Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Security Update: Retiring Weak TLS Cipher Suites
Zoho Corp announced that it will retire all weak TLS cipher suites across its data centers, with the change taking effect on June 30, 2026. Going forward, only strong TLS 1.2 and TLS 1.3 suites such as ECDHE‑ECDSA and CHACHA20‑POLY1305 will be supported. The company provides a public test endpoint for customers to verify their browsers or API clients are using approved ciphers. Organizations using outdated clients must upgrade before the deadline to maintain uninterrupted access to Zoho services.

Webinar: From Phishing to Fallout — Why MSPs Must Rethink Both Security and Recovery
BleepingComputer will host a live webinar on May 14, 2026 featuring Kaseya experts to discuss why managed service providers (MSPs) must align security and recovery strategies. The session highlights the rise of AI‑driven phishing, business‑email compromise, and targeted ransomware that...
Team Cymru Launches Total Insights Feed to Replace Legacy Threat Intelligence Lists
Team Cymru Inc. launched Total Insights Feed, a unified threat‑intelligence platform that replaces traditional indicator‑list feeds with machine‑actionable, scored data across the entire internet. The service evaluates over 57 million IP addresses and 400 million domains each day, assigning 0‑to‑100 risk scores...

Veeam Report Reveals a Market-Wide Shift From Recovery Confidence to Proven Data Resilience Amid Ransomware Threats and AI Adoption
Veeam’s Data Trust and Resilience Report 2026, based on more than 900 senior IT and security leaders, shows a stark gap between confidence and reality: while 90% of organizations believe they can recover from a cyber incident, only 28% fully recover...

New Vodafone Research Highlights Growing Mobile Devices Security Concerns Among Irish SMEs
Vodafone’s latest Business Cybersecurity Report shows that 70% of Irish SMEs are increasingly worried about mobile‑device attacks, yet more than 40% let employees access corporate resources on personal phones without dedicated security controls. Mobile‑based threats now represent over 42% of...

In Other News: Satellite Cybersecurity Act, $90K Chrome Flaw, Teen Hacker Arrested
The Senate advanced the bipartisan Satellite Cybersecurity Act of 2025, directing the Commerce Department to create a central hub for satellite security best practices as half of commercial satellite signals remain unencrypted. Law enforcement agencies dismantled the W3LL phishing‑as‑a‑service operation...

Another Microsoft Defender Privilege Escalation Bug Emerges Days After Patch
Researchers have disclosed a new local privilege escalation exploit called “RedSun” that abuses Microsoft Defender’s handling of cloud‑tagged files to rewrite protected system binaries and gain SYSTEM rights. The proof‑of‑concept works on Windows 10, Windows 11 and Windows Server 2019+...

Embrace Soft Forks Now to Prepare Bitcoin for Quantum Threat
The most important thing for Bitcoin community to get ready for addressing the quantum threat is taking head out of sand when it comes to soft forks and start embracing them. It'll be a big change to get post quantum, so...
DDoS-For-Hire Services Disrupted by International Police Action in ‘Operation PowerOff’
Operation PowerOff, a coordinated law‑enforcement effort across 21 nations, dismantled the infrastructure behind DDoS‑for‑hire services. Authorities seized 53 domains, removed over 100 URLs, and confiscated databases containing more than three million criminal user accounts. The operation led to four arrests...
Tycoon 2FA Is Down, but Not Out – Researchers Warn the Phishing as a Service Operation Is Still a Huge...
Security researchers say Tycoon 2FA attacks remain a major threat despite a law‑enforcement takedown last month. Incidents fell 77% but still top two million per month, with the service once targeting over 500,000 organizations monthly through an adversary‑in‑the‑middle proxy that stole MFA...
Mythos and Cybersecurity
Anthropic unveiled Claude Mythos Preview, an AI that autonomously discovers and exploits software vulnerabilities, but deemed too risky for public release. Access is limited to roughly 50 critical‑infrastructure firms through Project Glasswing, including Microsoft, Apple, AWS and CrowdStrike. The model...

SAPS Medical Aid Scheme Probes Potential Data Breach
Polmed, the medical aid scheme for South African Police Service members, is investigating a suspected data breach after a threat actor issued a ransom demand on March 25. The scheme has engaged independent cyber‑security and forensic specialists and reported the...
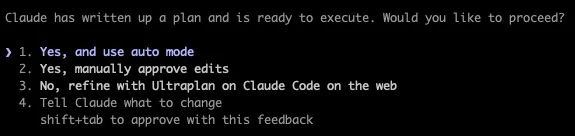
Critical Permissions Should Never Be Auto‑Approved by LLMs
@boris_cherny Is there a way to get approve and auto accept edits back? I work on database systems my environment has very critical permissions that I just don't ever want an LLM to be able to use by itself regardless of...

Google Blocks 8.3B Policy-Violating Ads in 2025, Launches Android 17 Privacy Overhaul
Google announced that in 2025 it blocked or removed 8.3 billion policy‑violating ads and suspended 24.9 million accounts worldwide. At the same time it rolled out Android 17, which replaces the broad READ_CONTACTS permission with a granular Contact Picker and adds a one‑time...

As AI-Driven Fraud Grows More Sophisticated, Advanced Digital Defense Becomes Essential
TransUnion’s H1 2026 Top Fraud Trends report warns that AI‑driven scams are becoming more sophisticated, even as overall digital‑fraud rates dip. One in six U.S. consumers reported losing a median $2,307, with stolen‑card and fraudulent‑charge schemes accounting for a third of...

FBI and CISA Warn of Russian-Backed Phishing Campaigns Targeting Private Messaging Apps
The FBI and the Cybersecurity and Infrastructure Security Agency (CISA) released a joint advisory this week warning that Russian intelligence‑linked hackers are conducting large‑scale phishing campaigns against private messaging apps. The attacks aim at government officials, military personnel and journalists,...

LMA Survey Shows 93% of Lloyd’s Firms Adopt AI Frameworks in One Year
The Lloyd’s Market Association reports that 93% of firms across the Lloyd’s market now have or are building formal AI frameworks, up from half a year ago. The shift, driven by generative AI tools, emphasizes governance, data security and human...

Google Agrees to $135 Million Android Data‑harvesting Settlement
Google has agreed to pay $135 million to resolve a class‑action lawsuit accusing it of harvesting data from Android devices without consent. The settlement, pending final court approval on June 23, also forces Google to revise its Play Store terms and give...

Trader Joe’s Pays $7.4 M to Settle Class Action Over Card‑Info Printed on Receipts
Trader Joe’s has agreed to a $7.4 million class‑action settlement for printing the first six and last four digits of credit‑card numbers on receipts in 2019. The deal, which could pay roughly $102 per eligible shopper, underscores heightened scrutiny of payment‑data handling...

Paramount+ Film Leak Exposes Security Gaps, Sparks Cybersecurity Scrutiny
A hacker known as @ImStillDissin posted the entire "Legend of Aang: The Last Airbender" movie online, six months before its Paramount+ debut. The leak, traced to a compromised email chain and a 4chan distribution, has forced Paramount to launch an...

Palo Alto’s Helmut Reisinger Sees a Cyber Sea Change Ahead as AI Advances
Palo Alto Networks is deepening its AI‑centric security push by joining Anthropic’s Project Glasswing, an exclusive initiative that uses Claude Mythos to uncover zero‑day vulnerabilities. The company has accelerated its platformization strategy through recent acquisitions—Protect AI, Chronosphere and the soon‑to‑close...

Kuwait Banks Deploy Real-Time War Room to Fight Growing Cyber Fraud Threats
Kuwait’s banking sector has launched a virtual war room that connects banks, the Central Bank, the Ministry of Interior and the Public Prosecution in real time. The platform instantly flags suspicious transactions, halts fund movement and initiates legal action, shifting...

Orange Rag Legal Tech Clinic: “Assume You Will Be Breached” – What Law Firms Must Prioritise Now on Cyber Risk
Legal tech expert Matthew Stringer urges law firms to assume they will be breached, emphasizing that phishing, ransomware and supply‑chain compromises are now routine threats. He highlights the sector's exposure due to valuable client data, time‑critical operations and sophisticated attackers....

GitLab 18.11 Brings Agentic AI to Security Fixes, CI Pipelines, and Delivery Analytics
GitLab unveiled version 18.11, extending its agentic AI across security remediation, CI pipeline creation, and delivery analytics. The GA Agentic SAST Vulnerability Resolution automatically generates fixes for true‑positive findings and opens merge requests with confidence scores. Two new agents—CI Expert...

‘It’s the Vibe’: Court Brawl Hinges on Alleged Industrial-Scale Data Hack
Australia's property data duopoly—CoreLogic (rebranded as Cotality) and Hubexo—has entered a Federal Court showdown over alleged large‑scale data theft. Hubexo claims Corelogic used bots and third‑party affiliates to scrape over 150,000 construction project records from Hubexo’s LeadManager service between 2016...
New CGrabber and Direct-Sys Malware Spread Through GitHub ZIP Files
Cyderes uncovered a sophisticated multi‑stage campaign that distributes new malware families—Direct‑Sys Loader and CGrabber Stealer—through ZIP files hosted on GitHub. The loader leverages DLL sideloading and direct syscalls to bypass antivirus and sandbox checks, while the stealer harvests passwords, crypto‑wallet...

Adumo Payment Tech Exposed, Hackers Offer Data for $7 000
Lesaka-owned Adumo, South Africa’s largest independent payments processor, suffered a cyber intrusion that exposed a 14‑GB technical database and source code, listed for $7,000 on a dark‑web marketplace. The breach involved 15,546 files but, according to the company, no consumer...

That Data Breach Alert Might Be a Trap
Data‑breach notifications have exploded, with over 280 million alerts sent in the U.S. last year and daily European incidents rising 22 % in 2025. Cybercriminals are exploiting this flood by sending fake breach alerts that mimic real notices, often using AI‑generated content...

Weaponized CVE-2026-39987 Pushes Blockchain Backdoor Through Hugging Face
Attackers are weaponizing CVE‑2026‑39987, a pre‑auth remote code execution flaw in the Marimo Python notebook platform, to drop a blockchain‑backed NKAbuse variant. By exploiting the vulnerability within ten hours of disclosure, they gain shell access, harvest environment variables, and pivot...
Microsoft: Some Windows Servers Enter Reboot Loops After April Patches
Microsoft confirmed that certain Windows domain controllers using Privileged Access Management enter reboot loops after installing the April 2026 security update KB5082063. The LSASS crashes cause repeated restarts, disabling authentication and potentially taking the entire domain offline. Affected operating systems include...

DNB Update on Reporting of Major ICT-Related Incidents Under DORA
The Dutch Central Bank (DNB) announced changes to DORA reporting for major ICT‑related incidents, adding a validation step that checks submissions against technical requirements. Effective mid‑April 2026, institutions will receive feedback highlighting unmet criteria. Warnings can be corrected in the...

U.S. CISA Adds a Flaw in Apache ActiveMQ to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added Apache ActiveMQ’s critical CVE‑2026‑34197 to its Known Exploited Vulnerabilities (KEV) catalog. The flaw, scoring 8.8 on the CVSS scale, lets an authenticated attacker exploit the Jolokia JMX‑HTTP bridge to load a...

Cursor AI Vulnerability Exposed Developer Devices
Security firm Straiker uncovered a critical vulnerability, dubbed NomShub, in the Cursor AI coding assistant. The flaw combines indirect prompt injection with a sandbox‑escape that lets attackers write files and hijack the editor’s Azure‑based remote tunnel, granting persistent shell access...

Man Gets 30 Months for Selling Thousands of Hacked DraftKings Accounts
Kamerin Stokes, a 23‑year‑old from Memphis, was sentenced to 30 months in federal prison for operating a fraud shop that sold access to tens of thousands of hacked DraftKings accounts. The accounts were compromised in a November 2022 credential‑stuffing attack...

Never Share Passwords in DMs—Verify Sender First
Twitter or X is fun but just for house keeping and safety rules, never put your password into something other than to log into the platform you need to access. Any DM message that asks you to input password, even if...
Prepare for Quantum Threats Now, Not on Q-Day
Post-Quantum Readiness Starts Long Before Q-Day by Etay Maor @Forbes Learn more: https://t.co/7bXzGooAsr #EmergingTech #Innovation #Technology https://t.co/fk6CZ8LQRE

Protecting Information at Work: Actionable Strategies for All Teams
Data protection has moved beyond the IT department to become a shared responsibility across every team and workflow. Simple, low‑cost habits—such as locking screens, using strong passwords, and shredding physical documents—can dramatically lower breach risk. Clear, jargon‑free policies and a...

AI Overwhelms Volunteers, Echoing Past Cybersecurity Struggles
12 years ago I wrote how the internet is being protected by two guys named Steve. Today, the situation isn't all that different, except those handful of volunteers are being swamped by AI systems finding holes in our digital systems....

$15M Grinex Hack Forces Trading Halt After Major Crypto Wallet Breach
Kyrgyzstan‑based crypto exchange Grinex halted all trading after hackers breached its hot‑wallet infrastructure and stole roughly $15 million in USDT, equivalent to about 1 billion rubles. The attackers rapidly moved the stolen tokens across Ethereum and Tron, consolidating the proceeds into a...

Recently Leaked Windows Zero-Days Now Exploited in Attacks
Threat actors are actively exploiting three newly disclosed Windows vulnerabilities after researcher “Chaotic Eclipse” published proof‑of‑concept code. The flaws—BlueHammer, RedSun and UnDefend—target Microsoft Defender, enabling attackers to gain SYSTEM or elevated admin rights. Huntress Labs confirmed real‑world use of all...

AI Tools Empower New Wave of Bank Hackers
Forewarned is fore armed. New level of hacking of banks could come from these AI advances. 👉Cops & robbers when the robbers get a new tool. https://t.co/GKklqa2Kai

Russian GRU Cyber Campaign Targets Western Logistics Firms Supporting Ukraine
A joint cybersecurity advisory has identified a sustained Russian GRU operation, attributed to Unit 26165 (APT28/Fancy Bear), that has been targeting Western logistics firms and technology providers supporting Ukraine since early 2022. The campaign leverages credential‑guessing, spear‑phishing, and weaponized CVEs such as...
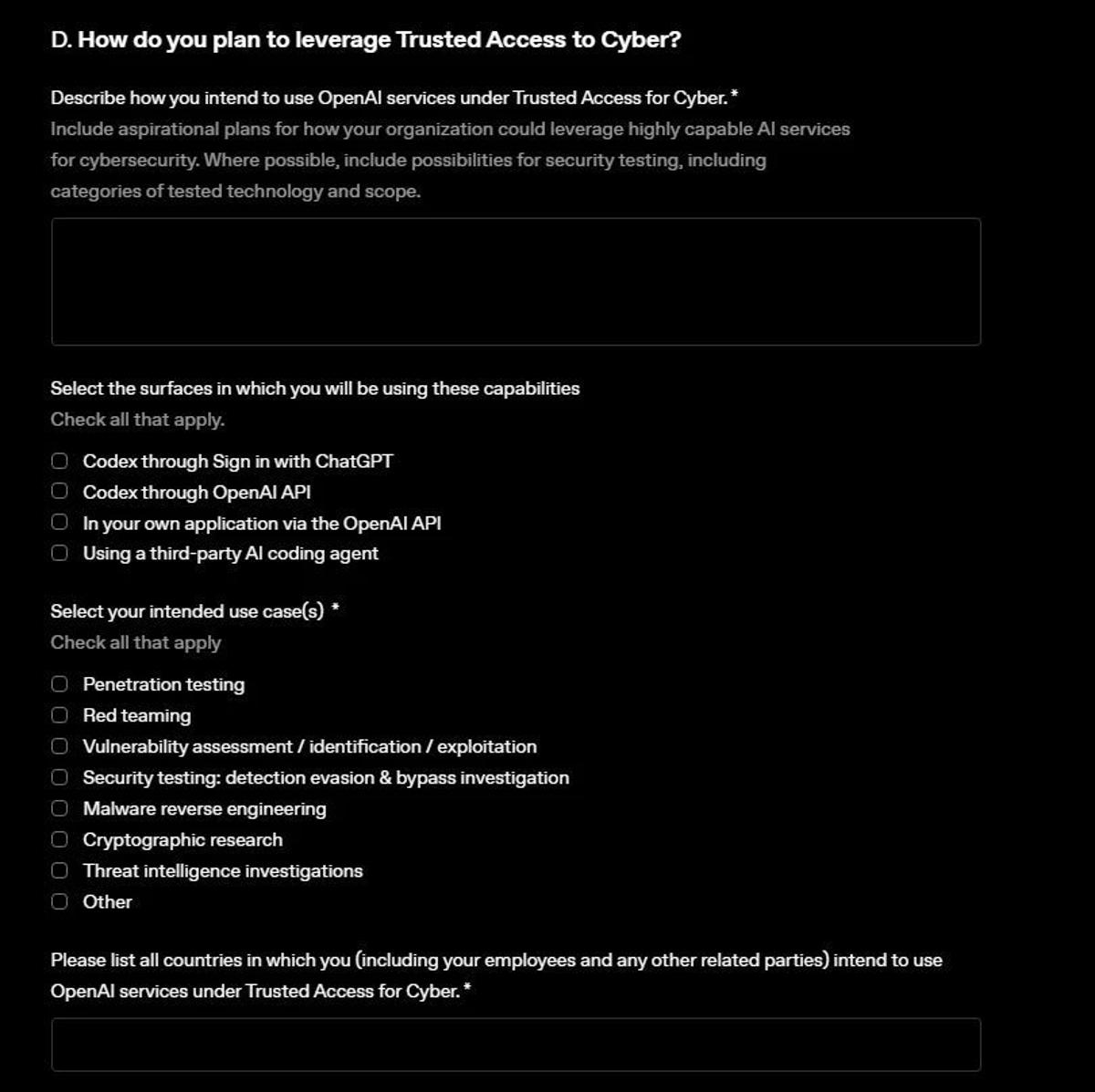
OpenAI Launches GPT‑5.4‑Cyber via Expanded Trusted Access
.@OpenAI releases GPT-5.4-Cyber, beefed-up Trusted Access for Cyber program https://t.co/Cqe6QG6I3Z OpenAI released GPT-5.4-Cyber, a model that will be released to select participants in a beefed-up Trusted Access for Cyber (TAC) program. https://t.co/pvHgkQtziD

Apple AirTag Tracking Can Be Misled by Replayed Bluetooth Signals
Apple’s Find My network uses Bluetooth Low Energy signals from AirTags to report locations via nearby Apple devices. Security researchers demonstrated a relay attack that captures an AirTag’s BLE advertisements, replays them from a different location, and injects false location data...

Claude Mythos Preview Demonstrates Advanced Cybersecurity Capabilities
Anthropic’s Claude Mythos Preview, released on April 7, was evaluated by the Government’s AI Security Institute (AISI). In capture‑the‑flag challenges it solved expert‑level tasks 73% of the time, the first AI to achieve that benchmark. It also completed three of ten...

Ising Models Redefine Quantum Error Correction
NVIDIA unveiled Ising, the first open‑source AI model suite built for quantum computing, on April 14‑15, 2026. The family includes a 35‑billion‑parameter vision‑language model that shrinks quantum‑processor calibration from days to hours, and a 3‑D CNN decoder that speeds error‑correction...

SBOM for OT: Can We Actually Do It?
The piece examines how Software Bill of Materials (SBOM) can be applied to operational technology (OT) environments, where opaque firmware, strict change‑control processes, and legacy systems make transparency challenging. It argues that SBOM should be treated as an operational‑risk workflow...

Voyager and IBM Demonstrate Post-Quantum Security on the International Space Station
Voyager Space and IBM have demonstrated a post‑quantum secured link between Earth and the International Space Station using Voyager’s Space Edge™ micro‑datacenter and IBM’s Quantum Safe Remediator. The system upgrades legacy encryption through a software proxy that translates to NIST‑standardized...
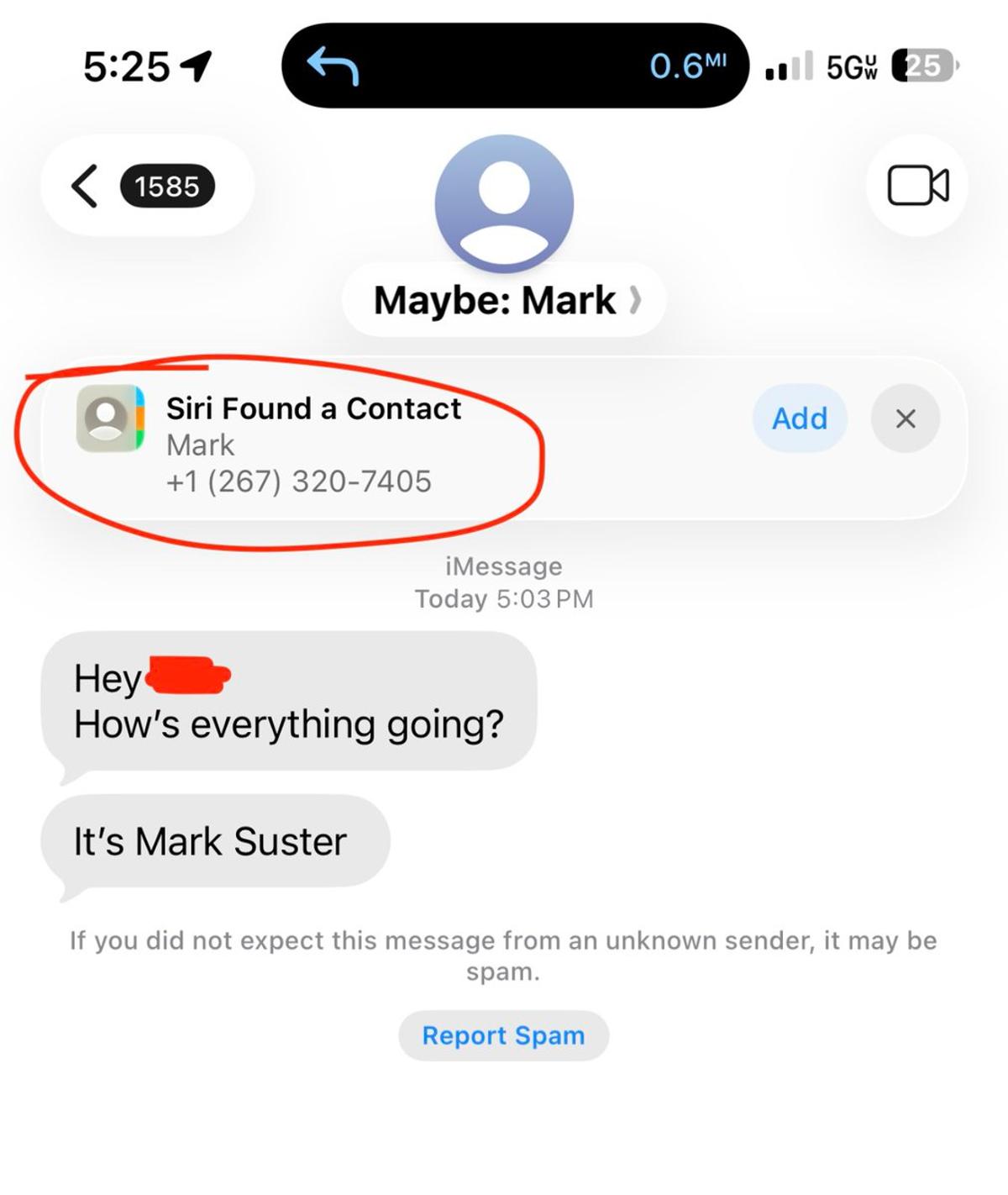
Phishing Attacks Now Pivot to Crypto Scam Pitches
Not me. Phishing. Apparently next step is they will pitch you a crypto scheme https://t.co/L4QDjDF1BH

Phishing Tactics Shift From Freebies to Political Pitches
Evolution of phishing scams: -“Click here to redeem a free iPhone” -“This is USPS. We’re holding your package” -“Vote for me to co-host a podcast”