Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Disgraced US Gov Software Contractor Found Guilty of Database Destruction
A Virginia contractor, Sohaib Akhter, and his twin brother Muneeb were convicted of a coordinated attack that erased roughly 96 government databases within an hour after their termination from a software supplier serving 45 federal agencies. The deletions targeted Freedom of Information Act files, DHS production data, and sensitive investigative records, while the brothers also exfiltrated EEOC complaints and IRS tax information for hundreds of individuals. Prosecutors highlighted the use of AI prompts to erase system logs, and Sohaib faces additional firearms charges after a cache of rifles and ammunition was discovered. Muneeb remains awaiting trial, facing a potential 45‑year sentence.

Manual Updates Reveal Outdated Security Practices
"If your security strategy relies on a sysadmin logging into a server to run apt-get upgrade on a Tuesday morning, you aren't running a modern security program; you’re running a historical reenactment society." #overheard
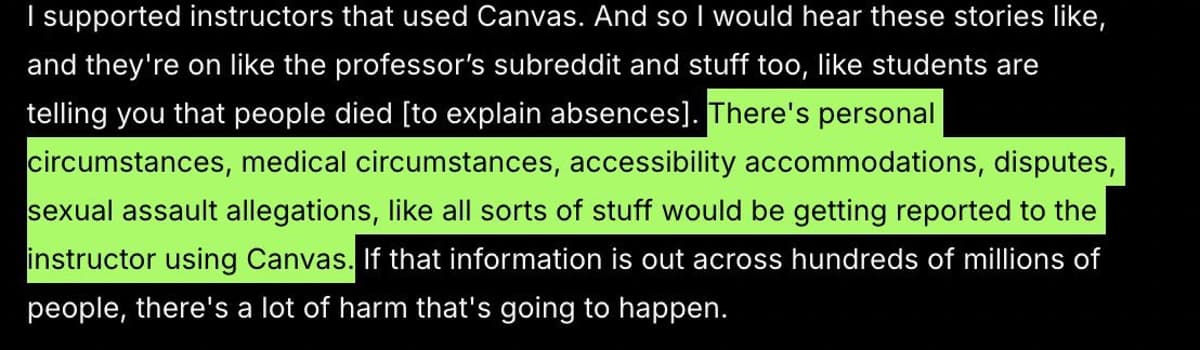
Canvas Breach Exposes Private Faculty‑student Disclosures
When they say “personal messages between faculty and students may be leaked” due to this breach, that sadly includes sensitive messages including medical situations, accessibility needs, and sexual assault allegations reported to the educator on Canvas 😞 https://t.co/mMGMtJC8mU

Meta Can See Your Instagram Messages Now, and It's Time to Stop Using It
Meta has removed end‑to‑end encryption from Instagram direct messages as of May 8, 2026, allowing the company to read and analyze message content. The change is justified by low adoption of encrypted chats and Meta’s desire to improve moderation of harmful activity....

Researcher’s Linux Vulnerability Disclosed Before Patch Available
A researcher shared their findings with Linux distro maintainers, but leaked before a patch was built. https://t.co/UMfIxI2WpM

Secure Your Flanks: CISO Strategies During Upgrades
#TimTalk - How can CISOs protect their “flanks” when they are most vulnerable during a security upgrade for example? with Zach Lewis https://t.co/pKVV0x2VFb via @DLAIgnite #SocialSelling #DigitalSelling #CyberSecurity #CyberSec #Ransomware #LockBit #LockBitRansomware #CyberAttack #DataBreach #Malware

Is 2026 the End of iMessage Work Group Chats?
Businesses relying on iMessage for internal communication face three critical risks: departing employees walk away with years of client data, legal disputes lack a retrievable audit trail, and disgruntled staff can retain access to confidential chats. iMessage was designed for...

US Defense Contractor Who Sold Hacking Tools to Russian Broker Ordered to Pay $10M to Former Employers
Former L3Harris executive Peter Williams was ordered to pay $10 million in restitution, on top of a prior $1.3 million judgment, after stealing and selling advanced hacking tools to Russian broker Operation Zero. Williams, an Australian‑born former intelligence officer, exploited his full access to...

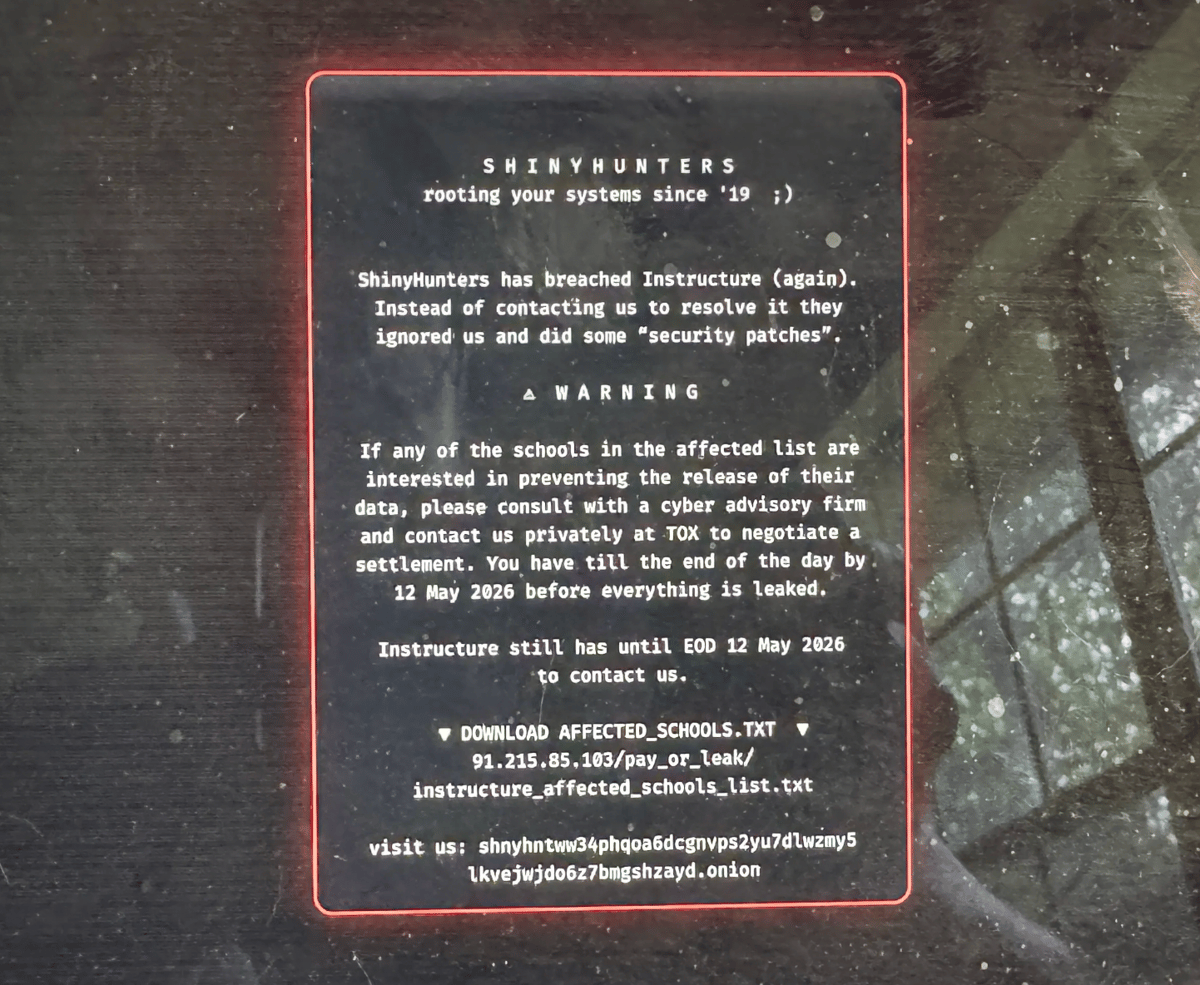
Platform Breach Downs Nearly 9,000 Colleges, Universities in the U.S.
Nearly 9,000 U.S. colleges and universities experienced a Canvas outage after the criminal group ShinyHunters claimed to have stolen user data. The attackers demanded a ransom by May 12, threatening to publish the information if unpaid. The disruption struck during a...

Turn Off Direct Send in Microsoft Exchange to Protect Yourself From Phishing
Microsoft Exchange’s Direct Send feature allows legacy devices to transmit email without authenticating, a convenience that can be weaponized by cybercriminals. Attackers harvest public staff content, use AI to mimic writing styles, and send phishing messages that appear legitimate, bypassing...

#243: Suricata in Modern Network Defence
Over the past decade, endpoint and cloud security have dominated defensive discussions, yet ransomware still depends on moving data across networks. Suricata has evolved into a high‑performance, multi‑threaded IDS/IPS platform that provides real‑time telemetry from Layer 3 through Layer 7, enabling detection...

Keeper Security Appoints Former ZoomInfo CRO Tim Strickland to Drive Revenue Growth
Keeper Security announced the hiring of Tim Strickland as its new chief revenue officer. The former ZoomInfo CRO brings over 20 years of SaaS revenue leadership, including steering ZoomInfo through an IPO and integrating multiple acquisitions. His mandate is to accelerate...

Integris Report Finds Law Firms Lag Behind Client Expectations on Tech, Security and AI Transparency
Integris' 2026 law‑firm trust report, based on 416 firm decision‑makers and 600 clients, reveals a widening gap between client expectations and firm capabilities. One‑third of firms cite budgeting and roadmap issues, nearly two‑thirds report email‑based breaches, and over a third...

Canvas Breach Cripples California Colleges, Exposes 280 Million Records
The learning management system Canvas was taken offline after the hacker group ShinyHunters announced it had stolen 280 million records from 8,809 schools. California’s UC and CSU campuses were among the hardest hit, leaving thousands of students unable to access coursework...

Some College Finals Delayed After Canvas Online Platform Hacked
Instructure Inc., the KKR‑owned operator of the Canvas learning platform, suffered a cyber‑attack that forced a temporary shutdown of the portal used by thousands of colleges worldwide. Hackers exploited a vulnerability in teacher accounts, gaining access to exam and grading...

Flipkart, Axis Bank, PayU Launch Biometric Card Authentication, Ditching SMS OTPs
Flipkart, Axis Bank and payment gateway PayU have deployed a fingerprint and Face ID based authentication system for card purchases on Flipkart, eliminating the need for SMS one‑time passwords. The device‑bound solution, built on Axis Bank’s Wibmo platform, aims to curb...

GitHub Deploys ‘Immune System’ to Guard AI Coding Agents on MCP Platform
GitHub announced a public‑preview immune system for its Model Context Protocol (MCP) server, integrating dependency scanning and secret detection directly into AI‑assisted development workflows. The move follows high‑profile incidents where over‑privileged AI agents caused data loss, highlighting the need for...

PCPJack Worm Hijacks Cloud Credentials and Erases TeamPCP Infections
Security researchers at SentinelLabs have uncovered PCPJack, a Linux‑based worm that steals credentials from exposed cloud services and actively removes any existing TeamPCP malware. The framework scans Docker, Kubernetes, Redis and other services, exfiltrates data to Telegram, and could fuel...

Bring AI Agents Into the Identity Fabric
Okta’s partner content warns that AI‑driven agents are emerging as a non‑human identity layer that expands the cyber‑attack surface. It calls for standardized AI lifecycle management to prevent machine‑speed threats from compromising agency missions. The piece positions the identity fabric...

Microsoft Warns of Sophisticated Phishing Campaign Heavily Targeting Health Care Organizations
Microsoft Threat Intelligence has identified a large‑scale, multistage phishing campaign that disproportionately targeted the U.S. health‑care sector. The operation sent “code of conduct” themed emails to more than 35,000 users across 13,000 organizations, using adversary‑in‑the‑middle techniques to hijack authentication tokens...

NightBeacon Delivers Faster Detection for Today and Tomorrow
This is real world stuff we are doing at #BinaryDefense. I've worked on NightBeacon for 12 months of my life, barely sleeping - to bring something to the industry that changes faster response times, faster detections - it's needed now, but...
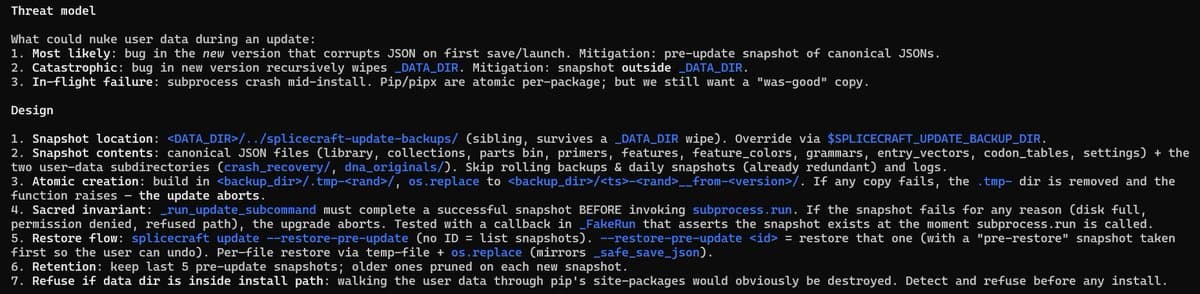
Ensuring Backups Prevent Patch‑induced Data Loss
Shoring up user data protections to prevent any future updates from nuking plasmid collections or other user input data. Backups and copies of everything. Hardened, sanitized, and secure. My nightmare scenario is for a user to tell me latest patch...
'The Biggest Student Data Privacy Disaster in History': Canvas Hack Shows the Danger of Centralized EdTech
On Thursday, ransomware group ShinyHunters breached Instructure’s Canvas platform, locking out millions of students and stealing data tied to more than 275 million users. The attackers claimed to have exfiltrated names, email addresses, student IDs and private messages, prompting a rapid,...

Canvas Breach Moves From Disclosure to Demand as ShinyHunters Sets May 12 Deadline
Extortion group ShinyHunters defaced Canvas login pages and set a May 12 deadline to leak data it claims to have exfiltrated from roughly 9,000 schools. The group alleges 275 million records and 3.65 TB of information, including names, emails, student IDs and messages,...

The Human Factor: Why AI-Powered SOCs Still Need People in Charge
Artificial intelligence is reshaping security operations centers (SOCs), especially when paired with managed detection and response (MDR) services. Sophos’ white paper shows its AI agents can trim alert noise by more than 60% and cut investigation time by up to...

A Practical Guide to Third-Party Cyber Risk Management
Ethixbase360 released an eBook titled “A Practical Guide to Third‑Party Cyber Risk Management,” highlighting how cyber threats now frequently originate from vendors, cloud services, and SaaS providers. The guide explains why incidents are rising, how attackers leverage a single supplier...

Your Instagram Conversations Won’t Be so Private Anymore
Effective May 8, 2026, Instagram Direct Messages lost end-to-end encryption, meaning Meta and any third party with access can read the content of private chats. The change was quietly noted in a help‑center update in March, with no public announcement...

Exec Ordered to Pay $10M for Selling Exploits to Russia
Trenchant exec, Peter Williams, who stole zero day exploits from his employer and sold them to a Russian buyer (known to sell exploits to the Russian government) has been ordered to pay $10 million in restitution to his former employer...

European Data Protection Authority Fines Yango €100M
The Dutch data‑protection authority (AP) fined Yango’s Dutch arm MLU B.V. €100 million (≈$109 million) for illegally sending driver and rider personal data to Russia. The joint probe with Norway and Finland revealed that sensitive information—including licence scans, addresses, payment details and...

Mobile Credentials Are an Operational Commitment. Evaluate Them Like One
Mobile credential programs on campuses transition from a technical procurement focus to an operational reality where the system is live the moment a student uses their phone. Unlike traditional enterprise rollouts, there is no soft‑launch window; failures surface immediately and...

5 Steps for Frontier AI Readiness
Frontier AI models such as Anthropic's Claude Mythos and OpenAI's GPT‑5.4‑Cyber can autonomously discover software flaws and generate exploits, compressing the gap between vulnerability discovery and attack. This acceleration forces a move from traditional vulnerability management to continuous exposure management,...

CIOs Must Prioritize Plugin Security Over AI Hype
A personal agent is only as safe as its plugins. In the wild, we're already seeing extensions act as conduits for malware. CIOs: It’s time to move from "opportunity" to "risk mitigation." 📉 https://t.co/5poCN8at4u #CIO #AI #Cybersecurity #RiskManagement #InfoSec

Privacy and Security Rules Extend to Paper Records
Health systems that revert to paper charts during electronic health record (EHR) downtime remain subject to HIPAA’s privacy and security rules, warns Polsinelli attorney Rebecca Romine. The guidance emphasizes that paper‑based protected health information (PHI) must be handled, stored, and...

The 7 Best Endpoint Encryption Software Choices in 2026
The article lists the seven top endpoint encryption solutions for 2026, from free open‑source tools like VeraCrypt to enterprise suites such as ESET PROTECT Complete. It evaluates each product on price, support, password‑manager integration, on‑the‑fly decryption, and enterprise‑grade encryption. Modern solutions...

Healthcare Cybersecurity Has Become an Operational Risk, Not Just a Security Function
Healthcare cybersecurity has moved from a back‑office IT issue to a core operational risk that directly affects patient care, revenue, and regulatory compliance. Ransomware and other attacks now disrupt electronic health records, scheduling, imaging and connected devices, forcing hospitals into...

Inside Department 4: Russia’s Secret School for Hackers
Investigative journalists uncovered Department 4, a secret faculty at Bauman Moscow State Technical University that serves as a direct recruitment pipeline for Russia’s GRU. The program trains elite students in offensive cyber techniques, including password cracking, virus development, and covert surveillance,...

Multiple Colleges Hit by Disruptions After Canvas Service Hack
Education technology provider Instructure, owner of the Canvas learning platform, suffered a cyber‑attack on May 1 that forced a temporary shutdown of teacher accounts across thousands of colleges, including Harvard, Princeton and Stanford. The breach, attributed to the ShinyHunters group, exploited...

In Other News: Train Hacker Arrested, PamDOORa Linux Backdoor, New CISA Director Frontrunner
The U.S. government is proposing a drastic cut to its critical‑vulnerability remediation window, moving from 14 days to just three days as AI‑driven exploits accelerate. Meanwhile, a new Linux backdoor called PamDOORa is being sold for $900, offering persistent SSH...

What's the Playbook for Continuity and Compliance when IT Systems Are Down
Rebecca Romine of Polsinelli outlines a practical playbook for health‑care providers to preserve patient privacy when cyberattacks force a switch from electronic health records to paper‑based workflows. She stresses pre‑approved paper‑form templates, strict access controls, and real‑time documentation of manual...
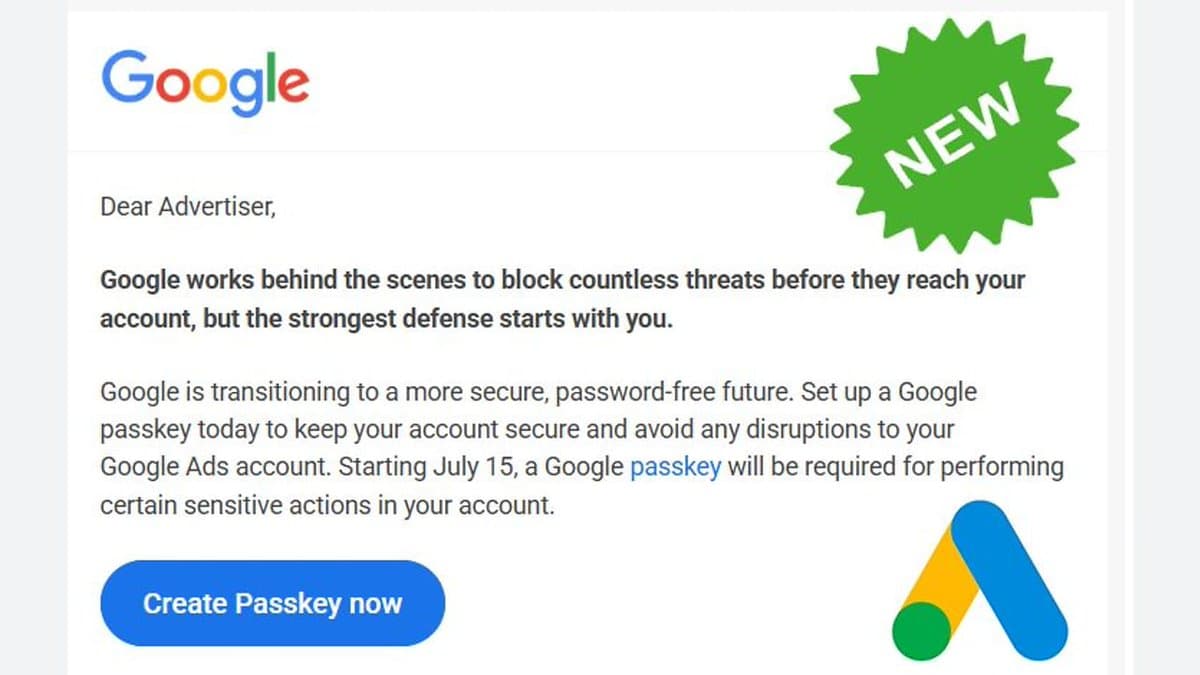
Google Ads Mandates Passkeys for Sensitive Actions July 15
Google Ads to require passkeys for certain sensitive actions starting on July 15 https://t.co/ERPAYU10eg https://t.co/q4LeLR7byl

Meta's Moltbook Acquisition Sparks New Privacy Concerns
Meta's acquisition of AI-agent social network Moltbook raises fresh data privacy concerns for billions of users. https://t.co/P6d9uHIyjh

'Dirty Frag' Linux Flaw One-Ups CopyFail with No Patches and Public Root Exploit
A new Linux privilege‑escalation vulnerability dubbed "Dirty Frag" has been disclosed without a CVE, patches, or coordinated mitigation. Security researcher Hyunwoo Kim revealed that the flaw chains a 2017 xfrm‑ESP kernel issue with a 2023 RxRPC bug, allowing unprivileged users...

Eyewitness Accounts and Recommended Actions to Counter AI’s Strain on Cyber Defense
Cooley partner Michael Egan warned that artificial intelligence is enabling attackers to develop exploits and ransomware faster, exposing many organizations to heightened risk. He highlighted a pervasive gap: firms often lack incident‑response plans for supply‑chain failures. Egan emphasized the need...

Pam Backdoor Targets Linux Systems to Steal SSH Credentials
Researchers at Group‑IB have identified a new Linux backdoor called Pam that abuses the Pluggable Authentication Modules (PAM) framework, specifically the pam_exec module, to capture SSH credentials. By inserting a malicious entry into /etc/pam.d/sshd, the backdoor runs a hidden script...

Kloudfuse 4.0 Launches AI‑Governed Observability and Workload Isolation for Enterprises
Kloudfuse announced the general availability of Kloudfuse 4.0, a platform that adds AI‑governed observability and independent scaling of ingestion, query and control planes. The upgrade targets enterprises facing tighter FIPS compliance, AI‑agent usage, and the need for cost‑effective telemetry at...

IMF Warns AI-Driven Cyber Attacks Could Trigger Funding Strains for Emerging-Market Banks
The International Monetary Fund warned that AI‑enhanced cyber attacks could cause extreme losses, strain funding and raise solvency concerns for banks and sovereign debt holders in emerging markets. The IMF’s blog highlighted the rapid diffusion of advanced models like Anthropic’s...

Secure Halo Flags Critical CVE-2026-40372 Flaw in Microsoft ASP.NET Core
Secure Halo has warned that a newly disclosed CVE‑2026‑40372 flaw in Microsoft’s ASP.NET Core DataProtection package (versions 10.0.0‑10.0.6) carries a 9.1 severity rating and can let unauthenticated attackers gain system‑level privileges on Linux and macOS. The firm urges immediate key‑ring...

Pro-Ukraine BO Team and Head Mare Hackers Appear to Team up in Attacks Against Russia
Pro‑Ukraine hacktivist groups BO Team and Head Mare appear to be coordinating cyber attacks against Russian and Belarusian entities, according to Kaspersky. The firms identified shared command‑and‑control infrastructure and overlapping malware toolsets, suggesting joint operations. BO Team, previously known for autonomous activity, now...

271 Bugs Found in Firefox, Zero Written by a Human Attacker. What This Means for the Future of Safe Code...
Mozilla’s Mythos AI, built by Anthropic, scanned Firefox and uncovered 271 security‑sensitive bugs, all originating from machine‑generated code. The previous scan with a general model found only 22 issues, highlighting the power of purpose‑built AI for vulnerability research. The findings...

Recorded Future Report Flags Quantum Risks to Encryption, Highlights $1.3T Market
Recorded Future has released a report that maps four emerging security risks posed by quantum computing, with a focus on the imminent threat to public‑key encryption and the growing “harvest now, decrypt later” (HNDL) activity. The paper also cites an...