
Shared Observability Unites SOCs and DevOps
RT SOCs and DevOps will need shared observability for agents: data access, tool calls, MCP interactions, and risk levels in one view. #Security #DevOps @Star_CIO https://t.co/tRGwCPc4Mb

AI Could Multiply Software Vulnerabilities Twentyfold, Globally
What we can see is only a fraction of what exists. Jay Chaudhry has been in cybersecurity for over 30 years. In a recent CRN interview, the @zscaler CEO said he's never seen anxiety in the field like this. He's staring...

Beware: Impersonator Sending Scam Emails, Not on Instagram
PSA: There’s an impersonator pretending to be me sending out scam emails about some trading system. Please disregard emails like that. Same for scams on Instagram and such. I’m not on Instagram. (sigh)

Never Trust Unknown Calls: My Hubris Cost Everything
“I still love you even though you are a dummy,” Maryam told me as she gave me a needed hug this morning after I wished her happy Mother’s Day. Yesterday’s social hack wherei basically gave a caller access to everything...

Claude Extension Flaw Lets Other Add‑ons Hijack It
This was one of the first things I thought could happen when reading about Claude's chrome extension -> ClaudeBleed: A Flaw In Claude’s Browser Extension Allows Any Extension to Hijack It I believe this is partially patched now, but underscores...

AI Responsible for 40% of 2025 Breaches, to Dominate 2026
Ah, AI... -> Experian says 40% of the 5,000 data breaches it serviced in 2025 were AI-powered, and predicts agentic AI will be the leading cause of data breaches in 2026 https://t.co/huKoCEldFh

Secure AWS Keys with MFA, IP Restrictions, Least Privilege
Do you add MFA and/or IP address restrictions to AWS Developer access key IAM user policies and trust policies ~ or both? Also create policies that only give necessary permissions. Even with short lived tokens there is a period of time...
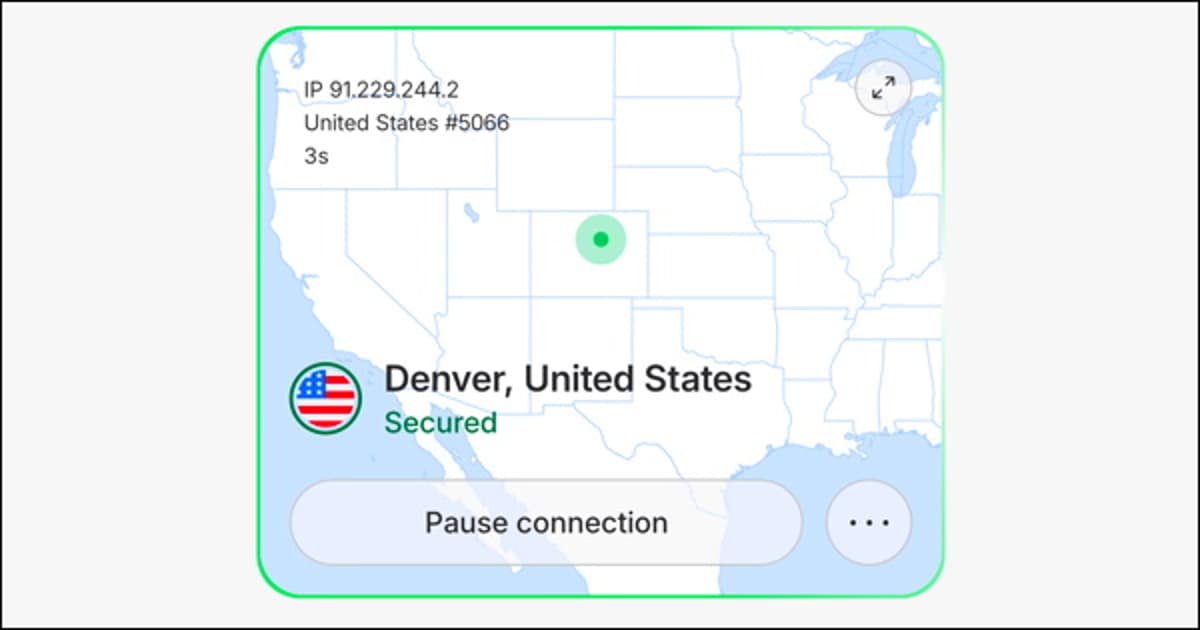
Cellular Is Secure, Wi‑Fi Isn’t—Add NordVPN
Your Android phone uses a secure connection when you're on cellular, but on Wi-Fi? Nope. That's why a VPN is such a win. Here's how to add @NordVPN to your own Android device with just a few clicks... https://t.co/kN7arxgmEY #android...

Ad Trackers Shared State Health Insurance Data with Social Media
Social Media Sites Got Information from Ad Trackers on US State Health Insurance Sites https://t.co/H2b2XTF5jg

Never Trust Cloud Defaults—Review Settings First
Working in cloud taught me that defaults are dangerous. ☁️ Default security groups are too open ☁️ Default instance sizes cost more than you need ☁️ Default retention policies keep too much or too little Always know what you're accepting when you accept a...

Ghost Participants Won’t Crack Encrypted Group Chats
“Ghost participants” have been floating around for years as a way to break encrypted messaging. The idea is to add invisible extra people (the police, essentially) to group chats. It’s a dumb idea, and let me explain why.

Asia’s Top Travel Apps Are Massive Data Hoarders
Surfshark’s latest research reveals that the most popular travel apps in Asia are real data hoarders https://t.co/GE2selYbtX

April 2026 Sees $635M Lost in Crypto Breaches
JUST IN: Crypto security breaches totaled over $635 million across 28 incidents in April 2026, the worst month for crypto exploits this year.
Upgrade Telegram's Weak Defaults: Essential Privacy Settings
Whether you're an old hand or just jumping into Telegram, it's important to set up your privacy and security settings, because the defaults just ain't that good. Here's what to update: https://t.co/hFFAXUo8ox #telegram #privacy #security @telegram https://t.co/5M0G6Y3SDx
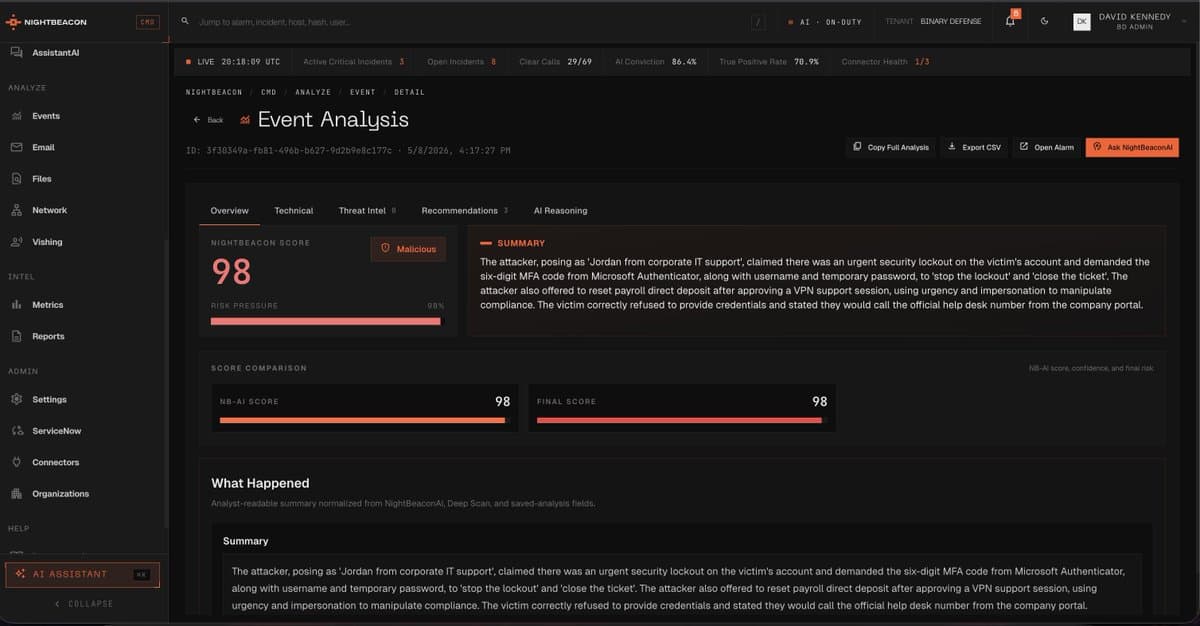
AI Detects Vishing Calls in Seconds, Real‑Time
Just finished tidying up Vishing analysis within NightBeacon AI for @Binary_Defense. Can upload voice recording, or tie into audio systems to do real-time vishing analysis, understands tonality - urgency - phishing campaigns realtime. 11 minute call took 4.3 seconds to analyze...

Incident Escalates: Massive Breach Looms Before Data Leak
This is just going from bad to worse. The scale of this incident is massive, and that’s *before* any data has leaked.

AI Threats Rise; Defenders Must Adopt Guardrails
AI is changing cybersecurity on both sides. Attackers are using it—and defenders must too. CTG shares how to build the right guardrails. 🔗 https://t.co/mbvrjTVwVw @CTGinc #HIMSS26 #HITSM

Effective Bug Bounties and Triage Prevent IDOR Breaches
I’m reading about the Canvas breach which runs infrastructure on AWS: Canvas login portals hacked in mass ShinyHunters extortion campaigns. The details are light but from what I can gather they may have used IDOR/BOLA to bypass trust boundary between free...

Environment Variables Aren't Secure; Switch to a Secrets Manager
Environment variables are not a secret management strategy. • They leak into logs • They end up in version control • They get copy-pasted into Slack Use a secrets manager. ✨ Please ✨
Seeking Metrics to Predict Impending Vulnerability Apocalypse
OK, humans, I plan to vibe code an app to predict the coming of vuln apocalypse, like when do we know it is here. Growth in KEVs? Lowering of VRP numbers? More vulns in general? What else to track? ...

Manual Updates Reveal Outdated Security Practices
"If your security strategy relies on a sysadmin logging into a server to run apt-get upgrade on a Tuesday morning, you aren't running a modern security program; you’re running a historical reenactment society." #overheard
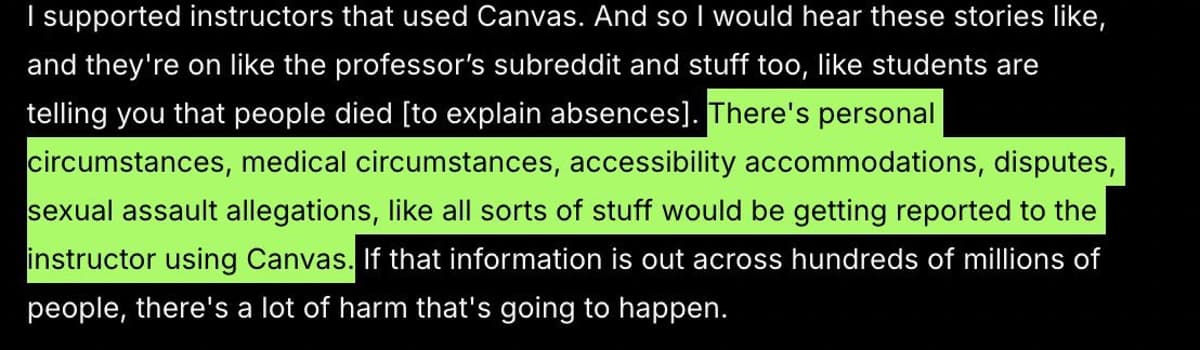
Canvas Breach Exposes Private Faculty‑student Disclosures
When they say “personal messages between faculty and students may be leaked” due to this breach, that sadly includes sensitive messages including medical situations, accessibility needs, and sexual assault allegations reported to the educator on Canvas 😞 https://t.co/mMGMtJC8mU

Researcher’s Linux Vulnerability Disclosed Before Patch Available
A researcher shared their findings with Linux distro maintainers, but leaked before a patch was built. https://t.co/UMfIxI2WpM

Secure Your Flanks: CISO Strategies During Upgrades
#TimTalk - How can CISOs protect their “flanks” when they are most vulnerable during a security upgrade for example? with Zach Lewis https://t.co/pKVV0x2VFb via @DLAIgnite #SocialSelling #DigitalSelling #CyberSecurity #CyberSec #Ransomware #LockBit #LockBitRansomware #CyberAttack #DataBreach #Malware

NightBeacon Delivers Faster Detection for Today and Tomorrow
This is real world stuff we are doing at #BinaryDefense. I've worked on NightBeacon for 12 months of my life, barely sleeping - to bring something to the industry that changes faster response times, faster detections - it's needed now, but...
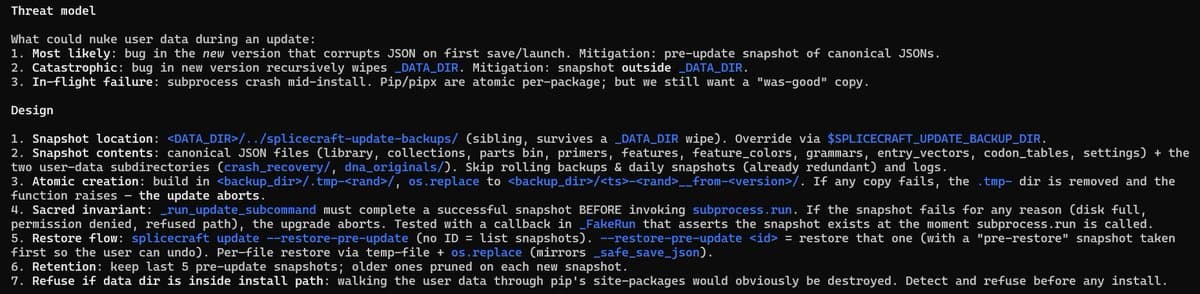
Ensuring Backups Prevent Patch‑induced Data Loss
Shoring up user data protections to prevent any future updates from nuking plasmid collections or other user input data. Backups and copies of everything. Hardened, sanitized, and secure. My nightmare scenario is for a user to tell me latest patch...

Exec Ordered to Pay $10M for Selling Exploits to Russia
Trenchant exec, Peter Williams, who stole zero day exploits from his employer and sold them to a Russian buyer (known to sell exploits to the Russian government) has been ordered to pay $10 million in restitution to his former employer...

CIOs Must Prioritize Plugin Security Over AI Hype
A personal agent is only as safe as its plugins. In the wild, we're already seeing extensions act as conduits for malware. CIOs: It’s time to move from "opportunity" to "risk mitigation." 📉 https://t.co/5poCN8at4u #CIO #AI #Cybersecurity #RiskManagement #InfoSec
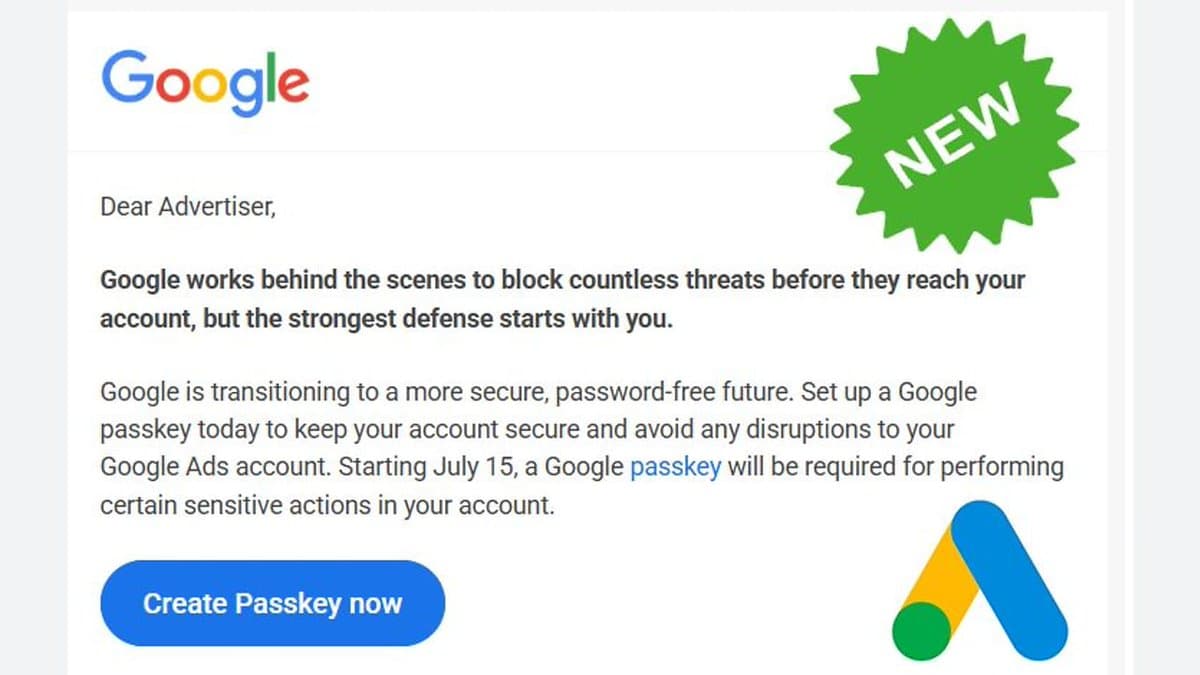
Google Ads Mandates Passkeys for Sensitive Actions July 15
Google Ads to require passkeys for certain sensitive actions starting on July 15 https://t.co/ERPAYU10eg https://t.co/q4LeLR7byl

Meta's Moltbook Acquisition Sparks New Privacy Concerns
Meta's acquisition of AI-agent social network Moltbook raises fresh data privacy concerns for billions of users. https://t.co/P6d9uHIyjh

Scaling, Privacy, and Post‑Quantum Ready: Our Future Tech
Scale matters Privacy matters Post-quantum security matters We nailed scale We're launching privacy We'll easily transition to post-quantum security Future tech. https://t.co/wPPltaMlWA

VoidStealer Trojan Steals Chrome Master Key via Debugger
The new VoidStealer Trojan has learned to bypass Chrome's stored data protection: the infostealer attaches to the browser process as a debugger, and intercepts the master key from RAM. Cookies, sessions, and passwords in Chrome and other browsers – Microsoft...
AI-Driven Threats Make Cyber Resilience Essential for Survival
Cybersecurity is entering a different era. Frontier AI models can now discover and exploit vulnerabilities continuously and at scale, shrinking attack timelines and expanding risks far beyond traditional defenses. The priority is changing fast. Cyber resilience is no longer optional infrastructure, it...
Real‑Time Threat Detection Keeps Businesses Ahead
OpenClaw Security offers innovative protection solutions that focus on real-time threat detection and response, ensuring businesses can stay ahead of cyber threats. Learn more here: https://t.co/xD7sxwrMiz @handvantage
Beware: Near‑phishing Scam Almost Fooled Me
be aware of this kind of phishing. i was almost tricked. cc @nikitabier @business https://t.co/lqgbXgcQzU

Frax Leads with Early, Robust Cross‑Chain Security Measures
At Frax, we did all of these mitigations immediately & more at the very beginning before rolling out our frxUSD LZ mint-burn mesh. I'm surprised how many other projects didn't. We use our own libraries (no external entity can upgrade...

AI Enables Warrantless Mass Surveillance of Americans
AI is supercharging the ability to warrantlessly spy on Americans on a massive scale. https://t.co/DRUOdtx6Ji
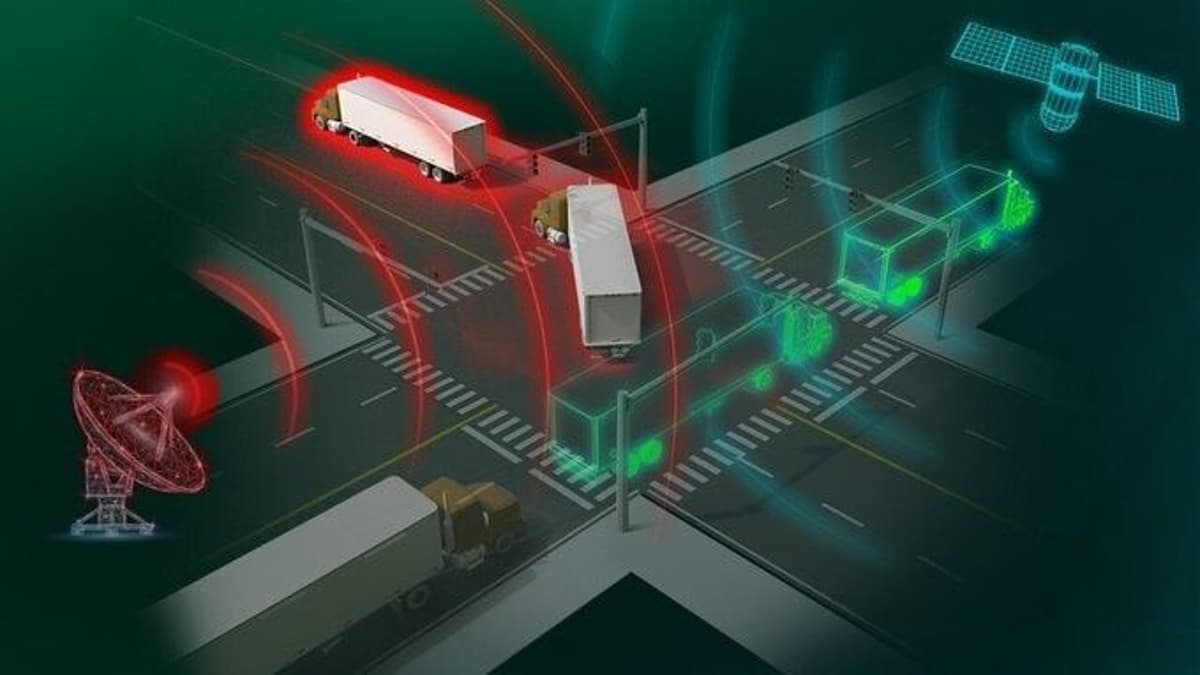
Portable Device Detects Real-Time GPS Spoofing On‑the‑Move
Portable detector spots GPS spoofing in real time, even on move by Oak Ridge National Laboratory @TechXplore_com Learn more: https://t.co/JUKIEROcOm #Innovation #Technology #EmergingTech https://t.co/4JevkxiUhG

Act Now: Secure Your Company Without Delay
we'd like to help companies secure themselves and we think it's important to start work on this quickly

Sophisticated Hack Attempt Targets Nate’s Account
If anyone knows Nate, let him know his account was hacked. Almost got me with a sophisticated account-takeover attempt. https://t.co/hmkPkV4Jbi
Canvas Breach Threatens 230M; Steps to Protect Finals
Canvas is hacked and stressing out 230+ Million students, teachers and staff during finals. What does this mean and how do we stay safe? What are the next steps for the 8,800 affected schools during finals. Answered below in my...
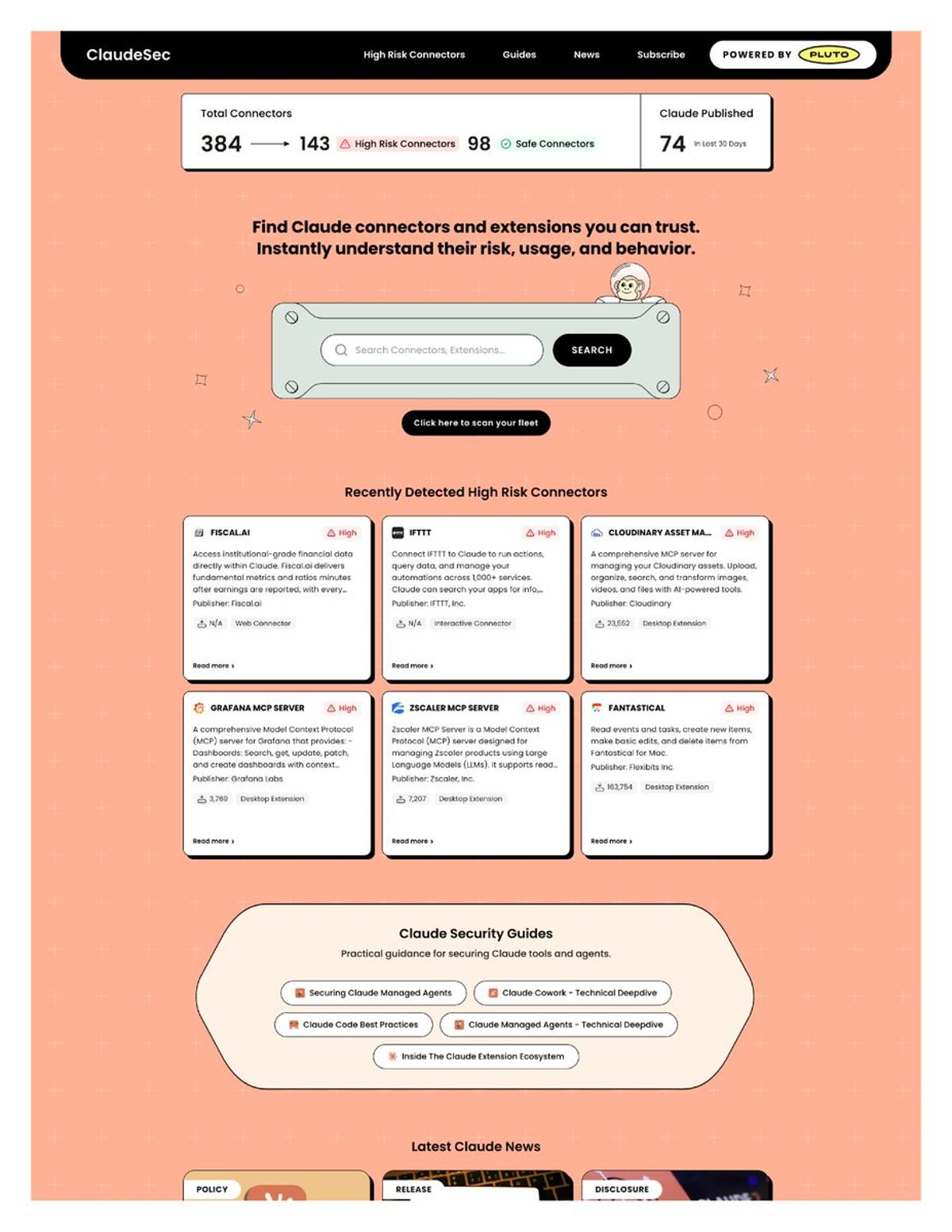
New Claude Connectors Flagged for Data Leak Risks
Anthropic just shipped 128 new Claude connectors in 30 days. Nobody is reviewing them. Pluto Security just launched ClaudeSec, a free database that flags which ones can leak your data, exfiltrate files, or hijack agent sessions. Here's what they found ↓ https://t.co/h1mWAoSFHT

Security Key to Agentic Economy; IronClaw Leads
Excited to work with FailSafe to bring AttackBench: a benchmark for red teaming agents. I believe that true agentic adoption and agentic economy is limited by security and that’s why IronClaw is focused on becoming the most secure (and private) agentic...
Adjust WhatsApp Settings for Better Privacy Abroad
WhatsApp is a great way to stay in touch with friends and family traveling abroad, but you do want to make a few changes in @WhatssApp for maximum privacy and security. Here's the rundown: https://t.co/pBNbgmlbVR #whatsapp #privacy #security https://t.co/JyZg1OaWpa

AI Success Depends on Robust QA and DevOps Maturity
RT 77% of orgs are confident in AI outputs? while many still lack secure CI/CD, automated audit trails, and even basic defect escape metrics. Your QA and DevOps maturity will make or break AI agents in production. #AI #DevOps #QA @Star_CIO ...
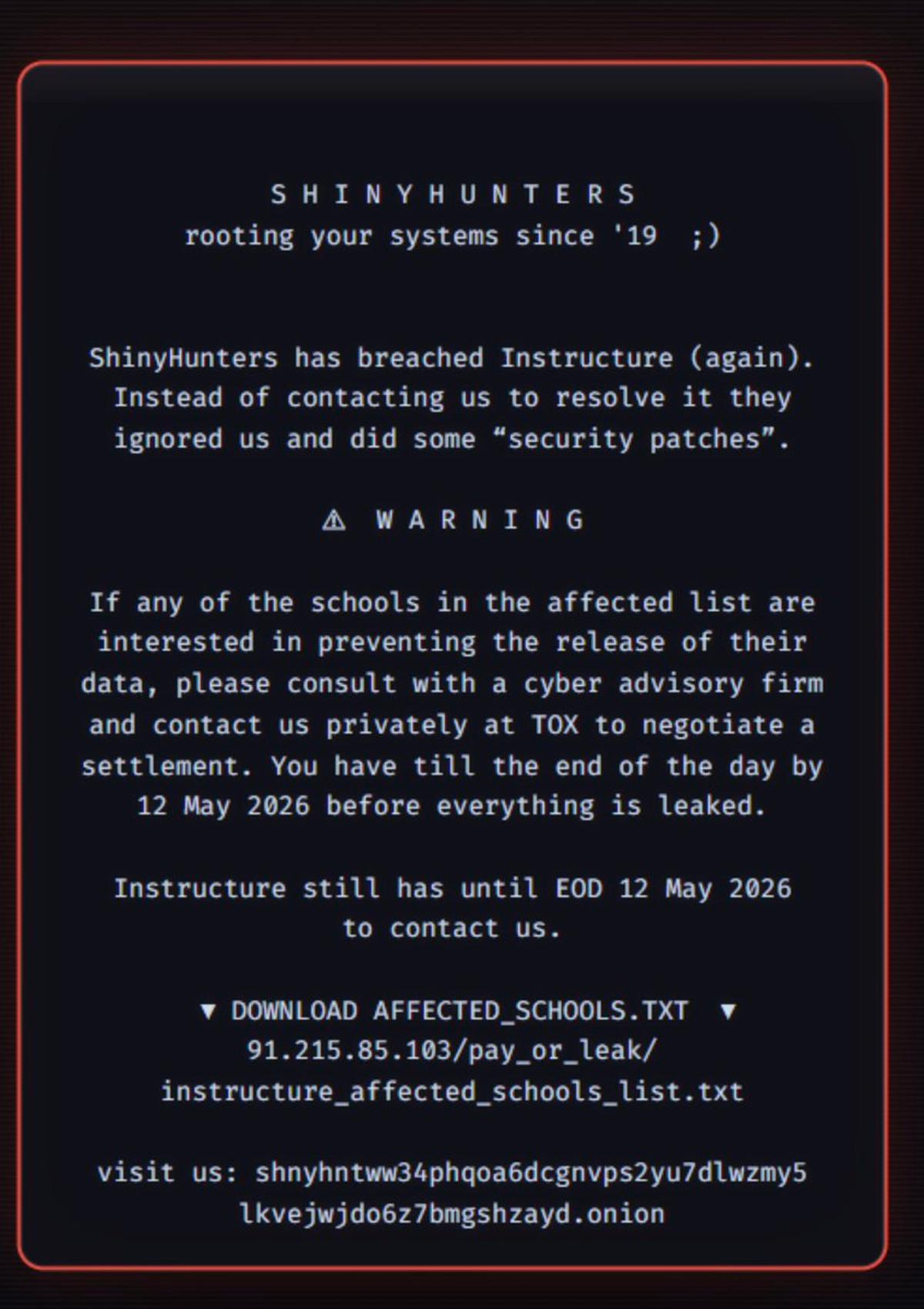
Canvas Ransomware Disrupts Finals, Threatens Student Data
Canvas, the tool teachers and students are using for finals right now, was hit w/ ransomware by (folks who claim to be) ShinyHunters. Lots of students/educators saying this is making finals studying/tests v hard (not even considering the amount of...

J.P. Morgan Secures AI Agent Identity for Future Payments
J.P. Morgan Payments has partnered with Mirakl to build infrastructure for agentic commerce in an effort to radically transform the traditional payment rail. But as autonomous agents move from browsing to buying, they introduce some risks: processing untrusted inputs, accessing sensitive...

Secure Oracles and Bridges: Chainlink Sets New Industry Standard
Glad to see all the hard work that Chainlink has put into generating real security is being recognized as valuable by more and more teams in our industry. It seems that focusing on making the secure and reliable solution is...

AI Could Secure Software by Eliminating All Vulnerabilities
Maybe powerful AI will favor the cyber defense. Vulnerabilities are finite in number, so if you can fix them all, maybe software just becomes much more secure.
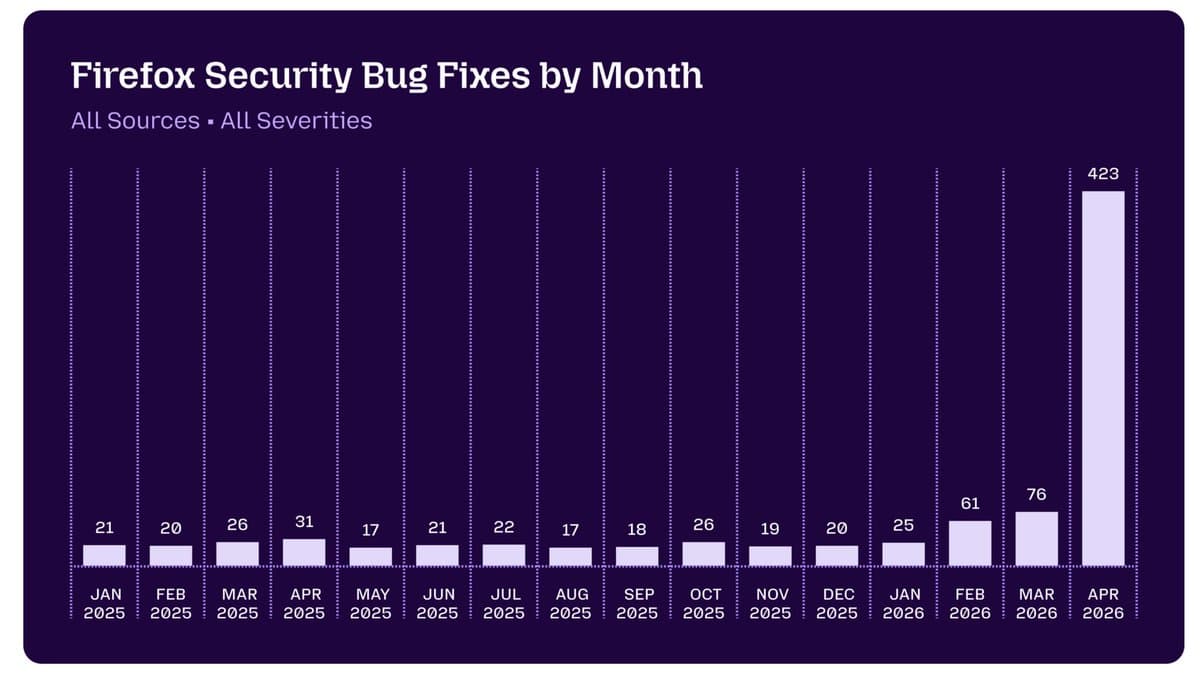
Mythos Boosts Firefox Bug Fixes: April Beats 15 Months
Skepticism of corporate marketing and AI boosterism is always warranted, but I think the folks who accused Anthropic of overrating Mythos should check out this post by Mozilla developers indicating that the Firefox team fixed more security bugs in April...