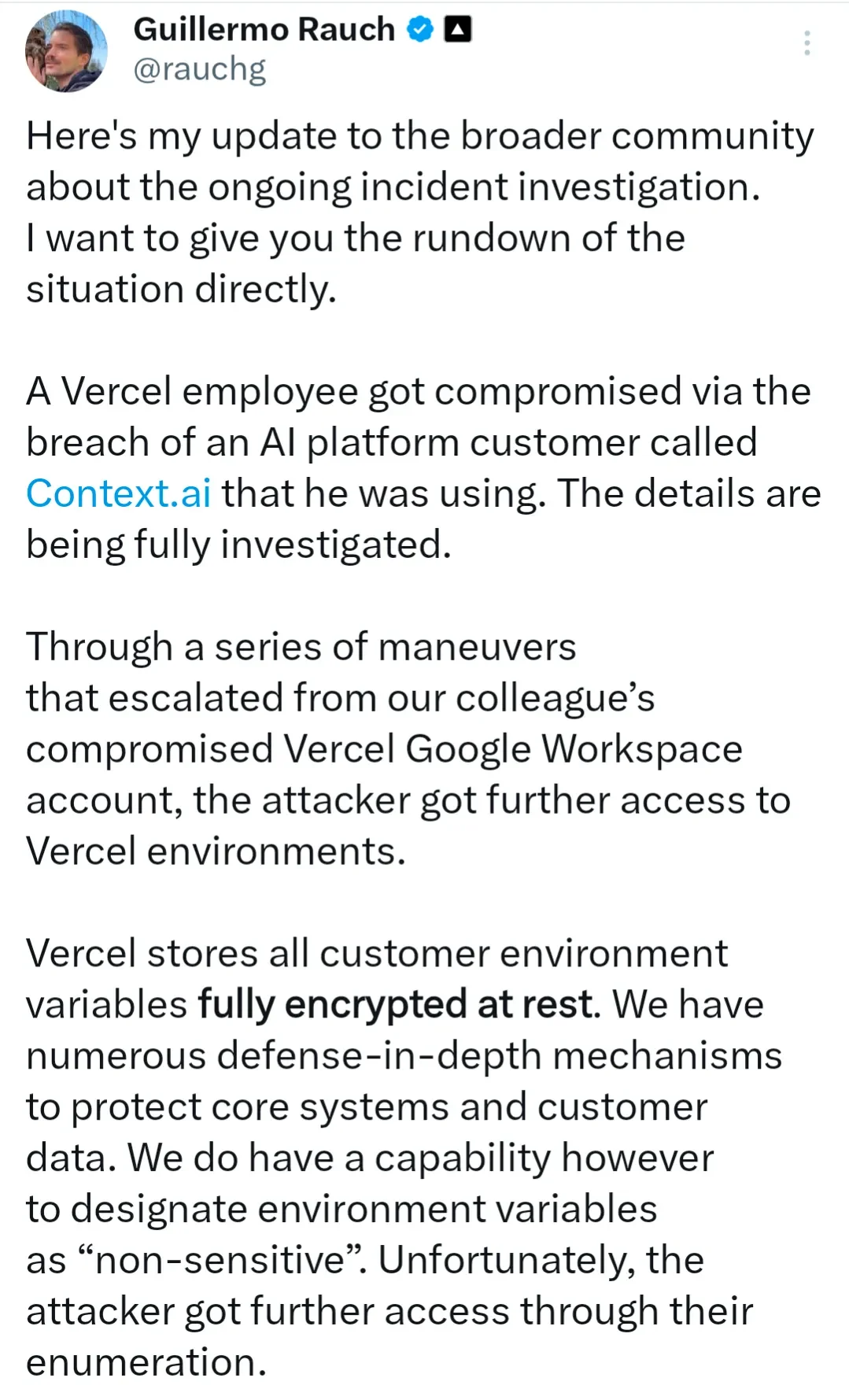
AI-Driven Attacks Will Cripple Complex Systems Soon
Vercel today, someone else tomorrow... Complex systems will be hit hard by sophisticated attacks - augmented by AI systems.

OAuth's Pitfalls Push Teams Toward Password-Only Integrations
Oauth is great until it’s not. I have a strong feeling that this incident will see a few security playbooks adjusted to “user/password only for external services.”

CIRCIA Rule Faces Funding Gap, Delays Past May 2026
Policy Pulse #11 just dropped. Top story: CIRCIA's final rule is on a collision course with a DHS funding lapse. Town halls cancelled, slippage past May 2026 looks likely. VDP programs: your intake needs to be 72-hour ready before the clock...

Breach Frequency Surges Despite Sparse Vercel Details
The info about the Vercel breach is very limited but the amount of breaches has definitely accelerated in the last few months.

AI Powers Modern Penetration Testing: AWS Community Talk
How I Use AI for Penetration Testing. Presentation at the AWS Security Community Day at the Computer History Museum on YouTube https://t.co/hP5kPanmUX

Claude’s Chrome Extension: Game‑Changer or Security Threat?
Is adding the chrome extension to Claude a security risk? Allowing it to take over your computer and browse the Internet in order to complete tasks is an insane game changer beyond belief. Seemingly.
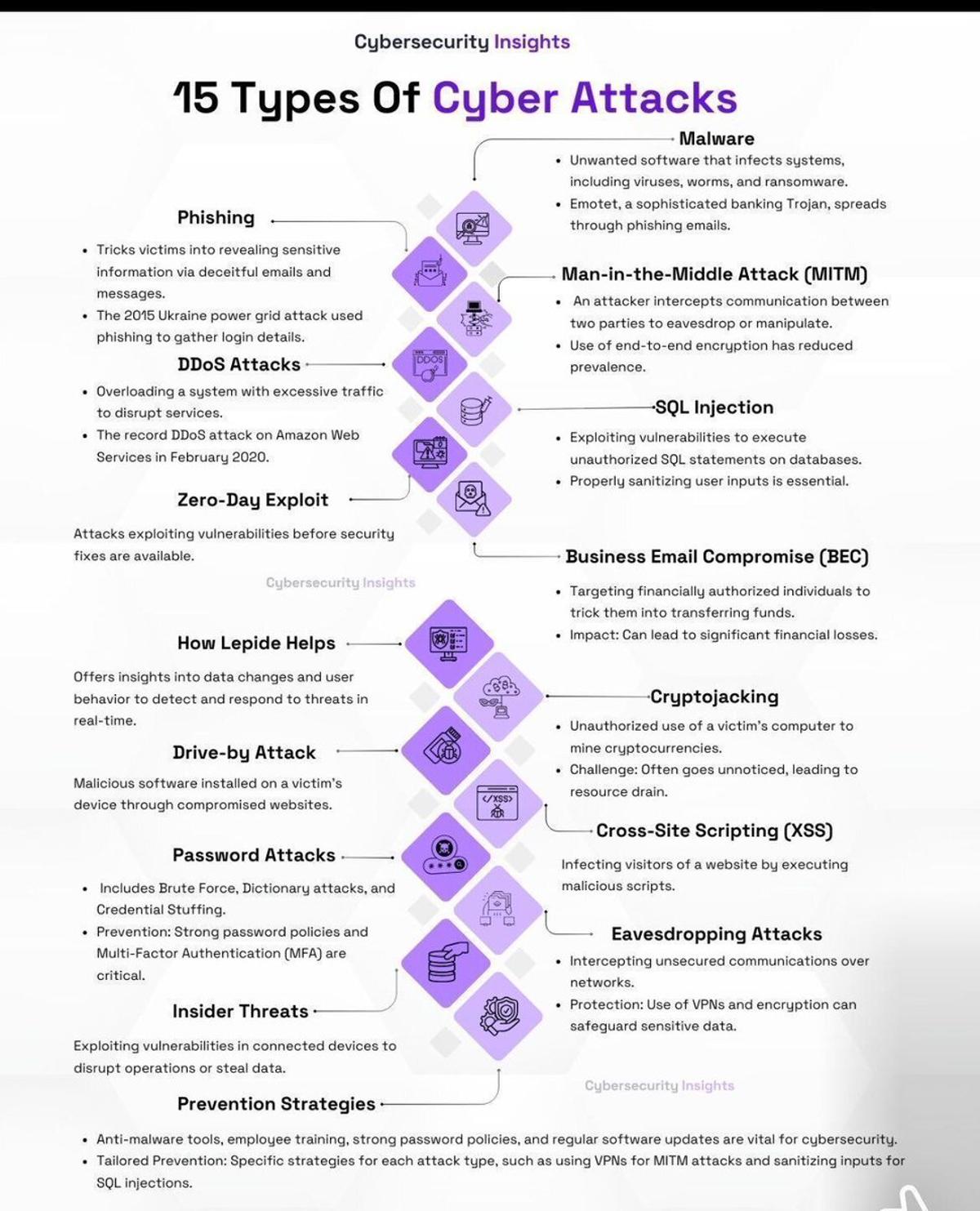
Know 15 Cyber Attacks to Boost Resilience
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk https://t.co/3B7i8nznnK
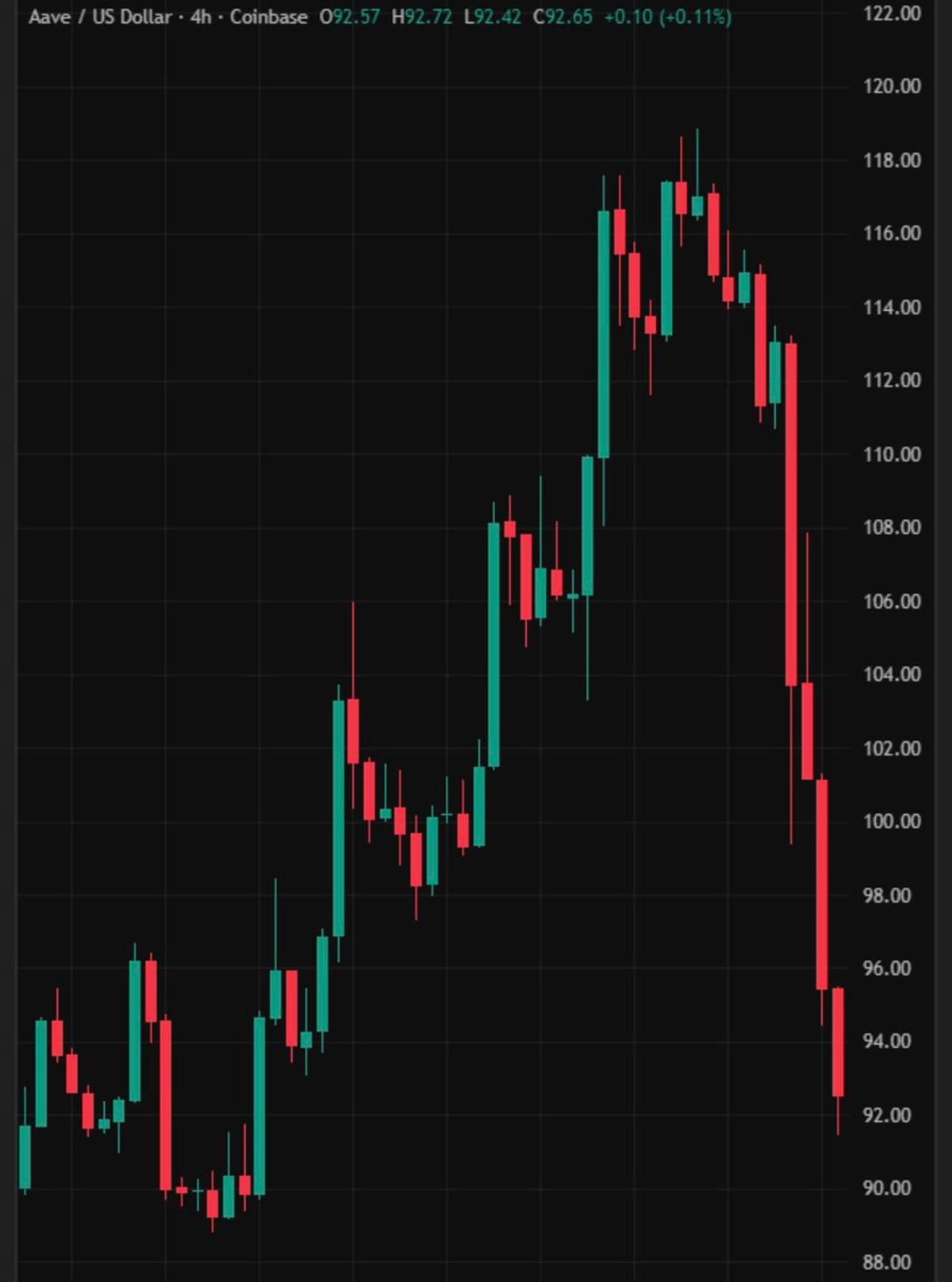
Aave Crashes 20% as rsETH Exploit Empties ETH Pool
💥 JUST IN: $AAVE is down -20% today after a $292M Kelp DAO rsETH exploit triggered a liquidity crisis. Aave's ETH pool just hit 100% utilization. That means there's almost no ETH left to withdraw now 😐😐 https://t.co/IdwkDX8KMc

Cross‑border Cooperation Essential to Curb Sophisticated Global Scams
With “the increasingly internationalized nature of scamming and the techniques becoming more sophisticated, governments and companies really need to do more—especially on cross-border cooperation—to crack down on scammers. Via @sharivahl @BBC https://t.co/quprxzVKlm

VPC Endpoints: Security Gains Vs. Complexity and Cost
AWS VPC Endpoints are so complicated and expensive but I really want to use them. They provide a unique level of security that a NAT does not replicate. The problem is the rabbit hole you end up going down after...

Understanding Man-in-the-Middle Attacks in PV Systems
Cyber threats for PV: What are man-in-the-middle attacks and how do they work #energysky -- via pv magazine global: https://t.co/skCBCwYMLQ

Basic Cyber Hygiene Beats AI Security Risks
What can regular people do about all the security findings of the latest AI models? My comments to Nicole Nguyen for @WSJ Our usual advice, but seriously, now more than ever: Keep software up to date Use long unique passwords Use a password manager Use...

DeFi Must Trade Efficiency for Stronger Guardrails
It’s hard to build in DeFi. Mad respect for everyone doing it like G. You need constant, never-ending vigilance against an evolving attack surface area Which is why I’ll keep saying it: we need to be comfortable trading some efficiency and...
Full‑Access AI Needs OS‑Level Sandbox Safeguards
AI agents are far more cable when they have full system access; but when they do, they can mess a lot of stuff up (not unique to any one model). AI harnesses have guardrails: but those can fail. I wonder if...

Negotiating with KelpDAO Hacker to Avoid Costly Loss
OK — Kelpdao hacker, how much you want? Let’s just talk. With KelpDAO’s help, of course. It’s simply not worth it to sacrifice both Aave and KelpDAO and let them go down over this hack. You can’t spend $300 million...

AI Hacking Tool Threatens U.S. Security, Urgent Hardening Needed
I was hanging out with one of the best hackers in the world last night. He has a model that finds more security issues than the Anthropic “for special people only” model. It is the scariest technology I have ever seen. There are...

Beware: X DMs Vulnerable to Hacking Attacks
I almost fell victim to an @X hacking attempt. Likely, the same people who got @SharkAlertsBio. Folks, be REALLY careful these days, especially with DMs.
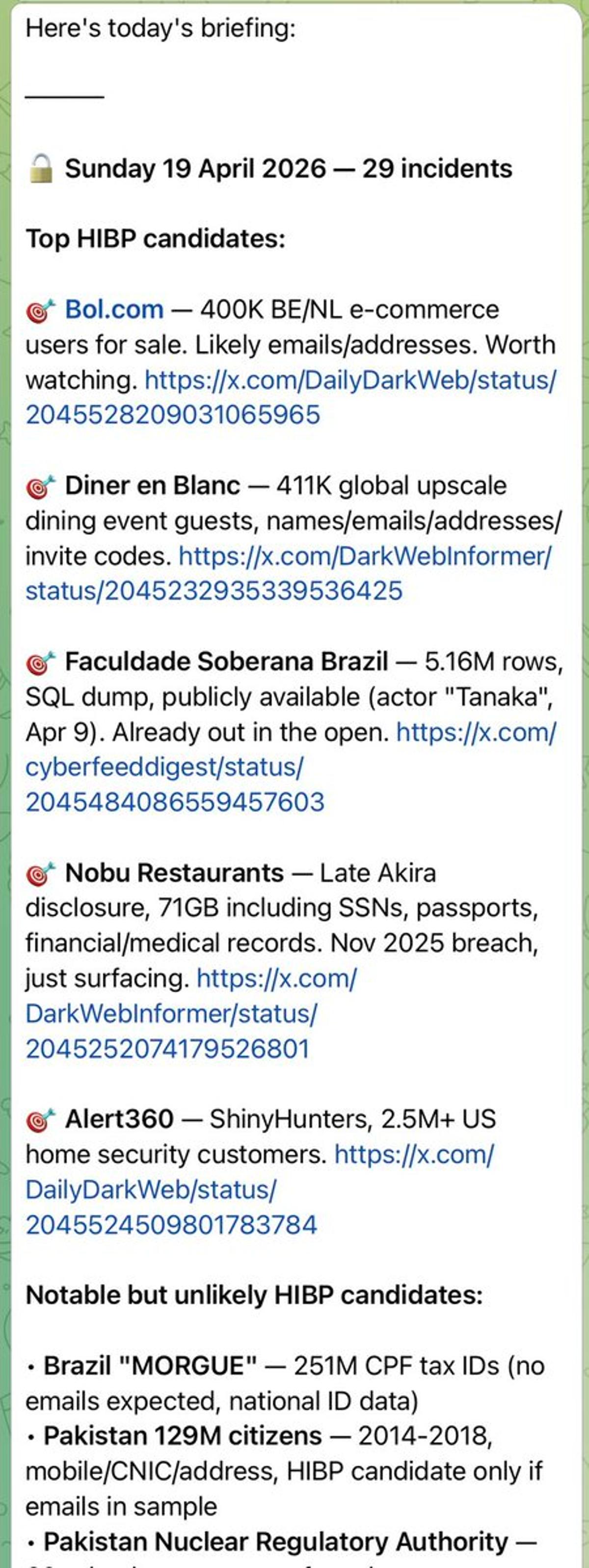
Automated 4 AM Tweet Summaries Power Daily Breach Reports
Been doing something very similar to this for my daily breach reports: each day at 4am it pulls all the tweets from this list and summarises them into a report: https://t.co/pT8dTLPnnY https://t.co/yuYqQs7zFq

Key Breach Triggers rsETH Theft; Protocol Safeguards Liquidity
We are continuing to investigate the L0/rsETH incident, initial reports seem to indicate a private key compromise/bad config allowed ~200m worth of rsETH to be stolen, this was then deposited into Aave to borrow ETH (since rsETH has insufficient liquidity)....