130K Users Compromised by StealTok Campaign That Uses Fake TikTok Downloaders
Why It Matters
The incident shows how trusted browser extensions can evolve into persistent data‑exfiltration tools, forcing enterprises to tighten extension governance and adopt zero‑trust controls.
Key Takeaways
- •130K+ users infected by fake TikTok downloader extensions.
- •Extensions stayed hidden for up to a year before activating.
- •Remote‑config servers let attackers change behavior without store updates.
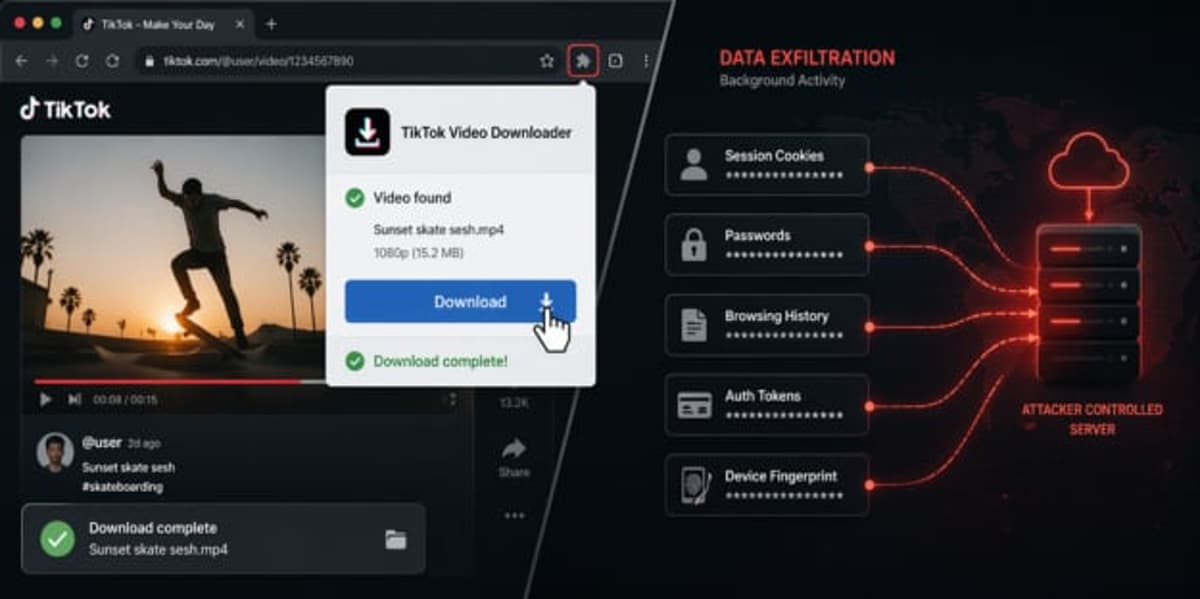
- •Broad permissions expose session tokens, device fingerprints, and browsing data.
- •Zero‑trust and strict allowlists are essential defenses.
Pulse Analysis
Browser extensions have long been marketed as convenience tools, but their elevated privileges make them attractive attack surfaces. Over the past few years, major browsers have struggled to balance open ecosystems with security, allowing thousands of extensions into official stores. The StealTok operation exploits this tension, slipping past automated reviews by offering a legitimate TikTok video downloader while embedding a hidden codebase that can be reprogrammed after installation. This model mirrors the broader shift toward supply‑chain attacks, where initial legitimacy masks later malicious intent.
StealTok’s tactics are noteworthy for their patience and adaptability. By remaining inert for up to a year, the extensions built user trust and accumulated a sizable install base before triggering covert tracking and data‑exfiltration modules. Remote configuration servers enable attackers to push new capabilities without triggering store updates, effectively sidestepping traditional review processes. The harvested data—device characteristics, language settings, battery status, and session tokens—creates a rich fingerprint that can be leveraged for targeted phishing, credential theft, or cross‑service tracking, amplifying the risk beyond the browser itself.
Mitigating this threat requires a multi‑layered approach. Enterprises should enforce strict allowlists, limiting extensions to vetted, business‑critical tools and applying least‑privilege permissions. Continuous telemetry integration with SIEM and XDR platforms can flag anomalous network calls or permission changes in real time. Coupling these controls with a zero‑trust mindset—verifying every extension’s behavior post‑deployment—reduces the attack surface and ensures that trusted platforms do not become covert conduits for data theft. As attackers refine post‑install manipulation, proactive governance will be the decisive factor in protecting corporate browsers.
130K Users Compromised by StealTok Campaign That Uses Fake TikTok Downloaders
Comments
Want to join the conversation?
Loading comments...