Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

AI Security Needs a Shift From Models to Systems, Researchers Argue
Researchers from Google, UC San Diego, and UW‑Madison argue that enterprises must stop treating AI agents as trusted software and instead secure them as untrusted systems. Their new paper shows that model‑level defenses like prompt guardrails fail when agents access tools, memory, and APIs, citing eleven real‑world attacks that violated core security principles. The authors propose five systems‑security principles—least privilege, tamper resistance, complete mediation, secure information flow, and human‑factor accounting—and outline three mechanisms needed for robust agentic defenses. They also introduce an Agentic Detection and Response (ADR) framework that identified 67% of attacks with zero false positives in a large‑scale deployment.

AWS Security Digest #262 - Not Private
The May 25 AWS Security Digest warns that a CISA contractor accidentally exposed high‑privilege GovCloud keys on a public GitHub repo, remaining active for 48 hours after discovery. A new wave of supply‑chain attacks, the TeamPCP npm worm, infected Alibaba’s @antv data‑viz suite...

As AI Speeds Coding, CVE Lite CLI Keeps Security Deliberately AI-Free
The OWASP‑backed CVE Lite CLI offers a local‑first vulnerability scanner for JavaScript and TypeScript projects, analyzing npm, pnpm and Yarn lockfiles directly on a developer’s machine. By surfacing dependency risks at the moment code is written, it aims to replace...

US States Step up Cyber Defenses to Protect Local Communities
U.S. state governments are expanding cyber defense programs—including cybersecurity clinics, regional security operations centers (RSOCs), and state cyber corps—to protect local communities and essential services. A new guide from UC Berkeley’s Center for Long‑Term Cybersecurity outlines a roadmap for shared...

266,000 Affected by Data Breach at Radiology Associates of Richmond
Radiology Associates of Richmond disclosed a data breach that compromised protected health information for approximately 266,000 individuals. The intrusion began around July 25, 2025, was contained with external cybersecurity help, and a forensic investigation concluded on April 6, 2026. On May 21 the firm mailed...

Zero-Click WhatsApp Account Takeover Hits iPhone Users Running iOS 16. No Linked Devices, No Warning
Italian forensic firm Forenser uncovered a zero‑click attack that hijacked WhatsApp accounts on iPhones running iOS 16. The exploit leverages CVE‑2025‑43300 in Apple’s ImageIO framework and CVE‑2025‑55177 in WhatsApp’s sync code to steal session keys without any user interaction. Compromised devices...

Taiwan Flags Five Major Cyber Risks After 726 Security Incidents in 2025
Taiwan’s Ministry of Digital Affairs recorded 726 cybersecurity incidents in 2025, a slight decline of 29 cases from 2024. Most incidents were low‑severity Level 1 events, but unauthorized access accounted for 68.6 % of all reports. The Administration for Cyber Security identified...

To Pay, or Not to Pay: 58% of CISOs Say They Would Pay the Ransom for Their Data
A survey of 750 CISOs in the US and UK shows 58% would pay a ransomware ransom to recover data. Law‑enforcement agencies in both countries warn against payment, citing no guarantee of data return and the encouragement of attackers. IDC...

Wireshark 4.6.6 Resolves ROHC Parser and Buffer Overflow Vulnerabilities
The Wireshark Foundation released version 4.6.6, addressing two critical security flaws: a Dissector Crash in the ROHC protocol parser (wnpa‑sec‑2026‑51) and a global‑buffer‑overflow in the MACsec dissector. The update also resolves multiple Windows‑specific stability problems, including crashes in Visual Studio...
![[Interview] Europe’s Data Chief on Sharing Info with US: ‘The Concerns Are Really Big’](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://static.euobserver.com/2026/05/DSC_9931-2400x1804.jpg)
[Interview] Europe’s Data Chief on Sharing Info with US: ‘The Concerns Are Really Big’
European Data Protection Supervisor Wojciech Wiewiórowski warned that data‑sharing arrangements with the United States and Israel raise serious privacy risks. His latest annual report noted a sharp rise in complaints about Europol data breaches and highlighted the lack of a...
TrapDoor Supply Chain Attack Spreads Credential-Stealing Malware via Npm, PyPI, and CratesIO
A coordinated supply‑chain attack dubbed TrapDoor has compromised more than 34 packages across npm, PyPI, and Rust’s Crates.io since May 22, 2026. The malicious modules target developers in crypto, DeFi, AI, and blockchain circles, stealing wallets, SSH keys, cloud tokens and other...
OpenHack: Open-Source AI-Powered Vulnerability Research
Hadrian, a Dutch security firm, released OpenHack, an MIT‑licensed, file‑based workspace that enables AI‑assisted vulnerability research. The platform integrates with coding harnesses such as Claude Code, Codex and Cursor, orchestrating agents through a state‑machine workflow while preserving all data in...
Webinar Today: A 30-Day Plan to Protect Your SME From Cyberattacks
South African SMEs are increasingly targeted by cybercriminals, as recent breaches at institutions like Wits University and tech wholesaler Esquire Technologies illustrate. The attacks often start with simple tactics such as phishing emails or stolen Microsoft 365 passwords, highlighting weak...

UAE Advances One of the World’s First National Post-Quantum Migration Programs
The United Arab Emirates announced one of the world’s first national post‑quantum migration programs, outlining a roadmap to transition critical government infrastructure to quantum‑resistant cryptography by 2028. The initiative follows a broader surge in quantum activity, including a $28 M+ angel...
Cisco Issues Emergency Patch for CVE‑2026‑20182, a CVSS 10 SD‑WAN Zero‑Day
Cisco has rolled out an emergency patch for CVE‑2026‑20182, a maximum‑severity authentication bypass in its Catalyst SD‑WAN Controller and Manager. The flaw, rated CVSS 10.0, is being actively exploited by a sophisticated threat actor, prompting a CISA emergency directive for federal...

The AI Security Gap Nobody Wants to Admit Is Already Here
On March 31, 2026 Anthropic mistakenly published the full Claude Code source—about 512,000 lines across 1,906 files—to a public npm bucket, where it was quickly mirrored on GitHub. The leak exposed the AI agent's permission‑enforcement logic, hidden feature flags and references to an...

If You're Still Hanging on to This Classic Android File Explorer, You Need to Switch Now
ES File Explorer, once a staple Android file manager, was pulled from the Google Play Store in 2019 after investigations revealed ad‑fraud and intrusive advertising. The app’s later versions added aggressive ads and background activity, turning it into a security...

Qualys Uncovers Nine-Year-Old Linux Kernel Flaw Giving Root Access to Unprivileged Users
Security researchers at Qualys disclosed CVE-2026-46333, a logic error in the Linux kernel’s ptrace subsystem that has lingered since November 2016. The flaw lets an unprivileged user read /etc/shadow, steal SSH keys and execute commands as root, putting millions of...

Anthropic’s Project Glasswing AI Finds 10,000+ Critical Flaws in One Month, Only 97 Patched
Anthropic disclosed that its restricted Project Glasswing AI uncovered more than 10,000 high‑or critical‑severity software flaws in just four weeks, yet only 97 have been patched. The speed of discovery outpaces the open‑source ecosystem’s ability to remediate, prompting urgent calls...

The US Blacklisted Anthropic as a Security Threat. Its Spy Agencies Are Using Claude Anyway.
The Pentagon has officially blacklisted Anthropic as a national‑security supply‑chain risk, yet the NSA continues to run Anthropic’s Claude model because a critical chip shortage leaves it with no viable alternative. The White House approved a secret $9 billion emergency package...

Verizon Deploys Anthropic’s Claude Mythos AI to Hunt Network Vulnerabilities
Verizon announced on May 15 that it will use Anthropic’s restricted‑access Claude Mythos Preview model to scan its network for zero‑day vulnerabilities. The move makes Verizon the first major U.S. telecom to field a frontier large‑language model for real‑time security,...

Sophos Flags AMOS macOS Stealer as Top Threat to CI/CD Agents, Citing 40% Surge
Sophos MDR disclosed that the AMOS macOS infostealer now accounts for nearly 40% of all macOS protection updates in 2025, a sharp rise that threatens macOS‑based CI/CD agents. The malware relies on a single malicious Terminal command, prompting urgent hardening...

Verizon DBIR Shows Vulnerability Exploits Now Top Breach Vector, Surpassing Credential Theft
Verizon’s 2026 Data Breach Investigations Report reveals that 31% of confirmed breaches began with vulnerability exploitation, eclipsing credential theft, which fell to 13%. The shift is driven by AI‑accelerated weaponization and slowing patch‑management, raising fresh challenges for defenders.

What Corporate Boards Need to Know and Do About Anthropic’s Mythos and Project Glasswing
Anthropic unveiled Claude Mythos Preview, an AI model that discovers thousands of high‑severity vulnerabilities, and launched Project Glasswing to give select critical‑infrastructure firms defensive access. The controlled release aims to shift the attacker‑defender balance by providing unprecedented visibility into latent...

Yarbo Robot Mowers Vulnerable to Remote Hack, Exposing Home Networks
Security researcher Andreas Makris disclosed that roughly 6,000 Yarbo autonomous lawn mowers and snow blowers contain hard‑coded root passwords and a persistent remote‑access tunnel. Yarbo co‑founder Kenneth Kohlmann confirmed the findings and said the company is rolling out firmware fixes.

LeakWatch 2026, Security Incidents, Data Breaches and IT Situation for the Current Calendar Week 21 – Pentecost, Fake Voices and...
Calendar week 21 (May 19‑25 2026) was defined by a wave of trust‑based attacks rather than single high‑profile leaks. Phishing campaigns timed with the Pentecost holiday duped users of PayPal, SecureGO, easybank and the Deutschlandticket, while the Storm‑2949 group abused Self‑Service Password Reset...

Ukraine Reclaims 400 Km² After Cutting Off Russian Starlink Access
U.S. intelligence reports that Ukraine recaptured about 400 square kilometres of land after Ukrainian teams disabled thousands of illicit Starlink terminals used by Russian forces. The move disrupted Moscow’s command‑and‑control, shifting battlefield momentum in Kyiv’s favor.

Genesis Ransomware Claims US Law Firm Victim as FBI Warns of Surge in Microsoft 365 Phishing
The Genesis ransomware gang announced a breach of an unnamed US law firm, and the FBI issued a fresh alert about the Kali365 phishing toolkit that can bypass Microsoft 365 multi‑factor authentication. Both developments underscore escalating cyber threats to legal...

Google Report Finds LLM‑Generated Malware Evades Detection, Threatens 2FA Defenses
Google's latest research shows that large‑language‑model (LLM) generated malware is increasingly difficult to detect and can bypass two‑factor authentication. The findings signal a shift toward more automated, scalable cyber threats and have prompted security firms to reassess defensive tools.

Megalodon Attack Inserts Malicious CI/CD Workflows Into 5,500+ GitHub Repos in Six Hours
A threat actor named Megalodon automated a supply‑chain assault that added malicious GitHub Actions workflow files to 5,561 repositories, delivering 5,718 commits in a six‑hour window on May 18, 2026. The campaign harvested AWS keys, GCP tokens, SSH keys and...

Quantum Bridge Secures $8 Million Series A to Deploy Quantum‑Resistant Network Security
Quantum Bridge Technologies announced an $8 million Series A round led by Primo Capital SGR, bringing its total funding to $16 million. The capital will accelerate deployment of its patented Distributed Symmetric Key Establishment protocol across financial, telecom, and government networks to...

Laravel Lang Open‑Source Packages Compromised with RCE Backdoor in 700+ Versions
A supply‑chain attack inserted a remote code execution backdoor into more than 700 historical versions of Laravel Lang localization packages. The malicious tags were published on May 22‑23, 2026, and could run automatically when Composer loads the packages, putting countless...

Ghostwriter APT Group Revives Phishing Campaign Using Ukrainian E‑learning Platform
The Belarus‑linked APT group Ghostwriter has launched a fresh phishing operation against Ukrainian government agencies, using the domestic e‑learning platform Prometheus as bait. The campaign delivers a malicious JavaScript file that drops the OYSTERBLUES payload and ultimately a Cobalt Strike...

DORA Compliance Is Not Resilience: Why Financial Services Need Continuous Validation
The EU’s Digital Operational Resilience Act (DORA) took effect in January 2025, obligating major financial firms to conduct a Threat‑Led Penetration Test (TLPT) at least every three years. Mark Kuhr argues that this three‑year cadence is out of step with a...
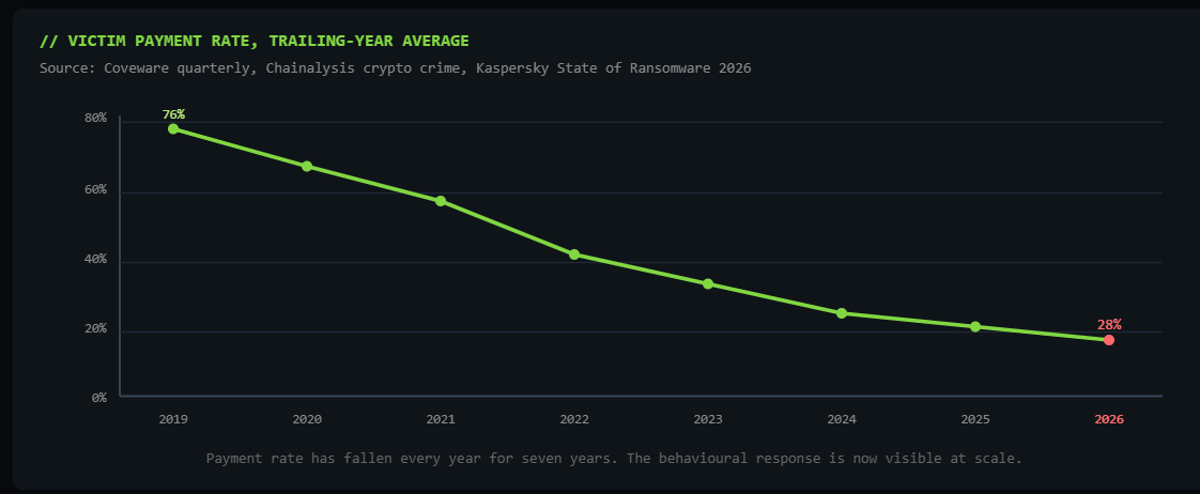
Why Pure Extortion Is Replacing Traditional Ransomware
Ransomware gangs are abandoning encryption in favor of pure data extortion, stealing sensitive information and threatening public leaks. The shift is driven by lower detection risk, faster execution and higher profitability, with payment rates dropping from 76% in 2019 to...

Polymarket Loses $700,000 After Six‑year‑old Private Key Hack, Spotlighting Web3 DevOps Gaps
Polymarket confirmed a $700,000 loss after a six‑year‑old internal private key was exploited on May 22, 2026. The breach, traced to 16 addresses and multiple exchanges, prompted the firm to rotate the key and shift to KMS‑managed secrets, raising alarm...
Cisco Patches Critical CVSS 10.0 Flaw in Secure Workload APIs, Raising Zero‑Trust Concerns
Cisco issued emergency patches for CVE-2026-20223, a CVSS 10.0 authentication bypass in its Secure Workload API platform. Security experts warn the flaw threatens zero‑trust segmentation, urging immediate remediation and architectural review.

Cyber-Star Wars: Securing Satellites and Critical Infrastructure
Space systems are now classified as critical infrastructure, making them prime targets for cyber‑attacks amid heightened geopolitical tensions such as Russia’s war in Ukraine and the Iran conflict. Attack vectors include DDoS, spoofing, supply‑chain malware, and command hijacking, with a...

‘Underminr’ Vulnerability Lets Attackers Hide Malicious Connections Behind Trusted Domains
Security researcher ADAMnetworks has identified a new CDN‑based vulnerability called Underminr, a variant of domain fronting that lets attackers present a trusted SNI and Host while the request is routed to a different tenant’s IP. The technique exploits mismatches between...

Dirty Frag, Copy Fail, Fragnesia: The Start of a Worrisome Linux Security Trend
A trio of Linux kernel vulnerabilities—Dirty Frag, Copy Fail and Fragnesia—have been disclosed within a week, illustrating how AI‑driven analysis can surface page‑cache bugs almost instantly after a fix. Linus Torvalds and other leaders note that AI‑generated findings are no...

Npm Launches Staged Publishing and New Install‑source Flags to Tighten Supply‑chain Security
npm announced today that its CLI 11.15.0 now supports staged publishing and three new install‑source flags. The changes require human approval before a package version becomes installable and let maintainers explicitly allow or block file, remote and directory sources, addressing...

Riot's Vanguard Update Knocks $6,000 Cheat Hardware Out of Play
Riot Games rolled out a Vanguard anti‑cheat update that disables high‑cost Direct Memory Access (DMA) cheat cards used to hack Valorant. The move turns $6,000‑plus rigs into unusable paperweights, prompting both praise for its effectiveness and concern over hardware‑level enforcement.

JFrog’s 2025 Supply Chain Report Warns AI‑Powered Threats Surge as Package Growth Soars 67%
JFrog released its 2025 Software Supply Chain Security State of the Union 2026 report, showing a 67% year‑over‑year rise in new packages and a rapid expansion of AI‑driven attack surfaces. The findings call on DevOps and security leaders to move...

Project Glasswing Secures Over 10,000 Software Components Using Anthropic’s Mythos AI
Anthropic’s Project Glasswing, a collaboration of roughly 50 tech firms, has used its Claude Mythos AI to uncover more than 10,000 high‑ or critical‑severity vulnerabilities in essential software. The effort, highlighted by Cloudflare’s discovery of 2,000 bugs, marks a dramatic...
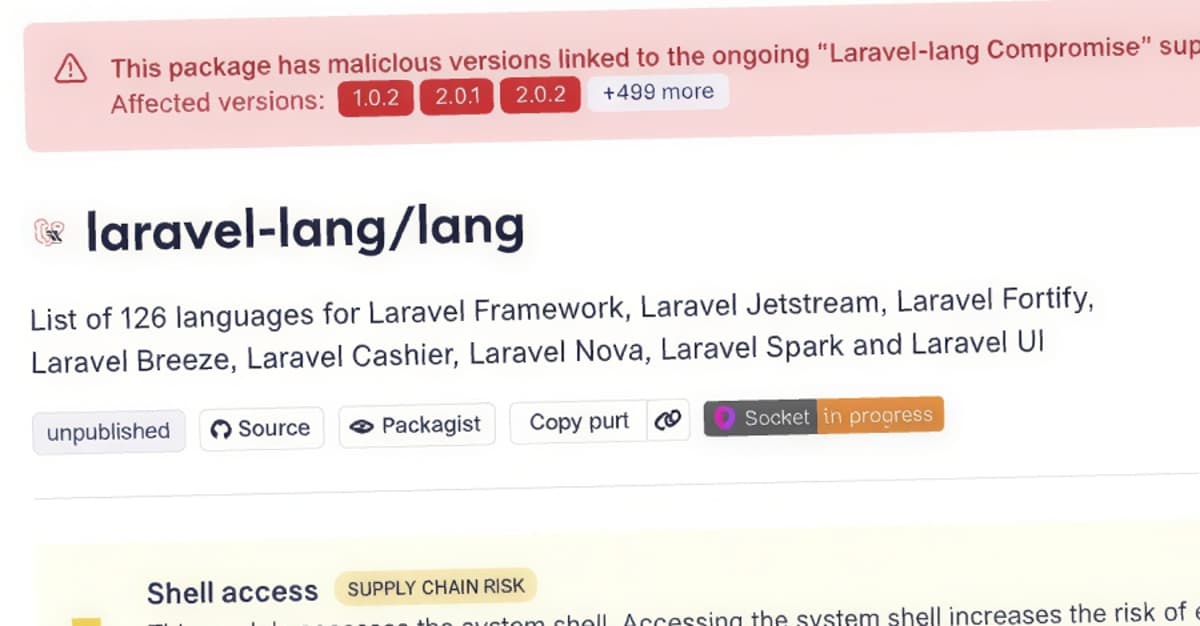
Laravel-Lang PHP Packages Compromised to Deliver Cross-Platform Credential Stealer
Researchers discovered a supply‑chain attack that compromised four Laravel‑Lang PHP packages by rewriting all existing Git tags to a malicious commit. The malicious src/helpers.php file is added to the Composer autoload files, causing automatic execution whenever a Laravel or other...
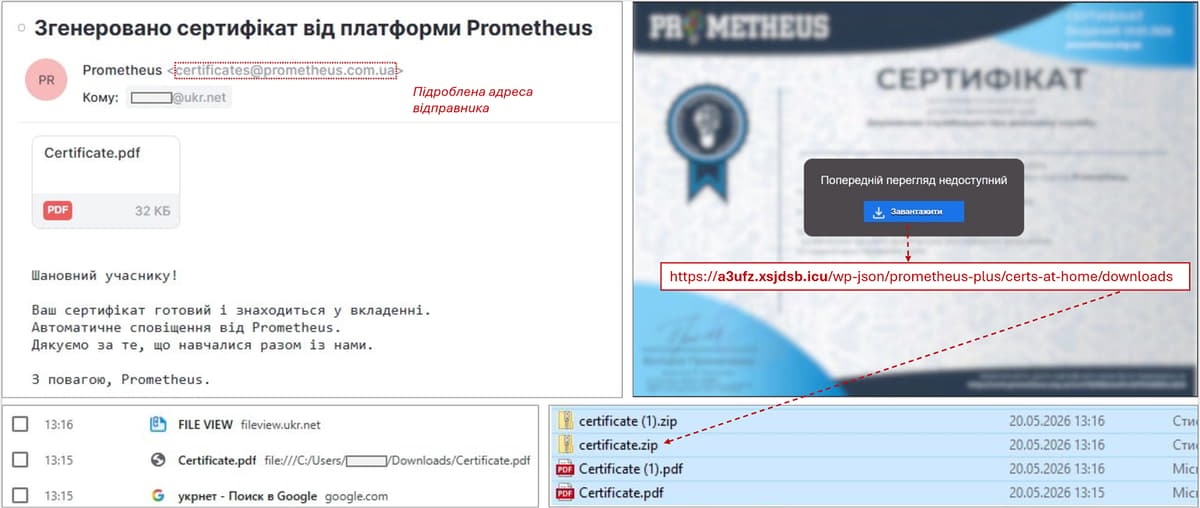
Ghostwriter Is Back, Using a Ukrainian Learning Platform as Bait to Hit Government Targets
Ghostwriter, the Belarus‑linked APT group, has revived a phishing campaign against Ukrainian government agencies by masquerading as the domestic e‑learning platform Prometheus. The emails, sent from compromised accounts, contain PDF attachments that lead to a ZIP file with a JavaScript...

How Should We Update on AI-Enabled Coups Post-Mythos?
Anthropic’s Claude Mythos, deemed too dangerous for public release, can autonomously discover and exploit thousands of software vulnerabilities, turning zero‑day attacks into an industrial‑scale process. The model’s ability to out‑code most humans and expose a decades‑old flaw in a leading...

NY DFS Issues AI‑Focused Cybersecurity Guidance for Insurers
The New York State Department of Financial Services (DFS) has issued new cybersecurity guidance aimed at insurers, banks and other financial firms to address a "heightened threat environment" driven by AI and geopolitical risks. Acting Superintendent Kaitlin Asrow said the...

P2PInfect Botnet Breaches Kubernetes Clusters via Exposed Redis Services
FortiGuard Labs disclosed that the Rust‑based P2PInfect botnet has been compromising Google Kubernetes Engine clusters by exploiting Internet‑exposed Redis instances. The campaign, observed from November 2025 through February 2026, leverages CVE‑2022‑0543 and a peer‑to‑peer mesh to maintain a dormant foothold inside cloud...

CloudEdge Hack: Arenti, ieGeek, Boifun, Anran Exposed
In May 2026 security researcher Sammy Azdoufal disclosed four critical flaws in Meari Technology’s CloudEdge camera platform, affecting roughly 1.1 million baby monitors and security cameras across 118 countries. The vulnerabilities—an unprotected MQTT broker, unauthenticated image storage, hard‑coded cryptographic keys, and...