Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Interview: Critical Local Infrastructure Is Missing Link in UK Cyber Resilience
Jonathan Lee, TrendAI’s cyber‑strategy director, warns that UK local infrastructure—councils, social‑care and transport—remains a blind spot in cyber‑resilience planning. While the Cyber Security and Resilience Bill targets national services such as health and energy, municipal systems lack mandatory safeguards and often ignore the NCSC’s voluntary Cyber Assurance Framework. Lee cites the risk of simultaneous attacks that could cripple public services and ripple into the NHS. The government’s upcoming Cyber Action Plan and updated Cyber Essentials programme aim to close the gap, but implementation remains uncertain.

Who’s Really to Blame When a White Hat Goes Gray?
A security researcher, frustrated by a slow and dismissive vulnerability disclosure process, released exploit code publicly, endangering customers. The company’s compliance team labeled the researcher a villain, while the author questions whether firms have an ethical duty to maintain respectful,...

UK Faces ‘Perfect Storm’ for Cybersecurity, Says Cyber Chief
At the CYBERUK conference, NCSC chief Richard Horne warned that the UK faces a "perfect storm" of cyber risk driven by rapid AI advances and heightened geopolitical tension. While the total number of incidents reported to the centre remains steady,...

Hackers Steal Customer Data From Rituals
Cosmetics retailer Rituals announced a data breach that exposed customer names, email addresses and dates of birth across up to five countries. The intrusion did not compromise passwords or payment information, and the company says it swiftly blocked the illegal...

North Korean Hackers Use AppleScript, ClickFix in Fresh macOS Attacks
North Korean state‑linked groups have launched two macOS‑focused campaigns against financial firms. One uses the ClickFix technique, tricking executives into running a Terminal command that installs the Go‑based Mach‑O Man malware. A second, attributed to Sapphire Sleet, leverages compiled AppleScript files to...

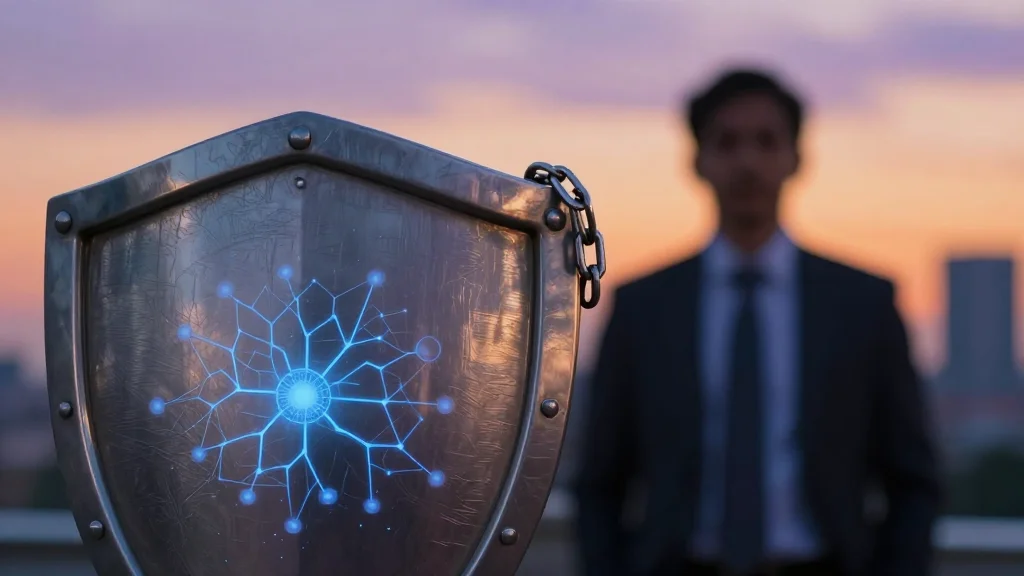
UK to Build ‘National Cyber Shield’ to Protect Against AI Cyber Threats
The UK government announced a "national cyber shield" to defend against AI‑powered cyber attacks, calling for close cooperation between AI firms and public agencies. Security Minister Dan Jarvis highlighted that the National Cyber Security Centre dealt with over 200 nationally...
Toxic Combinations: When Cross-App Permissions Stack Into Risk
On Jan. 31 2026 researchers revealed that Moltbook, an AI‑agent social network, left its database exposed, leaking 35,000 email addresses and 1.5 million agent API tokens. Private messages also contained plaintext third‑party credentials, including OpenAI API keys stored alongside the tokens. The breach...

Anthropic’s Mythos Under Fire as OpenAI Attacks Its Marketing and Unauthorised Users Breach the Model
Anthropic’s restricted cybersecurity AI, Mythos, faced a turbulent week after OpenAI CEO Sam Altman labeled its limited rollout as “fear‑based marketing.” The model, offered to roughly 40 firms under Project Glasswing, was reportedly accessed by unauthorized users through a third‑party vendor...

CyberSmart Partners with Renaissance to Deliver Complete Cyber Confidence for SMEs
Irish reseller Renaissance has entered a strategic partnership with UK‑based CyberSmart to bring its continuous‑protection platform to small and medium‑sized enterprises. The solution delivers real‑time threat detection, automated patching, vulnerability management and compliance automation across desktop and mobile devices. It...

Brace Yourself for a Flood of Patches in All of Your Tech Gadgets
Anthropic unveiled Mythos, its most powerful AI model, capable of automatically identifying hidden software vulnerabilities across operating systems and browsers. The company has granted early access to 40 leading tech firms, including Apple, Google, and Amazon, to remediate flaws such...

Seiko USA Website Defaced; Hackers Claim Theft of Entire Customer Database and Demand 72‑hour Ransom
Seiko USA's U.S. website was defaced over the weekend with a fake “HACKED” page that alleges attackers accessed its Shopify backend and stole the entire customer database. The threat actors gave the company 72 hours to begin ransom negotiations, while...

Researchers Uncover ProxySmart Software Powering 90+ SIM Farms
Infrawatch researchers identified a Belarus‑originated software platform, ProxySmart, operating 87 control panels across 17 countries and supporting 94 SIM farms in 19 U.S. states. The platform offers a turnkey “SIM Farm as a Service” solution, handling device management, automated IP...
The AI Era Demands a Different Kind of CISO
The article argues that traditional CISO frameworks—focused on audits, static vulnerability checks, and compliance—are obsolete in an AI‑driven threat environment. AI models can discover and exploit weaknesses in minutes, outpacing legacy risk metrics that capture only past conditions. To stay...

New GoGra Malware for Linux Uses Microsoft Graph API for Comms
Symantec discovered a new Linux variant of the GoGra backdoor that uses Microsoft Graph API to communicate with a hijacked Outlook mailbox. The malware authenticates with hard‑coded Azure AD credentials, retrieves OAuth2 tokens, and polls a folder named “Zomato Pizza”...

Deadly Deepfakes: A Survival Guide for the Age of Algorithmic War
Artificial intelligence is now a dual‑edged weapon in modern conflicts, powering both precision targeting and the rapid creation of deepfake footage. In the recent U.S.–Israel confrontation over Iran, AI‑generated videos of burning landmarks and missile strikes circulated widely, blurring reality...

Another DeFi Protocol Hacked as Sui-Based Volo Hit by $3.5M Exploit
DeFi liquid‑staking platform Volo on the Sui blockchain disclosed a security breach that stole roughly $3.5 million from three isolated vaults. The protocol quickly froze about $2 million of the stolen assets, including blocking a bridge attempt of 19.6 WBTC (≈$590 k). Around $28 million...

Google Antigravity in Crosshairs of Security Researchers, Cybercriminals
Google’s Antigravity, an AI‑agent development platform powered by Gemini, has drawn attention from both security researchers and cybercriminals. Pillar Security uncovered a sandbox‑escape vulnerability that allowed remote code execution, which Google patched in late February 2026. Separately, Malwarebytes reported a...

A&K Travel Journeys with Colt for Global Quantum-Safe Network
Travel operator A&K Travel Group has partnered with Colt Technology Services to build a global, quantum‑safe network for its portfolio of luxury travel brands. The solution incorporates Arqit’s quantum‑resistant encryption, enabling secure, low‑latency connectivity across more than 100 countries, including...

Sendmarc Review: Features, User Experiences, Pros & Cons (2026)
Sendmarc is an email‑authentication platform that streamlines DMARC, SPF and DKIM deployment through guided workflows and managed support. Pricing starts at $45 per month, with hosted DNS services reserved for Premium and Enterprise tiers. The solution targets mid‑size firms, enterprises and...
Visibility-Led Security Key to Pre-Emptive Defence: Exclusive Networks
Exclusive Networks is sponsoring the ITWeb Security Summit 2026 in Johannesburg to engage Africa’s cyber‑security ecosystem. The event will feature an Infoblox workshop that demonstrates how deep visibility into everyday internet traffic can reveal compromised devices, command‑and‑control activity and data...

How Energy Medicine Yoga Reached 57% Open Rates and Simplified BIMI Implementation with EasyDMARC
Energy Medicine Yoga, a global wellness brand, partnered with EasyDMARC to overhaul its email authentication and adopt Brand Indicators for Message Identification (BIMI). The managed BIMI service guided the non‑technical team through DMARC enforcement, VMC acquisition, logo preparation, and DNS...

Anthropic Bets on EPSS for the Coming Bug Surge
Anthropic introduced Mythos, an AI model that can discover software flaws at unprecedented speed, intensifying the existing vulnerability overload. To help defenders prioritize, Anthropic advises using the Exploit Prediction Scoring System (EPSS), a probabilistic model that forecasts exploitation likelihood within...

Exclusive: OpenAI Briefs Feds and Five Eyes on New Cyber Product
OpenAI has begun briefing U.S. federal agencies, state governments, and Five Eyes allies on its new GPT‑5.4‑Cyber model, a large‑language‑model designed for advanced cybersecurity tasks. The company demonstrated the tool to about 50 cyber‑defense practitioners in Washington, D.C., and announced...
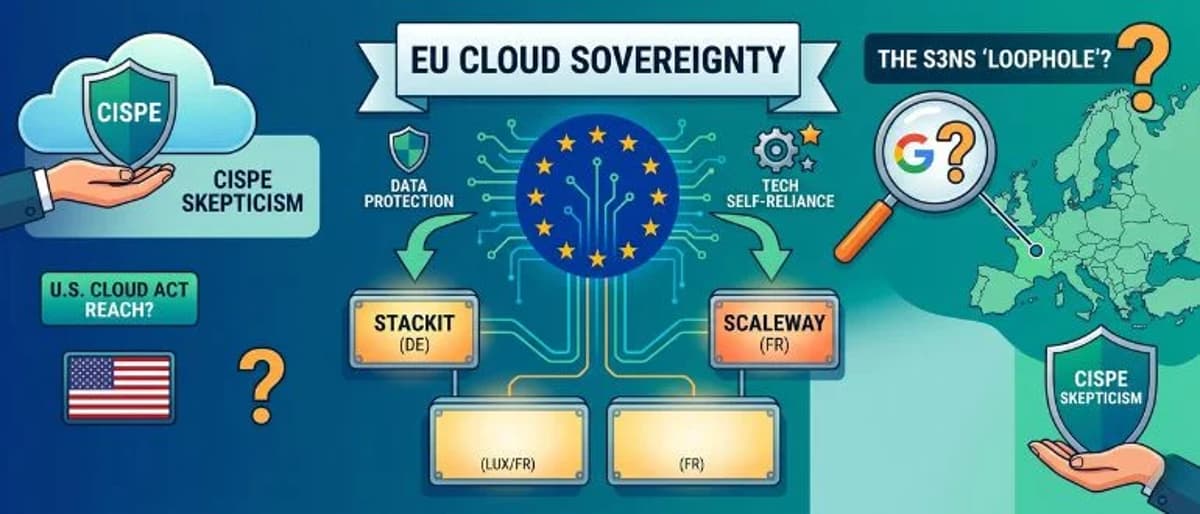
European Commission Awards New Sovereign Cloud Contracts To ‘Mostly’ EU Clouds
The European Commission has signed four sovereign‑cloud contracts worth about €180 million ($210 million) over six years, aiming to keep public‑sector data inside the EU and curb reliance on non‑European hyperscalers. The deals target German provider STACKIT, French provider Scaleway, a Franco‑Luxembourg...

Default BitLocker Configuration Isn’t Enough: Defending Endpoints Against Physical Attacks
Physical‑access attacks on laptops are becoming commonplace as employees work from cafés, airports and hotels. While many enterprises rely on BitLocker’s default TPM‑only configuration to encrypt drives, researchers have shown that TPM‑bus snooping can capture the decryption key in under...

March 2026 Cyber Threat Landscape Fueled by Ransomware, Breaches, and Access Markets
In March 2026 the global cyber threat landscape intensified, with CRIL reporting 702 ransomware incidents—56% of which were driven by five prolific groups such as Qilin and Akira. The month also saw 20 access‑broker listings, a growing underground market that...

Oracle Patches 450 Vulnerabilities With April 2026 CPU
Oracle issued its April 2026 Critical Patch Update, delivering 481 security patches that address roughly 450 CVEs across 28 product families. More than 300 of the fixes target vulnerabilities that can be exploited remotely without authentication, and about three dozen are...

Silverfort and SentinelOne Partner to Tackle AI-Era Identity Security
Silverfort and SentinelOne announced a partnership that merges Silverfort’s identity discovery and runtime enforcement with SentinelOne’s AI‑powered Singularity Platform. The joint solution extends real‑time protection to human users, machine identities and autonomous AI agents, enabling automatic detection, blocking and isolation...

Podcast: Inside the $9 Billion DeFi Hack That’s Shaking Crypto’s Foundations
The Kelp DAO decentralized finance platform suffered a $292 million cross‑chain restaking exploit on April 18, sparking a chain reaction that erased roughly $9 billion from the sector’s largest DeFi lending protocol. Unlike prior attacks that targeted private keys or smart‑contract bugs, the...

Connected and Secure: Building BAS Across Legacy, Hybrid, and Cloud Networks
At AHR Expo 2026, industry leaders warned that building automation systems (BAS) are rapidly shifting from legacy architectures to hybrid and cloud‑connected models, making cybersecurity a foundational requirement. The panel highlighted the convergence of IT and OT, the risks of...

Today’s Regulatory Intelligence Solutions Replace Drudgery With Confidence
Volatility in the B2B landscape is now the norm, driving leaders to seek smarter compliance tools. Over 170 countries have introduced cybersecurity and data‑protection laws, overwhelming security and risk teams with manual research. Forrester’s 2026 study shows regulatory intelligence platforms...

Inside Rhino’s Push to Make Privacy-Preserving AML Collaboration Work
Rhino Federated Computing, a Massachusetts startup founded in 2021, offers a privacy‑preserving AI stack that lets banks run anti‑money‑laundering (AML) models where their data resides. By training locally and sharing only encrypted model updates, institutions avoid moving raw transaction records...

AI Drives Surge in ‘Bug Bounty’ Reports, but ‘Slop’ Is Rising Too
Bug bounty programs across the crypto and open‑source sectors are experiencing a dramatic surge driven by AI tools that can quickly generate vulnerability reports. Cosmos Labs reported a 900% increase in submissions, averaging 20‑50 daily, while HackerOne logged 85,000 valid...

South Korea Expands AI Cybersecurity to Safeguard Cloud-Based Education Systems
South Korea’s Ministry of Education and KERIS are expanding an AI‑driven cybersecurity platform to protect private‑cloud environments used by schools and universities. The AI‑based Automated Cyber Intrusion Detection and Notification System recorded roughly 480 million threat indicators in 2025, confirming 86 000...

A Tsunami of Flaws: When Frontier AI and Patch Tuesday Collide
Microsoft’s April 2026 Patch Tuesday released over 160 vulnerabilities, the second‑largest monthly batch on record. The surge coincides with the debut of Anthropic’s frontier‑model AI, Mythos, under Project Glasswing, which claims to discover thousands of zero‑days. Experts warn that AI‑driven bug...

Hotline: Cybersecurity and Privacy | April 2026
Michael Corn’s April 2026 column tackles three pressing higher‑education security dilemmas: AI‑enabled cheating, drastic cybersecurity budget cuts, and audit‑driven heroics. He argues that multi‑factor authentication alone cannot stop AI‑driven fraud and proposes a five‑layer defense spanning identity, device context, behavioral...
The Security Metric That’s Failing You
Security teams have let patch‑rate metrics become the de‑facto strategy, but clean patch reports hide far greater risks such as misconfigurations, stale permissions, and legacy network segments. The window for exploiting a disclosed vulnerability has collapsed from weeks to roughly...

Think You’re Not A Data Broker? California’s Delete Act Might Say Otherwise
California’s Delete Act now forces any business that collects and sells consumer data without a direct relationship to register as a data broker with the California Privacy Protection Agency. Starting August 1 2026, registered brokers must process deletion requests through the new...

Think You’re Not A Data Broker? California’s Delete Act Might Say Otherwise
California’s Delete Act now forces any business that collects and sells consumer data without a direct relationship to register as a data broker with the CPPA. Starting August 1, 2026, registered brokers must process deletion requests through the new Delete Request and...

2Apply Raked for 'Dark Patterns' Used to Snare Renters' Data
Australian privacy regulator OAIC ruled that 2Apply, the nation’s largest rent‑tech platform, employed dark‑pattern design tricks to pressure prospective tenants into providing excessive personal data. The commissioner identified tactics such as “confirmshaming” and bundled consent that misled users about the...

User Login Causing Problems: Unexpected Tag Write or Trigger
Industrial automation systems are seeing safety risks when user login events unintentionally write to PLC tags. Poorly designed SCADA scripts, shared UI‑control tags, and mishandled retentive bits can cause equipment to start, reset, or trip without operator intent. The article...

Japan Finance Minister Meets Banks on Claude Mythos Cyber Threat
JUST IN: Japan's finance minister is holding talks with major banks to tackle cybersecurity threats from Claude Mythos.

TekStream Acquires ImagineX Cybersecurity Business in $0 Deal to Consolidate Digital Resilience
TekStream announced the acquisition of ImagineX's cybersecurity business, adding Cyber Strategy, vCISO, GRC, CTEM and IAM capabilities to its portfolio. The deal, disclosed on April 21, 2026, aims to deliver single‑owner accountability for cyber risk and reflects accelerating consolidation in...

China Cyber‑spies Western Defense Firms, Dutch Intel Warns
China’s Cyberspying Targets Western Defense Industry, Dutch Intel Chief Says—Military intelligence report warns China poses a growing threat, alongside Russia @kimmackrael @DanMichaelsWSJ https://t.co/cu728ldZmp https://t.co/cu728ldZmp

Sekuro, The Missing Link Celebrated as Top CrowdStrike JAPAC Partners for 2026
CrowdStrike announced that Sekuro, an Insight company, and The Missing Link, an Infosys affiliate, were named among its top-performing partners in the Japan and Asia‑Pacific (JAPAC) region for 2026. Sekuro secured the JAPAC Partner of the Year award for the...

ServiceNow Seals $7.75 Bn Deal for Cyber‑exposure Leader Armis
ServiceNow has closed a $7.75 bn cash acquisition of Armis, a cyber‑exposure management firm. The deal adds real‑time, agent‑less monitoring of billions of connected devices to ServiceNow’s workflow platform, reinforcing its push into security after the earlier Veza purchase.

Lattice-Based Signature Schemes for MCP Host Authentication
Lattice‑based signature schemes, especially the ML‑DSA (Dilithium) family, are emerging as the quantum‑resistant alternative to RSA and ECDSA for Model Context Protocol (MCP) host authentication. The article explains how module‑LWE and module‑SIS underpin these schemes, delivering verification times under 30 ms...

AI Agent Rush Ignites Security Gaps and Data Risks
Rapid adoption of AI agents without proper safeguards is leading to exposed systems, data risks, and increased opportunities for attackers to exploit access controls. https://t.co/HE5t3QmHqC

Next.js CVE‑2025‑55182 Exploited to Breach 766 Hosts and Steal Cloud Credentials
Cisco Talos confirmed that threat cluster UAT‑10608 leveraged the CVSS 10.0 Next.js remote code execution bug (CVE‑2025‑55182) to compromise 766 hosts worldwide. Attackers harvested cloud access keys, SSH keys and API tokens, exposing entire cloud estates of affected organizations.

Unauthorized Group Has Gained Access to Anthropic’s Exclusive Cyber Tool Mythos, Report Claims
Anthropic’s newly announced AI cybersecurity tool, Mythos, was reportedly accessed by an unauthorized group through a third‑party vendor. The breach was uncovered after members of a Discord channel posted screenshots and a live demo of the tool. Anthropic says no...