Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Cursor and Chainguard Partner to Lock Down the AI Agent Supply Chain
Cursor and Chainguard announced a partnership that embeds Chainguard’s catalog of hardened container images and vetted language libraries directly into Cursor’s AI‑driven coding agents. The integration lets agents pull dependencies from Chainguard’s signed artifact store instead of public registries, reducing exposure to compromised packages. Joint customers gain access to over 2,300 container images and millions of Python, JavaScript, and Java libraries that are continuously rebuilt to a zero‑CVE state. The solution automates credential handling and provenance verification, making secure supply‑chain decisions at machine speed.

The ESA’s Joint Committee Highlights Digitalisation, Cyber Resilience and Sustainable Finance as Key Priorities of 2025
The European Supervisory Authorities’ Joint Committee released its 2025 Annual Report, highlighting digitalisation, cyber‑resilience and sustainable finance as top priorities. The report details the rollout of the Digital Operational Resilience Act (DORA) to harden cyber defenses, tighter rules for sustainable‑finance...

OCR Announces Settlements of Four Ransomware Investigations that Affected Over 427,000 Individuals
The U.S. Department of Health and Human Services Office for Civil Rights announced settlements with four HIPAA‑covered entities after ransomware breaches that exposed the protected health information of more than 427,000 individuals. Regional Women’s Health Group, Assured Imaging, Consociate Health...

Bridging the AI Agent Authority Gap: Continuous Observability as the Decision Engine
Enterprises face an AI Agent Authority Gap because agents inherit authority from existing human, bot and service‑account identities. The core problem is not the agents themselves but the ungoverned delegation chain, often hidden as "identity dark matter" across applications and...
26 FakeWallet Apps Found on Apple App Store Targeting Crypto Seed Phrases
Cybersecurity firm Kaspersky uncovered 26 malicious iOS apps on Apple’s App Store that impersonate popular cryptocurrency wallets, primarily targeting users with Chinese‑region Apple accounts. The apps use typosquatted names and identical icons to trick users into installing them, then hijack...

Quantum‑Safe Becomes Mandatory Baseline, Market Will Price It
My prediction about post-quantum security: we'll see the same thing we saw with privacy -- one day, out of the blue, quantum-safety will no loner be optional. It will become a consensus baseline requirement, the obvious feature that chains...

Weekly Roundup: April 17-23, 2026
Harvard Law School’s Forum weekly roundup (April 17‑23, 2026) covered a spectrum of governance issues, from SEC Commissioner Hester Peirce’s warning about the Consolidated Audit Trail’s multi‑billion‑dollar cost and privacy risks to ISS’s legal challenge against Indiana’s proxy‑filing statute. The collection also...

BT Has Now Blocked over a Billion Clicks to Malicious Websites, Says NCSC
BT and its mobile arm EE have now blocked more than a billion clicks to malicious websites, leveraging the UK National Cyber Security Centre’s Share and Defend programme. The service protects roughly 46 million mobile subscribers and 12 million fixed‑line customers by...

Cybersecurity in the AI Age: Speed and Trust Define Resilience
Cybersecurity now hinges on speed and trust as AI reshapes threat dynamics. CrowdStrike reports e‑crime breakout time has collapsed from 582 minutes in 2019 to just 29 minutes today, forcing organizations to detect and contain attacks within half an hour....

Threat Actors Ditch ‘Spray and Pray’ Attacks in Shift to Targeted Exploitation
Cyber criminals are abandoning high‑volume "spray and pray" campaigns in favor of precision attacks, according to SonicWall research. While overall ransomware volumes fell 87% last year, the number of compromised organizations in the UK rose 20%, with small‑businesses hit hardest....

Axios Npm Supply Chain Compromise – Guidance for Azure Pipelines Customers
On March 31 2026 malicious versions of the popular JavaScript HTTP client Axios (1.14.1 and 0.30.4) were briefly published to the npm registry, embedding a hidden dependency that contacted attacker‑controlled servers. The supply‑chain breach can affect Azure Pipelines builds that resolve dependencies...
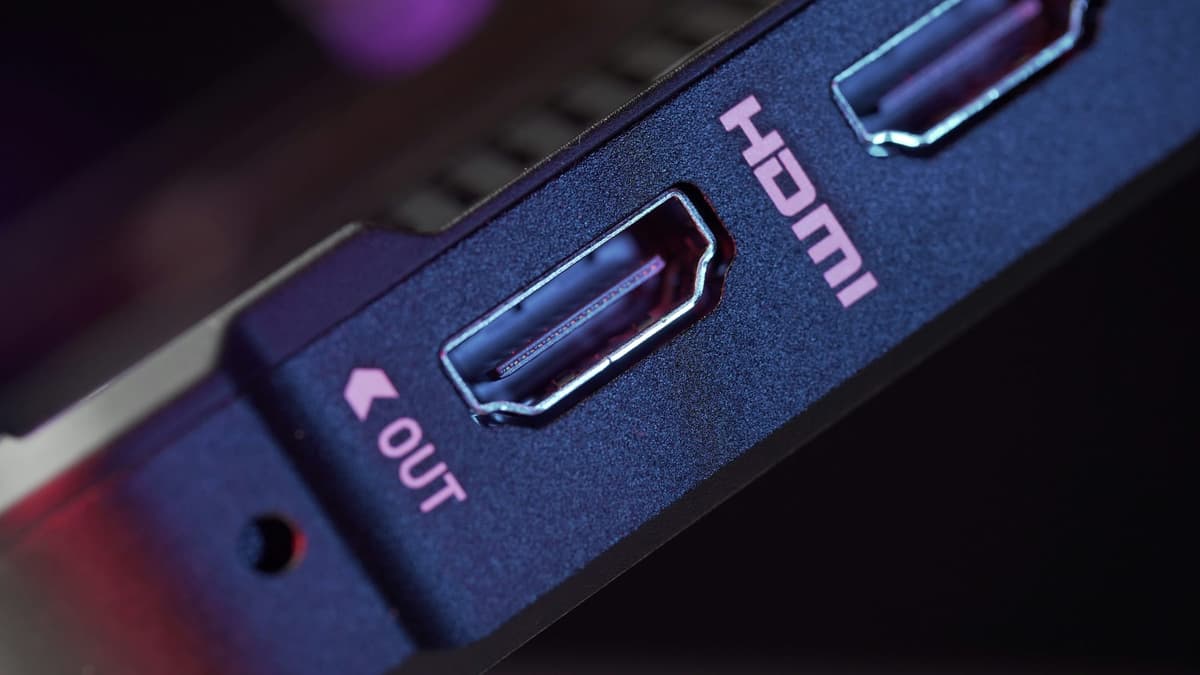
The NCSC Is Worried About HDMI-Based Attacks, Should You Be?
The UK National Cyber Security Centre (NCSC) has unveiled SilentGlass, a hardware device that acts as an HDMI‑to‑DisplayPort firewall, blocking unexpected or malicious signals. Built on NCSC‑owned intellectual property and licensed to UK firm Goldilock, the product will be manufactured...

AI‑Driven Crypto Scams Cost U.S. Victims Tens of Billions, IRS Warns
Federal investigators say AI‑enhanced cryptocurrency scams have already drained tens of billions of dollars from U.S. investors, with the IRS highlighting a surge in “pig‑butchering” schemes. Law‑enforcement agencies warn the rapid evolution of AI tools is outpacing detection efforts.

UK Petitions with 229,000 Signatures Demand End to Palantir Public Contracts
More than 229,000 people have signed two petitions calling on the UK government to terminate all public contracts with Palantir. The campaign targets contracts worth roughly £600 million across the NHS, Ministry of Defence and local authorities, arguing the US firm’s...

VMO2 Warns AI Is Generating Fake Customer Service Numbers
Virgin Media O2 (VMO2) warns that AI‑generated fake customer‑service numbers are being used by fraudsters, exposing 13% of Britons and 27% of 25‑34‑year‑olds to bogus contacts. The operator reports that 10% of consumers rely on AI‑generated numbers, and 20% of...

5 Clues Your Network Has Shadow AI
Enterprises are confronting widespread shadow AI, where unsanctioned AI tools operate across networks. An IBM study shows one‑in‑five firms suffered AI‑related breaches, yet only 37% have policies to detect such activity. The article outlines five network indicators—outbound traffic shifts, unverified...

UK Biobank Data of 500,000 Volunteers Listed for Sale on Alibaba
UK Biobank’s de‑identified health and genetic data for 500,000 volunteers appeared on the Chinese e‑commerce platform Alibaba. The breach, traced to three Chinese research institutions, prompted a parliamentary briefing, a temporary shutdown of the Biobank’s research platform, and renewed calls...

Anthropic’s Mythos Model Draws White House Attention Amid Global AI Policy Scrutiny
Anthropic’s latest AI system, Mythos, has prompted a flurry of high‑level meetings in Washington, a coordinated response from Indian banks, and early adoption by Mozilla for vulnerability hunting. The model’s unprecedented ability to locate software flaws is forcing regulators and...
Coupang Data Breach Sparks US‑South Korea Diplomatic Row Over E‑commerce Fairness
South Korean e‑commerce giant Coupang faces a massive data breach affecting 33.7 million users, prompting 54 US Republican lawmakers to accuse Seoul of discriminatory treatment. Korea’s National Assembly Speaker denounced the letter as interference, turning a corporate scandal into a diplomatic...

Rapid7 Confirms Kyber Ransomware Uses Quantum‑Safe ML‑KEM1024 Encryption
Security firm Rapid7 disclosed that the Kyber ransomware family encrypts files with the post‑quantum ML‑KEM1024 algorithm, making it the first ransomware known to employ quantum‑safe encryption. Threat analyst Brett Callow called it a historic first, underscoring a new direction for...

787: Disaster Recovery & Incident Response For Accidental Techies – Tony Martignetti Nonprofit Radio
In this episode of Nonprofit Radio, Amanda Bache, IT support and operations specialist at Paths for Families, breaks down disaster recovery (DR) and incident response (IR) basics for "accidental techies"—non‑technical staff who need clear, actionable plans. She emphasizes the importance...

Shadow AI Morphs Into Shadow Operations
The cybersecurity focus is shifting from data leakage in LLM prompts to the uncontrolled deployment of autonomous AI agents, termed “shadow operations.” Organizations are rapidly adopting open‑source agentic frameworks like Moltbot, often granting them high‑privilege API keys without proper oversight....

How Big a Threat Are Iranian-Backed Cyberattacks?
Iran‑backed hacking groups have infiltrated programmable logic controllers (PLCs) that run U.S. water, energy and wastewater systems, prompting a CISA advisory on April 7. The article traces a decade of Iranian cyber intrusions, from a 2013 dam hack to the recent...

Vulnerabilities Patched in CrowdStrike, Tenable Products
CrowdStrike and Tenable disclosed critical vulnerabilities in their flagship products and released patches this week. CrowdStrike’s LogScale suffered CVE‑2026‑40050, an unauthenticated path‑traversal that lets attackers read arbitrary files, mitigated for SaaS users and patched for self‑hosted deployments. Tenable reported CVE‑2026‑33694...

Kaspersky Discovers Vulnerability in Qualcomm Snapdragon Chips
Kaspersky ICS CERT uncovered a hardware‑level flaw in Qualcomm Snapdragon BootROM firmware that spans several MDM, MSM and SDX50 chip families. The vulnerability, catalogued as CVE‑2026‑25262, lets an attacker with brief physical access bypass secure‑boot, seize sensor data, and install persistent malware....

Cyber Security Agency Warns of Online Group 'Grooming Then Scam' Tactics
Taiwan’s National Institute of Cyber Security warns that hobby‑based online communities are becoming a new hunting ground for scammers. The fraudsters first send private messages, add victims on apps like LINE, and invite them to interest‑based groups before deploying surveys...

Tropic Trooper Uses Trojanized SumatraPDF and GitHub to Deploy AdaptixC2
Zscaler ThreatLabz uncovered a new campaign attributed to the APT group Tropic Trooper that weaponizes a trojanized version of the SumatraPDF reader to drop the AdaptixC2 post‑exploitation beacon. The malware fetches encrypted shellcode, uses GitHub as a command‑and‑control hub, and later...
The Calm Before the Ransom: What You See Is Not All There Is
The article warns that prolonged periods of security calm breed complacency, causing organizations to over‑estimate their protection and ignore emerging ransomware tactics. It cites Verizon’s 2025 DBIR, which found 54% of ransomware victims had credentials already circulating on dark‑web markets...

Security by Design – Cornerstones of Security and Compliance in an AI-Driven BSS
Telecom operators are rapidly adopting AI‑driven, SaaS‑based Business Support Systems, but the shift brings heightened security and compliance risks. Etiya’s Agentic BSS tackles these challenges by embedding security‑by‑design principles across architecture, AI governance, and data privacy. The platform leverages certified...

China-Linked Cyber Actors Turn to Massive Covert Botnets to Evade Detection
A new advisory from the UK National Cyber Security Centre reveals that China‑linked threat groups, dubbed China‑Nexus, have shifted from dedicated servers to massive covert botnets composed of compromised SOHO routers and IoT devices. The report cites networks like the...

ADoX Deployment in the Wild
Encryption between DNS clients and resolvers is expanding, yet the recursive‑to‑authoritative link remains largely unprotected. A recent study measured real‑world ADoX (ADoT/ADoQ) deployment, finding fewer than 1 % of domains support the RFC 9539 mechanism. Adoption is highly concentrated, with One.com alone...

LMDeploy CVE-2026-33626 Flaw Exploited Within 13 Hours of Disclosure
A critical SSRF flaw (CVE‑2026‑33626) in LMDeploy’s vision‑language module was exploited within 13 hours of its public disclosure. The vulnerability, affecting all versions up to 0.12.0, let attackers reach cloud metadata services, internal databases and perform internal port scans. Sysdig’s...

Revocation of X.509 Certificates
Recent measurements reveal two critical trends in X.509 certificate revocation. A SIGCOMM ’25 paper proposes publishing only revoked serial numbers as DNSSEC‑signed TXT records, leveraging NSEC and aggressive negative caching to achieve roughly 99.8% cache‑hit rates, with Let’s Encrypt’s 612 million...

Virgin Media O2 Warns of AI-Driven Scam Surge as Fake Customer Service Numbers Target Millions
Virgin Media O2 warns that AI‑powered fraud is driving a surge in fake customer‑service phone numbers, with 13 percent of Britons and 27 percent of 25‑34‑year‑olds encountering deceptive listings. Scammers exploit trust in top search results and AI‑generated contacts, leading many consumers...
Why Supply Chain Resilience Is Under the Spotlight
Supply‑chain security has become a top priority as third‑party breaches surged, with Verizon reporting 30% of incidents linked to vendors—double the previous year—and SecurityScorecard finding over 70% of firms faced a material supplier breach. High‑profile attacks on NHS supplier DXS...

Bugs Aren’t the Whole Story in Cybersecurity
The amount of squabbling over bugs, bug quality, AI bug extermination, how security is doomed/not doomed/unchanged/improved based on bugs… it’s ridiculous. Bugs are not the totality of cybersecurity.

LG Uplus Surpasses One Million USIM Updates and Replacements
South Korean telecom LG Uplus reported completing over one million USIM updates and free replacements within ten days of launching a nationwide security programme. The effort, which began on April 13, saw 427,385 updates and 581,094 replacements by April 22,...

AI Is Speeding up Nation-State Cyber Programs
Microsoft’s senior cyber policy director Kaja Ciglic says nation‑state cyber programs have shifted from niche tools to a core element of national power, tightly linked with military, economic and diplomatic levers. Automation and AI‑enabled tooling now let adversaries scale reconnaissance, exploitation...

A Study of 1,000 Android Apps Finds a Privacy Policy Logging Gap
A new study of 1,000 Android apps reveals a stark gap between privacy policies and actual logging practices. Fewer than one‑third of policies mention logging, and only four policies accurately disclose the sensitive data found in runtime logs. The research...

The Top 8 Enterprise VPN Solutions
The article ranks the leading enterprise VPN solutions, naming Cisco AnyConnect as the best overall and highlighting Checkpoint, NordLayer, SonicWall, Fortinet, Palo Alto, and ZScaler for specific strengths. It underscores the rising urgency of secure remote access, citing IBM’s 2024...

Weak Security Means Attackers Could Disable All of a City's Public EV Chargers
Researchers at Black Hat Asia demonstrated that rented IoT infrastructure—such as public EV chargers and shared e‑bikes—often sacrifices security for convenience. Hetian Shi of Tsinghua University uncovered shared authentication keys, exposed debug ports, and backend services that fail to verify users. Using his...

Cybersecurity-Focused Regulation S-K Joint Trades Comment Letter
Five banking trade groups have filed a joint comment letter urging the SEC to rescind or sharply narrow Regulation S‑K Item 106 and Form 8‑K Item 1.05, both introduced by the 2023 Cybersecurity Disclosure Rule. The groups argue that Item 106 imposes a unique,...

Data Lakes Do Not Leak, Permissions Do
Modern analytics platforms are failing not because data lakes store too much information, but because permission models lag behind platform ambition. Organizations often apply broad, shared‑folder style access for convenience, which becomes a governance nightmare as the lake expands to...

CleanStart Launches Shell‑less, Read‑only Containers to Harden DevOps Pipelines
CleanStart introduced a statically compiled init binary, clnimg-init, that automatically converts Docker images into shell‑less, read‑only containers. The change requires no modifications to Dockerfiles, CI/CD pipelines or deployment processes, removing the migration barrier that has kept many enterprises from adopting...

Kubernetes 1.36 Rolls Out 70 Enhancements, Boosting AI‑Driven DevOps
Kubernetes 1.36 was released with 70 enhancements, cementing its role as the backbone of AI‑driven infrastructure. The update brings fine‑grained Kubelet API authorization to GA, a beta Resource Health State for Dynamic Resource Allocation, and an alpha Workload Aware Scheduling...

Cloudflare Launches GA Sandboxes, Giving AI Agents Persistent Isolated Environments
Cloudflare announced the general availability of its Sandboxes service, providing developers with persistent, isolated Linux environments for AI agent workloads. The rollout, part of Agents Week, follows a beta that began in June and aims to tighten security and streamline...

Bedrock Data Extends ArgusAI Governance to Google Vertex AI, Unifying AI Data Controls
Bedrock Data announced today that its ArgusAI governance platform now supports Google Vertex AI Search and Dialogueflow, enabling a single policy model for AI agents across Amazon Bedrock, Snowflake Cortex AI, ChatGPT Enterprise and Google's AI services. The move aims...

SANS Stormcast Friday April 24rd, 2026: Apple Update; Bitwarden Compromise; ASP.NET Core Patch
In this 6‑minute Stormcast episode, Johannes Ulrich discusses three urgent security updates: Apple’s iOS/iPadOS patch that fixes a notification‑center bug exploited to recover Signal messages, the compromise of Bitwarden’s command‑line tools via a GitHub‑worker attack linked to the earlier Checkmarx‑kicks...

Fake App Drains Filipino Retiree’s Life Savings via ‘Malware-as-a-Service’
A fraudulent mobile app, sold as a help‑desk tool, infected a 68‑year‑old Filipino retiree's phone with malware‑as‑a‑service, allowing criminals to siphon his life‑savings. The attack illustrates a broader shift in Southeast Asian cybercrime, where organized groups in Cambodia are moving...
AI Will Empower, Not Undermine, Security Teams
Somebody asked me here at the conference: given AI advances, are we fucked in D&R and SOCs? I said “no, AI will help a lot here, this is fine, defenders will be fine.” (1/2)