
AI Reshapes Bug Bounties: Insights From Industry Veterans
If I had a nickel for every time I was asked "How does AI impact bug bounty programs" last week, I would have several nickels... That's partly (*) why it was a hoot to sit down with my long-time vulnerabilityresearch trench-buddy tod beardsley and the runzero crew for a chat about * = The other part is that Tod is legend, and jamming with him is fun no matter the context https://m.cje.io/4bVbgru

Apple Patches iOS 18, Shields Even Older Devices From DarkSword Malware
Apple has patched iOS 18 to protect users from the DarkSword malware, even if they have an older device. https://t.co/hePrmRekFx

Key‑compromise Attacks Demand More Work than Usual
re Drift: "As far as key compromise hacks go, they had to do more work than normal." 😂 -- @tayvano_ https://t.co/TvMSeHiXJj

Solana's Transfer Limits Vulnerable to Hacker Manipulation
"Solana has all these policies. They have a limit on how much money can be moved at any given time ... but that limit can be changed by the hacker ..." -- @tayvano_ https://t.co/s7Jw0sjSwI

Only 1% Worry About AI Vulnerability Apocalypse
So why nobody (well, maybe <1%) care about the coming AI-powered vulnerability apocalypse? (ref @unpromptedconf vs #RSAC discussions, cc @gadievron ) #question

Malicious Axios Dependency Silently Compromises Projects
"They'll push a dependency to Axios so that anyone who used these packages or worked on projects that had these packages in them are compromised. Then they get one person on a call and make them run that... It's silent...

Thousands of API Keys Exposed, Highlight Ongoing Security Gaps
Researchers examined millions of webpages and found thousands of exposed API credentials, revealing persistent security gaps across cloud services and development environments. https://t.co/loHYTptzxC

US May Push Tencent Gaming Divestiture Over Privacy Risks
The FT reported earlier this month that the Trump administration is considering forcing Tencent to divest certain gaming assets over security concerns. The notion that gaming assets, particularly mobile gaming assets, could be useful in user-level profiling is not implausible; recall...
Agentic AI Unifies ITOps and SecOps for Resilience
RT Most orgs still treat ITOps and SecOps as separate universes, but incidents don't care about org charts. Agentic AI gives leaders a reason to redesign workflows around end-to-end resilience. #CIO #CISO #AI @Star_CIO https://t.co/e3w3lXkvfc

Quantum Threat to Bitcoin Imminent—Start Solving Now
Regarding the Quantum threat to Bitcoin: It's not a question of if, it's a question of when. And if when is being pulled closer by best estimates, then it's common sense to start discussing solutions. That's not FUD or hysterics,...

Illegalizing Ransom Payments Would Protect Future Victims
We would all have been much better off if we had made paying a ransom to ransomware criminals illegal. Tough for the first few victims, but then better for all.

Beware: This Account Is Impersonating Me
THIS IS NOT ME! Don't fall for any posts made by this account pretending to be me.
Red‑team Your AI: Guard Against Fraudsters and Edge Cases
Your AI harness needs to handle adversarial inputs Financial services aren't just about helpful customers asking good-faith questions It's fraudsters, edge cases, and people trying to break your system for profit. If your testing doesn't include red-teaming, you're not ready

Prompt Injection Lets Agents Bypass Read‑Only Permissions
If you are using OpenClaw on AWS or anywhere else please understand the following: > How prompt injection attacks work such as the Copilot attack I just reposted. > Understand indirect prompt injection where the attack is in a calendar invite, email...
Chrome Extensions Silently Adding Tracking—Build Your Own
I think I'll just vibe code all my Chrome extensions with Claude Code to avoid having to use any and being dependent on someone getting bribed to add malware to their extension It's not a question IF it happens, just WHEN

Restrict Agent Permissions to Mitigate Data Exfiltration
Why I am using agents on locked down sandboxes on EC2 instances and still have more to do. I don’t give agents credentials for the most part. The data needs to somehow be exfiltrated and sent back to the attacker....
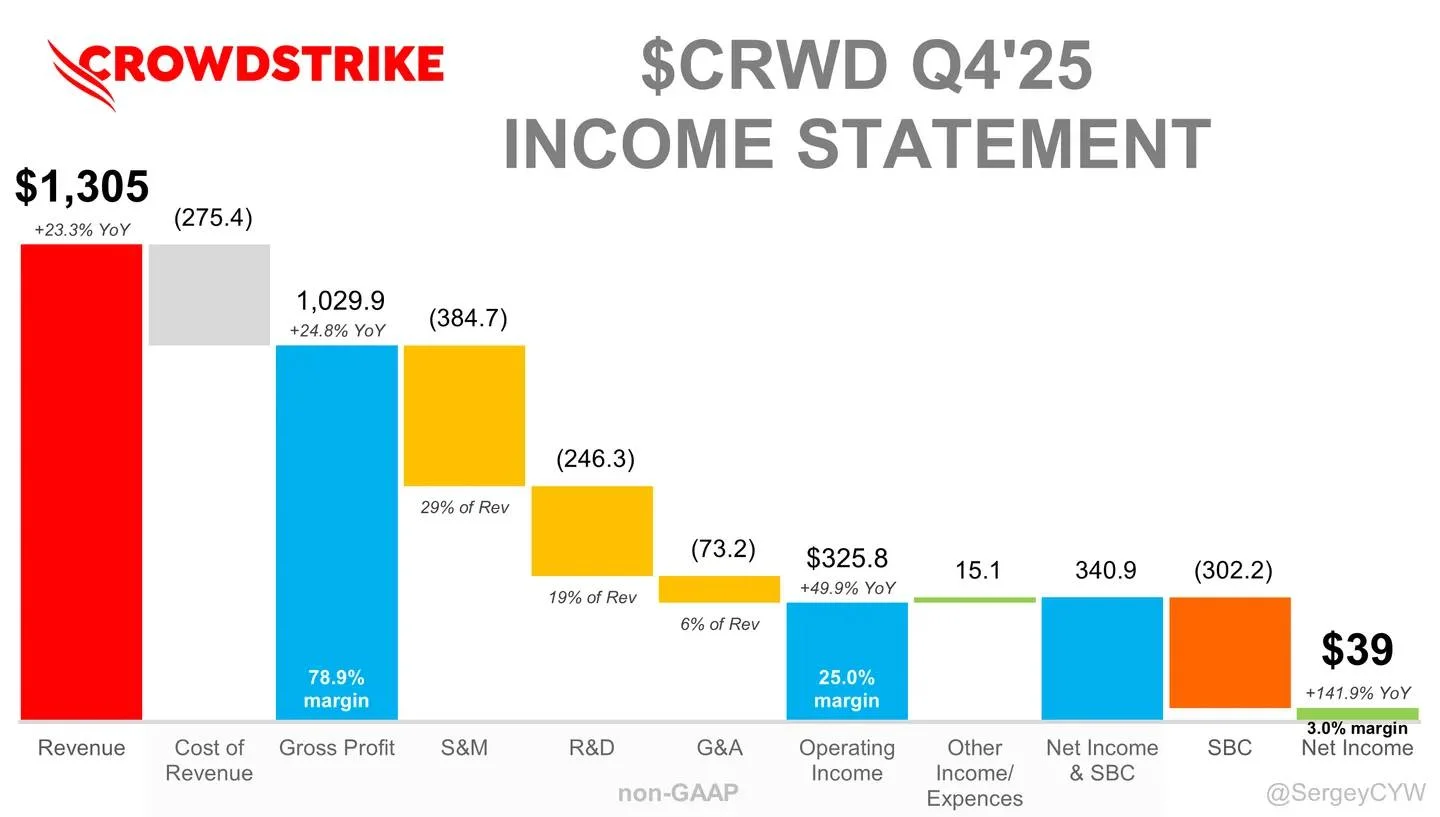
CrowdStrike Becomes AI Era’s Core Security Layer
AI-driven cyberattacks are scaling rapidly — and $CRWD is positioning itself as a core security layer for the AI era AI is not only increasing attack volume, but also redefining how attacks are executed. Security is shifting from reactive to autonomous. $CRWD...
Russia Bans Apple ID Payments to Curb VPN Use
Russia's Ministry of Digital Development has ordered mobile operators to disable Apple ID payments in a bid to make accessing VPNs harder. https://t.co/oKO2qFNeHk

Crypto's Security Flaw: Quantum Attacks Expose Real Risk
Literally the most braindead cope Newsflash: cryptographic currencies are vulnerable to cryptographic attacks Nic investing in quantum solutions to Bitcoin is conviction in the problem, not conflict of interest Focusing on the COI is denial cope
Quantum Computers Require Far Fewer Resources to Crack Encryption
Quantum computers need vastly fewer resources than thought to break vital encryption - Ars Technica https://t.co/pLuvHMFLOP

KiloClaw Releases First Public AI Coding Security Audit
🚨 KiloClaw just published something no AI coding platform has ever done. An independent 10-day security audit. Full findings. Public. Here's what every developer needs to know ↓ https://t.co/ykYrYWTIYX

Claude Code Source Leak Sparks Massive Online Uproar
Claude Code's entire source code has been leaked and the internet is up in arms. https://t.co/KcenyVm6zg

Data Sovereignty Now a Board‑level Infrastructure Priority
Sovereignty has gone from being a niche compliance concern to a board-level infrastructure priority. https://t.co/p9o7WKQHF9

OpenClaw's Powerful Automation Carries Significant Security Risks
OpenClaw can browse the web, run shell commands, and send emails on your behalf, but it comes with documented security risks that every user should understand before deploying it. https://t.co/UmAoMn8hSv

Anthropic Leaks 2,000 Claude Code Files, No Data Breach
Anthropic inadvertently included internal source code for its AI coding assistant Claude Code in a recent update, exposing nearly 2,000 files on GitHub; no sensitive customer data or credentials were compromised. cybersecurity

Banks Fail to Shield Your Money From Digital Scams
Your money is not safe. You are left completely exposed to digital financial crimes and e-banking scams. The latest BNM 2025 report proves that financial institutions are failing to properly protect you. Wake up before your hard-earned life savings vanish forever.
TEEs Have Been Fundamentally Flawed From the Start
I’ve been saying this for past decade at least. TEEs are a bad idea, from inception.

Align Security, IT, Ops for Disciplined Resilience
What does disciplined resilience look like when ResOps works? At @Commvault's ResOps Rumble at RSAC, Bill O'Connell asked a room of security leaders how many had perfect alignment across security, IT, and ops. Almost every hand dropped. @Commvault's Chris Bevil breaks down how...

Supply Chain Hacks Cripple Major Security and AI Tools
Rundown of the very bad week in security: - TeamPCP (sophisticated hacking group) attacks: Hackers broke into the system that builds a oss popular security scanning tool called Trivy. This was a supply chain attack (when bad code is slipped...

Iran's Threat Highlights AI as U.S. Security Issue
if iran has threatened to attack US AI companies and data centers does that mean AI is a matter of US national security or no? asking for a friend

Claude Code Leak Reveals Secrets Behind Its Powerful Harness
Claude Code's source files just leaked. We can finally see what makes the harness so good. Full breakdown: https://t.co/s7VRzoXdkj
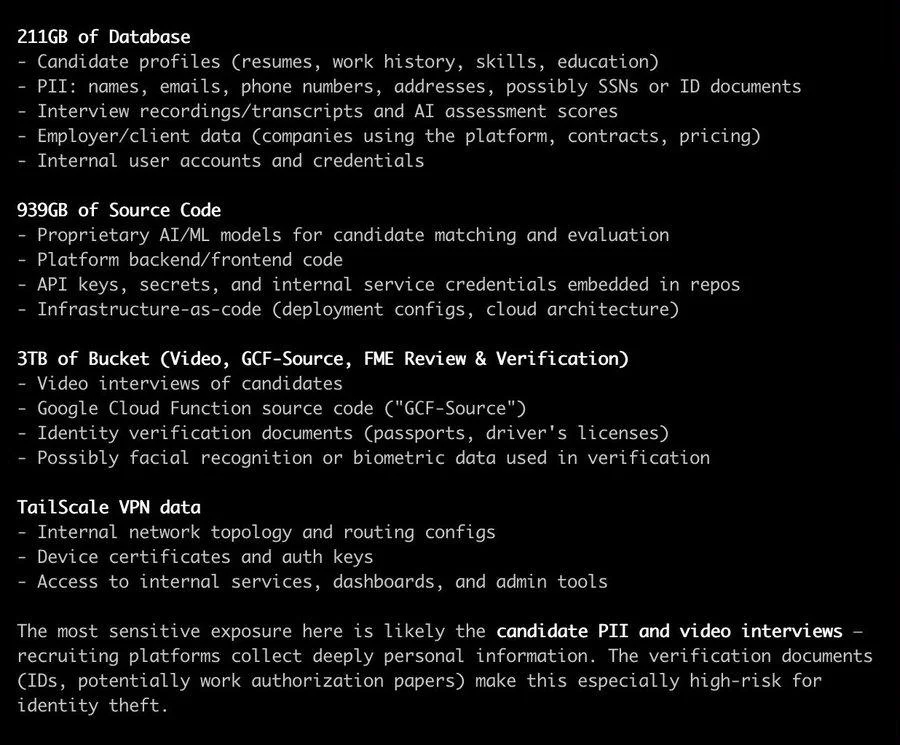
Mercor AI Hacked Amid Tailscale VPN Security Concerns
Is this because Tailscale VPN got hacked? or something else? Anyway, Mercor AI got hacked.

Massive JS Supply Chain Attack Threatens Laptops—Our Defense
If you’re coding on your laptop or most environments outside of Replit you might’ve been exposed to a massive JavaScript supply chain attack that can take over your computer. Here is what we do to protect our customers:

Secure Rust‑based AI OS: IronClaw Protects Agent Harnesses
Agent harnesses are the final operating system. Agent harnesses or “claws” are bringing a fundamental shift in computing, becoming the next-generation operating system with AI at its core. Unlike traditional OS that require users to navigate between apps, claws boot...

Attackers Leverage AI Faster Than Defenders' Policies
“Cyber criminals are the ones using AI most effectively.” One of those quotes from RSAC that stuck with me. Not because it’s surprising, but because it’s operationally true. Attackers iterate faster. They measure outcomes better. They deploy without governance friction. Meanwhile, defenders are still debating...

Cybersecurity Reckoning Arrives Sooner—Early 2027
Ok so the cybersecurity reckoning is happening a little faster than I expected (early 2027)

Supply Chain Attacks Threaten Trust, Server Checks Essential
Just had to check my servers to be sure, as I was working on stuff around this time frame, looks like all is ok. Supply chain attacks like this are becoming more of an issue, eroding the trust model. https://t.co/fOTLJCgCrH

Agentic AI Turns One Prompt Into System‑Wide Threat
From Anarchy to Authority: Closing the Governance Gap in Agentic AI “Agentic systems collapse the traditional attack chain in that a single manipulated instruction through prompt injection, tool misuse, or data poisoning can trigger disproportionate impact. Agency enables malicious intent...

Satoshi Warned of Quantum Risk, Urged Gradual Transition
JUST IN: Satoshi Nakamoto acknowledged Bitcoin quantum risk early in 2010, suggesting If it happens gradually, we can transition. https://t.co/P6PSea6doH

AI‑found Zcash Sprout Bug Fixed; Funds Remain Safe
Security Disclosure: last week a white-hat security researcher using AI found a bug in Zcash's old “Sprout” pool. Folks from ZODL and Shielded Labs worked together to fix it, and mining pools have updated. User funds are safe. Full report:...

AI Governance Gaps Enable Rogue Agent Threats
Governance around AI and data is still a significant problem. Many vendors still hesitate to talk about it. What Happens When AI Agents Go Rogue? https://t.co/5TE3g0hXng #CIO #CISO #AI #cybersecurity

AI Agents Turn Environment Into Attack Surface
AI agents don’t just inherit LLM risks — they amplify them. I came across an interesting paper: “AI Agent Traps.” Most discussions still focus on prompt injection. That’s already incomplete. Because once agents have: - autonomy - persistence - tool access...

Can Burning Satoshi's Coins Curb Quantum Risk?
Is burning Satoshi's coins the right path to solve [part of] the quantum threat? https://t.co/LVOy35zOxM
Quantum Threat May Reach Bitcoin Within One Block
Google now warns quantum attacks could happen within Bitcoin’s block time. Are we closer than we think? I’m speaking with Alex Pruden and Dolev Bluvstein about what this means for crypto. https://t.co/LVOy35zOxM

Elliptic Curve Crypto Underpins All Protocols—Removing It Requires Complete Rebuild
"Everything relies on elliptic curve cryptography. If you remove that foundation, you need to rebuild EVERYTHING. The issue? Most protocols use this." https://t.co/OMA9HmxIQs

Unsolicited Loan Data Leak Exposes Flawed Third‑Party Sharing
Great. My phone number was found on the dark web in conjunction with a breach of a site I don’t even use. Third party data sharing is not cool. Apparently it is a fintech blockchain HELOC company. Definitely did not...

Essential Security Docs Most Orgs Still Miss
Cybersecurity scales with process + templates 🔐 Key docs every org needs: 🛡️ InfoSec: incident logs, access matrix, data classification 🌐 Network: DDoS plan, VPN/NAC logs, patch schedule ☁️ Cloud: config baseline, IR log, backup testing, asset inventory 🧩 AppSec: secure coding checklist, SAST logs,...
Quantum Leap: 10k Atomic Qubits Threaten Crypto Security
From “millions of qubits” to ~10,000 atomic qubits. That’s a major shift. What does it mean for Bitcoin, Ethereum, and cryptography? We break it down live. https://t.co/OMA9HmxIQs

Quantum Leap Brings Excitement and Cryptographic Risks
"It's clear we are crossing a moment. It's exciting. We'll be able to use quantum computers. But it's CONCERNING too, because it'll be cryptographically relevant." Dolev Bluvstein https://t.co/OMA9HmxIQs

Quantum Leap Could Accelerate Crypto's Existential Threat
A new quantum breakthrough may have cut the timeline dramatically. On Unchained, Alex Pruden and Dolev Bluvstein join me to discuss: ⚛️ When quantum becomes a real threat 🔐 What breaks first in crypto ⏳ Whether we’re already behind https://t.co/OMA9HmxIQs