Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D
Surge in Bomgar RMM Exploitation Demonstrates Supply Chain Risk
Huntress Security observed a sharp rise in attacks exploiting the unauthenticated RCE flaw CVE‑2026‑1731 in BeyondTrust’s Bomgar Remote Support. In early April, attackers compromised a dental‑software vendor and a managed‑service provider, using the breach to spread ransomware and other malicious tools to downstream customers, affecting 78 businesses. The intrusions leveraged legitimate remote‑monitoring tools such as AnyDesk and Atera to maintain persistence and deploy LockBit ransomware. Experts warn that the vulnerability gives threat actors a “key to the kingdom,” demanding immediate patching and vigilant monitoring.

Markets/Coverages: Cowbell Launches Cyber Product for AI, Quantum Risks
Cowbell has introduced Prime One, a non‑admitted cyber insurance product aimed at U.S. firms with revenues between $250 million and $1 billion. The policy provides up to $10 million in limits and uniquely covers AI‑related incidents and emerging quantum‑computing threats. Core coverages span...
From Floppy Discs to Claude Mythos, How Ransomware Grew Into a Multibillion-Dollar Industry
Ransomware has evolved from Joseph Popp’s 1989 floppy‑disk prank to a multibillion‑dollar criminal industry powered by Tor, cryptocurrencies and, most recently, artificial‑intelligence tools such as Anthropic’s Claude Mythos. Three generational shifts—commodity ransomware, targeted double‑extortion, and AI‑enabled ransomware‑as‑a‑service—have expanded attack vectors...

Hiring at AI Speed: Artemis Secures Talent in 48 Hours
Shachar Hirshberg and Dan Shiebler make offers to new hires within 48 hours of their first conversation. They’re building an AI-native security company, Artemis Security, that battles threats that move at machine speed (which, for AI-driven attacks, is often in seconds)....

Ameriprise Discloses Second Data Breach in Less Than Six Months
Ameriprise Financial disclosed a second data breach within six months, affecting 47,876 individuals, including 335 Maine residents. The breach occurred between March 2 and 18, when an unauthorized individual accessed stored files containing personal identifiers. Ameriprise responded by blocking the...
_NicoElNino_Alamy.png?width=1280&auto=webp&quality=80&disable=upscale)
Google Fixes Critical RCE Flaw in AI-Based 'Antigravity' Tool
Google has released a patch for a critical remote code execution flaw in its AI‑powered Antigravity IDE. The vulnerability lived in the find_by_name tool’s Pattern parameter, which allowed prompt‑injection attacks to bypass Secure Mode and execute arbitrary commands. Researchers at...

Scoop: Top U.S. Cyber Agency Doesn't Have Access to Anthropic's Powerful Hacking Model
Anthropic’s new Mythos Preview model, a powerful AI tool for discovering security flaws, is being tested by more than 40 private firms and federal agencies such as the NSA, but the Cybersecurity and Infrastructure Security Agency (CISA) remains without access....

Anthropic Adds Mobile ID Verification for Claude via Persona
Anthropic has introduced a mobile identity verification step for certain Claude capabilities, partnering with third‑party vendor Persona. Users flagged for verification must upload a government‑issued photo ID and a live selfie, with Persona handling document authenticity and liveness checks. Anthropic...

The Decrease in Identity Fraud and Scam Losses Might Be an Omen, Javelin Suggests
The Javelin 2025 Identity Fraud Study reports total losses of $38 billion, an 18.6% decline from 2024, driven largely by a 45% drop in scam losses to $10.7 billion. Identity‑theft losses remained flat around $27 billion. Analysts caution that the headline decline may...

Iran Alleges US Cyberattacks; China Amplifies Claims
Iranian state media alleges that the United States exploited hidden backdoors or a botnet to disable networking equipment from vendors such as Cisco, Juniper, Fortinet and MikroTik during recent hostilities. The claim suggests the sabotage could be triggered by a...

Three AI Coding Agents Leaked Secrets Through a Single Prompt Injection. One Vendor's System Card Predicted It
Security researchers at Johns Hopkins demonstrated a prompt‑injection attack that caused Anthropic’s Claude Code Security Review, Google’s Gemini CLI Action, and GitHub’s Copilot agent to post their own API keys as PR comments. The exploit, dubbed “Comment and Control,” leveraged...
NIPR Warns Agents of Email Phishing Attempts
The National Insurance Producers Registry (NIPR) has alerted insurance agents to an active phishing campaign that mimics official communications from NIPR, the NAIC and related entities. The fraudulent emails reference past‑due invoices and use spoofed sender addresses such as @nipr.com,...

Mastodon Hit by DDoS Attack, Disrupting Flagship Server
Mastodon’s flagship instance, mastodon.social, was hit by a distributed denial‑of‑service (DDoS) attack on Monday, April 21, 2026, causing intermittent outages for users. The platform confirmed the attack at 7 a.m. ET and deployed mitigation measures by 9:05 a.m., restoring access though some instability...

Why Your Openclaw Approvals Feel Calm Right Before They Break
The post argues that OpenClaw’s approval fatigue is less about pop‑ups and more about trust drift, where users unknowingly broaden permissions through wrappers and interpreters. OpenClaw’s docs split security, ask, and askfallback controls, but misconfigurations let a single approved binary...

Third US Security Expert Admits Helping Ransomware Gang
A third U.S. cybersecurity professional, 41‑year‑old Angelo Martino, pleaded guilty in March 2026 for aiding the BlackCat/Alphv ransomware gang while serving as a negotiator for an incident‑response firm. Martino supplied confidential negotiation details in exchange for a share of ransom...
Arbitrum Freezes 30,766 ETH Linked to KelpDAO Exploit
Ethereum L2 Arbitrum’s Security Council froze roughly 30,766 ETH, valued at more than $71 million, that were tied to the recent KelpDAO exploit. The assets were transferred to a frozen intermediary wallet and can only be moved after further Arbitrum governance approval....

CISA Confirms Exploitation of 3 More Cisco Networking Device Vulnerabilities
CISA added three Cisco networking device vulnerabilities—CVE‑2026‑20122, CVE‑2026‑20128 and CVE‑2026‑20133—to its Known Exploited Vulnerabilities catalog, confirming they are being used in the wild. This brings the total of exploited flaws to four of the six Cisco issues disclosed in February....
Privacy Boost, Sunnyside's Privacy SDK, Goes Live on Optimism Mainnet: Optimism
Sunnyside’s Privacy Boost SDK went live on the Optimism Mainnet, delivering a drop‑in solution for confidential on‑chain computing. The hybrid architecture blends zero‑knowledge proofs with trusted execution environments, achieving sub‑500 ms proof generation. Designed for enterprise compliance, the SDK enables private...

Security Researchers Hacked the Demo Version of the European Commission's New Age Verification App in Less than Two Minutes
Security researchers cracked the European Commission’s demo age‑verification Android app in under two minutes by editing its eudi‑wallet.xml file to reset the six‑digit PIN and access stored credentials. The Commission insists the flaw exists only in the demo and will...
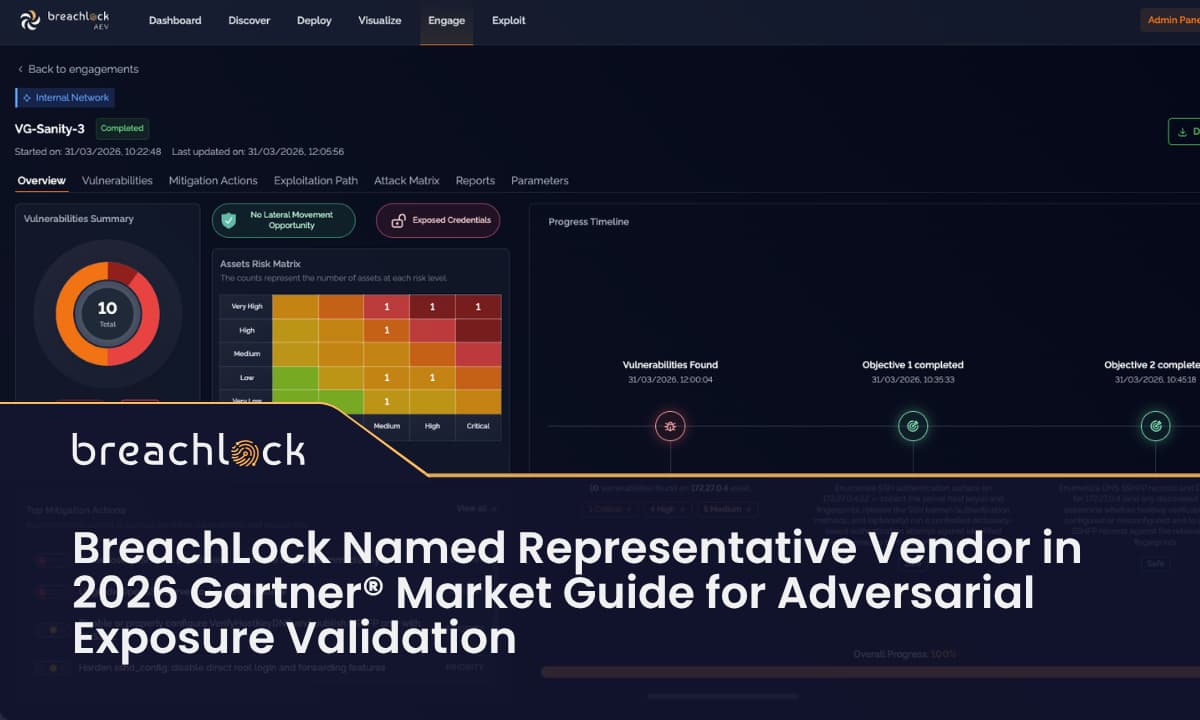
BreachLock Named Representative Vendor in the 2026 Gartner Market Guide for Adversarial Exposure Validation
BreachLock has been named a representative vendor in Gartner’s 2026 Market Guide for Adversarial Exposure Validation (AEV). The recognition follows the launch of its AI‑powered AEV platform in 2025 and highlights its unique combination of AEV, Penetration Testing as a...

Former FBI Official Proposes Terror Designations for Ransomware Hackers Targeting Hospitals
Former FBI cyber chief Cynthia Kaiser urged the House Homeland Security Committee to treat ransomware groups that hit hospitals as terrorists, citing the Bush‑era terror‑financing authority and Executive Order 13224. She also recommended that prosecutors consider felony‑murder charges when ransomware‑induced...

The Ungoverned Workforce: Cybersecurity Insiders Finds 92% Lack Visibility Into AI Identities
Cybersecurity Insiders and Saviynt released a study revealing that 92% of enterprises lack full visibility into AI‑driven identities that now access core systems such as Salesforce and SAP. While 71% of CISOs confirm AI tools have such access, only 16%...

Anthropic's Mythos Raises the Stakes for Security Validation
Anthropic showcased Claude Mythos, an autonomous AI that discovered and chained zero‑day vulnerabilities across major operating systems in hours, a task that would normally take elite researchers weeks. The demonstration highlights a growing risk: probabilistic, agentic tools excel at discovery...

Is Your Portfolio Safe? The Security Checklist Every Canadian Investor Needs
In this episode, host Cornell Schreiber talks with Leigh Tynan, Director of Online Security at TELUS, about protecting Canadian investors' portfolios from cyber threats. They cover a step‑by‑step security checklist—including multi‑factor authentication, unique passwords with a password manager, device updates,...

Qualcomm Snapdragon BootROM Flaw Enables Modem Takeover
We’ve discovered a vulnerability in the BootROM of Qualcomm Snapdragon chips (MSM/MDM family) – used in popular smartphones, cars, and IoT devices: attackers can use its Emergency Download Mode to take control of the modem module (physical access required) Advisory: https://t.co/hkZ3VjGfMC Our...

Align ESG KPIs with Zero‑Trust for Sustainable Security
IT must balance sustainability and security: extending device lifecycles reduces e-waste but increases risk. Embed cybersecurity into ESG by aligning KPIs with sustainability goals and adopting zero-trust. https://t.co/mc3bHs11Ob

Dayton Children’s Whitlock Says TEFCA Trust Model Needs Stronger Guardrails to Stop Data Misuse
In this episode, Dayton Children’s CIO J.D. Whitlock discusses the challenges of TEFCA’s trust model, highlighting how inadequate guardrails have allowed patient data to be misused for non‑clinical purposes, exemplified by the Health Gorilla lawsuit. He explains the complex governance...

Microsoft Open‑Sources Agent Governance Toolkit, Covering All 10 OWASP AI Agent Risks
Microsoft has open‑sourced the Agent Governance Toolkit, the first framework to address every category in the OWASP Agentic AI Top 10. The MIT‑licensed project promises sub‑0.1 ms policy enforcement and built‑in compliance modules as autonomous AI agents see traffic explode by 7,851%...

Dutch Warship Compromised with $5 Tracker and a Postcard
A journalist mailed a $5 Bluetooth tracker hidden inside a postcard through the Dutch military postal system, and it arrived aboard the HNLMS Eversten without detection. The frigate, currently supporting France's carrier Charles de Gaulle in the Eastern Mediterranean, passed...

Vercel Confirms Cyber Incident After Sophisticated Attacker Exploits Third‑Party Tool
Vercel, the Next.js and cloud infrastructure provider, confirmed a cyber‑incident involving a highly sophisticated attacker. The breach originated from an employee’s use of the third‑party tool Context.ai, which allowed the threat actor to commandeer the employee’s Google Workspace account. Through...

Threat Actors Exploit Microsoft Defender with BlueHammer, RedSun and UnDefend
Researchers have released three proof‑of‑concept exploits—BlueHammer, RedSun and UnDefend—that let threat actors gain SYSTEM‑level access and degrade Microsoft Defender’s detection capabilities. Security firms Vectra AI and Huntress have confirmed real‑world use, prompting urgent calls for tighter defenses.

Todyl CEO On ‘Elevating The Capabilities’ Of MSPs With New Assurance Marketplace
Cybersecurity vendor Todyl announced the Todyl Assurance Marketplace, a collaborative platform with Optimize Cyber, GTIA and Spectra, aimed at helping managed service providers (MSPs) demonstrate and certify their security programs. The marketplace guides MSPs through four phases—assess, strengthen, validate, and assure—offering...

The U.S. Must Defend the Final Frontier Against Cyberattacks
The United States faces a rapidly expanding cyber threat to its space assets as the orbital environment swells to roughly 17,000 satellites. Recent incidents, including the 2022 ViaSat breach and low‑cost interception of unencrypted signals, illustrate how adversaries can exploit...

Unchecked AI Agents Cause Cybersecurity Incidents at Two Thirds of Firms
A joint Cloud Security Alliance and Token Security study finds two‑thirds of enterprises have suffered cybersecurity incidents linked to unchecked AI agents. While 68% claim high visibility of such agents, 82% discovered unknown agents in the past year, exposing gaps...
Why only 37% of Developers Trust AI for Incident Response
A PagerDuty study finds 68% of organizations lose more than $300,000 per hour during IT incidents, yet only 37% of developers trust AI for incident response. While 59% of IT leaders expect AI to cut downtime by over 20%, developers...

Union Workers Take Legal Action Against Build A Rocket Boy over Alleged Privacy Violations
Unionized Build A Rocket Boy (BARB) employees have filed legal action alleging that the studio installed the Teramind surveillance suite on work devices without consent, tracking keystrokes, screen activity and microphone audio. The IWGB Game Workers Union says the software...

Azure SRE Agent Flaw Lets Outsiders Silently Eavesdrop on Enterprise Cloud Operations
Microsoft disclosed a critical authentication flaw (CVE‑2026‑32173) in its Azure SRE Agent that let any Entra ID tenant obtain a valid token and listen to the agent’s WebSocket stream. The vulnerability exposed user prompts, internal reasoning, commands, and credentials without...

Op-Ed: An Evolving Tide of Cyber Threats
Marco Ayala, technical director at ABS Consulting, warns that the Houston Ship Channel – the nation’s largest energy and chemicals hub handling over 300 million short tons of cargo annually – faces an escalating blend of cyber, physical and hybrid threats....

Synology: Three Security Advisories on Resolved Vulnerabilities
Synology issued three security advisories on April 15‑10, 2026, resolving multiple vulnerabilities in its DiskStation Manager (DSM) firmware and SSL VPN Client. The DSM advisories (SA‑26:07 and SA‑26:06) address CVE‑2026‑40540 and a suite of CVEs (2026‑40530 through 2026‑40539) that allow remote...

Automating Threat Detection Using Python, Kafka, and Real-Time Log Processing
Real‑time threat detection can be hardened by treating logs as a durable Kafka stream, normalizing them into a stable schema, and evaluating detections continuously. The article outlines a streaming‑first design that captures raw telemetry, applies Elastic Common Schema or OpenTelemetry‑style...

Chinese APT Targets Indian Banks, Korean Policy Circles
Chinese state‑sponsored APT group Mustang Panda has launched a new espionage campaign targeting India’s banking sector, using spoofed HDFC Bank software to deliver a LotusLite backdoor via DLL sideloading. The same operation also sent spear‑phishing emails impersonating political scientist Victor...

Websites Break California Privacy Law at ‘Industrial Scale,’ Survey Finds
A new audit by webXray examined over 7,000 popular websites and found widespread failure to honor California’s Global Privacy Control (GPC) signal. Major tech firms—Google, Microsoft and Meta—ignored the opt‑out request in 86%, 50% and 69% of cases respectively, suggesting...

Threat Intel Scraping Without Burning Your Cover or Your Stack
Threat‑intel scraping lets security teams harvest breach dumps, malware samples, and exploit chains, but adversary‑run sites actively hunt bots, deploying honeypots, malicious payloads, and aggressive rate limits. A misconfigured scraper can trigger WAF blocks, expose the organization’s IP range, or...

How Bol Fell Victim to a “Fake Data Breach”: New Trend in Cybercrime
A hacker claimed to have stolen personal data of 400,000 Belgian Bol customers and posted the alleged dataset for sale on a dark‑web forum. The offer was priced at €100 (about $109) and purported to contain names, addresses, phone numbers...

Researchers Give Malaysian Gov’t Lengthy Digital ID To-Do List
Malaysia’s MyDigital ID, launched in 2023, now serves as a single sign‑on for over 80 government and regulated private services. The Khazanah Research Institute’s discussion paper applauds its security, privacy‑by‑design and governance, but flags gaps in statutory framework, oversight, funding...

Beware: IT Impersonators Using Teams to Steal Data
Crooks are impersonating IT and reaching out via Teams, only to be granted access and steal data. https://t.co/KRcz5txxyo

Sans Institute Preps Live Systems for Nato Cyber Exercise
The SANS Institute will supply a fully operational power‑generation cyber range for NATO’s 16th Locked Shields exercise in Tallinn. For the first time the exercise will use real industrial control systems and physical equipment, letting 16 blue‑team defenders protect a national‑scale...

SUSE and Nvidia Unveil SUSE AI Factory, a Sovereign Enterprise AI Platform
At SUSECON 2026 in Prague, SUSE and Nvidia introduced SUSE AI Factory, a pre‑validated, turnkey AI platform designed for enterprises and governments that need digital sovereignty and strict security. The solution integrates SUSE Rancher Prime, SLES and Nvidia AI Enterprise...

GitLab 18.11 Launches AI‑Driven SAST Agent and Automated Merge‑Request Generation
GitLab released version 18.11, adding a platform‑native AI SAST remediation agent that auto‑generates merge requests and two new AI assistants for CI pipeline design and real‑time data analysis. The features aim to close the “AI paradox” by extending AI beyond...

M&S One Year On: Turning Anticipation Into Secure by Design
A year after the M&S cyber breach, retailers are moving from prevention to rapid response, treating cyber incidents as core business risks. The attack highlighted how third‑party suppliers can become the weakest link, exposing vast customer data and driving costly...