
China's Critical Sectors Run Vulnerable Software, Lack Oversight
NYT: “Inside China, researchers and the broader A.I. community have been watching…The country’s banks, energy companies and government agencies run on the same software in which Mythos found vulnerabilities—but for now, they have no seat at the table.” https://t.co/45lu2SGkPE
GDPR Enacted 2016, Compliance Deadline Passed 2018
#WaybackWeekend. April 14, 2016. #GDPR was first enacted. Any individual or business that handles personal data had until May 28, 2018, to begin following the GDPR rules. #Data #Privacy https://t.co/B68gph1gYn

US State Dept Issues Global Alert on Chinese AI Theft
Exclusive: US State Dept orders global warning about alleged AI thefts by DeepSeek, other Chinese firms https://t.co/pddPI6zgPF

AI's Growing Hacking Capabilities Raise Major Security Threat
AI has got better at hacking—how big a risk is it? https://t.co/pznks07gha via @YouTube #mythos #AIrisk #artificialintelligence #AISecurity #cybersecurity #cybersec @AlbertoEMachado @Eli_Krumova @postoff25 @Khulood_Almani @anand_narang @NutritiousMind @baski_LA @TanyaSinha_ @devaang @AlAmadi1 @jeancayeux @enilev @efipm @mvollmer1 @Nicochan33 @RagusoSergio @FrRonconi @Shi4Tech @sallyeaves @LaurentAlaus @Fabriziobustama @smaksked...
DeFi Veteran Fears On‑Chain Funds After Kelp DAO Hack
Five years building DeFi and @kaiynne says he’s never been more scared to have money on chain 😬 This is what the Kelp DAO hack aftermath looks like from the inside. @tayvano_ @LucaNetz @odysseas_eth: https://t.co/fnHoG3xB5V

Enable WhatsApp Two‑Step Verification: Simple, Better Than Nothing
Whether you just joined @WhatsApp or have been using it for years, it's a smart idea to enable two-step verification. Here's how, step by step, and why it's not as good as 2-factor authentication, but better than nothing... https://t.co/KDT8J6yjkd #whatsapp...
PoW Blockchains Repeatedly Vulnerable to Rollback Double-Spend Attacks
This isn't an isolated incident. There have been many of these rollback-and-double-spend attacks against Proof-of-Work-alone blockchains both years ago and recently, including recently against Monero and Grin.

Beware: Fake Login Alerts with Password Reset Links
Received an email from X warning you of new or unusual login attempts, with a handy 'change password' link? Beware, it's a slick new phishing attack that can trick even the most vigilant user. I've seen this with other sites...

Phishing Lockout Resolved Quickly Thanks to Community Support
Two days after falling prey to a phishing attack and getting locked out of my account, I'm back in. Sincere thanks to @X for resolving this so quickly. So grateful also to @lisaabramowicz1, @Brad_Setser, @AnnaEconomist, @baselinescene, @GagnonMacro and many others...

Your Router Silently Tracks You—18 Ways to Stop It
Your Wi-Fi router isn't "accidentally" tracking you. It's a feature, not a bug. I searched for a specific medical symptom once. 10 minutes later, my partner had an ad for it on their laptop. It’s called "IP-Bridging," and it’s happening through...

Kelp DAO Hack Used Spoofed RPC Node, Not Contract Exploit
The Kelp DAO hack wasn’t a contract exploit. It was a spoofed RPC node. @tayvano_ explains why that’s a harder and scarier attack vector. @kaiynne @LucaNetz @odysseas_eth Watch this: https://t.co/cBvUpFPcrk
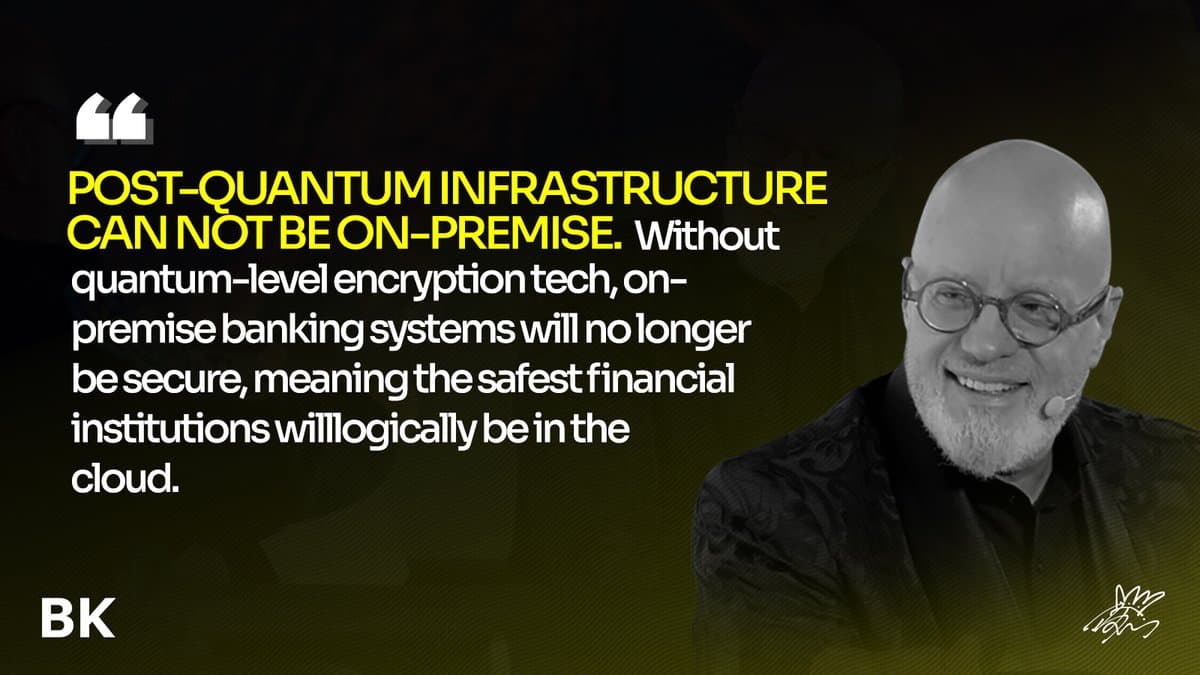
Banking Must Adopt Post‑Quantum Standards, Embrace Cloud
If banking systems cannot evolve to post-quantum standards, they risk becoming structurally insecure. The cloud becomes the logical foundation. https://t.co/4ZvlgernJn

Unified Observability Bridges SOCs and DevOps
RT SOCs and DevOps will need shared observability for agents: data access, tool calls, MCP interactions, and risk levels in one view. #Security #DevOps @Star_CIO https://t.co/tRGwCPc4Mb

AI Guardrails Needed for Secure Non‑Custodial Privacy
Privacy and non-custodiality is extremely important to avoid your information leaking. At the same time non-custodiality has led to easier way of stealing funds. We also need additional levels of AI based security which runs on account level and can...
AI Spam Pretends Victor Hugo Invites You
Last AI scam email of the day: Victor Hugo just emailed me to ask me to be part of his book club. Holding out for Moliere to contact me.

Phishing Attacks Surge, Spreading Anxiety Across All Channels
It’s hard to overstate the acceleration in frequency, cleverness and diversity of phishing and targeted exploits across every media channel over the past month or so. Have experienced it personally but also via friends and family, several of whom have...

KelpDAO Attack Timeline Discrepancy Challenges LayerZero Claim
Did something change between December of 2024 and now? Because unless I'm confused, this is saying that the attack on KelpDAO could not have happened as LayerZero described it.

Parallel AI Agents and Result Aggregation Boost Offensive Success
Sometimes success of using AI agents for offense is using them in multiple or parallel rounds. With different models. And aggregating the results.
New Wiper Links Venezuela Oil Firm to December Hack
Mystery around Venezuelan cyberattack deepens with new discovery of "highly destructive" wiper. Hard-coded into the wiper was the domain for Venezuela's state-run oil company, suggesting the wiper may have been used in December's attack against company https://t.co/v0gHlATx4w

Microsoft Now Lets You Pause Windows Updates Indefinitely
Microsoft will let you pause Windows Updates indefinitely, 35 days at a time. This is a good change, and it makes sense security wise that Microsoft wouldn’t let you totally disable updates https://t.co/rs0FWzHBtZ

GitHub Actions Less Secure Than Private Lambda Deployments
Hardening GitHub Actions: Lessons from Recent Attacks | Wiz Blog ~ really good article but I wrote about why I won’t use GitHub actions at all on a cloud instance. Not as many protections as you can get with Lambda...

Common Insecure Default Becomes De Facto Standard
What I found sharp in this segment: @TuongvyLe12's point that when 47% of teams choose the same insecure default, it stops being an individual choice and starts looking like industry standard architecture. @kkirkbos @DEXintheCityPod https://t.co/dgATW3fh8c

DeFi Must Harden Infrastructure and Adopt Transparent Governance
Takeaways from Kelp crsisis so far: 1. DeFi needs to be military-grade finance -- it has state actors going after it and the infrastructure better be strong enough to fight this enemy. right now, it's not. Stop using centralized infra, with...

AI Tools Empower Cybercriminals to Steal Money and Data
AI tools are making it easier than ever for online criminals to trick people and steal money and valuable confidential data.

Vulnerability Economics 2026: Deep Insights and Future Outlook
One of my favorite humans talking about one of my favorite topics: Mark Dowd goes deep into what vulnerability economics looks like in 2026, and where he thinks it goes from here. In true TBP-style it's long (2h) but it's...

Wave of Account Hacks Prompts Call for Platform Action
A number of folks accounts have been hacked recently, including it seems Robin Brooks -- please read this X needs to do something; I haven't been hacked but I have seen a wave of bad impersonators https://t.co/t06AZKPM5y

Cybersecurity Now the Gatekeeper to Business Growth
Cybersecurity is becoming a gatekeeper to business. Companies that can’t prove strong security risk losing access to supply chains, insurance, and markets. Cyber maturity is now a key differentiator for growth. https://t.co/Qup5czOaF2

DeFi’s $300M Kelp Hack Forces Liability Debate
The Kelp DAO exploit put a real number — $300M — on the question DeFi keeps avoiding: Who's liable when the infrastructure fails? @kkirkbos @TuongvyLe12 and Jessi Brooks on @DEXintheCityPod. 🎧 Timestamps: 🎙️ 0:00 Introduction live from the Eve Wealth Summit, Phoenix 🔓 2:08...

Secure Crypto with SOPs and Hardware Wallets
Learn how to deal with crypto: → Use a hardware wallet → Sign from a dedicated computer → Build an SOP: verify the data, simulate the tx, validate expectations, etc → Run the SOP every single time. No exceptions. Start today, don't wait until you...

Cybercrime Goes Corporate: AI‑Powered Attacks Demand Faster Security
Cybercrime is no longer a side hustle. Groups run like companies, with R&D, automation, & AI in daily use. They test, refine, and scale attacks with speed. AI gives them faster recon, stronger impersonation, and wider reach. If you build fast, secure with the...

Beware: @Teasri Hacked, Fraudulent DM Links Circulating
New scam underway. Unfortunately @teasri appears to have been hacked. DMs are being sent with a link that certainly appears fraudulent. Be on guard.

Botnets Conceal Origins While Powering DDoS Attacks
The botnets are used to hide locations and launch Distributed Denial of Service attacks. https://t.co/s6FzDuqe1h
AI Enables Hyper-Personalized Scams Exploiting Your Data
AI is making scams far more personal. Messages can now be tailored with real details about you, making them harder to detect and more convincing. The shift is subtle but serious. The more AI knows, the easier it becomes to exploit trust....

Mid-Size Firms See Cybersecurity as Essential, Not Optional
From ISMG: cybersecurity is becoming a must have for mid sized firms, not a nice to have. https://buff.ly/HzPfKHs The interesting shift is not the decision to invest. It is how organizations are deciding what actually moves the needle.

Bounty Platforms Need Spam Detection Like Email Systems
Instead of no bug bounty companies like HackerOne need to figure out how to flag potential bounty spam the same way email systems flag spam.

Infra Provider's Data Integrity Breach Triggers Real WTH Moment
A terrible incident coming from an infra provider. This is not an outage resulting in downtime, or data lost on the cloud (that is trivial to restore from local git.) It’s a data integrity issue, which sounds hard and difficult to...

Hidden ID Bug Lets Sites Track Private Mode Users
Researchers found a bug where websites could create a hidden ID and track users even in Private Mode. https://t.co/BkljdOYXC0

Quantum‑Safe Becomes Mandatory Baseline, Market Will Price It
My prediction about post-quantum security: we'll see the same thing we saw with privacy -- one day, out of the blue, quantum-safety will no loner be optional. It will become a consensus baseline requirement, the obvious feature that chains...

Bugs Aren’t the Whole Story in Cybersecurity
The amount of squabbling over bugs, bug quality, AI bug extermination, how security is doomed/not doomed/unchanged/improved based on bugs… it’s ridiculous. Bugs are not the totality of cybersecurity.
AI Will Empower, Not Undermine, Security Teams
Somebody asked me here at the conference: given AI advances, are we fucked in D&R and SOCs? I said “no, AI will help a lot here, this is fine, defenders will be fine.” (1/2)

Unstructured Data Security Hindered by Visibility Gaps
One of the biggest security challenges with unstructured data is the lack of visibility and lineage as information moves across systems, clouds, and teams." #DataLineage #AI https://t.co/PYomJYHDkY
Sony's 2011 Breach Exposed 77 Million PlayStation Accounts
#ThrowbackThursday. April 17, 2011. Sony began to notice its users about an attack that later disclosed to have compromised around 77 million of its PlayStation accounts. (CBS) https://t.co/iqjhF3SGSx

FCC Urges Court to Dismiss Hikvision Suit over Security Risk
.@FCC urges DC Circuit to reject Hikvision suit: "In any event, Hikvision’s arguments are meritless, particularly in view of the Secure Equipment Act, which ratifies and confirms the Commission’s authority to refuse equipment authorizations based on an unacceptable risk to...
Meta Turns Employees Into Data Source for AI Replacements
Meta is recording employee keystrokes, mouse movements, and screenshots across Gmail, LinkedIn, VSCode, Wikipedia. Stated purpose? training data for computer-use AI agents. Translation? the white collar workforce is now the dataset for its own replacements. Passwords, product roadmaps, immigration status, health info, all...

Powerful AI Models Learn to Self‑Jailbreak Automatically
I mentioned this project in this week's AI Lab newsletter. It suggests a kind of flip side to the idea of self-improvement in AI models. As models become more powerful, it shows they can automate the process of figuring out...

Guard Your Credibility: Vet Every LinkedIn Connection
Friendly reminder that you shouldn't accept a connection from just anyone who asks to connect on LinkedIn. I see sham accounts that have legit people connected to them. They're obviously using these connections to lure others into connecting. Don't lend...

FIRESTARTER Maintains Post‑patch Persistence on Cisco ASA/FTD
"FIRESTARTER can persist as an active threat on Cisco devices running ASA or Firepower Threat Defense software, maintaining post-patching persistence and enabling threat actors to re-access compromised devices without re-exploiting vulnerabilities" https://t.co/wVwgbLKaNj

Choose Your Protocol Wisely After Kelp DAO Exploit
"You have to make decisions on which protocol to trust" - @MiguelMorel on the Kelp DAO exploit https://t.co/C0Okymb2f3

Prioritizing Cyber Risks Beats Mere Awareness
One of the hardest parts of cybersecurity right now is not awareness. It is prioritization. Everyone knows there is risk. Few teams are aligned on what matters most. How do you know if you're tackling the most important risks for your organization?

Arkham Reveals Blockchain Intel as Kelp DAO Loot Freezes
The Kelp DAO loot is moving onchain and Arkham has had a front-row seat to the action. 🚨 Up Next on the stream today, Arkham CEO Miguel Morel joins me to discuss what his team has seen and how blockchain intelligence...