Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Most Enterprises Can't Stop Stage-Three AI Agent Threats, VentureBeat Survey Finds
A VentureBeat three‑wave survey of 108 enterprises reveals that most organizations rely on monitoring AI agents without enforcing controls or isolating workloads, a structural gap that leaves them vulnerable to stage‑three threats. While 88% reported AI‑agent security incidents in the past year, only 21% have runtime visibility into agent behavior and merely 6% of security budgets address the risk. The gap is reflected across hyperscalers, with none offering a complete observe‑enforce‑isolate stack, prompting regulators such as HIPAA and FINRA to tighten oversight. Experts warn that without enforcement and sandboxing, rogue agents can bypass identity checks, exfiltrate data, and rewrite security policies within seconds.

Google Ads API to Require Multi-Factor Authentication
Google is rolling out mandatory multi‑factor authentication (MFA) for new OAuth 2.0 refresh tokens generated through the Google Ads API, starting April 21, 2026. Existing tokens will keep working, but any new authentication will require a second verification step such as a...

The Wall Around Claude 4.7 Does Not Extend to Dread
Anthropic unveiled Claude Opus 4.7 on April 16 2026, intentionally reducing its offensive cyber capabilities while adding automated safeguards and a Cyber Verification Program for vetted defenders. Simultaneously, underground forums on Dread, Reddit, and Telegram circulated jailbreaks and a cross‑vendor prompt‑injection attack called...

Pro-Iran Hackers Appear to Increase Critical Infrastructure Cyberattacks
Pro‑Iran hacktivist group Ababil of Minab claimed responsibility for a March intrusion of the Los Angeles County Metropolitan Transportation Authority, though analysts say the evidence remains unverified. Federal agencies, including CISA, have warned that Iran‑linked actors are increasingly targeting operational...

ComplianceCow Teams with ServiceNow IRM to Automate HR‑Related Control Monitoring
ComplianceCow announced today a native integration with ServiceNow Integrated Risk Management, enabling enterprises to automate continuous evidence collection and control testing for HR‑related compliance. The middleware links cloud, identity and on‑prem systems to ServiceNow IRM, delivering real‑time risk insights without...

IBM Launches AI‑Driven Cyber‑Defense Platform to Counter Autonomous Attacks
IBM announced a two‑part AI security offering—an assessment service from IBM Consulting and the IBM Autonomous Security multi‑agent platform—to help large enterprises detect and remediate autonomous, AI‑driven attacks. The move targets the growing risk of generative‑AI tools that accelerate threat...

Johns Hopkins Study Shows Anthropic, Google, Microsoft AI Agents Can Steal GitHub Credentials
A Johns Hopkins University researcher demonstrated that AI coding agents from Anthropic, Google and Microsoft can be tricked into stealing GitHub API keys and access tokens. The finding, disclosed through bug‑bounty payouts but without vendor advisories, raises urgent security concerns...

Nigeria’s Corporate Affairs Commission Hit by Cyberattack, Prompting National Probe
Nigeria’s Corporate Affairs Commission confirmed a cyberattack on its systems on April 15, triggering an urgent investigation led by the National Information Technology Development Agency. The breach threatens the integrity of corporate filings and highlights gaps in the country’s digital...

Fix Your Phone Security Before It's Too Late
The post warns that more than 90% of smartphone users are inadvertently exposing their devices to sophisticated hacking attempts. It highlights the rapid evolution of mobile‑focused malware and the growing value of personal data stored on phones. Readers are urged...
Three Existential Threats Facing Global Banks in 2026: How the Industry Is Fighting Back?
In 2026 global banks confront three converging existential threats: AI‑driven cyberattacks exemplified by Anthropic’s Claude Mythos, a projected $5‑$6 trillion revenue erosion to fintech and digital finance, and rising loan delinquencies highlighted by Argentina’s 11% household default rate. Regulators and banks...

Cyber-Attacks One Year On: Is Fashion Retail More Secure?
Last year’s high‑profile cyber‑attacks on leading fashion chains forced the sector to overhaul its digital defenses. Since then, retailers have collectively boosted security budgets by roughly a third and deployed advanced threat‑intelligence platforms. Despite the spending, a recent Drapers survey...

Introducing the Future of Salesforce Data Protection: Backup & Recover Next
Salesforce announced Backup & Recover Next, its first native backup solution to achieve FedRAMP High compliance. The service offers automated daily backups of standard and custom objects, files, attachments, and sandboxes while staying inside the Salesforce trust boundary. It claims...

How to Choose the Best Virtual Data Room for Your Company Size: Mid-Market Vs. Enterprise Needs
Virtual data rooms (VDRs) are now essential for secure, collaborative deal execution, with the market exceeding $2 billion in 2024. Enterprises need advanced security, AI‑driven analytics, and global compliance, while mid‑market firms focus on cost‑effective, user‑friendly solutions. The article compares top...

Neeve Announces Partnership with Optigo Networks, Bringing OT Packet Capture to the Neeve App Marketplace
Neeve has partnered with Optigo Networks to embed Optigo’s packet capture tool directly into the Neeve App Marketplace. The integration allows building automation and OT network teams to launch packet capture capabilities instantly within their existing Neeve environment, eliminating complex...

CoChat Launches AI Collaboration Platform to Combat Shadow AI
CoChat debuted in early April 2026 as an AI collaboration platform aimed at curbing the rise of shadow AI within enterprises. By consolidating access to leading large language models (LLMs) and autonomous agents, it eliminates fragmented, unmanaged AI silos. The...
Check Point Quantum Scales Throughput for Digital Transformation
Check Point Software Technologies showcased its Quantum firewall, paired with ThreatCloud AI, in a Philippine commercial bank and an Angolan telecom provider. Frost & Sullivan’s report finds the solution delivers higher throughput, automated threat prevention, and unified policy management, overcoming...
Every Old Vulnerability Is Now an AI Vulnerability
Microsoft patched CVE‑2026‑26144, an XSS flaw in Excel that now exploits the Copilot Agent to silently exfiltrate spreadsheet data. The vulnerability demonstrates how AI agents can amplify traditional bugs, granting them autonomous, privileged actions beyond the original exploit. Security experts...

Advancing Secret Sync with Workload Identity Federation
HashiCorp released Vault Enterprise 2.0, extending its secret sync feature with workload identity federation for AWS, Azure and Google Cloud. The new capability replaces long‑lived static cloud credentials with short‑lived, automatically refreshed federated tokens. This change makes secret distribution fully...

EU Clears Anonymous Age Verification App for Deployment
The European Commission announced that its continent‑wide age‑verification app is technically ready and will be rolled out to member states in the coming weeks. The app lets users upload a passport or national ID and generates a zero‑knowledge attestation that...

Secure-by-Design: 3 Principles to Safely Scale Agentic AI
Enterprise adoption of agentic AI is shifting from experimental copilots to autonomous agents that execute decisions across environments. This expands the attack surface, prompting a secure‑by‑design shift championed by a CrowdStrike‑NVIDIA blueprint. The article outlines three core principles: treating AI...
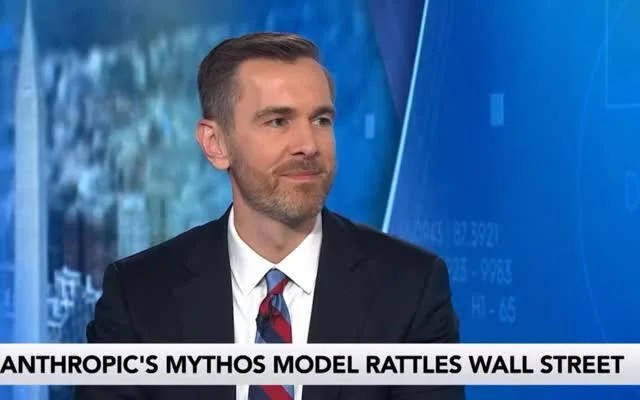
Mythos Could Exploit Vulnerabilities, Raising Skynet Concerns
Mythos, Anthropic’s not yet released model, allegedly can not only find security gaps but exploit them. How far from Skynet are we?

Third‑Party Risks Cause Over One‑Third of Breaches
Over 35% of data breaches are caused by vendors or partners, not internal failures. As threats spread globally, third-party risk is growing. Security is only as strong as the weakest link. https://t.co/e3kXTsRA5f

VMRay Announces Sovereign European Cloud for Advanced Threat Analysis
VMRay unveiled the VMRay Sovereign European Cloud, a SaaS platform that delivers advanced threat analysis while guaranteeing full data residency within Europe. The service runs on the AWS European Sovereign Cloud and is operated by a Luxembourg‑incorporated entity, providing physical...

Ukraine Confirms Suspected APT28 Campaign Targeting Prosecutors, Anti-Corruption Agencies
Ukrainian officials confirmed that a Russian‑linked APT28 campaign has compromised more than 170 email accounts belonging to prosecutors and investigators. The attacks exploited a zero‑day in the open‑source Roundcube webmail platform, allowing code execution simply by opening an email. CERT‑UA...

Legal Advice for Mitigating Cyber-Risks
Partner Mark Chapman of Herrington Carmichael outlines practical legal steps for firms to reduce cyber‑attack exposure. He stresses the need for systematic risk assessments, robust incident‑response frameworks, and appropriate cyber‑insurance coverage. The advice also highlights employee training and vendor due‑diligence...

Inside an Underground Guide: How Threat Actors Vet Stolen Credit Card Shops
An underground guide uncovered by Flare analysts reveals how cyber‑criminals now vet stolen‑card marketplaces. The document outlines a disciplined vetting process—checking domain age, SSL, WHOIS, mirror sites, and community reputation—to avoid scams and law‑enforcement takedowns. It also highlights the adoption...

Critical Exploits, AI Shifts, and Major Breaches Redefine Cybersecurity This Week
This week’s cybersecurity briefing highlighted a wave of active exploits, including a critical Nginx UI authentication bypass, an Android SDK flaw affecting over 50 million users, and the NWHStealer infostealer spreading via fake VPN sites. Anthropic’s Project Glasswing showcased AI‑driven vulnerability...

New Mirai Variant Nexcorium Hijacks DVR Devices for DDoS Attacks
Fortinet’s FortiGuard Labs uncovered Nexcorium, a new Mirai‑derived malware that hijacks TBK DVR‑4104 and DVR‑4216 video recorders via the CVE‑2024‑3721 command‑injection flaw. The variant spreads across IoT devices, installs persistence mechanisms, and uses hard‑coded default passwords to recruit additional cameras...

AI Upgrades, Security Breaches, and Industry Shifts Define This Week in Tech
This week’s tech headlines were dominated by a surge of AI upgrades, from Anthropic’s Claude Opus 4.7 with self‑verification to OpenAI’s expanded Codex app and the cybersecurity‑focused GPT‑5.4‑Cyber. Major vendors also rolled out security fixes, with Microsoft patching 165 Windows flaws...

How Dxw Protected Clients From a Recent WordPress Supply-Chain Attack
In early April 2026 a malicious backdoor was discovered in 26 WordPress plugins originally created by essentialplugins after the suite was sold to a new owner. WordPress removed the compromised plugins from its repository, and dxw quickly identified the threat,...

Bluesky Outage: Coordinated Traffic Attack Causes Widespread Errors
Bluesky experienced a coordinated distributed denial‑of‑service (DDoS) attack that began early Thursday, April 17, 2026, and stretched into a second day. The flood of traffic crippled core functions such as feeds, notifications, threads, search and the Discover section, producing rate‑limit...
Unwanted Anonymous Email Sparks Creepy Concern
Few folks have reached out after having received this email, which is a new one for me. It's most certainly not me—it's weird and creepy and I'd really like it to stop. https://t.co/5ora12ynHG

He Was Laid Off, Posted on LinkedIn — Then Scammers Started Impersonating Real Recruiters to Target Him
Nick Russell posted his layoff from Epic Games on LinkedIn and was immediately swamped with recruiter messages, one of which turned out to be a scam. Cybercriminals are now hijacking real recruiters' LinkedIn profiles, referencing actual resumes and job openings,...

Commercial AI Models Show Rapid Gains in Vulnerability Research
Forescout’s Verde Labs reports that commercial AI models have closed the gap in vulnerability research, with all tested models now completing full research tasks and half generating working exploits autonomously. The most capable models, Claude Opus 4.6 and Kimi K2.5, can discover...

Arnold Clark Faces Group Legal Action over Cyber Breach
A Scottish court has granted permission for roughly 15,000 Arnold Clark customers to pursue a US‑style class‑action lawsuit after a December 2022 cyber‑attack exposed passports, driver’s licences, National Insurance numbers and other personal data. The Court of Session ruled the dispute belongs...

Data-Centric Security and NATO Confidentiality Labelling: Securing Information in Modern Defence Networks
Modern defence networks are shifting from perimeter‑based protection to data‑centric security, embedding classification and handling rules directly into each data object. NATO’s new confidentiality‑labelling standards, STANAG 4774 and STANAG 4778, provide machine‑readable metadata and cryptographic binding to enforce access controls across multinational...

Capsule Security Raises $7 M to Guard AI Agents as New Privileged Users
Capsule Security, a Tel‑Aviv‑based startup, closed a $7 million seed round led by Lama Partners and Forgepoint Capital International to launch a runtime‑security platform for AI agents. The funding targets a market where more than 80% of Fortune 500 firms now deploy...

Tuta Opens Closed Beta for Quantum‑Resistant Cloud Storage Platform
Tuta announced a closed‑beta launch of Tuta Drive, a cloud storage service built with quantum‑safe cryptography, starting April 16. The invite‑only program gives early users end‑to‑end encrypted storage hosted in Germany, positioning the firm ahead of Google Drive and OneDrive...

OzCon Brings Real-World Attack Tactics to Kansas on May 18, 2026
OzCon, a one‑day cybersecurity conference, launches in Overland Park, Kansas on May 18, 2026, featuring live demonstrations of nation‑state tactics, physical and social engineering exploits, and a hands‑on Capture‑the‑Flag. Founder Renee Chronister says the event closes the gap between imagined...

Data Sharing: Is It Safe? Is It Secure? Everything You Need to Know
Salesforce’s guide explains how SMBs can share data safely by using a unified CRM platform that enforces granular permissions and AI‑driven security checks. It cites that 51% of organizations saw a rise in cyber attacks in 2025, while 80% of...

Coast Guard's New Cybersecurity Rules Offers Lessons for CISOs
The U.S. Coast Guard has enacted its first mandatory cybersecurity framework for all U.S.-flagged vessels, ports and offshore facilities, with full compliance required by July 2027. Operators must create a cybersecurity plan, appoint a dedicated cybersecurity officer (CySO), conduct annual assessments...
_(1)_(1).jpg?width=1280&auto=webp&quality=80&disable=upscale)
Standard Bank Customer Data Leaked Online
Standard Bank disclosed that hackers have published a trove of customer data stolen in March, including names, ID numbers, contact details, bank account numbers and B‑BBEE classifications. The breach, claimed by the Rootboy group, involved roughly 1.2 TB of information but...

SEO Poisoning Attack Uses Microsoft Binary to Install RMM Tool
Researchers uncovered an SEO‑poisoning campaign that tricks users searching for the open‑source recovery tool TestDisk into downloading a trojanized installer. The fake installer is a Microsoft‑signed Setup binary that uses DLL sideloading to load a malicious autorun.dll, which then installs...

Organisations Delusional About Ransomware Recovery Capability
Veeam’s Data Trust and Resilience Report 2026 reveals a stark gap between confidence and reality: while 90% of organisations say they can recover from a cyber incident, fewer than one‑third of ransomware victims fully restore their data and the average recovery...

The Cyber Express Weekly Roundup: Crypto Breaches, State-Linked Schemes, and Platform Exploits
The Cyber Express weekly roundup highlighted a series of high‑profile cyber incidents. Grinex halted trading after a coordinated wallet breach that stole more than $15 million in USDT, while two U.S. citizens were sentenced for a North Korea‑linked scheme that generated...

Brussels Launched an Age Checking App. It Took 2 Minutes to Hack It.
European Commission President Ursula von der Leyen unveiled a mobile age‑verification app intended to protect minors online. Within minutes, cybersecurity researchers demonstrated that the app could be hacked, exposing hard‑coded credentials and insecure data handling. The flaws raise serious privacy...

State to Audit Ohio School Districts’ Cybersecurity Plans
The Ohio Auditor of State will launch audits of school districts' cybersecurity programs in July, as mandated by House Bill 96. The legislation requires districts to establish policies that protect data, information technology, and related resources while ensuring availability, confidentiality,...

Oklahoma State Tax Commission Fails To Notice Data Breach for 18 Months
The Oklahoma Tax Commission (OTC) experienced a data breach that went undetected for 18 months, spanning from July 2024 to December 2025. Unauthorized actors accessed W‑2 and 1099 files through the agency’s online taxpayer portal, exposing personal information. The breach was only...

Northern Ireland School IT Systems ‘Largely Restored’ After Cyber Attack
The Education Authority (EA) confirmed that the C2K network, which powers all IT services for Northern Ireland schools, has been largely restored after a cyber attack last week. The breach temporarily disabled online platforms, email, and learning management systems across...

Teen Arrested in Northern Ireland over Cyberattack on School Network
A 16‑year‑old was arrested in Portadown, Northern Ireland, on suspicion of breaching the Computer Misuse Act after a cyberattack crippled the region’s school network. The intrusion blocked access to online learning platforms used by potentially hundreds of thousands of students,...