Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Next.js CVE‑2025‑55182 Exploited to Breach 766 Hosts and Steal Cloud Credentials
Cisco Talos confirmed that threat cluster UAT‑10608 leveraged the CVSS 10.0 Next.js remote code execution bug (CVE‑2025‑55182) to compromise 766 hosts worldwide. Attackers harvested cloud access keys, SSH keys and API tokens, exposing entire cloud estates of affected organizations.

AI Agent Rush Ignites Security Gaps and Data Risks
Rapid adoption of AI agents without proper safeguards is leading to exposed systems, data risks, and increased opportunities for attackers to exploit access controls. https://t.co/HE5t3QmHqC

Unauthorized Group Has Gained Access to Anthropic’s Exclusive Cyber Tool Mythos, Report Claims
Anthropic’s newly announced AI cybersecurity tool, Mythos, was reportedly accessed by an unauthorized group through a third‑party vendor. The breach was uncovered after members of a Discord channel posted screenshots and a live demo of the tool. Anthropic says no...

Mozilla Fixes 271 Firefox Bugs Using Anthropic Mythos
Mozilla scanned the Firefox codebase with Anthropic Mythos has fixed 271 vulnerabilities identified during this initial evaluation. https://blog.mozilla.org/en/privacy-security/ai-security-zero-day-vulnerabilities/
Enterprises Are Ramping up Preparations for a Post-Quantum World – Experts Worry It Could Be Too Late for Many
Post‑quantum computing adoption is accelerating, with Juniper Research projecting users to rise from 35,000 this year to over 100 million by 2035, yet only 27% of firms plan to implement quantum‑secure safeguards in time. Google now predicts quantum computers capable of...

UK Intelligence: 100 Nations Have Spyware that Can Hack Britain
The UK National Cyber Security Centre (NCSC) warns that roughly 100 countries have bought cyber‑intrusion software capable of targeting Britain’s infrastructure, businesses, and private networks. The commercial spyware market, exemplified by tools like Pegasus and Predator, has broadened its focus...

Guilt Admitted by British Hacker in $8M Crypto Theft Scheme
British hacker Tyler Buchanan pleaded guilty to a scheme that stole at least $8 million in cryptocurrency from U.S. victims, targeting roughly 12 companies across virtual‑currency, technology, telecom and entertainment sectors between September 2021 and April 2023. Prosecutors say he and co‑conspirators used...

Unpatched AI Flaw Poses Risk to Banking Sector
Security firm OX Security uncovered a critical flaw in Anthropic's Model Context Protocol (MCP) that lets AI agents execute arbitrary host‑machine commands via the default "stdio" setup. Anthropic has declined to patch the underlying code, placing the onus on developers—particularly...

Over 400K Records Allegedly Stolen From Major Dutch Webshop Bol, Data Leaked
A hacker using the alias “Jeffrey Epstein” claims to have stolen data on over 400,000 Belgian customers of Dutch e‑commerce giant Bol. The alleged dataset includes names, birthdates, contact details, shipping information and order history, though passwords and bank data are...

Crypto Stealing Wallet Apps Proliferate in Apple App Store
A wave of 26 counterfeit crypto‑wallet apps masquerading as Coinbase, MetaMask, OneKey and Trust Wallet surfaced in the Apple App Store. The apps redirected users to phishing pages that installed malicious provisioning profiles, enabling the theft of mnemonic seed phrases....
Microsoft Teams, Quick Assist Weaponized in Helpdesk Spoofing Intrusions
Threat actors are weaponizing Microsoft Teams and Quick Assist in a new help‑desk impersonation campaign. Attackers send spoofed Teams messages that convince users to approve a Quick Assist session, granting the intruder full control of the device within minutes. Once...

Novel Malware Campaign Bundles Gh0st RAT, CloverPlus Adware
A new malware campaign combines the Gh0st RAT remote‑access trojan with CloverPlus adware to monetize infected PCs while maintaining long‑term control. Attackers use an obfuscated loader that first installs CloverPlus to display ads and generate click revenue, then deploys a...

Whistleblower Says CIA Hid 2020 Election Threats To Help Biden
A declassified National Intelligence Council memo from January 2020 warned that foreign adversaries could exploit voter registration databases and other election infrastructure. Former cyber official Christopher Porter alleges the CIA suppressed the memo after President Trump ordered its public release,...

Ransomware Negotiator Pleads Guilty to BlackCat Scheme
Angelo Martino, a former ransomware negotiator at a US incident‑response firm, pleaded guilty to conspiring with the BlackCat/ALPHV ransomware gang to steal confidential negotiation data and facilitate extortion attacks in 2023. Together with two other cybersecurity professionals, he helped deploy...

$293M KelpDAO Crypto Heist Exposes Cross-Chain Weaknesses in DeFi
A coordinated attack stole roughly $293 million worth of rsETH from KelpDAO, a liquid restaking protocol on Ethereum. The thieves compromised RPC nodes and flooded the network with DDoS traffic, corrupting LayerZero’s cross‑chain verification and allowing fraudulent transfers. The stolen tokens...

The Missing Layer in Federal Data Protection
Federal agencies have long secured data at rest and in transit, but data in use remains vulnerable. Confidential computing, built on trusted execution environments (TEEs), encrypts memory and isolates workloads, offering a third layer of protection. The technology is already...

How Zero Networks Is Closing the Network Enforcement Gap for AI Agents
Zero Networks, founded in 2019, offers an agentless, automated microsegmentation platform that eliminates manual policy creation. The solution discovers assets via directories and third‑party tools, then enforces label‑based policies using native firewalls and switch ACLs. Its new AI Segmentation feature...

Thousands of Apache ActiveMQ Instances Still Unpatched, Weeks After an Actively Exploited Hole Discovered
Researchers at Horizon3.ai used Anthropic's Claude AI to uncover a remote code execution flaw (CVE‑2026‑34197) in Apache ActiveMQ within ten minutes. The vulnerability affects versions before 5.19.4 and 6.0‑6.2.2, exposing nearly 6,500 internet‑facing instances two weeks after disclosure. CISA has...

Murder, She Wrote: Ex-FBI Chief Wants some Ransomware Crims Charged with Homicide
Former FBI cyber‑division deputy chief Cynthia Kaiser urged the Justice Department to treat ransomware attacks on hospitals as felony murder, citing at least 47 deaths between 2016 and 2021 and likely hundreds today. She called on State, Justice and Treasury...

American College of Radiology Offers Cybersecurity Resources
The American College of Radiology (ACR) has unveiled a suite of cybersecurity resources, including a joint white paper with the Society for Imaging Informatics in Medicine (SIIM) that replaces its prior practice parameter, and an online Cybersecurity Hub that aggregates...

NIST Scales Back CVSS Scoring as CVE Submissions Surge 263% Since 2020
The National Institute of Standards and Technology announced it will scale back its Common Vulnerability Scoring System (CVSS) enrichment, citing a 263% jump in CVE submissions from 2020 to 2025. The change forces security teams to rely more on internal...

UWB Chips Stop Key‑fob Spoofing, Secure Cars
Car thieves don't just pick locks to break in. They've also found ways to spoof your key fob's "unlock" signal. No glass broken, no button pressed. But new UWB car security chips fight back with new tech that's tougher to...

XRP Ledger to Be Quantum-Proof Years Before Bitcoin
Ripple announced a hard deadline to make the XRP Ledger quantum‑proof by 2028, positioning it years ahead of the industry’s estimated "Q‑Day" in the 2030s. The roadmap, detailed by senior director Ayo Akinyele, outlines cryptographic upgrades that will protect the...

HHS Watchdog Advises CIOs to Secure Data Before AI Implementation
The HHS Office of the Inspector General warned federal CIOs that AI projects must be preceded by robust data‑security controls. Agencies are urged to adopt operational AI governance, drawing on NIST guidance, and to shift from static policies to real‑time...

Why Microsoft Is Betting on Temporary Identities to Stop Autonomous Agents From Going Rogue
Microsoft is introducing temporary, scoped identities for AI agents running on Azure Kubernetes Service, ensuring agents receive only the permissions needed for a specific task before automatic revocation. At KubeCon Europe 2026, the company demoed an agent that diagnosed and...

Hackers Reconstructed a Wrecked Car’s Every Move Using a Single Computer Module
White‑hat researchers extracted a telematics module from a wrecked BYD Seal and, because the memory was unencrypted, reconstructed the car’s complete GPS history from factory departure in China to its final crash in Poland. Using a simple USB flash tool...

New Lotus Data Wiper Used Against Venezuelan Energy, Utility Firms
Kaspersky has identified a previously unknown data‑wiping malware called Lotus that was deployed in late 2025 against Venezuelan energy and utility firms, including the state‑owned oil giant PDVSA. The attack begins with two batch scripts that disable Windows services, alter...

Mozilla Used Anthropic’s Mythos to Find and Fix 151 Bugs in Firefox
Mozilla announced that its Firefox 150 release incorporates fixes for 151 bugs and patches 271 vulnerabilities discovered with early access to Anthropic’s Mythos Preview AI model. The collaboration allowed the Firefox team to automate a broader search of the codebase, uncovering...

AES-128 Will Survive Cryptographically Relevant Quantum Computers
Ars Technica reports that AES‑128 encryption remains robust even against cryptographically relevant quantum computers. The analysis shows Grover’s algorithm provides only a quadratic speedup, and its advantage shrinks when the attack is parallelized across multiple quantum processors. Consequently, the effective...
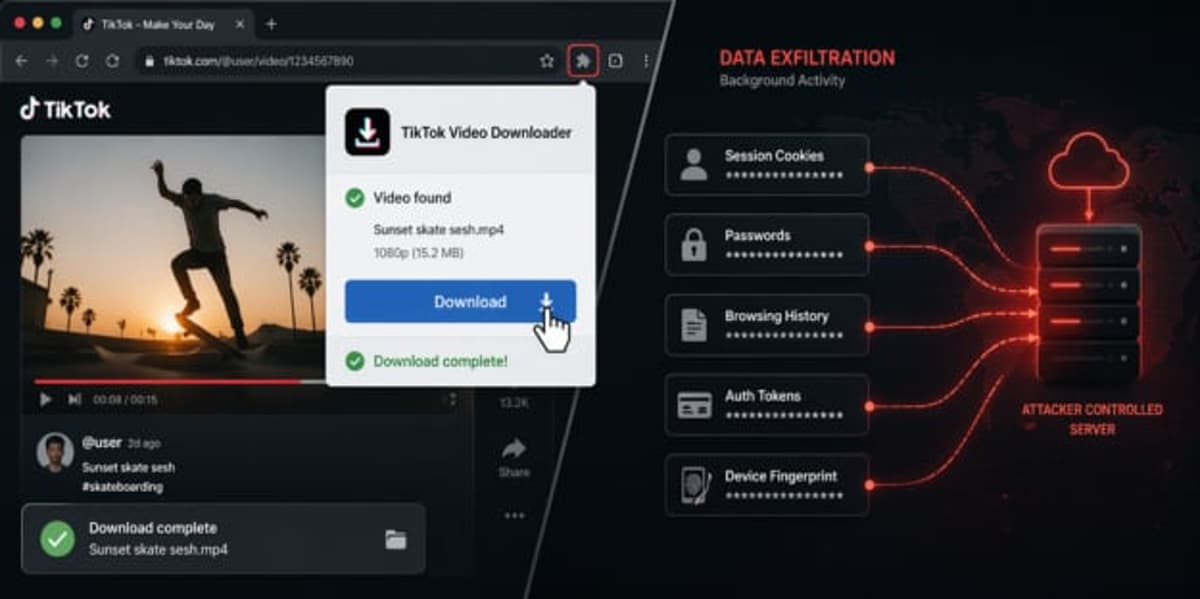
130K Users Compromised by StealTok Campaign That Uses Fake TikTok Downloaders
The StealTok campaign deployed malicious browser extensions masquerading as TikTok video downloaders, compromising more than 130,000 users. Listed in Chrome and Edge stores—some even featured—the extensions remained dormant for six to twelve months before activating data‑stealing functions via attacker‑controlled remote‑config...

FedRAMP and CMMC Compliance Deadlines Are Looming
Federal cloud and defense contractors face two critical compliance milestones before the end of 2026. FedRAMP requires vendors to submit machine‑readable authorization packages by September 30 2026 and to fully adopt NIST SP 800‑53 Revision 5 controls by September 30 2027. The Department of Defense’s CMMC...
Microsoft Vulnerabilities Drop, But Critical Flaws Double, Report Warns
BeyondTrust’s 13th Microsoft Vulnerabilities Report shows a 6% drop in total flaws to 1,273 this year, but critical vulnerabilities have doubled. Office suite bugs tripled, with a ten‑fold rise in critical issues, while Azure and Dynamics 365 saw nine times more...

Nation States Responsible for ‘Nationally Significant’ Cyber Attacks Against UK, Says NCSC Chief
The UK’s National Cyber Security Centre (NCSC) warned that hostile nation‑states are now behind the majority of "nationally significant" cyber attacks, averaging four incidents per week. Russia, China and Iran are adapting wartime tactics and leveraging sophisticated AI tools, such...

Open‑source CrabTrap Secures AI Agents with Policy‑Based Proxy
Brex just open-sourced CrabTrap. A transparent HTTP proxy that sits between your AI agent and every external API it calls. Okta, but for agents. AI agents in production are getting real credentials now. API keys. OAuth tokens. Database access. Write privileges to...

Tight Controls Needed to Prevent Mythos Abuse
A lab leak on their hands here. We don't want adversaries using Mythos to expedite the drop of 0days and other malicious AI-powered attacks. Without tight controls, we're may sadly see Mythos used for evil before we get to see everything...

What Is the 3-2-1 Backup Rule?
The 3-2-1 backup rule advises keeping three copies of data, using two different storage media, and storing one copy offsite. Originating from tape‑based eras, the principle remains a cornerstone of data protection. Modern businesses apply it with a mix of...

AI-Driven Pushpaganda Tricks Users with Malicious Notifications
Pushpaganda uses AI-generated content and deceptive tactics to trick users into enabling notifications that deliver scams and evade traditional security defenses. https://t.co/x8sjalWKPR

AI-Driven Research Will Shrink Attackers' Zero‑Day Arsenal
Sunlight seen through the storm. Mozilla security researchers say that after this wave of AI-augmented vuln discovery and exploitation, we'll reach a new equilibrium in which there are *fewer* vulns being used by attackers. “The zero-days are numbered”—https://t.co/MM5SNBJsjD

Aave Partially Unfreezes WETH After Kelp Bridge Exploit
Aave announced on April 21 that it has unfrozen wrapped ETH (WETH) supplies on its Ethereum Core V3 market, reversing a 24‑hour freeze triggered by the $290 million Kelp bridge exploit. The protocol kept WETH’s loan‑to‑value ratio at zero, preventing its...

Shielded Labs Boosts Zcash Security for Users
We at Shielded Labs have been working hard alongside others to urgently defend users and strengthen Zcash's security (https://t.co/GEDJVifGlc) …

Iran Blames US for Coordinated Network Shutdowns
Iranian media is reporting that networking infrastructure suffered coordinated shutdowns, and blames the US. https://t.co/Gil1Z55HhM

R26774 - MTS- Information Security & Business Continuity M…
Euronext’s MTS SpA is hiring a permanent Information Security & Business Continuity Manager in Milan to lead security and resilience initiatives for its electronic fixed‑income trading platform. The role will implement the Euronext Security Programme and Business Continuity Management Programme, ensuring...

Seiko Hasn't Confirmed Breach; Data Not on Dark Web
Seiko has not yet confirmed the incident and the data has not surfaced on the dark web. https://t.co/QqdC9km6on

Network‑layer Containment Stops Ransomware Before CAD Fails
Ransomware doesn’t announce itself. By the time CAD drops, the spread has already started. Containment at the network layer is what keeps dispatch online. @T_Priority Partner https://t.co/qHmY69QqfA

Auto Dealerships Pressed to Bolster Cybersecurity as Threats Surge
Cybersecurity consultants are urging auto dealerships to upgrade defenses as cybercriminals target the industry’s trove of customer and financing data. Sean Patronis of Proton Dealership IT stresses that in‑house teams alone can’t keep pace with sophisticated attacks, and recommends augmenting...

Second Coding Vibe: Security Prediction App Nears Functional
So my 2nd vibe coding experience is about building an app to do security prediction validation. My v0.3 kinda works (but has annoying issues, obviously). (1/n)

DeFi Security: Beyond Audits, Chasing Endless Dependencies
☠️ "You can have a million audits, but now it's about the dependencies on oracles and bridges and collateral and multisig configurations and operational security practices. It feels like you're just playing whac-a-mole." -- @TuongvyLe12 on all the DeFi hacks https://t.co/PvhRjgnJGF

Analysis Confirms Quantum Computers Won’t Undermine 128‑Bit Symmetric Encryption
A new analysis on the cryptography blog words.filippo.io refutes the widespread belief that quantum computers halve the security of symmetric keys, confirming that AES‑128 and SHA‑256 retain their strength. The piece explains why Grover’s algorithm does not provide a practical...

Mastodon’s Flagship Instance Hit by DDoS Attack, Service Disrupted
Mastodon reported that its flagship mastodon.social instance was hit by a distributed denial‑of‑service attack at around 7 a.m. ET on Monday, forcing the site offline until a countermeasure was deployed at 9:05 a.m. ET. The incident underscores operational vulnerabilities for open‑source, decentralized...

Microsoft Warns of Cross‑tenant Teams Helpdesk Impersonation Attacks Targeting MFA Tokens
Microsoft announced a new human‑operated intrusion playbook that leverages cross‑tenant Microsoft Teams chats masquerading as IT helpdesk messages. The tactic sidesteps traditional email gateways, aims at MFA approval tokens and privileged accounts, and forces security teams to rethink SaaS perimeter...