Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Re: Protecting Health Data at UK Biobank
A recent scandal revealed that health data from the UK Biobank was listed for sale on a Chinese website, prompting public outcry. The UK government responded by emphasizing the Biobank’s status as an independent, non‑profit charity that relies on volunteer donors. Critics argue that repeated state‑linked data exposures betray donor altruism and raise questions about oversight. The incident underscores growing concerns over international data governance and the protection of sensitive health information.
‘Harvest Now, Decrypt Later’ Attacks Push Federal Shift to PQC
Federal agencies are accelerating a shift to post‑quantum cryptography (PQC) after a surge in “harvest now, decrypt later” attacks that could expose today’s encrypted data once quantum computers mature. A June 2025 White House executive order mandates agencies to establish PQC...

Australian Regulators Come Together on Privacy, Online Safety
Australia’s eSafety Commissioner and the Office of the Australian Information Commissioner have signed a memorandum of understanding to coordinate privacy and online‑safety enforcement. The MoU formalises information‑sharing on the Privacy Act, Online Safety Act and emerging AI risks, and designates...

Kubernetes v1.36: User Namespaces in Kubernetes Are Finally GA
Kubernetes 1.36 makes User Namespaces generally available, a Linux‑only feature that lets pods run with root privileges confined to a user namespace. Setting hostUsers:false isolates capabilities such as CAP_NET_ADMIN to the container, preventing host‑wide escalation. The GA release relies on...
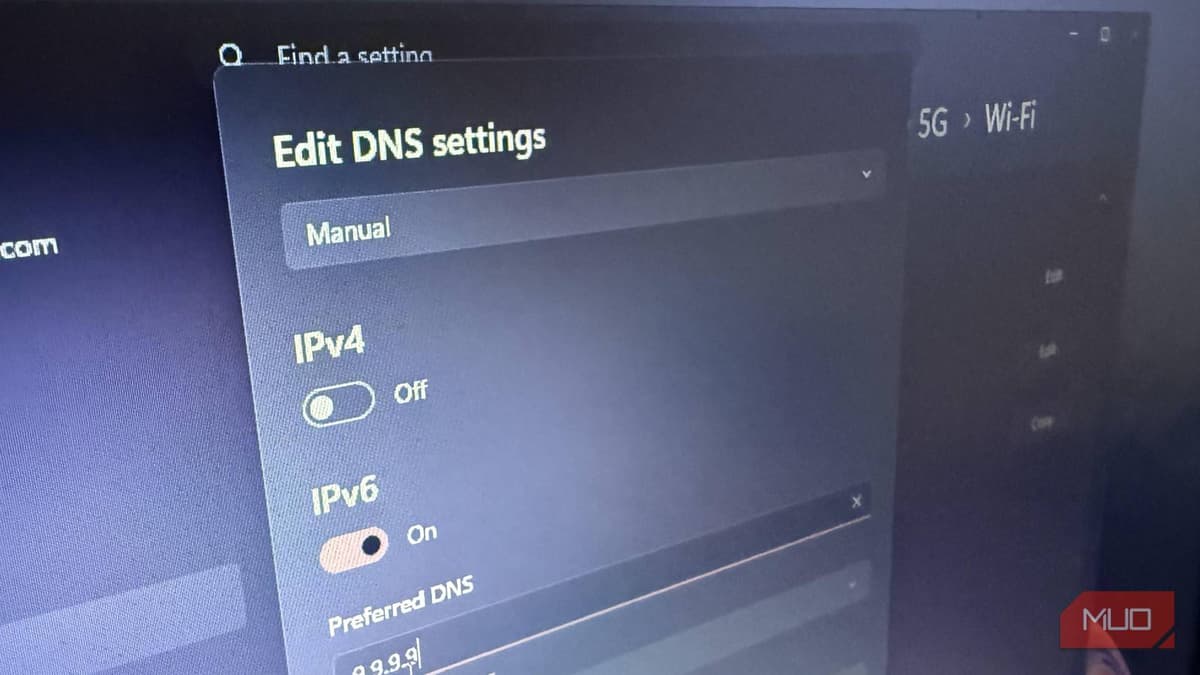
This Simple DNS Switch Is Always My First Privacy Recommendation
The article highlights DNS as a hidden yet critical layer that can expose browsing habits, even on encrypted sites. It recommends switching to Quad9, a nonprofit DNS resolver that blocks malware and phishing by default while refusing to log IP...

Anthropic Mythos - We’ve Opened Pandora's Box
Anthropic’s Mythos AI system has automatically discovered thousands of zero‑day vulnerabilities, many of which were previously known only to nation‑state actors. By turning sophisticated exploits into low‑skill, script‑kiddie‑ready tools, Mythos shifts the cyber‑security balance toward attackers. The article warns that...
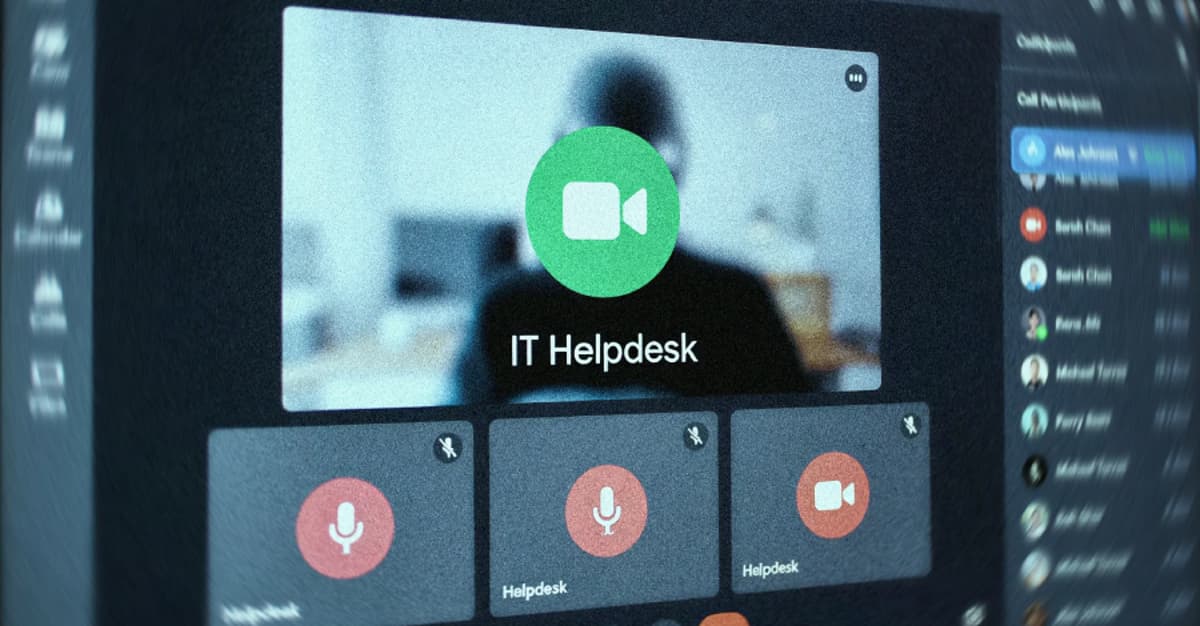
UNC6692 Impersonates IT Helpdesk via Microsoft Teams to Deploy SNOW Malware
UNC6692 is a newly identified threat group that hijacks Microsoft Teams to impersonate IT help‑desk staff and convince victims to install remote‑support tools. The actors deliver a custom SNOW malware suite—including the SNOWBELT browser extension, SNOWGLAZE tunnel, and SNOWBASIN backdoor—after...

Mythos Is a Wake-Up Call for DDoS Defense
Anthropic’s new AI model Mythos can autonomously identify software flaws and craft exploits, prompting an emergency meeting of top bank executives with Treasury Secretary Scott Bessent and Fed Chair Jerome Powell. The regulator‑level concern centers on AI‑driven attackers accelerating vulnerability...

The $2.8 Billion Email: What CEOs Get Wrong About BEC Fraud
Business Email Compromise (BEC) continues to drain U.S. companies of roughly $2.8 billion a year, according to the latest FBI Internet Crime Report. CEOs frequently attribute the threat to weak IT controls, overlooking the human element that attackers exploit. The article...
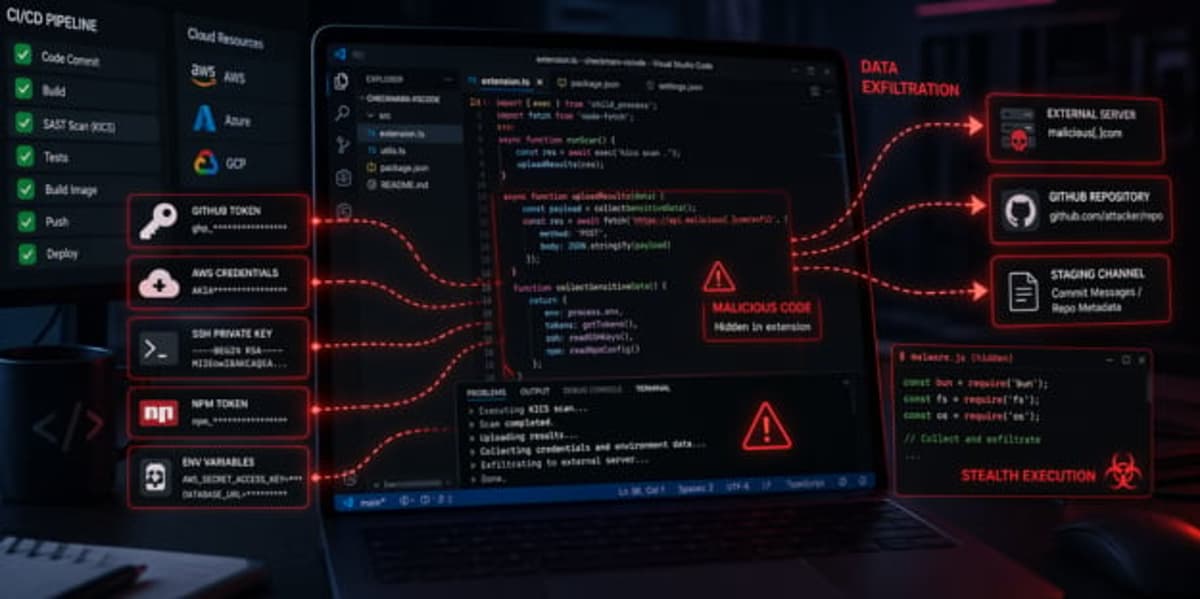
Checkmarx Supply Chain Attack Exploits Docker Images and CI/CD Pipelines
Checkmarx’s KICS tool was compromised through poisoned Docker Hub images and malicious VS Code extensions, allowing attackers to harvest credentials from CI/CD pipelines. The threat actor, identified as TeamPCP, modified tags such as v2.1.20 and introduced a rogue v2.1.21 image, while...

Unauthorized Users in Discord Group Had Weekslong Access to Anthropic’s Supposedly-Super-Dangerous Claude Mythos Model
Anthropic announced its Mythos model on April 7, touting it as a super‑dangerous AI capable of facilitating sophisticated cyber‑attacks. The same day, a Discord community of AI enthusiasts gained unauthorized access and has been using the model for weeks. The breach...

The Guardian View on Anthropic’s Claude Mythos: When AI Finds Every Flaw, Who Controls the Internet? | Editorial
Anthropic unveiled Claude Mythos, an AI system that can autonomously discover and exploit zero‑day vulnerabilities, prompting the company to withhold a public release because it could turn computers into crime scenes. The model writes exploit code, gains privileges, and could...

The Butlerian Jihad: Compromised Bitwarden CLI Deploys Npm Worm, Poisons AI Assistants, and Dumps GitHub Secrets
On April 23 2026 Mend.io uncovered a malicious npm package masquerading as Bitwarden’s CLI, version 2026.4.0. The package’s preinstall hook downloads the Bun runtime and runs a sophisticated TeamPCP payload that steals cloud credentials, SSH keys, AI tool tokens, and GitHub tokens. It...

Some Interrail Travellers Told to Cancel Passports as Hacked Data Posted Online
A hack of Eurail, the operator of Interrail passes, exposed personal data of more than 300,000 European travelers, including passport numbers, in December. The stolen information was posted on the dark web via Telegram, prompting the UK Passport Office and...

Marine Log, SNAME to Host Virtual Event on USCG Cybersecurity Rules and Vessel Design
Marine Log and the Society of Naval Architects and Marine Engineers (SNAME) will host a virtual webinar on June 4 at 11 a.m. ET titled “From Regulation to Drawing Board.” The session examines how the U.S. Coast Guard’s new cybersecurity regulations are...
Why Nonprofits Are Missing From the Responsible Disclosure Ecosystem
Nonprofits lack structured responsible disclosure programs, leaving vulnerabilities unaddressed. Researchers often have no clear channel to report findings, while the sector faces a surge in cyberattacks—Okta ranks it second most targeted globally with an 18% malicious login attempt rate. Existing...

Prioritizing Cyber Risks Beats Mere Awareness
One of the hardest parts of cybersecurity right now is not awareness. It is prioritization. Everyone knows there is risk. Few teams are aligned on what matters most. How do you know if you're tackling the most important risks for your organization?

When Elite Cyber Teams Can’t Crack Web Security
Hack The Box’s 2025 Global Cyber Skills Benchmark tested 796 corporate security teams on real‑world web, cloud and secure‑coding scenarios. Only 21.1% passed the web security challenges, revealing a stark gap between certifications and actual defensive ability. The study involved...

South Korea’s Regulator Fines Matchmaking Service Duo $830,000 over Data Breach
South Korea’s Personal Information Protection Commission fined matchmaking leader Duo Info $830,000 after a December 2025 hack exposed the personal data of about 430,000 members. The breach revealed 24 data points, ranging from basic identifiers to religion, hobbies, marital history,...

Healthcare AI Firm Sued Over Alleged Unlawful Disclosures of Genetic Data
Tempus AI, a publicly traded healthcare‑AI company, faces multiple class‑action lawsuits alleging it collected and disclosed genetic test results from Ambry Genetics without proper consent. Plaintiffs claim Tempus used Ambry’s genetic database to train its machine‑learning models, violating privacy protections....

Arkham Reveals Blockchain Intel as Kelp DAO Loot Freezes
The Kelp DAO loot is moving onchain and Arkham has had a front-row seat to the action. 🚨 Up Next on the stream today, Arkham CEO Miguel Morel joins me to discuss what his team has seen and how blockchain intelligence...

FIRESTARTER Maintains Post‑patch Persistence on Cisco ASA/FTD
"FIRESTARTER can persist as an active threat on Cisco devices running ASA or Firepower Threat Defense software, maintaining post-patching persistence and enabling threat actors to re-access compromised devices without re-exploiting vulnerabilities" https://t.co/wVwgbLKaNj

Quantum Networking Breakthrough Points to Key Security Gains
Researchers from New York University, in partnership with Qunnect and Cisco, have successfully demonstrated entanglement swapping across three city‑scale nodes using existing fiber in New York City. The experiment linked sites in Brooklyn and Manhattan, showing that quantum signals can...

Choose Your Protocol Wisely After Kelp DAO Exploit
"You have to make decisions on which protocol to trust" - @MiguelMorel on the Kelp DAO exploit https://t.co/C0Okymb2f3

Aave's Umbrella Module Under‑Capitalized, Fails to Cover $250M Exploit
"The Aave Umbrella module, meant to cover bad debt, which had $250 million going into the exploit, seemed like a nice cushion, because Aave has had less than $5 million worth of bad debt throughout its history. "But now we see...

OpenAI's New Trusted Access Program Gives Microsoft Its Most Capable Models for Cyber Defense
OpenAI announced a Trusted Access for Cyber program that grants Microsoft exclusive use of its most capable AI models for security tasks. In exchange, Microsoft will dedicate its entire cybersecurity team to protect OpenAI’s models, infrastructure, and shared customers. The...

Sri Lanka Investigates After Hackers Steal $2.5m
Sri Lanka’s finance ministry confirmed that hackers diverted $2.5 million—approximately £1.8 million—intended for a bilateral debt repayment to Australia. The breach, believed to have occurred in January, involved tampering with email‑based payment instructions, prompting the diversion of funds to unauthorized accounts. Four...

SIM‑Farm‑as‑a‑Service Fuels Global Scam Text Surge, Probe Finds
A new Infrawatch investigation maps 94 SIM‑farm locations across 17 countries that rent out bulk SIM cards to cybercriminals. The network, linked to Belarusian operators and promoted on Telegram, supplies scammers with the ability to launch mass phishing and fraud...

Security Leaders Discuss the Claude Mythos Breach
Security leaders reacted to reports that Anthropic’s Claude Mythos AI model was accessed without authorization. The breach stemmed from a simple credential guess and a third‑party vendor path, exposing weaknesses in supply‑chain and perimeter controls. Experts warn that AI models are...
New Phishing Scam: Fake Invitations
Hackers are sending fake event invitations that appear to come from Paperless Post, Evite and Punchbowl. The emails mimic a personal contact and contain dead‑link buttons that, when clicked, install malware or harvest personal data. The scheme exploits the human desire...

AI Is Making Cyberattacks on Local Governments Easier than Ever
Artificial intelligence is accelerating cyberattacks on local governments, with a 42% rise in incidents reported in 2025, according to Motorola Solutions. Experts say AI tools now generate attack code and bypass traditional safeguards like MFA and captchas, making breaches easier...

Trivy, KICS, and the Shape of Supply Chain Attacks so Far in 2026
Docker reported a supply‑chain compromise of Checkmarx’s KICS scanner on April 22, 2026. Threat actors used stolen publisher credentials to overwrite five tags and add two new malicious tags in the checkmarx/kics Docker Hub repository. The malicious images exfiltrated scan...

Collaboration Security and Governance Must Be Proactive
Collaboration platforms have become prime attack vectors as enterprises adopt a growing suite of messaging, video, and AI‑enhanced tools. Generative AI now creates meeting transcripts, summaries, and even presentations, expanding the data surface that must be protected. A proactive governance...

UK Launches Inquiry Into Security Risks of Chinese-Made 3D Printing Equipment
Britain’s Defence Secretary has launched an investigation into the British Army’s use of Chinese‑manufactured Bambu Lab 3D printers, which were deployed during a training exercise in Kenya. The inquiry focuses on potential security risks stemming from the printers’ default cloud...

AI-Written Software Creates Hassles for Wary Security Teams
A ProjectDiscovery report finds AI‑generated code is overwhelming security teams. Only 38% of practitioners feel they can keep up, while 60% say the workload is getting harder. Main concerns are corporate secret leakage, supply‑chain risk, and business‑logic vulnerabilities. Security teams...

Handling Subject Access Requests with Confidence Under New Data Act
The Data (Use and Access) Act 2025 gives UK HR teams new, legally backed tools to handle the expected flood of subject access requests (DSARs) that will follow the Employment Rights Act 2025’s reduction of the unfair‑dismissal qualifying period to...
Operationally Ineffective: Putting CVEs in a Chokehold with Privilege Disruption
The Mythos Preview leverages AI to accelerate vulnerability discovery, turning roughly 33,000 privilege‑path dependent CVEs from dormant assets into cheap, weaponizable exploits—estimated at about $2,000 per attack. These CVEs, which account for 70% of confirmed weaponized flaws, undermine traditional patch‑and‑remediate...

Navigating Federal Cloud Adoption
Federal health leaders are accelerating hybrid cloud adoption to boost scalability, security, and mission delivery. Former HHS CISO La Monte Yarborough and CMS infrastructure director Wade Zarriello highlighted how cloud strategies have evolved and outlined the next steps for agencies....
Your Passwords Are Officially Obsolete, According to Britain's Top Intelligence Agency
Britain’s National Cyber Security Centre announced at CYBERUK that passwords are now obsolete and recommends passkeys as the primary authentication method. The agency cites passkeys’ speed—up to eight times faster than traditional login—and their resistance to phishing. Around 50% of...

Rubrik Introduces Cyber Resilience Protection for Google Cloud SQL
Rubrik announced a new integration that brings its Security Cloud cyber‑resilience capabilities to Google Cloud SQL, protecting managed PostgreSQL databases with immutable, automated backups. The solution adds air‑gapped backup copies, cross‑region recovery and unlimited retention without changing existing database architectures....

Vercel Says some of Its Customers’ Data Was Stolen Prior to Its Recent Hack
Vercel disclosed that hackers accessed a small number of customer accounts before its widely reported April breach, indicating a longer‑running intrusion. The company traced the initial entry to a Context AI app that infected an employee’s workstation with infostealer malware,...

JPMorgan Says Persistent Security Flaws Curb DeFi’s Institutional Appeal
JPMorgan’s latest report warns that persistent security flaws are curbing DeFi’s appeal to institutional investors, highlighted by a roughly $20 billion loss from the KelpDAO exploit. Bridge and cross‑chain vulnerabilities remain the dominant source of hacks, with this year’s losses matching...

Bad Memories Still Haunt AI Agents
Researchers have identified AI memory files as a critical security weakness after Cisco demonstrated a persistent compromise of Anthropic’s Claude Code. By injecting malicious secrets into the model’s memory.md, attackers can influence code generation, select insecure packages, and propagate changes...

Bitwarden CLI Compromised in Ongoing Checkmarx Supply Chain Campaign
Socket Research uncovered a coordinated supply‑chain campaign affecting multiple development ecosystems. Malicious artifacts were found in the official Checkmarx KICS Docker repository, while Namastex.ai npm packages were infected with a CanisterWorm‑style payload. In parallel, 108 Chrome extensions were linked to...

Cosmetics Giant Rituals Discloses Data Breach Affecting Customers
Rituals, the Dutch cosmetics giant, disclosed a data breach that accessed personal information—including names, email addresses, phone numbers, dates of birth, gender and home addresses—of members of its My Rituals loyalty program. The breach, discovered in early April, did not...

Regular Password Resets Aren’t as Safe as You Think
Password resets cost roughly $70 each and remain a top help‑desk request, prompting many firms to adopt self‑service tools. The April 2025 breach of UK retailer Marks & Spencer, which lost about $5.1 million per day, showed how attackers can hijack a simple...

Hackers Seize AI Security Tools, Now Targeting Firewalls
Adversaries hijacked AI security tools at 90+ organizations. The next wave has write access to the firewall https://t.co/khjZkpWhc0

What Anthropic’s Mythos Means for the Future of Cybersecurity
Anthropic unveiled Claude Mythos Preview, an AI model that can autonomously locate and weaponize software vulnerabilities in operating systems and internet infrastructure. The company is restricting access to a handful of vetted partners, citing AI safety concerns. The announcement sparked...
Iran-Nexus Threat Groups Refine Attacks Against Critical Infrastructure
Iran‑aligned cyber groups have intensified destructive campaigns against critical infrastructure since the February war, deploying data‑wiping malware and novel threats like ZionSiphon that can tamper with water‑treatment controls. High‑profile incidents include a wiper attack on medical‑device maker Stryker and targeted...

UK Biobank Health Data Keeps Ending up on GitHub
UK Biobank has been using copyright takedown notices to remove health‑related data from GitHub, filing 110 requests since July 2025. The notices mainly target specific files such as Jupyter/R notebooks, genomic datasets, and CSV tables, rather than whole repositories. Developers...