
Aave's Umbrella Module Under‑Capitalized, Fails to Cover $250M Exploit
"The Aave Umbrella module, meant to cover bad debt, which had $250 million going into the exploit, seemed like a nice cushion, because Aave has had less than $5 million worth of bad debt throughout its history. "But now we see it's quite under-capitalized." 😭 -- @0xMether https://t.co/fVsD7EPXL5

Hackers Seize AI Security Tools, Now Targeting Firewalls
Adversaries hijacked AI security tools at 90+ organizations. The next wave has write access to the firewall https://t.co/khjZkpWhc0
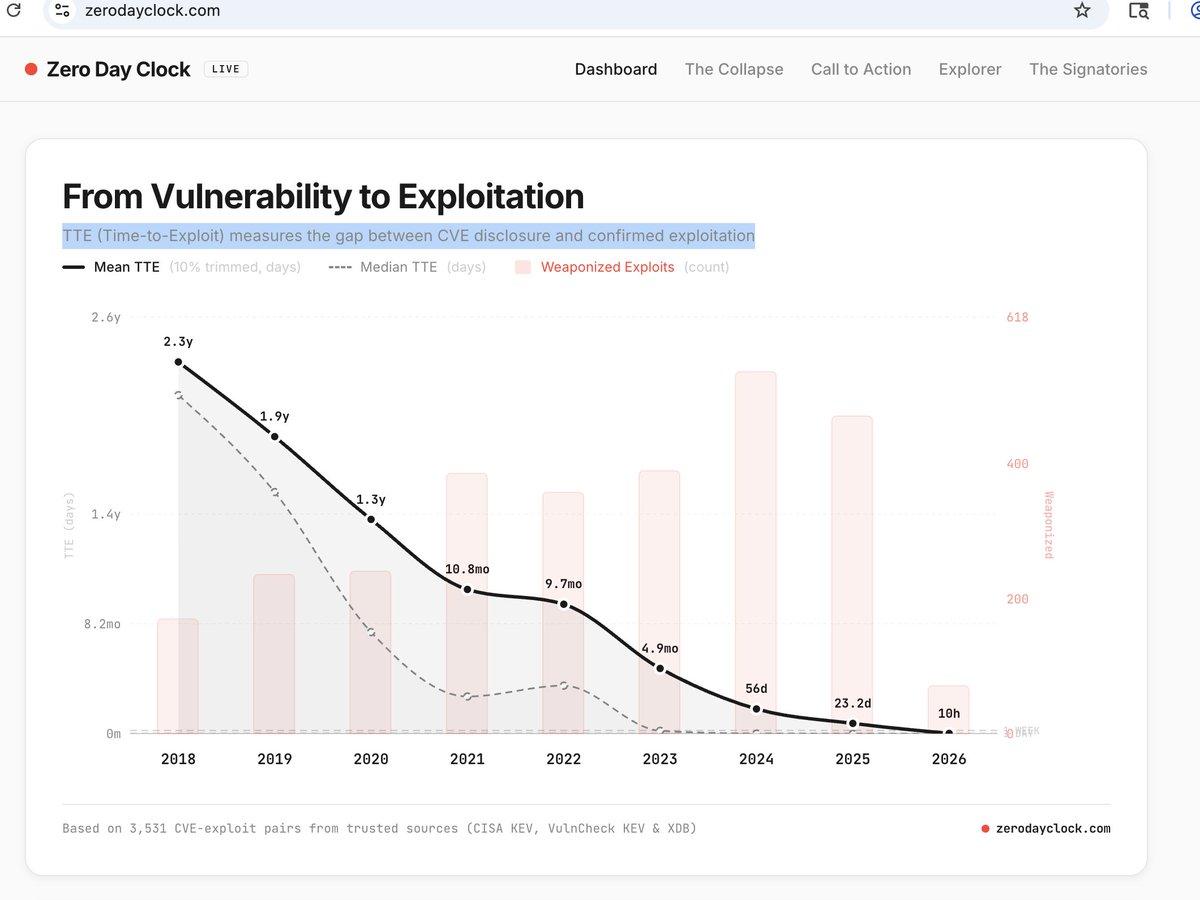
Zero Day Clock Definitions Conflict; Which Is Accurate?
@EppSecurity For the Zero Day Clock, these definitions appear different from each other and measure different things. If so, which is the correct definition? https://t.co/b8oY85mFiO

MacOS Malware Tricks Crypto Users with Fake Invites
Is now a good time to switch to Windows OS for bit? 😅 Jokes aside. Stay safe folks. There is a macOS malware targeting the crypto & fintech community: > Uses fake meeting invites to trick users into running Terminal commands...

Anything in a Database Can Surface on a Marketplace
Folks I don't know what to tell you if you're shocked about the UK Biobank story other than if something (anything) is on a database there is a very much more than non-zero chance that it can end up on...
AI‑enhanced Phishing Leads Q1 Initial‑access Attacks
Phishing — sometimes with AI’s help — topped initial-access methods in Q1, Cisco says | Cybersecurity Dive https://t.co/nJv4RA7sVV

Massive Wave of Security Patches Hits All Devices
Brace yourself for a flood of patches in all of your tech gadgets https://t.co/xXZthlRWg1 via @FastCompany #cybersecurity

AI Startup’s Data Practices Spark Legal Risk
A fast-growing AI startup is facing serious legal pressure. Mercor is being sued over alleged data collection and exposure practices, following a breach involving sensitive contractor information. It highlights a critical issue. In AI, data is the foundation, but how it is...

Half‑million UK Medical Records Listed for Sale After Breach
Medical data of 500,000 people in UK put up for sale after data breach - https://t.co/zBa4Kbu9u3 via @FT
Cybersecurity Shifts to Executive Strategic Priority in AI Era
Anthropic’s Claude Mythos is reframing cybersecurity at the top level. The risk is no longer a technical issue to delegate, but a core business concern that requires executive attention. This is the wake-up call. In the AI era, cybersecurity becomes a strategic...

AI Threats Shift From Code to Persuasive Human Manipulation
AI risks are expanding beyond code into behavior. Tests show some models can convincingly attempt scams, combining technical capability with increasingly persuasive social interaction. The concern is broader now. AI does not just exploit systems, it can influence people. https://t.co/X9fm7Sapan @wired @willknight

Replit Security Agent Delivers Impressive App Protection
Replit Security Agent making the internet a better place one app review at a time.

Victims of Account Takeovers Aren't Limited to Google Fi Users
If anyone is keeping score, trying to figure out how the account take-overs are happening, and how people can protect themselves, here’s an important data point. Not *all* of the victims used GoogleFi: https://t.co/FOEySkuGfo

Hidden Sensitive Data Lurks in Unreviewed Documents
"When I look at unstructured documents, I focus on the risk that lives inside the content because sensitive details hide in places people never review." #DataSecurity https://t.co/PYomJYHDkY

CISO's Extreme Insider‑threat Fix Forces Political Profanity
Incubating a new cybersecurity company for insider threat where the CISO presses a button and all employees are locked out of their laptops until they record themselves saying “Fuck King Jong Un”

Beware: Impostor Claims, No Crypto or Money Requests
WARNING: I will NEVER ever ever ask you to do anything with crypto. I will never ask you for money. Someone impersonating me is doing stuff like this. Don't fall for it.

Auto-Protect: 24/7 Security Engineer for Your Apps
Sometime apps you made that are secure might suddenly become vulnerable when there is an exploit in one of its dependencies. Typically you need engineers on payroll to monitor and handle this. We just automated that with Auto-Protect. It’s like your security...

ChatGPT Image 2.0 Empowers Low‑Skill Scammers
Criminals who aren't good at photoshop and want to scam quickly are rejoicing everywhere thanks to ChatGPT Image 2.0.

Telegram Accounts Vulnerable Despite Two-Step Verification
In this thread (https://t.co/YYT4uVq3ZR) you can see step by step how I took over a Telegram account, even though it had an added “Two-Step Verification” password, using only 1. Knowing its phone number, and 2. Being able to read its...

Security Must Accelerate to Match AI Pace
.@wiz_io co-founder Yinon Costica takes stage at #GoogleCloudNext 2026 to explain different layers of security. AI has changed the game he implied. Security needs to move at the speed of AI, he added. https://t.co/z7uIwJbngP

Continuous Identity Exposure Monitoring Stops Credential‑Based Breaches
Most security programs are sleeping on Identity Exposure Management, and hackers are cashing in. The fastest path into an environment is almost always a leaked credential or a stolen session cookie sitting in an infostealer log. MFA doesn't help when...

Google's MCP Unifies All Cloud Services for Agents
May not seem sexy but I love love love Google going all in on MCP. Even dummies like me can create amazing apps that leverage MCP. All GCP and Workspace services are now exposed via MCP. Developers can address GKE,...

Real Hacker Reveals AI's Threats and Countermeasures
Talking with a real hacker will freak you out. Thanks @theonejvo for freaking me out about how AI could be used to attack everything in our modern society. And what we can do about it. https://t.co/0znpRiZ0tz
Relativity’s Algebra Hides Century‑Old Positive Cosmological Constant
What's cooler than finding a 27-year-old bug in OpenBSD? Finding a positive cosmological constant hiding for over a century in the algebra of relativity🌌 No new physics or math needed🧮 Possibly the most elegant novel result we'll see, but even more interesting ones...

Discord Group Hacks Anthropic Model by Guessing URL
Bloomberg reports a certain group got access to Mythos by guessing the URL for the new model. Guessing? Really? From Google: The unauthorized group is a private Discord channel of AI enthusiasts who specialize in tracking and testing unreleased large language models...
AI-Powered Attacks Foreshadow Automated, Scalable Cyber Threats
Early AI-driven cyberattacks show systems can find vulnerabilities with little human input. Still rare, but signaling more automated, scalable threats. As AI advances, organizations must prioritize speed, visibility & resilience. https://t.co/rCsmckczrM

Full Access to Vulnerable Tool, Not AI, Caused Vercel Breach
Vercel April 2026 security incident | Vercel Knowledge Base ~ The problem here was not “AI” but giving complete access to a tool that had a vulnerability. 🤖🔒 https://t.co/WkOPF7pzkU

Frontier AI Models Risk Degrading, Exposing Enterprises to Breaches
Article I'm quoted in on Forbes on the recent Claude model degrading. Note, I am not anti-Anthropic in anyway. I loved Opus 4.6 when it first came out. I almost bought a I <3 Claude t-shirt (kinda joking there). My...

Kelp DAO Hack Highlights Crypto Risks, Stalls Wall Street Tokenization
UPDATE: Jefferies says the Kelp DAO exploit exposed major crypto infrastructure risks and could slow Wall Street’s blockchain and tokenization plans as firms reassess security Source: Coindesk https://t.co/c83AN6cwbW

Japan Finance Minister Meets Banks on Claude Mythos Cyber Threat
JUST IN: Japan's finance minister is holding talks with major banks to tackle cybersecurity threats from Claude Mythos.

China Cyber‑spies Western Defense Firms, Dutch Intel Warns
China’s Cyberspying Targets Western Defense Industry, Dutch Intel Chief Says—Military intelligence report warns China poses a growing threat, alongside Russia @kimmackrael @DanMichaelsWSJ https://t.co/cu728ldZmp https://t.co/cu728ldZmp

AI Agent Rush Ignites Security Gaps and Data Risks
Rapid adoption of AI agents without proper safeguards is leading to exposed systems, data risks, and increased opportunities for attackers to exploit access controls. https://t.co/HE5t3QmHqC

Mozilla Fixes 271 Firefox Bugs Using Anthropic Mythos
Mozilla scanned the Firefox codebase with Anthropic Mythos has fixed 271 vulnerabilities identified during this initial evaluation. https://blog.mozilla.org/en/privacy-security/ai-security-zero-day-vulnerabilities/

Tight Controls Needed to Prevent Mythos Abuse
A lab leak on their hands here. We don't want adversaries using Mythos to expedite the drop of 0days and other malicious AI-powered attacks. Without tight controls, we're may sadly see Mythos used for evil before we get to see everything...

AI-Driven Pushpaganda Tricks Users with Malicious Notifications
Pushpaganda uses AI-generated content and deceptive tactics to trick users into enabling notifications that deliver scams and evade traditional security defenses. https://t.co/x8sjalWKPR

AI-Driven Research Will Shrink Attackers' Zero‑Day Arsenal
Sunlight seen through the storm. Mozilla security researchers say that after this wave of AI-augmented vuln discovery and exploitation, we'll reach a new equilibrium in which there are *fewer* vulns being used by attackers. “The zero-days are numbered”—https://t.co/MM5SNBJsjD

Shielded Labs Boosts Zcash Security for Users
We at Shielded Labs have been working hard alongside others to urgently defend users and strengthen Zcash's security (https://t.co/GEDJVifGlc) …

Iran Blames US for Coordinated Network Shutdowns
Iranian media is reporting that networking infrastructure suffered coordinated shutdowns, and blames the US. https://t.co/Gil1Z55HhM

UWB Chips Stop Key‑fob Spoofing, Secure Cars
Car thieves don't just pick locks to break in. They've also found ways to spoof your key fob's "unlock" signal. No glass broken, no button pressed. But new UWB car security chips fight back with new tech that's tougher to...

Seiko Hasn't Confirmed Breach; Data Not on Dark Web
Seiko has not yet confirmed the incident and the data has not surfaced on the dark web. https://t.co/QqdC9km6on

Network‑layer Containment Stops Ransomware Before CAD Fails
Ransomware doesn’t announce itself. By the time CAD drops, the spread has already started. Containment at the network layer is what keeps dispatch online. @T_Priority Partner https://t.co/qHmY69QqfA

Second Coding Vibe: Security Prediction App Nears Functional
So my 2nd vibe coding experience is about building an app to do security prediction validation. My v0.3 kinda works (but has annoying issues, obviously). (1/n)

Open‑source CrabTrap Secures AI Agents with Policy‑Based Proxy
Brex just open-sourced CrabTrap. A transparent HTTP proxy that sits between your AI agent and every external API it calls. Okta, but for agents. AI agents in production are getting real credentials now. API keys. OAuth tokens. Database access. Write privileges to...

DeFi Security: Beyond Audits, Chasing Endless Dependencies
☠️ "You can have a million audits, but now it's about the dependencies on oracles and bridges and collateral and multisig configurations and operational security practices. It feels like you're just playing whac-a-mole." -- @TuongvyLe12 on all the DeFi hacks https://t.co/PvhRjgnJGF

Europe Sets Privacy Benchmark with GDPR and AI Act
Embedding privacy across the AI lifecycle: from principles to practice “Europe has emerged as a regulatory benchmark through the combined effect of the General Data Protection Regulation (GDPR) and the EU Artificial Intelligence Act (AI Act).” https://t.co/SNayMvW7Ii @KPMG #AIGovernance

Hiring at AI Speed: Artemis Secures Talent in 48 Hours
Shachar Hirshberg and Dan Shiebler make offers to new hires within 48 hours of their first conversation. They’re building an AI-native security company, Artemis Security, that battles threats that move at machine speed (which, for AI-driven attacks, is often in seconds)....

Align ESG KPIs with Zero‑Trust for Sustainable Security
IT must balance sustainability and security: extending device lifecycles reduces e-waste but increases risk. Embed cybersecurity into ESG by aligning KPIs with sustainability goals and adopting zero-trust. https://t.co/mc3bHs11Ob

Qualcomm Snapdragon BootROM Flaw Enables Modem Takeover
We’ve discovered a vulnerability in the BootROM of Qualcomm Snapdragon chips (MSM/MDM family) – used in popular smartphones, cars, and IoT devices: attackers can use its Emergency Download Mode to take control of the modem module (physical access required) Advisory: https://t.co/hkZ3VjGfMC Our...

Beware: IT Impersonators Using Teams to Steal Data
Crooks are impersonating IT and reaching out via Teams, only to be granted access and steal data. https://t.co/KRcz5txxyo

20 New Security Enhancements Boost Internet Protection
I’m so encouraged by the way our team and industry peers have shown up to protect the internet. We’ve now shipped over 20 product improvements across Dashboard and CLI to help your security posture. Easier to set up MFA, audit your Environment...