Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

The Real Cost of a Data Breach for Small Businesses & How to Prevent
Small businesses face a disproportionate cyber threat, with roughly one‑third hit by attacks in 2023. Microsoft estimates the average breach cost for an SMB at $254,000, including $77,957 in direct response expenses and $20,623 in regulatory fines. Indirect losses—downtime, customer churn, and reputational damage—can push total impact beyond $1 million. The article outlines layered defenses such as multi‑factor authentication, employee training, endpoint security, and proactive certificate management to curb these risks.

The Hidden Tax on Security: How Data Costs Are Eating Your Controls Budget
Security leaders are confronting a hidden budget drain: the cost of moving, normalizing, and ingesting massive volumes of telemetry before any detection occurs. As data sources proliferate across cloud, SaaS, endpoints, and IoT, ingestion expenses—both vendor fees and engineering labor—are...

Reverse Engineering With AI Unearths High-Severity GitHub Bug
GitHub disclosed CVE‑2026‑3854, an 8.7‑score remote‑code‑execution flaw in GitHub Enterprise Server that could be triggered by malicious git push options. The vulnerability also affected GitHub.com, Enterprise Cloud, and related hosted services, all of which were patched within hours. Cloud‑security firm...

Harvey Nash Study Finds 77% of UK Cyber Staff Got No Pay Rise as Workloads Surge
Harvey Nash’s 2025 survey reveals that 77% of UK cybersecurity professionals received no salary increase, with 71% globally seeing stagnant pay despite a 50% rise in severe attacks. The mismatch between expanding workloads and flat compensation is fueling burnout and...

What to Expect During the Dell and Intel ‘Securing the AI Factory’ Event: Join theCUBE May 7
Dell Technologies and Intel are hosting a "Securing the AI Factory" event on May 5, followed by a theCUBE livestream on May 7, to showcase how integrated hardware and security controls can protect enterprise‑scale generative AI workloads. The partnership leverages Intel’s Gaudi 3...

Map Cloud Security Services Across AWS, GCP, Azure
Cloud Security mapped across the Big 3 ☁️🔐 AWS vs Google Cloud vs Azure—same goals, different tools. From IAM to KMS, WAF to DDoS protection—understanding these equivalents is key for multi-cloud + DevSecOps workflows. If you can map the services, you can secure...
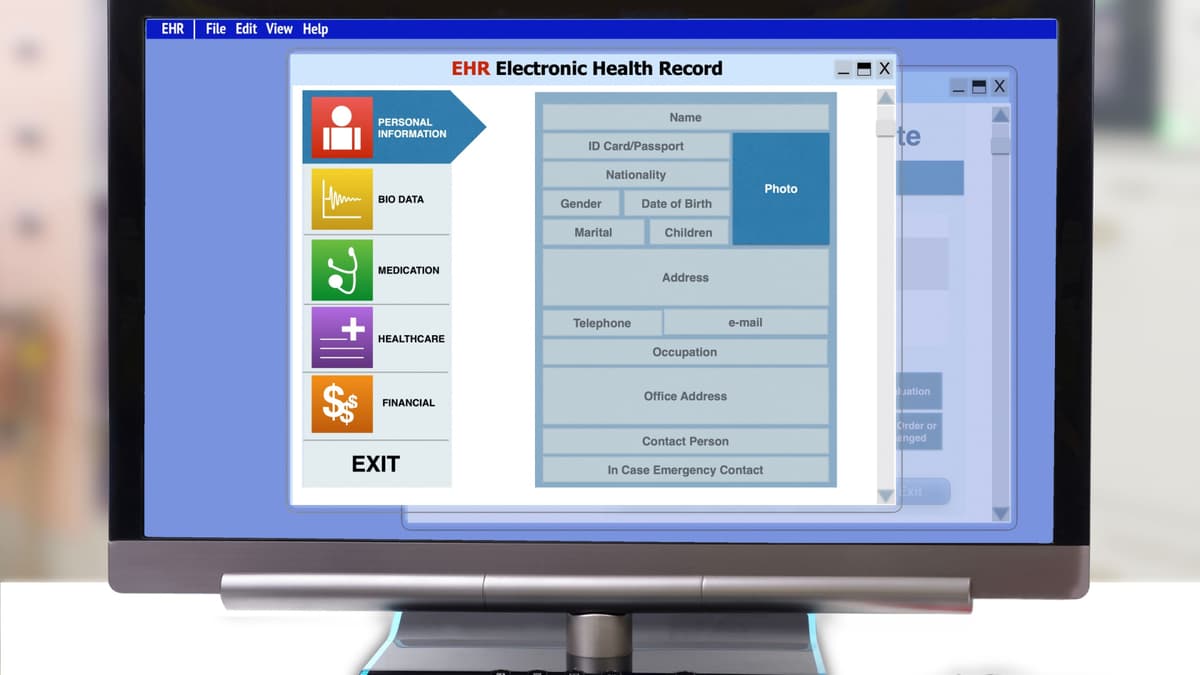
AI Finds 38 Security Flaws in Electronic Health Record Platform
Aisle's AI-powered scanner identified 38 previously unknown vulnerabilities in the open‑source OpenEMR platform, which serves over 100,000 providers worldwide. The flaws, spanning medium to critical severity, include SQL injection, cross‑site scripting, path traversal and authorization bypasses. OpenEMR released version 8.0.0 and...

ZetaChain Suspends Cross-Chain Operations on Mainnet After Security Incident Involving GatewayEVM Smart Contract
ZetaChain announced a temporary suspension of all cross‑chain transactions on its mainnet after detecting a targeted exploit on its GatewayEVM smart contract. The breach impacted only internal team wallets, and the protocol’s monitoring systems blocked the attack vector within minutes,...

House Panels Probe Airbnb, Anysphere over Use of Chinese AI Models
Republican‑led House Homeland Security and China Select committees have sent letters to Airbnb and Anysphere demanding details on their use of Chinese AI models. The inquiry targets Anysphere’s Composer 2, built on Moonshot AI’s Kimi model, and Airbnb’s deployment of Alibaba’s...

Congress, Industry Ponder Government Posture for Protecting Data Centers
Lawmakers on the House Homeland Security Subcommittee held a hearing to assess whether U.S. data centers should receive a standalone critical infrastructure designation. Industry witnesses cited recent Iranian drone attacks on Amazon facilities and the rapid AI‑driven construction boom as...

Choosing CTEM vs ASM: Which Delivers More Value?
Are you using CTEM or ASM for your organization? Interested to know how you've integrated these tools into your security operations? What’s delivering the most value?

Auvik Bets Agentic AI Can Fill the Networking Skills Gap
Auvik introduced Aurora, an agentic AI platform that moves network management from passive alerting to automated remediation. The system prioritizes alerts, tracks device lifecycle, monitors CVEs, and generates remediation scripts via natural‑language queries. Aurora draws on Auvik’s 15‑year data set—over...

Swisscom Radar Warns of Geopolitical Cyber Surge
Swisscom’s Cybersecurity Threat Radar warns that the Swiss threat landscape is being reshaped by a convergence of state‑sponsored attacks, hybrid disinformation campaigns, and AI‑driven risk multipliers. The report highlights software supply‑chain fragility, where a single compromised component can ripple through...

ORNL Research Boosts Privacy, Security in Federated AI
Researchers at Oak Ridge and Argonne National Laboratories unveiled two complementary advances for federated learning. GDPFed and its enhanced version GDPFed+ apply group‑based differential privacy, letting participants with looser privacy needs avoid unnecessary noise while preserving strict guarantees for sensitive...

The AI-DLC: The Good, The Bad, and the Risky
AI coding assistants such as GitHub Copilot, Cursor, and Claude Code have moved from experiment to enterprise standard, with a recent StackHawk survey showing 87% adoption and a third at full rollout. The tools boost developer velocity and can improve...

Is Your Crypto Safe From Hackers? - Dyma Budorin | ATC #609
In this episode, Dima Budarin, CEO of Core3 and co‑founder of Hacken, discusses the evolving landscape of Web3 security, emphasizing that while smart‑contract audits have improved, operational and supply‑chain security remain weak points. He explains Core3’s mission to provide Moody’s‑style...

A Glimpse Into Cyber-Security’s AI-Driven Future
Black Hat Asia 2026 turned its conference venue into a live cyber‑security proving ground, building a bespoke network from the ground up and defending it in real time. The event’s Network Operations Centre faced thousands of world‑class hackers, including participants...

Bentley Systems Achieves Key U.S. Government Security Milestone to Help Modernize Infrastructure
Bentley Systems announced that its ProjectWise and OpenGround platforms have received FedRAMP Moderate Impact Level authorization, clearing the way for U.S. federal agencies to use the tools in a secure cloud environment. The certification, driven by the Federal Risk and...

Kensington Launches FIDO2 Level 2 NFC Security Keys for Tap-Based Mobile Authentication
Kensington, a division of ACCO Brands, has introduced two NFC‑enabled security keys that achieve FIDO2 Level 2 certification, the highest tier in the FIDO Alliance’s authenticator program. The VeriMark NFC+ USB‑C and USB‑A models support both USB and tap‑based authentication, allowing...

Homebuyers Privacy Protection Act Forces Lenders to Upgrade Data Tools
The Homebuyers Privacy Protection Act, signed into law in September 2025 and effective March 5, 2026, bars credit bureaus from sharing mortgage trigger leads without explicit borrower consent. Lenders are scrambling to replace the lost channel with predictive‑analytics platforms, a...

Polymarket Rejects Data Breach Claims as Hacker Alleges 300K Records Stolen
A hacker identified as Xorcat alleges that they extracted roughly 300,000 records from Polymarket by exploiting undocumented API endpoints, a pagination bypass, and CORS misconfigurations. The purported data dump, said to total 2.24 GB, includes user profiles, market information, and an...
FBI Extradites China‑Linked Hacker, Spotlighting LegalTech’s Role in Cyber Forensics
FBI Director Kash Patel announced the extradition of Chinese national Xu Zewei from Italy to face U.S. charges for a 2020‑21 cyber campaign that targeted COVID‑19 research. The operation, coordinated with Italian authorities, highlights the growing reliance on digital forensics and...

Vibe Coding Promises AI‑Built Apps in Days, Raising Governance Concerns
Vibe Coding’s AI platform enables a marketing manager with no engineering background to launch a polished customer‑facing app within a week, showcasing the speed of “vibe coding.” The breakthrough accelerates delivery but also sidesteps traditional DevOps checks, prompting worries about...

Flo App Found to Have Sold Reproductive Health Data to Meta, Sparking Privacy Backlash
A federal jury concluded that Flo, the period‑tracking app with 75 million users, illegally shared sensitive reproductive health information with Meta. The verdict backs a class‑action suit representing 13 million users and raises fresh questions about data practices in consumer health tech.

Checkmarx Confirms Supply‑Chain Breach, Source Code Leaked to Dark Web
Checkmarx, a leading application‑security vendor, confirmed that a supply‑chain attack on March 23, 2026 compromised its GitHub repository. Threat actors posted source code, API keys and employee data on a dark‑web leak site, potentially affecting more than 170,000 users.

China Threatens the EU with Broad Retaliation if Huawei and ZTE Are Banned From European Networks
China’s Ministry of Commerce submitted a 30‑page warning to the European Commission, saying the EU’s draft Cybersecurity Act – which would make the removal of high‑risk vendors like Huawei and ZTE mandatory – could trigger reciprocal trade restrictions on European...
Vect 2.0 Ransomware Acts as Wiper, Thanks to Design Error
Check Point discovered that Vect 2.0, a ransomware‑as‑service variant, unintentionally erases any file larger than 128 KB because it discards three of the four ChaCha20‑IETF nonces needed for decryption. The flaw turns the malware into a data wiper, leaving victims unable to...

April Global Regulatory Brief: Digital Finance
In April 2026 regulators across Japan, Switzerland, the United States and the United Kingdom released new guidance targeting digital‑finance risks. Japan’s Financial Services Agency issued a comprehensive cybersecurity policy for crypto‑asset exchanges, while Switzerland’s FINMA published a digital‑fraud risk‑management guide for...

Hang up when Telemarketers Demand Gift‑card Payment
The next time a telemarketer asks you to pay with a gift card, hang up. https://t.co/eKgkYoJ3Cw

Cursor Extension Flaw Exposes Developer API Keys
A critical vulnerability in the AI‑driven IDE Cursor lets any installed extension read the tool’s local SQLite store, exposing API keys and session tokens without user interaction. LayerX’s research gave the flaw an 8.2 CVSS rating, highlighting the risk of...
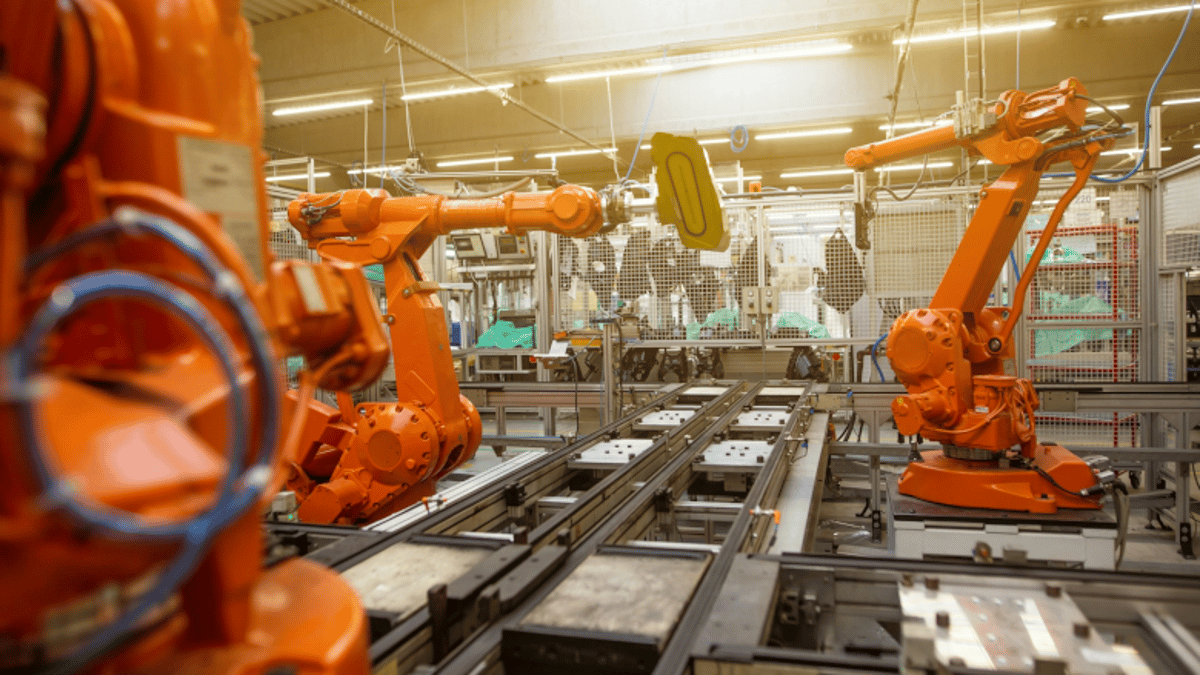
Ransomware Responsible for 90% of Manufacturing Cyber Losses
New claims analysis shows ransomware accounts for 90% of financial losses in manufacturing, even though it represents only 12% of incident volume. Phishing and transfer fraud make up 30% of claims, while MFA misconfigurations cause 26% of total losses. The...

Bitwarden CLI Compromised
In this episode Adam covers the latest developer‑tool news, highlighting a supply‑chain attack that compromised the Bitwarden CLI, the release of TypeScript 7 beta with a ten‑fold performance boost, and Ubuntu 26.04 LTS becoming the new long‑term release. He also...
CISA Adds Microsoft, ConnectWise Vulnerabilities to Active Exploitation Catalog
On April 29, 2026, the Cybersecurity and Infrastructure Security Agency (CISA) added two actively exploited software flaws to its Known Exploited Vulnerabilities (KEV) catalog: CVE‑2024‑1708 in ConnectWise’s ScreenConnect remote‑access tool and CVE‑2026‑32202 in the Windows Shell UI. The high‑severity ConnectWise bug enables...

These Two Critical Mac Security Features Are Off by Default - How to Turn Them on and Why You Should
Most macOS devices ship with the built‑in firewall turned off, leaving them exposed to network attacks. ZDNet explains how to enable the firewall and its companion Stealth Mode, which blocks ping and connection attempts. The step‑by‑step guide walks users through...

Rippling Rolls Out Automated Compliance Tool for SOC 2 Audits
Rippling, the San Francisco‑based workforce platform, unveiled an automated compliance tool that streamlines SOC 2 Type 1 and Type 2 audits. The solution leverages existing HR, device‑management and identity data to recommend controls, collect evidence in real time, and automatically remediate gaps. It consolidates...
How to Make CTEM Operational versus Aspirational
Continuous threat exposure management (CTEM) must evolve from a strategic buzzword into an everyday security rhythm. The piece outlines seven priorities—continuous asset reality, attacker‑centric exposure modeling, cross‑environment correlation, exploitability validation, dynamic reprioritization, outcome‑based metrics, and workflow integration—to embed CTEM in...

Blog 115a. XRP, Bitcoin, and the Quantum Threat.
The blog warns that major digital asset networks, including XRP and Bitcoin, are not quantum‑safe. While a quantum breakthrough isn’t imminent, the risk is real and predictable. Current cryptographic designs were never built for a future where encryption can be...

Even Perfect Prompts Can't Stop AI Code Vulnerabilities
“No matter how well you prompt, code generators generate security vulnerabilities” - Michael Beckley #AppianSummit #AI #CIO https://t.co/W1VnkrnWPi

OSIbeyond Launches Compliance as a Service (CaaS), Eliminating Upfront Costs for CMMC Compliance
OSIbeyond, a managed IT and cybersecurity firm serving the Defense Industrial Base, launched a Compliance as a Service (CaaS) solution that shifts CMMC compliance from a costly, project‑based model to a subscription‑based, fully managed service. The offering bundles secure Microsoft...

New Dawn Risk Introduces Specialist Cyber Insurance Solution Focused on US Healthcare Privacy Risks
New Dawn Risk, a Lloyd’s specialist broker, has launched a cyber insurance product tailored for U.S. healthcare, life‑science and pharmaceutical firms. The policy adds an aggregate limit dedicated to HIPAA and biometric privacy fines, preserving the main cyber coverage limit....

JSON Schema Emerges as Key Guardrail for Generative AI Outputs
Enterprises are turning to the long‑standing JSON Schema standard to impose structure on generative AI results. Experts say the move addresses data integrity, integration and security concerns that CIOs face as AI models become more pervasive.

OTAVA Appoints Donnie Gerault as President and CEO, Signaling New Growth Phase
OTAVA, a secure multi‑cloud solutions provider, announced on April 28 that Donnie Gerault has been appointed President and Chief Executive Officer. Gerault brings more than two decades of cloud‑service leadership, including senior roles at Lenovo, Atos and Cloud49. The move...

Dataiku Launches Kiji Privacy Proxy to Guard Enterprise Data in Generative AI
Dataiku announced the general availability of Kiji Privacy Proxy, an open‑source layer that prevents personally identifiable information from leaving a company when using third‑party generative AI services. The tool automatically masks and restores data, aiming to remove a key barrier...

Proton VPN Rolls Out Post‑Quantum Roadmap and Linux Stealth Protocol
Proton VPN disclosed a Spring‑Summer 2026 roadmap that adds client‑side post‑quantum encryption, a redesigned Linux app and the Stealth protocol to bypass aggressive firewalls. The plan, already in beta on Android and Windows, aims to cement the Swiss firm’s lead...

Apple Fixes Bug That Let FBI Extract Deleted Signal Messages After 404 Media Coverage
Apple released an iOS update that eliminates a flaw allowing the FBI to retrieve deleted Signal messages stored in the iPhone’s notification database. The bug let investigators extract copies of incoming messages even after the app was removed, as reported...

Medtronic Confirms Cyberattack as ShinyHunters Claims Theft of 9 Million Medical Records
Medtronic disclosed a cyberattack on its corporate IT systems after the ShinyHunters ransomware group claimed to have stolen roughly 9 million medical records. The company said patient safety and product operations were unaffected, but the breach raises significant data‑privacy questions for...

Researchers Track 2.9 Billion Compromised Credentials
KELA’s 2026 State of Cybercrime report reveals nearly 2.9 billion compromised credentials worldwide in 2025, driven by a dramatic rise in macOS infostealer infections. Ransomware victims increased 45% to 7,549 incidents, while DDoS attacks jumped 400% to 3,500. The firm also...
State CISOs Losing Confidence in Ability to Manage Cyber Risks
Statewide chief information security officers are losing confidence in their ability to manage cyber risk, with only about 25% feeling "extremely" or "very" confident that state assets are protected—a sharp drop from nearly half in 2022. The decline coincides with...

Brinker Introduces a Novel Approach to Deepfake Detection
Brinker unveiled a malicious‑intent based deepfake detection capability that adds a new risk‑focused layer to AI‑driven disinformation defense. The feature centers on a Malicious Intent Probability metric, assessing sentiment, risk alignment, coherence, context and source corroboration rather than pure forensic...

What to Expect at ITS America 2026: Tech, Cybersecurity and the Future of Transportation
The ITS America Conference & Expo returns to Detroit June 9‑12, 2026 under the “Empowering Innovation” theme. Organized by Rx Global and ITS America, the four‑day event will spotlight connected, automated and data‑driven transportation technologies. A dedicated Cybersecurity & Data Zone and...