
AI Agent Identity Layer: Next Cybersecurity Frontier
I recently joined @reckless on @DecoderPod to discuss the “SaaSpocalypse,” the future of software, and why the identity layer for AI agents could become the biggest category in cyber. Really enjoyed this conversation: https://t.co/afZ84f2ymM
State Quantum Power Lies in Hidden Communications Exploitation
Ok I just want to add one thing. Folks, for state actors, the value of having a quantum computer is massively higher if you DON’T tell people you have a quantum computer. Exploiting Bitcoin is a parlor trick. Exploiting the world’s communications...

Victims Receive $27.92 Settlement After 2024 Evolve Hack
Remember back in 2024 when a Russian cybercrime group hacked Evolve and exfiltrated terabytes of data, including user data like SSN and account numbers? Victims are finally getting their settlement payments: $27.92 https://t.co/9rKUgGOh5I

Secure Hybrid Self‑Managed and Managed MCP Server Setup
You could use a mix of self-managed and managed MCP servers. Here's an example of using both, and securing them in a production-ready way. https://t.co/reHeaq6QEV https://t.co/5pLxHwGKWv

Anthropic's Claude Code Leak Exposes Internal Architecture
Oh boy, including "Undercover" Claude -> Claude Code's source code appears to have leaked via a misconfigured npm package, revealing internal codenames, a “Self-Healing Memory” architecture, and more "For Anthropic, a company currently riding a meteoric rise with a...

Dynamic Identity Systems Needed for Independent AI Agents
Identity for AI agents came up in almost every serious conversation last week at RSAC. It is not just “give them an identity.” It is that: identities are dynamic agents act independently and they will outnumber humans We built identity systems for people. Now we need...

BeyondTrust Reveals New Token Injection and Exfiltration Vectors
Where else can the tokens be injected and exfiltrated. This is the original report from BeyondTrust.

Autonomous Agents Risk Malicious Prompts Despite Sandbox Efforts
This is the type of thing I’m worried about with completely “autonomous” agents only the inclusion of something more malicious than ads. It could be unintentional or via prompt injection. I have some tools that can run while I’m sleeping...

AI Safety Becomes a Cybersecurity Priority
AI safety has entered the cybersecurity era. @IrenaCronin and I write this newsletter every week. AI safety is becoming a cybersecurity issue because advanced AI can now help both defenders and attackers, making the risks more immediate and practical. As AI systems...

DNS Covert Channel Bypasses AI Guardrails, Enables Remote Shell
“Specifically, it abuses a hidden DNS-based communication path as a "covert transport mechanism" by encoding information into DNS requests to get around visible AI guardrails. What's more, the same hidden communication path could be used to establish remote shell access...

Map Data, Centralize Control—Simple Shift, Big Cybersecurity Impact
Cybersecurity is overdue for a makeover. More of a focus on knowing where data lives, who has access, and how risk moves. One university proved it: map the data, identify real risks, centralize control. Simple shift. Big impact. https://t.co/GLJlBbM1uN

AI's Dual Role Fuels Security Edge at RSAC
“AI on Both Sides: Friend, Foe, and Everything In Between” RSAC 2026 Recap: Chatbots, Deepfakes, and Smart Glasses Highlight a Security World on Edge https://t.co/qHl5CXvVip #RSAC #RSAC26 https://t.co/IgIm5EZ5DI

AI Code Leaks Boost Demand for Software Security Jobs
Woke up to news of supply chain attacks on NPM and Claude Code’s source code leaking…again. It seems the only tech jobs that AI with any job security are going to be software security jobs. It’s only going to get...

From AI Risks to Rapid Control Implementation
I hosted a roundtable at RSAC with NTT Data on AI risk. The conversation has shifted. We are past “what are the risks of AI.” Now it is: how do we operationalize controls fast enough? That is a very different problem.

Quantum Crypto Threats Unlikely Within Our Lifetime
Neat paper on securing cryptocurrencies against quantum attacks. I want to stress that I am not convinced we have anything to worry about in my lifetime. This tweet might haunt me. https://t.co/d1i4reP93g

AI Model Mythos Amplifies Attack Scale and Internal Threats
A leaked model is raising new concerns about AI and cybersecurity. Anthropic’s “Mythos” is described as a step change in capability, especially in how AI agents can act, reason and operate independently. That makes it easier for attackers to scale operations...

PQC Adoption Accelerates as Qubit Requirements Shrink
More warning lights keep blinking for the urgency of PQC adoption in many fields as advances in both hardware and algorithm construction keep reducing the number of qubits and gates needed for a CRQC. https://t.co/55FxttUDdD https://t.co/nmDa4iDWbr https://t.co/MOfzj3Tl4O
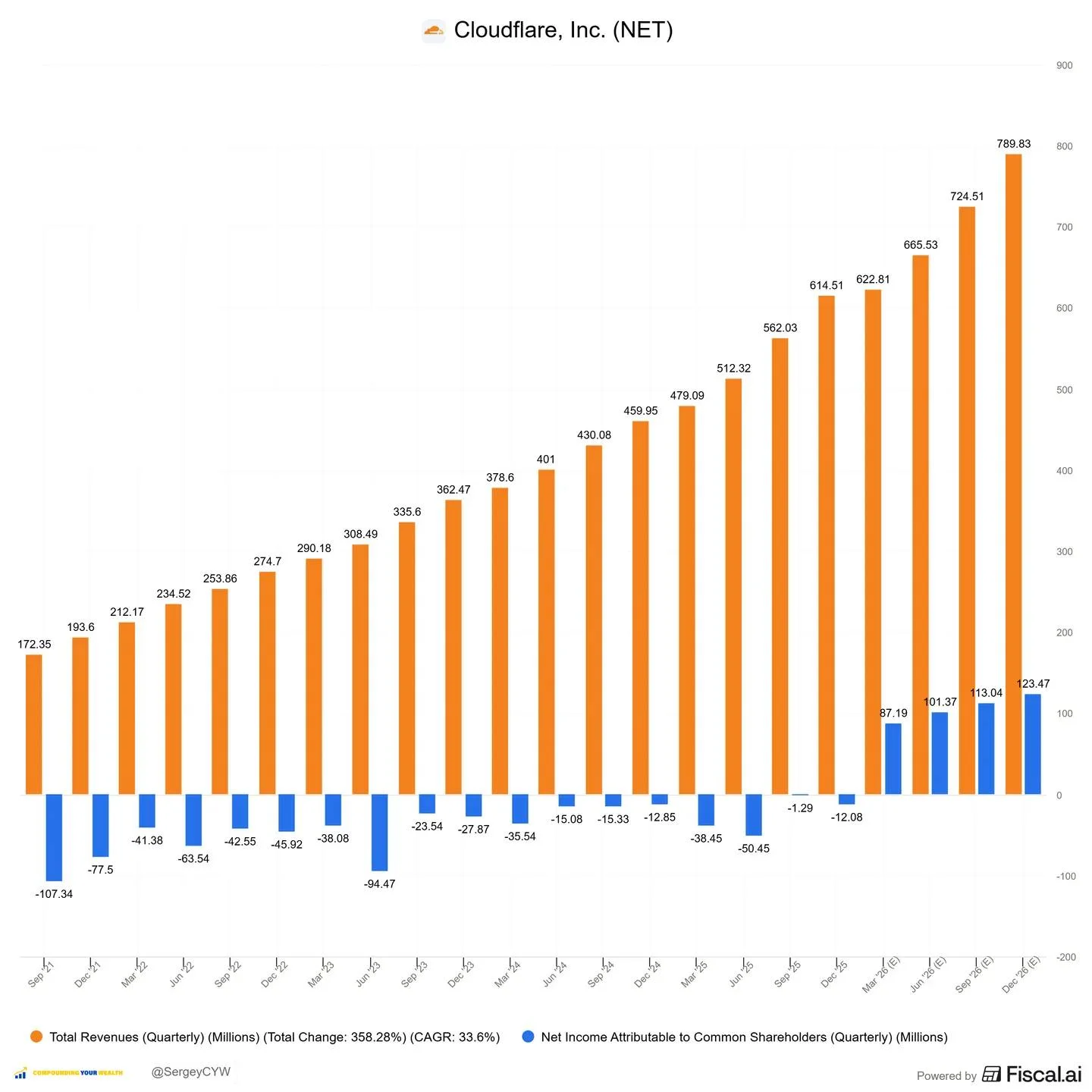
AI Cyberattacks Surge, Cloudflare’s AI Defense Boosts $NET
AI-driven cyberattacks are scaling rapidly — and $NET is a direct beneficiary Cloudflare’s AI-powered defense, driven by Cloudforce One and its global network, now blocks ~230 billion threats daily. Attack sophistication is rising fast. AI is being used for exploit development, network mapping,...

Claude's Source Code Allegedly Exposed Through Npm Map File
WILD if true. @Fried_rice is reporting that Claude's source code leaked via an npm .map file 👀 Code: https://t.co/nQFCcCCc6Z https://t.co/ACLKa6wVFf

Quickly Detect Axios Supply‑Chain Compromise with New Claude Skill
🚨 Want to quickly check if you've been compromised by the Axios supply-chain attack? Hari (@hrkrshnn) just shipped a free @claudeai skill for us 🙏 /plugin marketplace add cantinasec/plugins /plugin install cantinasec@cantinasec-plugins /reload-plugins /cantinasec:axios https://t.co/XlUdHdDcl7

IOS 26.5 Restores Encryption, Paves Way for Maps Ads
iOS 26.5 brings back end-to-end encryption when messaging Android users, but it also brings us one step closer to ads in Apple Maps. https://t.co/uhPJbpMa8C

Supply Chain Attacks Force Permanent Passwordless Rotation
Whoever is doing all the supply chain attacks really wants us to switch to passwordless auth for everything. If the cadence of attacks continues we will end up just having to permanently rotate everything for the rest of the year.

Consumers Shouldn't Bear the Burden of Spotting Scams
Why should consumers be the ones trying to work out whether something is a scam or not? #CyberSecurity #Scam #Fraud #DigitalSignatures https://t.co/UykiRfLj5z

Beyond Pinning: Harden Node and Python Supply Chains
Supply chain attacks are becoming more frequent, and far more serious. What are sensible practices to protect against these when using Node or Python packages? I assume pinning versions is the bare minimum; for those with security teams / tools: why else...

Scaling Speed and Trust in AI-Driven Systems
How do we build systems where speed and trust can scale together? I explored this with @MichaelLeland, field CTO of #island at RSA and it’s the challenge of the AI era. AI is now an actor. Fast, boundaryless, and creating risks most...

Bitcoin Must Start Quantum-Resilience Work Today
Bitcoin needs to get ready for the quantum era. We need to strengthen initiatives like BIP 360. We need to invest more efforts in finding creative, smart solutions to ensure Bitcoin is post-quantum secure. Saying that quantum computers are coming is not FUD....
Npm Supply Chain Attacks Becoming Disturbingly Frequent
is it me or supply chain attacks on npm are getting regular occurrence these days?

AI Automation Fuels Sophisticated, Costly Cyberattacks Across Businesses
AI-driven cyberattacks are becoming more sophisticated and costly, with automation enabling highly targeted phishing, synthetic identities, and a surge in ransomware and coordinated attacks impacting businesses of all sizes. cybersecurity

Treat AI Agents Like Malware: Three Safety Lessons
AI Agents Act a Lot Like Malware. 3 core lessons that can help companies safely adopt agentic AI https://t.co/jmHx1BceXK https://t.co/nhAWPPp2OG

Hardware Advances Slash RSA Break Time to Minutes
Still a lot to build on the hardware side, but the last state of the art papers were stating about 8 hours to crack RSA, now it's 9 minutes. Lots of gates, lots of hardware, but we are seeing quite...

Beware: Surge of Fake Scammer Profiles Targeting DMs
big influx of fake scammer profiles on here, be careful out there folk (be very wary of people DM-ing you out of the blue or inviting your to chatrooms etc)

AI Bot PwnedClaw Analyzes This Week's Data Breaches
Weekly update is up! Join Me in Investigating Today’s Data Breaches With the PwnedClaw, the OpenClaw Agentic AI Bot Doing My Legwork: https://t.co/KeML1pLTOL

AI Will Supercharge Security, But Transition Will Be Rough
I think the situation with AI and security this talk highlights is kind of indicative of how AI disruption will play out. AI is going to make it really, really easy and cheap to find exploits in software. The end...

Most Firms Can't Apply Zero Trust to AI Agents
Zero trust for humans – but implicit trust for machines? - Raconteur “In 65% of organisations, zero trust controls cannot secure non-human identities (NHIs), including new agentic AI systems.” https://t.co/pK57KjAzoS https://t.co/JA0DMauDdc

Shadow AI Emerges as Active Threat Amid Rapid Adoption
Shadow IT was always a problem. Shadow AI is different. Now it can act, not just exist. And the pace of adoption is like nothing I have seen before. What are you doing to manage shadow AI?

National Labs Drive Multi‑Agency Solar Cybersecurity Standards
National laboratories lead multi-agency push for solar cybersecurity standards #energysky -- via pv magazine usa: https://t.co/2zCsruApti

Veteran Researcher Warns: AI-Driven Security Apocalypse Underway
Another veteran computer security research — Thomas Ptacek — says we're currently in middle of the Computer Security AIpocalypse: https://t.co/80HQZjpMDb https://t.co/8llU4N93SX

New Have I Been Pwned Features Boost Privacy, Usability, Performance
Today, after many months of hard work, we're launching a bunch of new @haveibeenpwned features that improve privacy, usability and performance. We're a little team, but we've done a lot since this pic in November. Here are all the details:...

Never Store Passports; Avoid KYC Data Leaks
I'm not sending anyone my passport anymore My Portuguese lawyer wanted me to email her a copy of my passport for KYC I rejected and she was confused "I've never been hacked" 99% of people are not aware any account probably can and will...

New WordPress Flaw Lets Hackers Read Any File
Hackers can read arbitrary files, including those containing passwords, with this newly discovered WordPress flaw. https://t.co/rCE6SHGYXW

Secure Sandbox Empowers Local AI Assistants with Control
OpenClaw has proven that local AI assistants have product-market fit. But the big issue with them has been security. The team at @Pokee_AI is fixing it with PokeeClaw: works like OpenClaw, but with in a secure sandbox architecture with isolated environments, approval workflows,...

Identity Remains Primary Defense in AI-Driven Threats
Identity is the first line of defense, especially in an AI-fueled threat landscape | Cybersecurity Dive https://t.co/8y0zjDUN0H

Drone Attacks Expose Risk of Centralized Cloud Infrastructure
Iranian drones hit AWS data centres twice this month. Banks went down. Apps went offline. Thats centralised cloud, one strike and everything breaks. This war is making the case for decentralised computing like Ocean Network. No single point of failure. No data centre...

AI Defense Must Outpace AI Attack to Preserve Internet
Let's hope AI cyber defense beats AI cyber offense, or the internet age is over

AI‑Powered Recruiter Scam Uses Fake Jobs to Sell Software
PSA: There’s a new scam going around with exec search firms targeting people to say there’s a role they’re well suited for in order to sell resume software. The tell is AI: They essentially leveraged LinkedIn keywords to market these...

Falsely Accused, Bail Granted; Fraud Was Impersonator Scheme
I want to address what happened to Neeraj and me last week. Of course, it was quite shocking to us as well and honestly very disheartening. But today, we want to talk about what actually happened and more importantly, what...
AI Agents Could Automate Large‑scale Cyberattacks, Warns Experts
A new wave of AI models could turn cyberattacks into something far more scalable. According to industry and government sources, upcoming systems may enable autonomous agents to plan and execute sophisticated attacks with minimal human involvement. What once required teams could...

North Korea Pressures Russian Officers over Crypto Ransomware
I assess with medium confidence this is a North Korean state actor looking for Russian officers with large crypto holdings from shaking down ransomware cyber criminals.

SIM Swaps Bypass 2FA, Exposing Unprotected Accounts
This hack often occurs 1) if accountholder fails to protect account with two-factor authentication and their credentials get leaked thru an infostealer or 2) account is protected with 2FA but hackers succeed to get accountholder's phone SIM swapped to their...

Claude + Codex Automate Comprehensive PRD and Security Reviews
Been doing this for months. Any PRD/Spec/Implementation/Bug + Security hunts includes Claude + Codex, much better thorough analysis and things one or the other misses it'll pick up. My Claude Code instance has hooks + gpt skills for doing...