Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

IOCTA 2026 Report Warns of Rising AI-Driven Cybercrime and Dark Web Threats
Europol’s Internet Organised Crime Threat Assessment 2026 warns that AI, encryption and cryptocurrencies are accelerating the sophistication of cybercrime across Europe. The report highlights a surge in AI‑generated phishing, fragmented dark‑web marketplaces and a shift toward data‑extortion ransomware. Child sexual‑exploitation networks are expanding using encrypted messaging and synthetic content. Europol calls for tighter law‑enforcement coordination and innovative investigative tools to counter these evolving threats.

Encryption, Proxies, AI Fuel Growing Cybercrime Threat
IOCTA 2026 – The evolving threat landscape: how encryption, proxies and AI are expanding cybercrime - Internet Organised Crime Threat Assessment (IOCTA) 2026 | Europol https://t.co/cAUHnrvjYT

Nigeria Moves to Mandate Organisations to Disclose Cyber Attacks Amid Rising Threats
Nigeria’s tech regulator, NITDA, announced that banks, fintechs and other organisations must disclose cyber‑breaches or at least share threat intelligence. The push follows a weak reporting record – only 37% of financial institutions filed fraud incidents in 2023 and fraud...

Hundreds of Internet-Facing VNC Servers Expose ICS/OT
Forescout’s latest research reveals that roughly 1.8 million RDP and 1.6 million VNC servers are exposed to the public internet, with a significant share linked to critical industries in the United States and China. Among these, 91 000 RDP and 29 000 VNC instances...

Hutt City Council Confirms Phishing Attack, Data of Hundreds Potentially Exposed
In March 2026 the Hutt City Council suffered a phishing attack that compromised email accounts, exposing identity details of five individuals and potentially financial information for up to 732 residents. The council swiftly secured the affected accounts, notified the Privacy...

How AI Boosts Cybersecurity Defenses
Artificial intelligence is reshaping cybersecurity by delivering real‑time anomaly detection, predictive analytics, automated response, and deeper forensic insight. The same technology also empowers threat actors with deepfakes, AI‑generated phishing, and self‑learning malware, creating a two‑sided sword. Experts advise firms to...
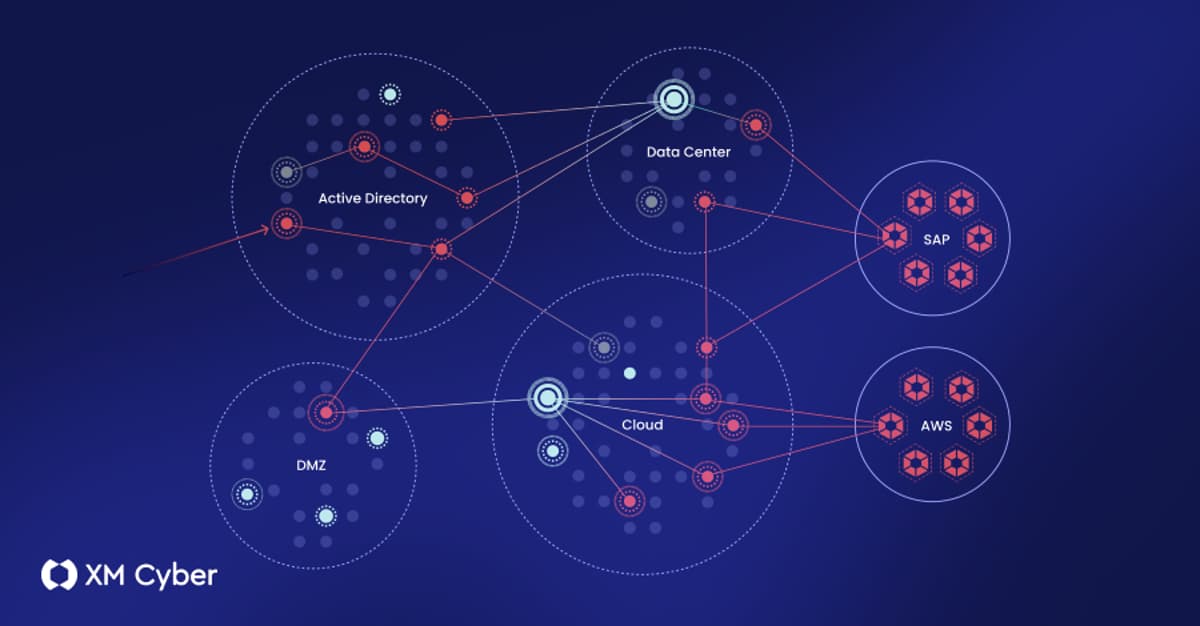
What to Look for in an Exposure Management Platform (And What Most of Them Get Wrong)
The article dissects exposure‑management platforms, outlining four architectural approaches—stitched portfolios, data aggregators, single‑domain specialists, and fully integrated solutions. It argues that only integrated platforms can correlate diverse exposure types, validate exploitability, and map realistic attack paths across on‑prem, cloud, and...

Ransomware Wipes Files over 128KB; Backups Essential
New ransomware variant destroys everything bigger than 128kb, making retrieval without a backup impossible. https://t.co/yeVN6pONet

North Korean Hackers Are Duping Freelance Developers with Fake Interviews to Steal Cryptocurrency and Deliver Malware — Sophos Warns the...
North Korean state‑backed group Nickel Alley is luring freelance developers through fake job interviews on platforms like Upwork, Fiverr and LinkedIn. The scheme convinces victims to download malicious npm packages or clone compromised GitHub repositories, installing the PyLangGhost RAT that...
Checkmarx Confirms Data Stolen in Supply Chain Attack
Checkmarx confirmed that a supply‑chain attack on its open‑source KICS project resulted in the theft of source code, employee data, API keys and a 96 GB archive. The breach originated from the Trivy supply‑chain compromise on March 23, 2026, which allowed the...

Your Phone Notifications Reveal More Than You Realize. Here’s How to Lock Them Down
The FBI recently extracted incoming Signal messages from an iPhone by exploiting the iOS notification database, even after the Signal app and its encrypted chats were deleted. Apple’s iOS 26.4.2 update now automatically purges expired notification logs, closing the specific loophole...

Iranian Cyber Group Handala Targets US Troops in Bahrain
Iran‑linked cyber group Handala escalated its campaign by targeting U.S. service members stationed in Bahrain, sending WhatsApp messages that threatened drone and missile strikes. The group also published personal data of 2,379 Marine Corps personnel and claimed responsibility for the...
Attack Path Visibility Concerns Outstrip AI Among Security Leaders
A recent study of cyber‑security leaders reveals that ransomware threats and the need for clear attack‑path visibility outrank the adoption of artificial‑intelligence solutions. Executives overseeing more than $100 billion in annual IT spend prioritize tools that map lateral movement and expose...

GitHub Patches Critical RCE Flaw in Enterprise Server, 88% Still Exposed
GitHub released emergency patches for CVE‑2026‑3854, a critical remote‑code‑execution vulnerability affecting its internal git infrastructure. While GitHub.com was fixed within six hours, 88% of GitHub Enterprise Server (GHES) installations remain vulnerable, forcing admins to upgrade to version 3.19.3 or later.

Workplace Apps Harvest Your Data and Sell It
Your personal data is being collected by your workplace app, and sometimes passed on to advertisers https://t.co/cZIU1lZZRT
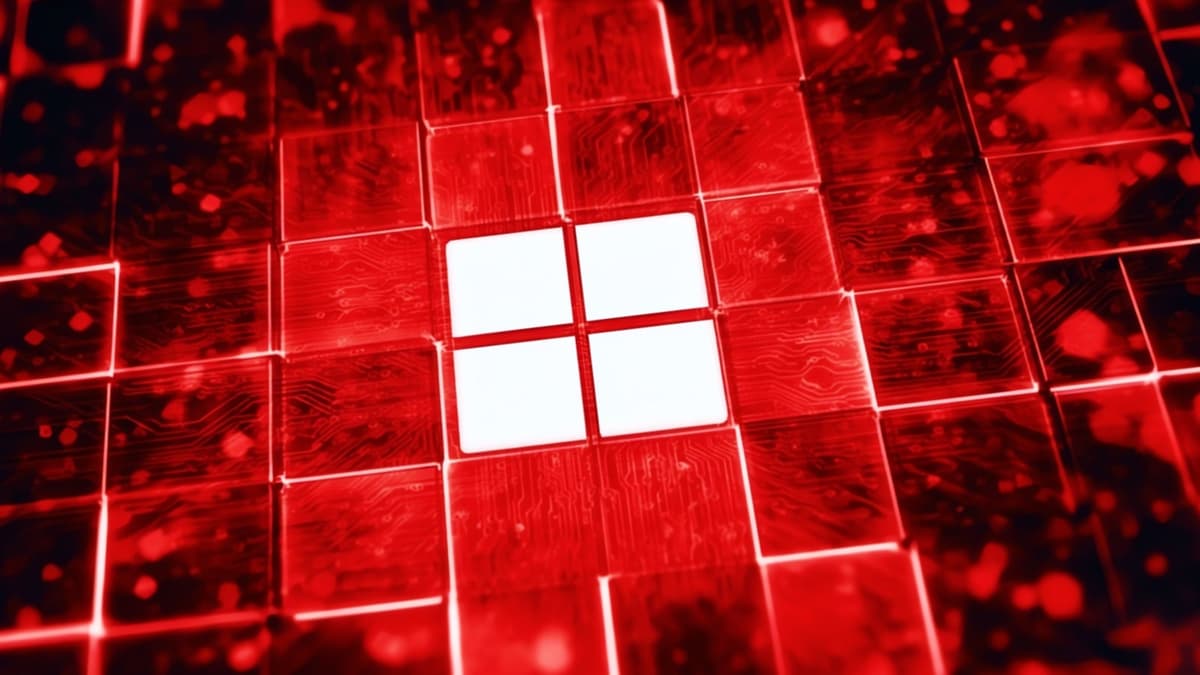
CISA Orders Feds to Patch Windows Flaw Exploited as Zero-Day
CISA has added Windows vulnerability CVE‑2026‑32202 to its Known Exploited Vulnerabilities catalog and issued Binding Operational Directive 22‑01, requiring federal agencies to patch by May 12. The zero‑click NTLM hash‑leak flaw stems from an incomplete fix for CVE‑2026‑21510 and enables pass‑the‑hash attacks...

Starlink's Precise Location Tool Could Aid Malicious Actors
Duh, why does no one think about the bad actors that might want to use this feature... it's just like the speed limits on airborne use...

A Quarter of Healthcare Organizations Report Medical Device Cyber-Attacks
RunSafe Security’s 2026 Medical Device Cybersecurity Index found that 24% of healthcare organizations experienced cyber‑attacks on medical devices in the past year. In 80% of those incidents, the impact on patients was moderate or significant, ranging from delayed imaging to...

GitHub Patches AI‑found Critical RCE in Under Six Hours
GitHub rushed to fix a critical vulnerability in less than six hours. A critical remote code execution vulnerability was discovered using an AI model and patched within hours. Details 👇 https://t.co/MVGhe8zsCX

GitHub Rushed to Fix a Critical Vulnerability in Less than Six Hours
GitHub patched a critical remote code execution vulnerability in less than six hours after Wiz Research used AI to discover the flaw in its internal git infrastructure. The security team reproduced the bug within 40 minutes, deployed a fix to...

Ameriprise Financial Breach Exposes Data of 48,000 Customers
Ameriprise Financial confirmed that unauthorized actors accessed stored data affecting almost 48,000 U.S. customers. The firm says no funds were moved but is offering credit and identity monitoring while lawsuits over the incident linger.
Somebody’s Watching Me: The Crackdown on Stalkerware
The podcast episode spotlights Eva Galperin’s fight against stalkerware, a hidden class of spyware used to monitor victims’ phones. After uncovering a colleague’s decades‑long abuse in 2018, Galperin founded the Coalition Against Stalkerware to coordinate researchers, advocates, and legal action....

Aviatrix Intros Platform For Agentic AI Security The ‘Containment Era’
Aviatrix has introduced AgentGuard, a platform designed to contain compromised AI agents rather than merely detect and remediate them. The solution discovers agents across VMs, Kubernetes clusters, and serverless functions, mapping their connections and enforcing zero‑trust communication governance. By limiting...

Your AI Agent Is Ready to Go. Is Your Infrastructure?
TransUnion has spent $145 million building the OneTru platform, a hybrid architecture that couples traditional expert systems with generative AI, and has already generated $200 million in cost savings. The platform powers the AI Analytics Orchestrator Agent, leveraging Google Gemini to let...

38 Vulnerabilities Found in OpenEMR Medical Software
A security audit by Aisle uncovered 38 vulnerabilities in OpenEMR, the open‑source electronic medical records platform used by more than 100,000 healthcare providers worldwide. The flaws include two critical SQL‑injection bugs (CVE‑2026‑24908 and CVE‑2026‑23627) and an authorization‑bypass issue (CVE‑2026‑24487) that...

Critical cPanel Authentication Vulnerability Identified — Update Your Server Immediately
cPanel has issued emergency security updates to fix a critical authentication bypass vulnerability (CVE‑2026‑41940) that scores 9.8 on the CVSS scale. The flaw affects all supported cPanel and WHM versions and can allow unauthenticated attackers to gain full administrative control...

Chrome 147, Firefox 150 Security Updates Rolling Out
Google and Mozilla released critical security updates for Chrome 147 and Firefox 150, addressing a total of 34 memory‑safety flaws. Chrome 147 includes 30 fixes, four of which are critical use‑after‑free bugs, while Firefox 150.0.1 patches four high‑severity vulnerabilities. Google...

AWS Leans on Prior Ingenuity to Face Future AI and Quantum Threats
AWS marks its 20‑year anniversary while confronting AI‑driven attacks and the looming quantum‑computing risk. The Nitro hardware platform gives AWS a “zero‑human” infrastructure, enabling isolated bare‑metal instances and protecting encryption keys. Early adoption of symmetric encryption means most data at...

Top AI-Powered Vendor Risk Management Platforms for SaaS Companies in 2026
Vendor risk breaches now account for roughly 30% of incidents, prompting regulators like Europe’s DORA and the SEC to tighten third‑party oversight. AI‑powered TPRM platforms promise continuous, machine‑speed visibility, turning multi‑page SOC 2 reports into concise insights and auto‑generating tickets in...

Greece’s AI Smart Policing System Ruled Unlawful After €4 Million Public Spending\
In 2019 the Hellenic Police awarded a €4 million (≈ $4.3 million) contract to Intracom Telecom for a “Smart Policing” system that equips officers with portable devices for facial‑recognition, fingerprint and license‑plate scanning. The AI‑enabled tools were intended to speed up identity checks...

It’s Not Just Spyware Scandals: EU Is Funding the Industry that Spies on Europeans
In February 2026 Greece sentenced four people for the Predatorgate espionage scandal, marking the first criminal conviction of executives from spyware maker Intellexa. Investigations reveal that EU subsidies, loans and investment funds have funneled hundreds of thousands to millions of...

U.S. CISA Adds Microsoft Windows Shell and ConnectWise ScreenConnect Flaws to Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added two new flaws to its Known Exploited Vulnerabilities (KEV) catalog: a high‑severity path‑traversal issue in ConnectWise ScreenConnect (CVE‑2024‑1708) and a lower‑severity Windows Shell spoofing flaw (CVE‑2026‑32202). The ConnectWise bug scores...

Microchip Launches PQC-Ready Root of Trust Controllers for Secure Platforms
Microchip Technology unveiled the TS1800 root‑of‑trust controller and the TS50x secure‑boot family, both engineered to run post‑quantum cryptography (PQC) algorithms. The TS1800 provides external root‑of‑trust functions with hardware acceleration for NIST‑standard PQC schemes such as ML‑DSA, LMS and ML‑KEM, while...
Met Police Federation Decries ‘Outrageous’ Palantir AI System
The Metropolitan Police Federation is threatening legal action over the force’s new Palantir AI system, which it says breaches officers’ privacy and GDPR rules. The pilot, launched last week, has already led to two arrests and two suspensions while hundreds...

CERT-In Warns of AI-Driven Cyber Threat Surge, MSMEs at Highest Risk
India’s cyber‑security agency CERT‑In warned that frontier AI is reshaping cyber threats, making attacks faster, more scalable and accessible to low‑skill actors. The advisory highlights that AI can scan code, spot zero‑day vulnerabilities and launch coordinated multi‑stage attacks in seconds....

Malaysian Indians Least Likely to Be Scammed as They Ask Too Many Questions: Police
Malaysians suffered an estimated 2.7 billion ringgit (about US $684 million) loss to online scams in 2024, a 76% jump from the prior year. The Penang Commercial Crime Department reported that only 7% of the 5,090 scam cases in the state involved Indian...
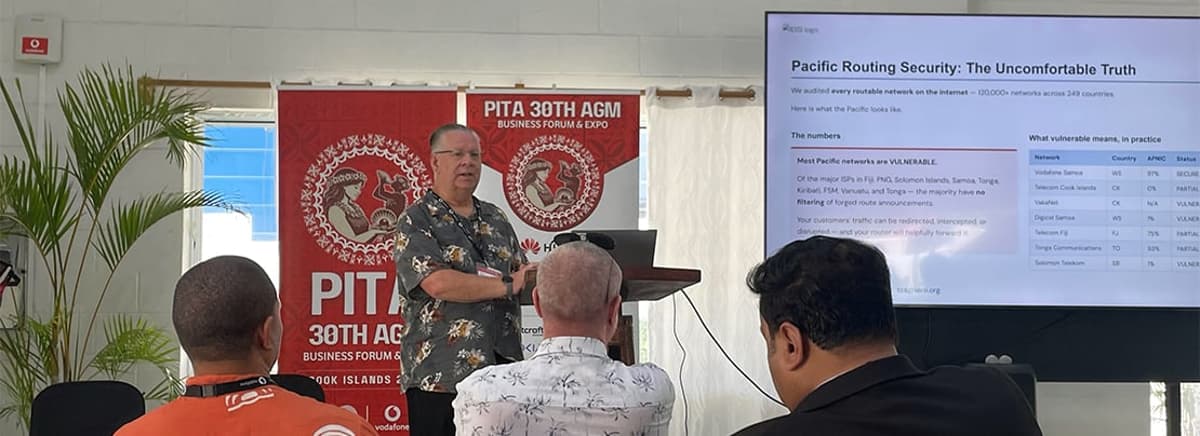
Pacific Routing Security Sets a Deadline
At the APNIC Sub‑Regional Forum during PITA 30 in Rarotonga, routing‑security chair Terry Sweetser asked Pacific telco leaders whether they filter forged BGP announcements. The discussion revealed widespread uncertainty, with only 49 of 116 regional ASNs showing any protection and many...

ClickUp Discloses Feature Flag Misconfiguration That Exposed 893 Customer Email Addresses and a Live API Token
ClickUp disclosed that a misconfigured feature‑flag setup exposed 893 customer email addresses and a live API token. The emails were embedded in Split.io flag targeting rules and became publicly queryable through the client‑side SDK key, which is intentionally exposed in...

Airrived and Wisdom Technology Deploy Qatar Sovereign Cloud with Agentic AI
Airrived and Wisdom Technology announced a strategic partnership to launch a Qatar‑based sovereign cloud platform powered by Airrived’s Agentic OS. The service targets energy operators, government agencies and financial institutions, promising secure, AI‑driven operations within national borders.

Privacy Watchdog Clears Jollibee’s Christmas Ads
The National Privacy Commission (NPC) cleared Jollibee Foods Corp. and Rakuten Viber of violating the Philippines’ Data Privacy Act after a probe into the 2025 Holiday Gems Christmas campaign. The investigation found the stickers were delivered via on‑device keyword matching, with...

Dell Introduces Quantum‑Ready PCs to Bolster Cyber Resilience
Dell Technologies rolled out quantum‑ready protections for its commercial PC line, hardening firmware and BIOS against future quantum‑enabled attacks. The move expands Dell’s cyber‑resilience portfolio amid growing concerns over AI‑driven threats and the long‑term risk of quantum decryption.

Router (Home Network): OWE Authentication Question
A home‑network user in NYC noticed their router reporting OWE (Opportunistic Wireless Encryption) instead of the expected WPA2. The moderator explained that when a router is set to WPA3/WPA2 mode it operates in an OWE transition mode, causing compatible devices...

BlueAPACHE Partners with NinjaOne to Strengthen Services Delivery
blueAPACHE announced a strategic partnership with NinjaOne, embedding the latter’s unified IT operations platform into its managed‑services framework. The integration will enable remote monitoring, automated patching, secure access and proactive remediation across client environments. blueAPACHE will first run NinjaOne‑enabled services...

Pentagon CIO Kirsten Davies Unveils Four‑Pillar Digital Transformation Plan
At the 2026 Digital Transformation Summit, Pentagon Chief Information Officer Kirsten Davies presented a four‑pillar strategy aimed at delivering resilient connectivity, agile software delivery, hardened cyber defenses and a skilled workforce. The plan is positioned as the backbone for U.S....

Microsoft Confirms Active Exploitation of Windows Shell Flaw CVE‑2026‑32202
Microsoft announced that the high‑severity Windows Shell vulnerability CVE‑2026‑32202 is being actively exploited in the wild. The flaw, patched in April’s Patch Tuesday, is leveraged by Russian‑linked APT28 in a zero‑click campaign targeting Ukraine and EU entities.

Smart Firms Treat Vendor Risk Like Their Own
Artificial intelligence is accelerating the discovery of third‑party software flaws, turning vendor risk into a frontline concern for enterprises. Microsoft’s April 14, 2026 patch cycle addressed 167 Windows vulnerabilities, illustrating how quickly weaknesses can surface. Mid‑market firms, heavily reliant on cloud and...

New Report From the MPA’s Content Security Initiative Links Control Failures to Content Security Incidents Across the Entertainment Industry
The Motion Picture Association’s Trusted Partner Network released the TPN STAR Report, the first industry‑wide study linking security‑assessment data to real‑world content‑security incidents. The report finds that while most studios have basic policies, inconsistent execution of technical controls—especially MFA, vulnerability management,...

Why Backing Up Your Microsoft 365 Data Is Only Half the Job
Microsoft 365 has transformed from a suite of web apps into the enterprise’s central control plane, intertwining identity, collaboration, security, and workflow. While Microsoft secures the underlying platform, customers now shoulder configuration, access delegation, and governance responsibilities. A breach at a...

Building Cyber Resilience Through Zero Trust in the Public Sector
Public sector agencies are prime cyber‑crime targets, prompting governments to replace perimeter defenses with identity‑led Zero Trust models. In Australia, Zero Trust is codified in the 2025 Protective Security Policy Framework and reinforced by state strategies such as NSW’s 2026‑2028...

U.S. Ends Investigation Into Claims WhatsApp Chats Aren’t Private
The U.S. Commerce Department abruptly ended a 10‑month investigation into allegations that Meta Platforms can access and store unencrypted WhatsApp messages. The probe, led by an export‑control agent who claimed Meta viewed all content, was shut down at senior agency...