Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB
Security Firm Releases 114m-Record Dataset Built From Live Enterprise Attack Traffic
WitFoo, a US‑New Zealand security vendor, released the Precinct 6 Cybersecurity Dataset, a free, Apache‑2.0‑licensed collection of 114 million labelled security‑event records captured from five enterprise networks in mid‑2024. The data spans telemetry from 158 products across more than 70 vendors, with 99.34% benign events and 0.11% confirmed malicious activity. Developed with the University of Canterbury, the dataset is hosted on Hugging Face and is positioned as the largest real‑world adversary‑behaviour set, dwarfing synthetic alternatives like CICIDS2017. WitFoo estimates that training a large language model on the full set could cost up to $9.38 million in compute.

Aave Models $124M to $230M in Bad Debt From Kelp Exploit
Aave’s service providers released an incident report quantifying the protocol’s exposure to the April 18 Kelp DAO rsETH bridge exploit, estimating bad‑debt between $123.7 million and $230.1 million. Attackers moved 89,567 rsETH onto Aave, borrowing roughly $193 million in WETH and wstETH, with health factors...

The Gentlemen Ransomware Now Uses SystemBC for Bot-Powered Attacks
The Gentlemen ransomware‑as‑a‑service has begun deploying the SystemBC proxy‑malware botnet, which now comprises over 1,570 compromised hosts. The botnet, historically used for SOCKS5 tunneling, is being leveraged to deliver Cobalt Strike payloads and facilitate lateral movement in corporate networks. Check Point...

QEMU Hijacked to Install Stealth Backdoor for Credential Theft and Ransomware
Security researchers have uncovered two advanced QEMU‑based campaigns, STAC4713 and STAC3725, that embed hidden Linux VMs inside Windows hosts to steal credentials and launch PayoutsKing ransomware. The technique evades traditional endpoint tools, raising alarms for cloud and on‑prem operators.

Claude Desktop Changes App Access Settings for Browsers You Don't Even Have Installed Yet
Anthropic’s Claude Desktop for macOS silently creates a Native Messaging manifest that pre‑authorizes Claude browser extensions across Chromium‑based browsers, even if those browsers are not yet installed. The manifest registers a local executable that runs outside the browser sandbox without...

Increased Attacks on Physical Infrastructure by Pro-Iran Hackers: Defense One
A pro‑Iran hacktivist group called Ababil of Minab claimed to have accessed the Los Angeles County Metropolitan Transportation Authority’s internal systems. Transit operations continued without interruption, but the breach underscores a broader trend of Iranian‑aligned actors targeting U.S. critical infrastructure,...

Lovable Denies Mass Data Breach
Swedish low‑code AI startup Lovable denied a mass data breach after an X user claimed they could view other customers' chat histories and personal details. The company admitted its documentation on "public" project visibility was unclear, but says no breach...

Many Smartphones Don’t Detect Face Biometrics Spoofs or Properly Warn Consumers
Which? tested 208 Android smartphones and found 64% vulnerable to 2D printed photo spoofs. iPhones remain largely immune due to depth‑sensing Face ID, while some newer Pixel models also resisted flat images. Many Android manufacturers, including OnePlus and Motorola, fail...

Data Poisoning: Yet Another AI Threat: Artificial Intelligence Trends
Data poisoning, once viewed solely as a security attack, is now being adopted by companies as a defensive tool to control how AI models ingest their content. By inserting subtle errors, honeytokens, adversarial perturbations, or structural noise, firms can create...
Your Crypto Stays Safe with Multi‑sig, Advisor‑approved Transfers
A compromised Google account wiped out someone's XRP. Assets at Digital Wealth Partners are not tied to your Apple ID or Google account. Separate login, multi-sig verification, whitelisted addresses only. Nothing moves without a wealth advisor signing off. Some partners...

AI and CMMC: A Double-Edge Sword for Defense Contractors
The Pentagon’s CMMC program forces defense contractors to safeguard controlled unclassified information, and the surge of generative AI has complicated compliance by expanding assessment boundaries and introducing new attack vectors. Employees may inadvertently feed CUI into commercial large‑language models, risking...

Flying Somewhere This Spring? A Burner Phone Might Save You From a Border Headache
U.S. Customs and Border Protection inspected over 55,000 mobile devices last fiscal year, using forensic tools to clone and extract data from more than 4,000 phones. The deep‑scan capability means even deleted messages, photos and app data can be recovered,...

Seiko USA Website Defaced as Hacker Claims Customer Data Theft
Seiko USA’s public website was defaced over the weekend, showing a “HACKED” page that claimed attackers had stolen its Shopify customer database. The ransom note warned that the full set of customer names, emails, phone numbers, order histories and shipping...

Best Identity Theft Protection Services We've Tested in 2026
CNET’s 2026 roundup names Aura as the top identity‑theft protection service, citing its three‑bureau credit monitoring, unlimited family coverage, and a low entry price of $13 per month. Competing providers such as LifeLock, IdentityForce, IDShield and Zander offer higher insurance...

EP273 From CISA to Cloud: AI Assurance, Concentration Risk, and the New Regulatory Frontier
In this episode, Google Cloud’s VP of Risk and Compliance, Jeanette Manfra, discusses how moving to the cloud reshapes security, privacy, and regulatory compliance for organizations, emphasizing the benefits of scale, transparency, and auditable controls. She explains that cloud introduces...

Threat Actor Hijacked Subdomains at 30+ Major Universities, Researcher Found
A cybersecurity researcher discovered that a threat actor hijacked 34 .edu subdomains across more than 30 major U.S. universities, including MIT, Harvard, Stanford and Columbia. The compromised subdomains are now serving pornographic spam that Google has already indexed, exploiting the...

Scot Becomes Second Scattered Spider-Linked Crook to Plead Guilty in US
Tyler Robert Buchanan, a 24‑year‑old Scottish national linked to the Scattered Spider cybercrime group, pleaded guilty in California to conspiracy to commit wire fraud and aggravated identity theft for a phishing and SIM‑swap scheme that stole at least $8 million in...

We Can’t Trust Palantir with Our NHS Data
Palantir Technologies UK secured a data‑analytics contract with the NHS valued at roughly $15 billion over two years, promising faster cancer diagnoses and reduced discharge delays. Critics highlight that private firms have already earned about $2 billion in profit from NHS contracts,...

SGLang CVE-2026-5760 (CVSS 9.8) Enables RCE via Malicious GGUF Model Files
SGLang, a popular open‑source framework for serving large language models, has been found vulnerable to CVE‑2026‑5760, a critical 9.8‑score remote code execution flaw. The issue resides in the `/v1/rerank` endpoint, where unsandboxed Jinja2 rendering of a malicious GGUF model’s `tokenizer.chat_template`...

Italian Regulator Fines National Postal Service Orgs $15 Million for Data Privacy Violations
Italy’s data protection authority fined Poste Italiane and its digital‑payments subsidiary Postepay a total of €12.5 million ($14.7 million) for privacy breaches. The regulator said the Postepay and BancoPosta apps forced users to authorize invasive monitoring of device data, including installed applications,...

Dune Analytics Reveals 47% of LayerZero OApps Use Minimal DVN Security Following KelpDAO Hack
Dune Analytics examined roughly 2,665 active LayerZero OApp contracts over the last 90 days and found that 47 % run with a 1‑of‑1 Decentralized Validator Network (DVN) security floor, the weakest possible setting. A further 45 % use 2‑of‑2 configurations, while only...

Crypto Infrastructure Company Blames $290 Million Theft on North Korean Hackers
Crypto infrastructure firm LayerZero says a North Korean hacking group, TraderTraitor, stole nearly $290 million from the Kelp platform by exploiting a single‑verifier (DVN) setup. The attackers minted counterfeit rsETH tokens without collateral, used them as loan collateral on platforms like...

20i Hosting Range Flagged for Malware Activity
The malware report below is interesting for those who want to get into reverse engineering malware, but the IP range would immediately stand out on my network if you are trying to block such things. I looked into who owns the...

The Vercel Breach Is Not a Vercel Problem
Vercel disclosed a security incident on April 19 after a third‑party AI platform, Context.ai, was compromised and used to hijack a Vercel employee’s Google Workspace account. Through the OAuth grant, attackers accessed Vercel’s internal environments, enumerated non‑sensitive environment variables and posted...
Agencies Urge ‘Trust and Verify’ as Supply Chain Cyber Risks Shift
Federal leaders at the CyberScape summit urged agencies to adopt a continuous "trust and verify" approach to supply‑chain cybersecurity. They highlighted a visibility gap, noting that 60‑65% of Defense Logistics Agency partners are small businesses with limited cyber budgets. Officials...

Sensors Converge Presentation on Process Sensor Cybersecurity Considerations
Joe Weiss will present at Sensors Converge in Santa Clara on May 7, 2026, focusing on process sensor monitoring for cybersecurity, reliability, and safety. He argues that Level 0 process sensors are inherently vulnerable yet largely ignored by OT security forums...

Cisco Issues Emergency Patches for Four Critical Webex and ISE Vulnerabilities
Cisco disclosed four critical security flaws in its Webex Control Hub and Identity Services Engine (ISE) and released emergency patches. The vulnerabilities, each rated as high as 9.9 on the CVSS scale, could let attackers bypass authentication or execute commands...

Vercel Breach Originated From an Employee’s AI Tool
Vercel confirmed a data breach after an employee used the consumer AI service Context.ai with corporate credentials. The tool gave attackers access to the employee’s Google Workspace account, which they leveraged to enter limited Vercel internal environments. The company says...

AI Security Shifts to Governance, Data Control, Real Risk
Great roundtable in NY last week with Zscaler on securing the next wave of AI in financial services. The conversation has changed. Less hype, more focus on governance, data control, and real risk.

Serial-to-IP Converter Flaws Expose OT and Healthcare Systems to Hacking
Researchers at Forescout Technologies uncovered 20 new vulnerabilities in serial-to-IP converters from Silex and Lantronix, devices that bridge legacy serial equipment to Ethernet networks. The flaws, dubbed BRIDGE:BREAK, allow unauthenticated command injection, firmware tampering, denial‑of‑service and full device takeover. Nearly...

Fake TikTok Downloaders on Chrome and Edge Spying on 130,000 Users
LayerX Security uncovered a coordinated campaign dubbed “StealTok” that distributes fake TikTok video‑downloader extensions on Chrome and Edge. The extensions, marketed as watermark‑free download tools, have silently harvested data from more than 130,000 users worldwide, with roughly 12,500 still active....

Vercel Breach Explained: OAuth Risk in AI + SaaS Environment
Vercel suffered a breach when an employee granted OAuth access to the third‑party AI tool Context.ai, which was later compromised. The attacker used the OAuth token to infiltrate the employee’s Google Workspace account, exposing internal code, secrets, and deployment pipelines....

Quantifying Cyber Risk
The article argues that cyber risk must be quantified to answer concrete business questions, not merely to produce abstract loss figures like $420 million. It stresses that quantification should start with the adverse impact on enterprise objectives and use scenario‑based ranges...

Keeper Security Adds Enterprise-Grade Approval Governance and Real-Time Visibility to Endpoint Privilege Management
Keeper Security has upgraded its Endpoint Privilege Manager with enterprise‑grade governance tools. The update adds a centralized, role‑based approval framework, configurable approval windows, and real‑time visibility with expanded audit logging. Automated monitoring now enforces policies across Windows, macOS and Linux...

EuroStack and the Kill Switch
Four European vendors—Cubbit, SUSE, Elemento Cloud and StorPool—have announced the EU’s first EuroStack‑style sovereign disaster‑recovery pack, aiming to protect businesses from a potential U.S. kill‑switch that could block access to critical digital services. The initiative is part of a broader...

Formbook Malware Campaign Uses Multiple Obfuscation Techniques to Avoid Detection
WatchGuard researchers identified two new Formbook phishing campaigns that continue to target organizations worldwide. One campaign uses DLL sideloading, embedding malicious DLLs in a RAR archive to trick legitimate Windows processes, while the other hides obfuscated JavaScript in PDFs and...
![[Un]prompted 2026 – Gadi Evron – Opening Words](/cdn-cgi/image/width=1200,quality=75,format=auto,fit=cover/https://securityboulevard.com/wp-content/uploads/2018/01/TwitterLogo-002.jpg)
[Un]prompted 2026 – Gadi Evron – Opening Words
Gadi Evron, CEO of Knostic and committee chair at unprompted, delivered the opening remarks for the unprompted 2026 AI Security Practitioner conference. The session was recorded and posted on Infosecurity.US, then syndicated through the Security Bloggers Network. The event, streamed...

Vercel Systems Targeted After Third-Party Tool Compromised
Vercel disclosed that attackers accessed internal systems after a third‑party AI tool, Context.ai, was compromised. An employee’s Google Workspace account was hijacked, exposing non‑sensitive environment variables and credentials for a limited set of customers. Vercel has notified affected clients, urged...

Inside the Booking.com Data Breach—Should You Be Worried?
On April 13, 2026, Booking.com disclosed a cyberattack dubbed “reservation hijacking,” in which hackers accessed personal details such as names, email addresses, phone numbers and past booking information. The breach did not expose financial data like credit‑card numbers, according to...

MCMC Issues Security Guide for Remote Work: Key Risks and What Employers Can Do to Ensure Employees Work Safely
The Malaysian Communications and Multimedia Commission (MCMC) has issued a security guide aimed at protecting employees who work from home under the Bekerja Dari Rumah (BDR) scheme. The advisory warns that personal devices and unsecured home networks heighten exposure to...
SignalShot: AI-Driven Proof of Signal’s Full Security
Today is the launch of SignalShot: An AI-powered moonshot launched to prove that Signal Messenger is bug-free and secure – and turbocharge the AI-powered quest to secure all critical software.The spectacular power of new AI tools such as Mythos to find...

Permission Overhaul Unintentionally Exposed Public Project Chats
Crazy. “We also retroactively patched our API so public project chats couldn't be accessed, no matter what. Unfortunately, in February, while unifying permissions in our backend, we accidentally re-enabled access to chats on public projects.”

Court Ruling in Amazon-Perplexity Case Raises New Questions for Agentic AI in Enterprise Systems
A U.S. federal court in Northern California issued a preliminary injunction in Amazon.com Services LLC v. Perplexity AI, holding that AI agents accessing password‑protected platforms without explicit platform permission may violate the Computer Fraud and Abuse Act and California’s data‑access...
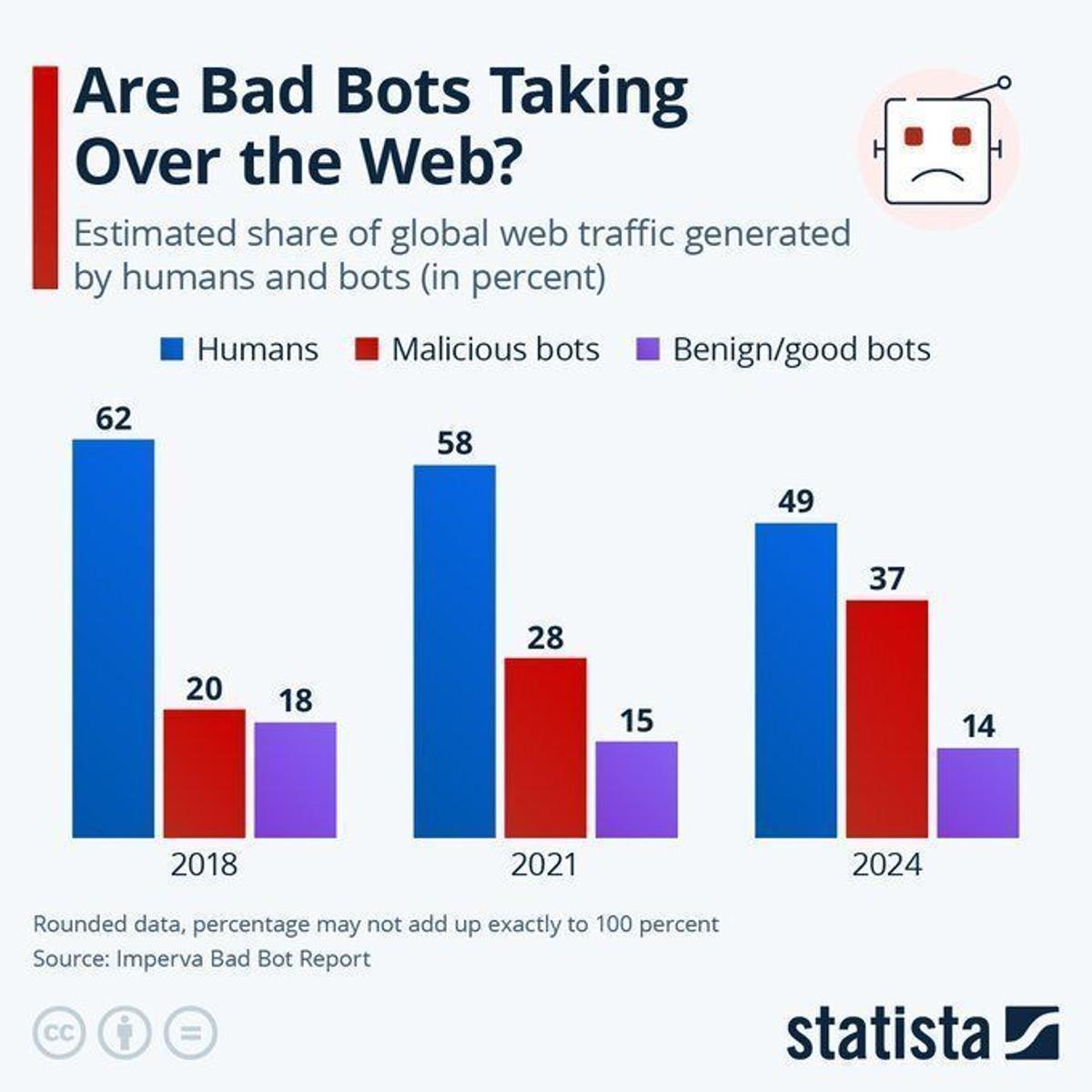
Bots Account for 37% of Web Traffic, Redefine Analytics
Web traffic metrics increasingly hide a structural distortion. Malicious bots generate 37% of activity, so marketing analytics, ad spend and cybersecurity baselines must be recalibrated because a growing share of “users” is no longer human. Source @StatistaCharts via @antgrasso https://t.co/kfAwyiqWYw

Security Alerts Steal Your Entire Workday
Ok great. Now I have to spend all day figuring out who is trying to access my systems and network. Thanks.

WhatsApp Leaks User Metadata to Attackers
Security researcher Tal Be'ery demonstrated that WhatsApp’s design leaks user metadata, allowing attackers to infer online status, device type, and activity patterns without sending visible messages. By exploiting silent ping messages and device fingerprinting through the WhatsApp Web protocol, anyone—from...

Prioritize PQ‑safe Outputs and Signatures Now, Defer Other Fixes
Follow up on Bitcoin and Quantum: A proposed roadmap. https://t.co/QoOrvnxeOe tl;dr: we should work towards activating a PQ-safe output type with PQ signatures now. everything else (including escape hatches, zk proofs, commit/reveal, to freeze or not) can, and should, wait.
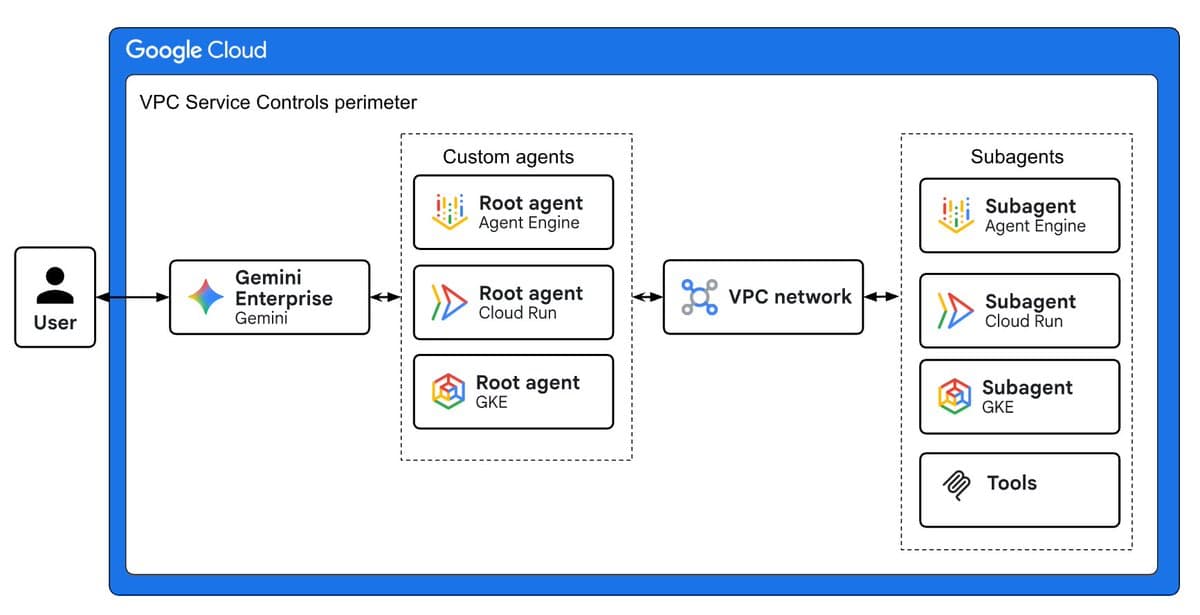
New Guide Shows Secure Multi‑Agent Networking Patterns
If you don't need more than one agent, keep it simple. But when you do, it's important to know the patterns and tech for secure networking. We just shipped a terrific new architecture guide that you can study, or give to an...
58% of Organizations Spend Over 10 Hours a Month Securing AI-Generated Code
A Cloudsmith report reveals that 58% of organizations devote more than ten hours each month to validating and securing AI‑generated code, with 8% spending over forty hours. The study also shows 44% of respondents have suffered security incidents linked to...

How CISOs Can Thrive Amidst Geopolitical And Economic Uncertainty
Forrester’s 2026 report warns that CISOs now operate amid heightened geopolitical conflict, economic volatility and AI‑driven attack surfaces. It urges security leaders to embed AI protection in core budgets, streamline overlapping controls, and adopt visible change‑leadership practices. The report also...