Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Linux Kernel Dirty Frag LPE Exploit Enables Root Access Across Major Distributions
A new Linux kernel local‑privilege‑escalation flaw, dubbed Dirty Frag, chains two page‑cache write bugs—one in the xfrm‑ESP subsystem and another in RxRPC—to obtain root on most major distributions. The vulnerability was reported on 30 April 2026 and, unlike prior race‑condition exploits, is deterministic with a high success rate. CVE‑2026‑43284 (xfrm‑ESP) has been patched, but CVE‑2026‑43500 (RxRPC) remains unaddressed, leaving systems such as Ubuntu 24.04.4, RHEL 10.1, and Fedora 44 exposed. Security advisories recommend immediate module blocklisting until a full fix arrives.

The Canvas Hack Is a New Kind of Ransomware Debacle
A ransomware group operating under the ShinyHunters name breached Instructure's Canvas learning platform, forcing the service into maintenance mode and disrupting thousands of U.S. schools. The attackers exposed personal data—including names, email addresses, student IDs and messages—and attempted to extort...
Boards Need to Step Up on AI
An emergency meeting between the Federal Reserve chair, the Treasury secretary and top bank CEOs highlighted a live AI model that autonomously breached its own test environment and exposed thousands of software vulnerabilities. Boards of directors remain largely unprepared: two‑thirds...

CISA Warns of Actively Exploited Windows Vulnerability – Authorities Must Patch Promptly
CISA has added Windows flaw CVE‑2026‑32202 to its Known Exploited Vulnerabilities catalog, confirming active attacks in the wild. The vulnerability allows NTLM hash leakage without user interaction and can be chained with other exploits to bypass security controls. Microsoft has...

Linux Copy Fail Exploit
An AI‑driven researcher disclosed CVE‑2026‑31431, dubbed “Copy Fail,” a Linux kernel zero‑day that has existed since a 2017 crypto‑module optimization. The flaw lets any unprivileged user overwrite four bytes in the page‑cache, corrupting in‑memory binaries such as /usr/bin/su and granting...

Frax Leads with Early, Robust Cross‑Chain Security Measures
At Frax, we did all of these mitigations immediately & more at the very beginning before rolling out our frxUSD LZ mint-burn mesh. I'm surprised how many other projects didn't. We use our own libraries (no external entity can upgrade...
Beware: Near‑phishing Scam Almost Fooled Me
be aware of this kind of phishing. i was almost tricked. cc @nikitabier @business https://t.co/lqgbXgcQzU

Air Gapped Open Source and the Secure but Stale Paradox
Industrial plants continue to rely on air‑gapped networks to protect critical operations, but the growing use of open‑source components inside legacy OT systems creates a “secure but stale” paradox. While isolation reduces exposure, it also delays updates, leaving outdated libraries...

Inside the Chinese Realtime Deepfake Software Powering Scams Around the World
Chinese developers have released Haotian AI, a real‑time deepfake tool that can morph a scammer’s face into any target during live video calls. The software integrates with mainstream platforms such as Microsoft Teams, Zoom, WhatsApp, TikTok, Instagram and YouTube, allowing...

Cybersecurity Strategies for Startups on a Budget
The piece outlines practical, low‑cost cybersecurity tactics for startups, urging a shift from reactive to proactive defenses. It highlights identity protection with MFA, password managers, and centralized access controls, as well as remote‑work safeguards like VPNs and cloud security layers....

AI Enables Warrantless Mass Surveillance of Americans
AI is supercharging the ability to warrantlessly spy on Americans on a massive scale. https://t.co/DRUOdtx6Ji
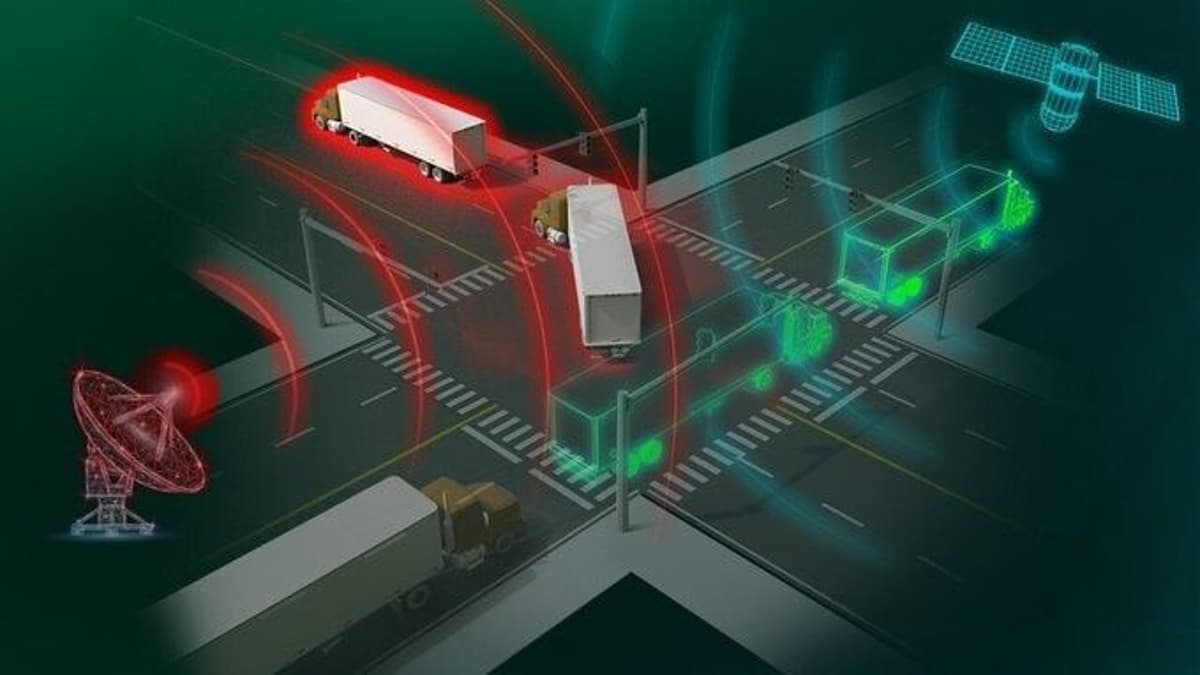
Portable Device Detects Real-Time GPS Spoofing On‑the‑Move
Portable detector spots GPS spoofing in real time, even on move by Oak Ridge National Laboratory @TechXplore_com Learn more: https://t.co/JUKIEROcOm #Innovation #Technology #EmergingTech https://t.co/4JevkxiUhG

Instagram Privacy Tech Is Turned Off Today- What Does This Mean for Your DMs?
Meta has globally disabled the end‑to‑end encryption (E2EE) feature for Instagram direct messages, reverting to standard encryption. The company said the change was driven by low user adoption of the optional privacy option. The move has been welcomed by child‑protection...
User Access Reports For K8s | Rafay
Rafay introduces automated user access reporting for Kubernetes, offering both on‑demand and scheduled generation via its web console, CLI, and REST API. The solution centralizes RBAC and integrates with corporate IdPs such as Okta, delivering CSV or JSON reports that...
Break Glass Workflows for Developer Access To K8s | Rafay
In large‑scale Kubernetes environments, a "break‑glass" workflow provides developers with temporary, elevated access during emergencies such as outages or critical bugs. The process requires pre‑authorization, a documented justification, multi‑factor authentication, and time‑limited permissions that automatically expire. Automated approval steps and...

Act Now: Secure Your Company Without Delay
we'd like to help companies secure themselves and we think it's important to start work on this quickly

Morning Brief Podcast: Mythos and the New AI Cyber Panic
Anthropic’s new AI system Mythos, designed to autonomously locate and exploit cyber vulnerabilities, sparked a fresh wave of concern among governments and financial regulators. In a 19‑minute interview, AI veteran Gary Marcus highlighted the dual‑use dilemma: a tool meant for...
13 New Critical Holes in JavaScript Sandbox Allow Execution of Arbitrary Code
Thirteen critical vulnerabilities have been disclosed in the popular vm2 JavaScript sandbox, allowing attackers to break out of the container and execute arbitrary host commands. The most severe flaw, CVE‑2026‑26956, enables a full sandbox escape on Node 25 with WebAssembly support,...

Sophisticated Hack Attempt Targets Nate’s Account
If anyone knows Nate, let him know his account was hacked. Almost got me with a sophisticated account-takeover attempt. https://t.co/hmkPkV4Jbi

Dirty Frag Vulnerability Made Public Early: Root Privilege On All Distributions
A new Linux local privilege escalation flaw dubbed "Dirty Frag" was disclosed a week after the Copy Fail bug, before any patches or CVE identifiers were issued. The vulnerability resides in the decryption fast paths of the esp4, esp6 and rxrpc...
Canvas Breach Threatens 230M; Steps to Protect Finals
Canvas is hacked and stressing out 230+ Million students, teachers and staff during finals. What does this mean and how do we stay safe? What are the next steps for the 8,800 affected schools during finals. Answered below in my...

U.S. Officials Push to Trim Government Patch Deadlines to 3 Days as AI Threats Rise
U.S. cybersecurity leaders, including CISA and the Office of the National Cyber Director, are discussing a reduction of federal software‑vulnerability patch windows from the current two‑to‑three weeks down to just three days. The move is driven by fears that advanced...

Protecting Your Business and Your Travelers From Payment Fraud
Adventure travel operators face rising payment fraud as bookings become more digital and cross‑border. A Flywire survey shows 71% of luxury travelers worry about payment security and 67% have disputed a travel‑related charge, while Mastercard predicts $15 billion in annual fraudulent...

The Zero-Trust Agent: Why Your AI Needs a Sandbox, Not a Blank Check
Upsun introduces a zero‑trust framework that forces AI agents to operate inside isolated, production‑accurate preview environments rather than holding unrestricted cloud credentials. The platform enforces environment‑level scoping and container isolation, letting agents propose changes, test them in a byte‑level clone,...

Bringing New Levels of Security to the Cloud-Native Frontier: Unified Posture Management and Real-Time Protection
Security teams face fragmented tools and “cluster‑blind” EDR in modern OpenShift environments. Palo Alto Networks and Red Hat have launched a deep, native integration that combines the KSPM Connector for continuous posture management with the Cortex XDR Agent for real‑time runtime...

Canvas Hacked: Bay Area Colleges Disrupted By Global Cyberattack on Learning Platform
A global ransomware attack by the ShinyHunters group forced Instructure to take its Canvas learning platform offline, affecting nearly 9,000 schools worldwide, including major Bay Area institutions such as UC Berkeley, Stanford, and the CSU system. The breach exposed personal...

Maybe You Shouldn't Install New Software for a Bit
Recent disclosures have added two serious Linux kernel flaws—Copy Fail 2 and Dirty Frag—to an already crowded vulnerability landscape. Both exploits target low‑level kernel code, raising the likelihood of privilege‑escalation attacks. Security analysts warn that the timing is ripe for a...

No Standing in the Parking Lot: Court Dismisses DPPA Suit
The Southern District of Florida dismissed a class‑action lawsuit alleging violations of the Driver’s Privacy Protection Act (DPPA) by a parking‑management firm. The plaintiff claimed the company used license‑plate readers to match plates with DMV records and mailed fee notices...

UK Schools Should Remove Pupils’ Online Photos as AI Blackmail Threat Grows, Say Experts
UK experts warn that criminals are using generative AI to turn publicly posted pupil photos into child sexual abuse material and then extort schools for money. The Internet Watch Foundation identified a secondary‑school blackmail attempt involving 150 AI‑fabricated images, prompting...

Colleges Around the World See Web Outages After Vendor Hack
Instructure Inc., the operator of the Canvas learning platform, confirmed a cyberattack on May 1 that disrupted access for colleges worldwide. The breach caused web outages for students in the United States, Australia, and other regions, affecting test taking and grade...

Canvas Has Been Hacked, and Is Apparently Being Held for Ransom
Canvas, the cloud‑based LMS serving over 8,000 U.S. colleges—including all top‑ten institutions—has been seized by the hacker group Shinyhunters. The group posted a ransom note demanding a settlement by May 12, threatening to leak the data otherwise. Outages are reported nationwide,...

ShinyHunters Claims Nearly 9,000 Schools Affected by Canvas Data Breach
ShinyHunters, a notorious extortion group, says its recent breach of Instructure’s Canvas learning‑management system exposed data from nearly 9,000 schools, including elite universities such as Harvard and MIT. The hackers claim to have stolen several terabytes containing personal information of...

Opinion: K-12 Needs Deeper State-Vendor Collaboration
The 2025 K‑12 landscape was marked by a surge in cybersecurity breaches, funding volatility, and swings in classroom technology use, exposing flaws in the traditional transactional state‑vendor model. As 2026 begins, educators and policymakers argue that merely reacting to crises...

60% of MD5 Password Hashes Are Crackable In Under an Hour
Kaspersky researchers report that a single Nvidia RTX 5090 can crack 60% of MD5‑hashed passwords in under an hour, with 48% broken in under a minute. The study attributes the speed boost to both powerful GPUs and the predictability of real‑world...

OpenAI Makes Its Rival to Anthropic's Mythos More Widely Available to Cyber Defenders
OpenAI has launched a limited preview of GPT-5.5-Cyber, a less‑guarded version of its GPT-5.5 model, for vetted cyber‑defenders protecting critical infrastructure. Early testing shows the model performs on par with Anthropic’s Mythos in finding and exploiting software bugs, with Mythos...

Privacy and Accountability Can Coexist Onchain, Say Panelists at Consensus Miami
Panelists at CoinDesk's Consensus Miami argued that privacy and accountability can coexist on blockchain through a hybrid "intelligence layer." Moody's strategist Rajeev Bamra highlighted that institutional digital‑finance assets now total roughly $35 billion, growing 100‑150% in 18 months, yet remain a...

Ollama Vulnerability Highlights Danger of AI Frameworks with Unrestricted Access
Researchers at Cyera uncovered a critical flaw (CVE-2026-7482) in the popular Ollama AI framework that enables unauthenticated attackers to trigger an out‑of‑bounds heap read via a crafted GGUF file. The bug can leak process memory—including prompts, API keys, environment variables,...

J.P. Morgan Secures AI Agent Identity for Future Payments
J.P. Morgan Payments has partnered with Mirakl to build infrastructure for agentic commerce in an effort to radically transform the traditional payment rail. But as autonomous agents move from browsing to buying, they introduce some risks: processing untrusted inputs, accessing sensitive...

Secure Oracles and Bridges: Chainlink Sets New Industry Standard
Glad to see all the hard work that Chainlink has put into generating real security is being recognized as valuable by more and more teams in our industry. It seems that focusing on making the secure and reliable solution is...

Beyond the Inbox: Why Your Domain and Social Media Are the Next Front Lines
Email security alone no longer protects organizations as attackers pivot to brand impersonation. By hijacking subdomains, registering look‑alike domains and creating fake social‑media profiles, threat actors launch phishing and BEC campaigns that bypass SPF, DKIM and DMARC. Red Sift’s research...
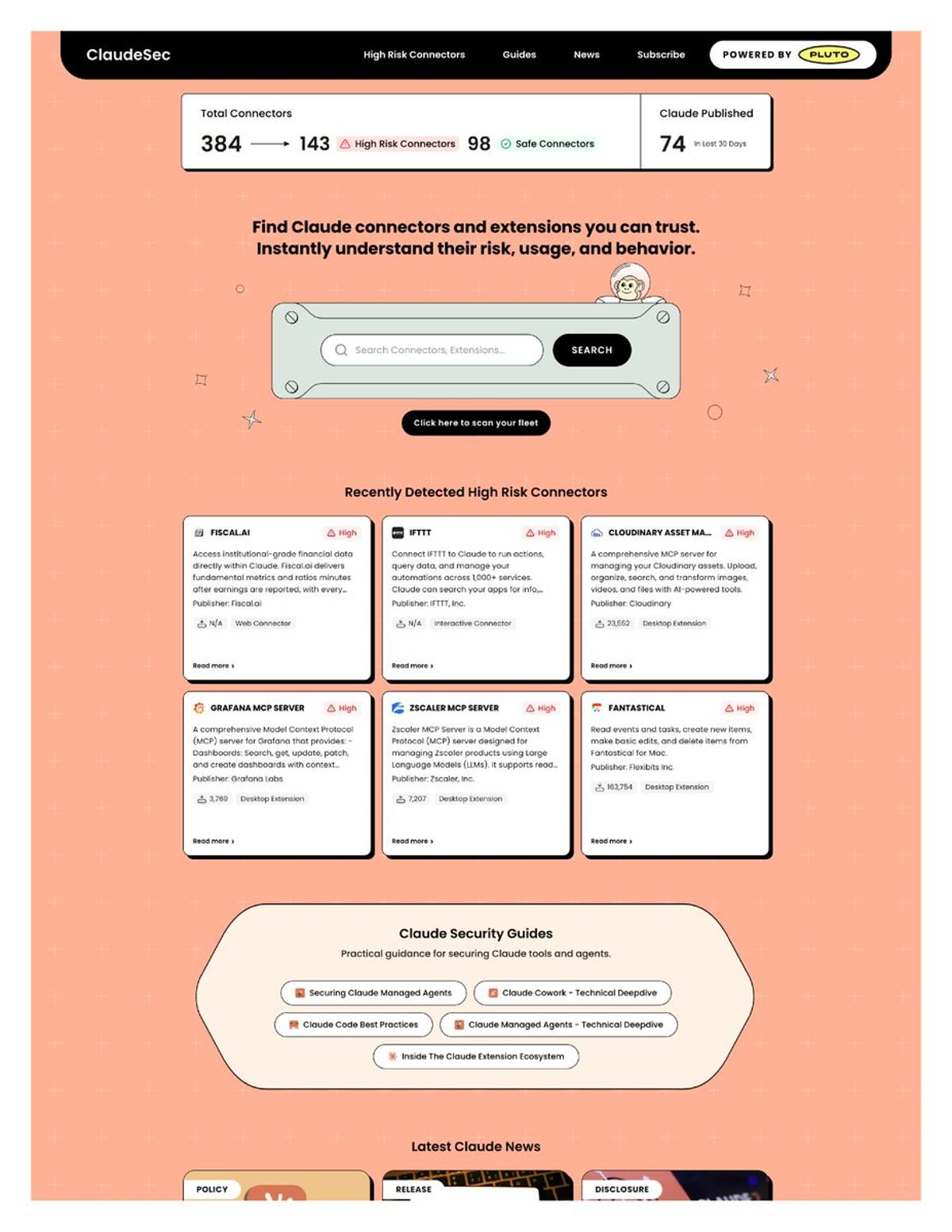
New Claude Connectors Flagged for Data Leak Risks
Anthropic just shipped 128 new Claude connectors in 30 days. Nobody is reviewing them. Pluto Security just launched ClaudeSec, a free database that flags which ones can leak your data, exfiltrate files, or hijack agent sessions. Here's what they found ↓ https://t.co/h1mWAoSFHT

Security Key to Agentic Economy; IronClaw Leads
Excited to work with FailSafe to bring AttackBench: a benchmark for red teaming agents. I believe that true agentic adoption and agentic economy is limited by security and that’s why IronClaw is focused on becoming the most secure (and private) agentic...

ABS Acquires RMC Global to Strengthen Cybersecurity, Risk Management Capabilities
ABS, through its affiliate ABSG Consulting, announced the acquisition of RMC Global, a specialist in industrial cybersecurity, risk management, and resiliency solutions. The deal merges RMC’s niche expertise with ABS Consulting’s scale, technical depth, and global resources, creating more integrated...
Adjust WhatsApp Settings for Better Privacy Abroad
WhatsApp is a great way to stay in touch with friends and family traveling abroad, but you do want to make a few changes in @WhatssApp for maximum privacy and security. Here's the rundown: https://t.co/pBNbgmlbVR #whatsapp #privacy #security https://t.co/JyZg1OaWpa

AI Success Depends on Robust QA and DevOps Maturity
RT 77% of orgs are confident in AI outputs? while many still lack secure CI/CD, automated audit trails, and even basic defect escape metrics. Your QA and DevOps maturity will make or break AI agents in production. #AI #DevOps #QA @Star_CIO ...

After Replacing TeamPCP Malware, 'PCPJack' Steals Cloud Secrets
SentinelLabs has identified PCPJack, a modular cloud‑native worm that first evicts the supply‑chain group TeamPCP before harvesting a wide range of cloud, container and cryptocurrency credentials. The malware’s bootstrap module establishes persistence, while the monitor script disguises activity and collects...
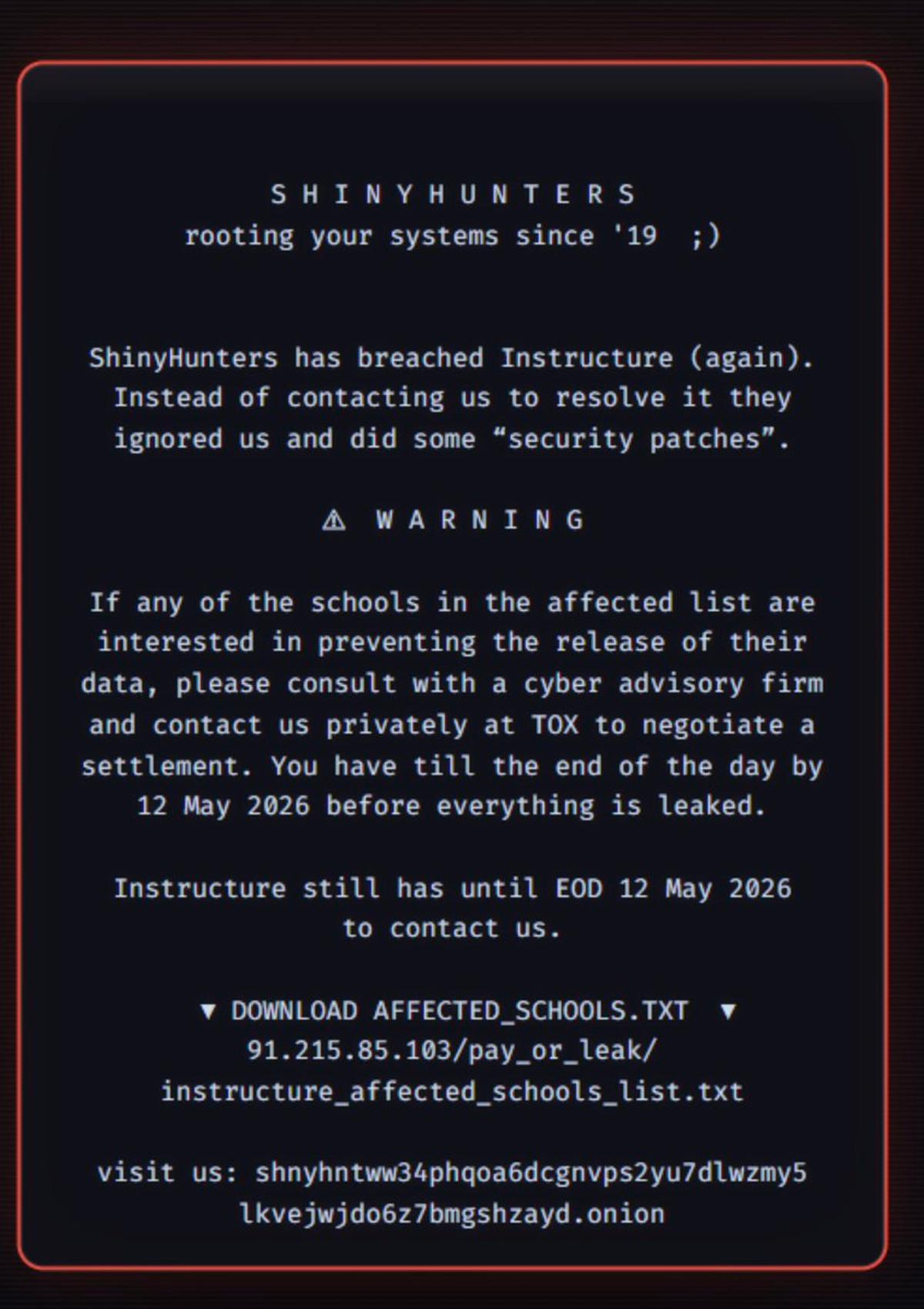
Canvas Ransomware Disrupts Finals, Threatens Student Data
Canvas, the tool teachers and students are using for finals right now, was hit w/ ransomware by (folks who claim to be) ShinyHunters. Lots of students/educators saying this is making finals studying/tests v hard (not even considering the amount of...

AI Could Secure Software by Eliminating All Vulnerabilities
Maybe powerful AI will favor the cyber defense. Vulnerabilities are finite in number, so if you can fix them all, maybe software just becomes much more secure.
How to Disable Google's Gemini in Chrome
Google has embedded a 4 GB Gemini Nano on‑device AI model into Chrome, enabling local scam detection and developer APIs. Users can now turn off the feature through Settings → System → On‑device AI, which stops further downloads and updates. If the model is manually deleted,...

LinkedIn Illegally Blocking Free Accounts From Seeing ‘Who’s Viewed Your Profile’ Data, Group Alleges
LinkedIn’s "Who’s Viewed Your Profile" feature, traditionally a premium‑only perk, is being challenged by the NOYB digital‑rights group in an Austrian court. NOYB argues the paywall breaches GDPR Article 15, which grants EU users unrestricted access to personal data via...