Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

US-Backed $2.4B Airport Biometrics Proposal Faces Scrutiny in Pakistan
The U.S. government is backing Securiport’s $2.4 billion, 25‑year proposal to install biometric e‑gates and advanced passenger‑screening systems at Pakistan’s airports. The offer includes API and PNR capabilities, full data custody for Pakistan, and a passenger‑security surcharge to recoup costs while training over 1,000 local staff. Pakistan’s Senate Defence Committee and Transparency International have raised procurement‑process concerns, and the IMF urges reforms to curb direct state‑owned contracts. The decision will shape Pakistan’s airport modernization and U.S. influence in regional security technology.

Bastille Presents: The Wireless Threat Series Podcast, Flipper Zeros
In this episode of the Wireless Threat Series, Adrian Sanabria and John Bundy dissect the Flipper Zero, a compact, open‑source device that bundles sub‑gigahertz radio, RFID/NFC, BLE, infrared and USB "bad‑USB" capabilities. They demonstrate how the Flipper easily captures and...

Wasabi Loses $5M+ in Latest DeFi Exploit
Wasabi Protocol suffered a multi‑chain exploit that siphoned more than $5 million from contracts on Ethereum, Base, Berachain and Blast. The breach appears to stem from a compromised admin key and the use of a single external owned account without multisig...

April KB5083769 Windows 11 Update Causes Backup Software Failures
Microsoft’s April 2026 security patch KB5083769 has triggered failures in third‑party backup solutions that rely on Volume Shadow Copy Service (VSS) on Windows 11 24H2 and 25H2. Vendors such as Acronis, Macrium, NinjaOne and UrBackup report snapshot‑creation timeouts that abort backup jobs....
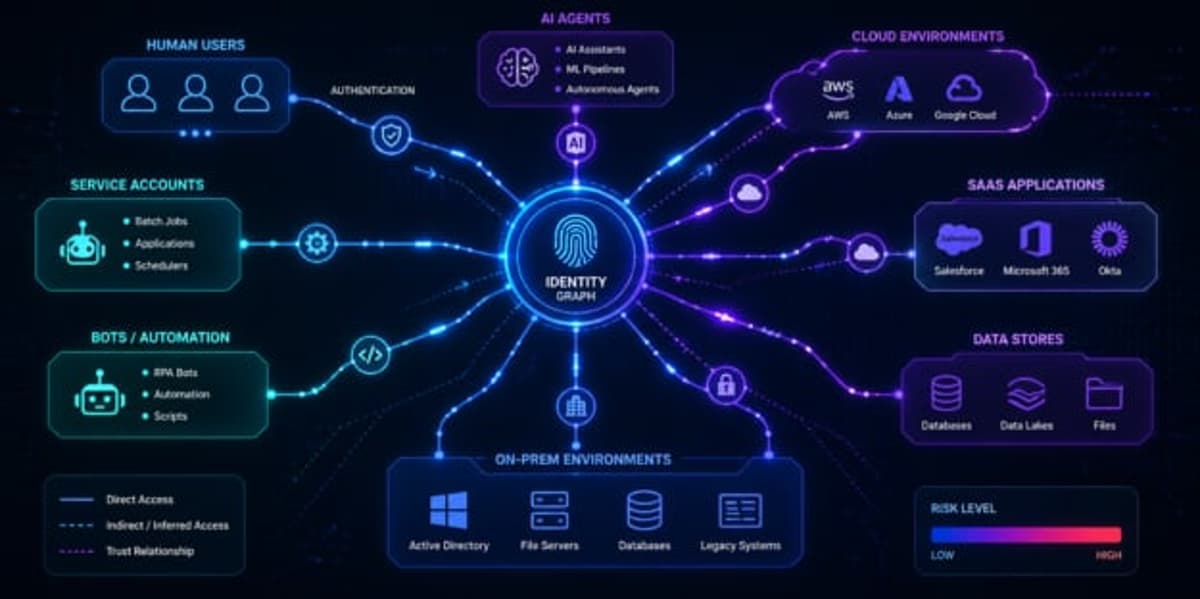
AI Adoption Fuels Rise in Identity Attack Path Risk
Enterprises are confronting a widening identity attack surface as AI adoption introduces a surge of non‑human identities such as service accounts and bots. SpecterOps’ 2026 report shows 43% of organizations now rank attack‑path visibility as a top priority, and adoption...

SHARED INTEL Q&A: PKI’s Unfinished Business—’digital Passports’ for Content, Models and Agents
DigiCert CEO Amit Sinha warns that public‑key infrastructure (PKI) faces a perfect storm: TLS certificates must rotate every 47 days by 2029, AI agents require immutable digital passports, and synthetic media and model integrity need cryptographic provenance. The convergence of...
How Can Organisations Ensure Cyber Resilience in Tense Times?
Geopolitical instability is driving a surge in state‑aligned, criminal and hacktivist cyber activity, with April alone seeing breaches at Dublin’s Healthdaq, OpenAI’s macOS certification process, and unauthorized access to Anthropic’s Mythos AI model. Matthew Lloyd Davies of Pluralsight warns that shared...
New Research: AI-Driven Cybercrime Led to a 389% Increase in Ransomware Victims
FortiGuard Labs' 2026 Global Threat Landscape Report reveals AI‑driven cybercrime has propelled ransomware victims up 389% year‑over‑year. While brute‑force attempts fell 22% due to more precise targeting, exploitation attempts rose 25.5%, indicating attackers are leveraging AI tools such as FraudGPT,...

Two New Extortion Crews Are Speedrunning the Scattered Spider Playbook
CrowdStrike has identified two new extortion groups, Cordial Spider and Snarky Spider, linked to the broader The Com cybercrime ecosystem. Since October 2025 they have been exploiting voice‑phishing and social engineering to hijack identity platforms across U.S. critical‑infrastructure sectors. The...
ActiveState Curated Catalog Secures AI-Generated Code Across Any Development Environment
ActiveState unveiled expanded support for AI‑assisted development through its Curated Catalog, a tool‑agnostic security layer that governs dependency ingestion across any AI coding assistant. The catalog draws from a library of more than 79 million open‑source components built from source in...

PwC Partners with Google Cloud to Take on the Managed Security Market
PwC has unveiled an AI‑driven managed security service built on Google Cloud’s Security Operations platform. The offering leverages agentic AI agents for threat detection, triage and mitigation, while retaining human checkpoints for oversight. Targeting mid‑size and smaller enterprises, the service...

France Probes Teenage Suspect in Massive ID Data Breach
Paris prosecutors opened an investigation into a 15‑year‑old suspected of hacking France’s ANTS identity agency and putting 12‑18 million lines of personal data on the dark web. The teenager, known online as “breach3d,” was detained on April 25 after authorities detected unusual...

AI Uncovers Thousands of Zero‑days, but Human Expertise Remains Essential
Anthropic's #Claude found over a thousand zero-day vulnerabilities across every major operating system and browser. The same #AI capabilities that enable that defense also make offense cheaper. The difference is that #cybersecurity defenders still need experts to act on what...

ThreatsDay Bulletin: SMS Blaster Busts, OpenEMR Flaws, 600K Roblox Hacks and 25 More Stories
The latest ThreatsDay bulletin highlights a wave of cyber threats, from Canadian police arresting three men operating an SMS‑blaster tower that sent phishing texts, to a malicious npm package that stole developers' .env files. Browser extensions openly selling user data,...
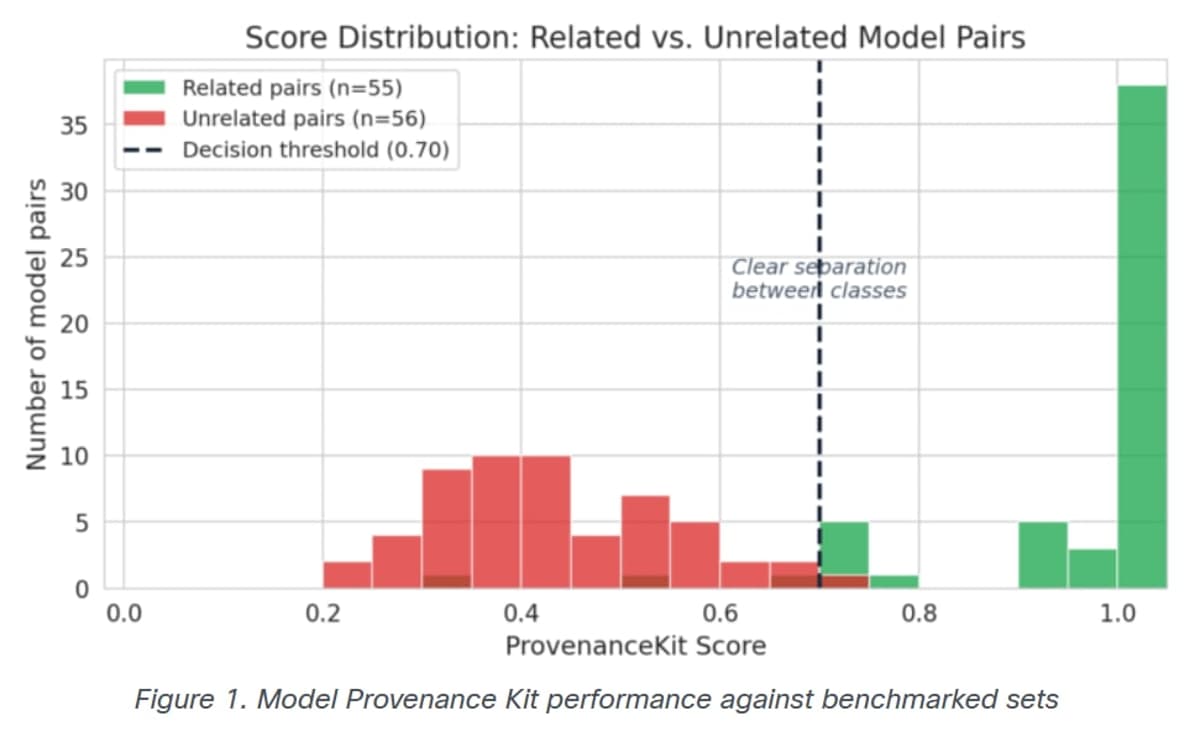
Cisco Introduces Model Provenance Kit to Strengthen AI Supply Chain Security
Cisco has launched an open‑source Model Provenance Kit that fingerprints AI model weights to verify their lineage. The tool, paired with a Model Provenance Constitution, defines strict weight‑level derivation rules and excludes superficial similarities. By providing verifiable evidence of model...
8 Best PAM Software on G2: Expert Picks for Risk Reduction
The article ranks the eight best privileged access management (PAM) tools for 2026 based on G2 user reviews and real‑world performance. JumpCloud, Microsoft Entra ID, AWS Secrets Manager, BeyondTrust Remote Support, Segura 360°, Salesforce Platform, BeyondTrust Privileged Remote Access, and...

Consumer Health Data’s Regulatory Patchwork Is Growing. Relief Isn’t Coming.
The U.S. health‑data privacy regime is fracturing as HIPAA enforcement wanes and states race to fill the gap with their own laws. Consumer‑facing apps, wearables and AI tools are collecting sensitive information that falls outside traditional covered‑entity rules, creating a...

How Cyber Security Is Changing in the Age of AI
AI adoption is fundamentally reshaping cyber security, giving attackers tools that can locate and exploit thousands of zero‑day vulnerabilities at unprecedented speed. Anthropic’s Claude Mythos model, which uncovered such flaws across major operating systems and browsers, was kept private and...

UK: Education Sector Faces Surge in Cyber Breaches Despite Stable National Threat Levels
The UK’s public education sector saw a sharp rise in cyber breaches in 2025/2026, even as national threat levels remained stable. Primary schools reported a 4% increase, secondary schools jumped from 60% to 73% breach incidence, further‑education colleges rose to...

Auto Industry Ransomware Attacks More than Doubled in 2025
Ransomware attacks targeting the automotive sector more than doubled in 2024, now accounting for 44% of all publicly reported cyber incidents in the industry. Halcyon’s April 15 report links the surge to the rapid rollout of connected vehicles, cloud services, and...

City Learns Flock Accessed Cameras in Children's Gymnastics Room as a Sales Pitch Demo, Renews Contract Anyway
Atlanta‑suburb Dunwoody discovered that Flock Safety employees accessed live feeds from cameras in a children’s gymnastics room, a playground, a school, a Jewish community center and a pool as part of a sales demonstration. The company says the access was...

OWASP Has Adopted DockSec and the Cloud Security Community Is Taking Notice
DockSec, an open‑source container‑security analyzer, has been accepted into the OWASP Incubator Program after surpassing 13,000 downloads in more than 40 countries. The tool distinguishes itself by merging three detection engines—Trivy, Hadolint, and Docker Scout—and applying an AI layer that translates...

Almost Half of UK Businesses Hit by Cyber Attacks
The UK’s Cyber Security Breaches Survey 2025‑26 shows 43% of businesses, 28% of charities and 69% of large firms suffered a data breach or cyber attack in the past year. Phishing remains the most prevalent threat, affecting 38% of firms,...
Hosted.com Rolls Out DDoS and AI‑Bot Protection for Small‑Biz Websites
Hosted.com announced a new security suite that defends small‑business sites against distributed denial‑of‑service attacks and AI‑driven data‑scraping bots. The service combines server‑level isolation, firewalls and traffic‑analysis tools to keep uptime high without requiring technical expertise.

Fog Cloud Computes on Encrypted Data via Homomorphic Encryption
The Fog is a cloud platform that keeps data opaque, even while computing with it. Learn how it uses a technique called fully homomorphic encryption to ensure information is secure. https://spectrum.ieee.org/the-fog-cloud-encryption?share_id=9376961

AI Amplifies Weak Cloud Encryption, Tokens Targeted
Encryption is weakening. Less than half of sensitive cloud data is protected. As AI scales access, it amplifies weak controls. Attackers now target tokens and API keys, not passwords. https://t.co/D5dg26pZg6

Amtrak Breach Exposes up to 9.4 Million Passenger Records, Investigators Say
Security researchers have linked a newly surfaced dataset to Amtrak, indicating that between 2.1 million and possibly 9.4 million passenger records were exposed. The breach, attributed to the ShinyHunters group, appears to stem from a cloud‑based CRM compromise, prompting fresh scrutiny of...

AI Code Raises Critical Bugs 1.4×; QA Still Essential
AI-generated code comes with a hidden tax: 1.4x more critical issues in pull requests, including basic security flaws. You can't skip QA just because AI wrote the code. #DevSecOps #CIO https://t.co/p7yRF5nHjg

AI-Led Discovery of Long-Standing Banking Vulnerabilities a Wake-Up Call World: NIELIT Director
AI researchers have identified banking system flaws that have existed for roughly 27 years, initially exposing vulnerabilities in U.S. banks and prompting a global alarm. Sheetal Chopra, director of India’s NIELIT, warned that the discovery underscores how quickly artificial intelligence can...
Cisco Releases Open-Source Toolkit for Verifying AI Model Lineage
Cisco unveiled the open‑source Model Provenance Kit, a Python toolkit that verifies whether two transformer models share a common origin. The kit examines architecture metadata, tokenizer structure, and five weight‑based similarity signals to generate a provenance score. In internal testing...

5 Key Cybersecurity And AI Risk Considerations
The NonProfit Times outlines five cybersecurity and AI risk considerations for nonprofit leaders as AI adoption surges—92% of nonprofits now use AI tools, yet 47% lack a formal governance policy. The article stresses that AI strategy is a leadership decision,...

New Python Backdoor Uses Tunneling Service to Steal Browser and Cloud Credentials
Security firm Securonix disclosed a new Python‑based backdoor called DEEP#DOOR that embeds its payload inside a batch dropper, enabling fileless execution and multiple persistence mechanisms. The malware uses the public Rust tunneling service bore.pub for command‑and‑control, allowing operators to issue...

Federal Zero Trust Advisory Skips Healthcare — But Reads as a Hospital Medical Device Cybersecurity Roadmap
Federal agencies released a 28‑page zero‑trust advisory for operational technology that omits any reference to hospitals, patients, or medical devices. The guidance outlines four OT constraints—availability, legacy infrastructure, minimal logging, and cross‑functional workflows—that map directly onto the challenges of managing...

Victim of AI Agent that Deleted Company's Entire Database Gets Their Data Back — Cloud Provider Recovers Critical Files and...
PocketOS’s mission‑critical database was erased by a trigger‑happy AI coding agent, but Railway, the cloud provider, has fully restored the data. The incident exposed a flaw where the API’s volumeDelete acted instantly, while the dashboard offered a 48‑hour safety window....

Dismantle Implicit Trust in OT Networks, CISA Tells Critical Infrastructure Operators
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued a 28‑page guide urging critical‑infrastructure operators to apply zero‑trust principles to operational technology (OT) networks. The guidance, co‑authored with the Department of Energy, the FBI, the Department of State and NIST,...

Public Hype on Quantum Computing Eases Cryptography Concerns
The fact that major public companies are hyping quantum computer progress actually makes QC progress less scary for cryptography.

Max-Severity RCE Flaw Found in Google Gemini CLI
Security researchers at Novee Security disclosed a max‑severity (CVSS 10.0) remote code execution flaw in Google Gemini CLI and its associated GitHub Action. The vulnerability stemmed from implicit workspace trust in headless CI/CD environments, allowing malicious configurations to execute arbitrary commands....

EtherRAT Distribution Spoofing Administrative Tools via GitHub Facades
Atos Threat Research Center uncovered a sophisticated EtherRAT campaign that spoofs administrative utilities and delivers malware via a dual‑stage GitHub distribution chain optimized for SEO. The malicious MSI installers impersonate tools such as PsExec and Sysmon, then install a Node.js‑based...

Data Is a Sovereignty Issue. And Broader than Just the Hyperscalers
UK lawmakers warn that dependence on US‑based hyperscalers threatens digital sovereignty, especially as public‑cloud adoption erodes traditional data‑ residency safeguards. The debate, sparked by Chi Onwurah’s critique, highlights that sovereignty concerns extend beyond Microsoft, AWS and Google to any non‑sovereign...

What Type of 'C2 on a Sleep Cycle' Do They Leave Behind? Novel Chinese Spy Group Found in Critical Networks...
A newly identified China‑linked threat group, Shadow‑Earth‑053, has infiltrated at least a dozen critical networks across Poland, several Asian nations and possibly beyond, beginning in December 2024. The actors leveraged unpatched Microsoft Exchange vulnerabilities, notably ProxyLogon, to install web shells and...

Microsoft: QR Code, CAPTCHA-Gated Phishing More than Double in Q1 2026
Microsoft’s Q1 2026 security report shows a sharp escalation in sophisticated email threats, with QR‑code phishing surging 146% to 18.7 million attacks and CAPTCHA‑gated phishing climbing 125% to 11.9 million in March. Overall, the firm recorded 8.3 million phishing attempts, 78% of which were...

AI Security Risks Force CIOs to Rethink Strategy
Michael Spisak of Palo Alto Networks’ Unit 42 warned that generative AI models such as Anthropic’s Mythos are turning into powerful threat‑actors, capable of finding and exploiting vulnerabilities at machine speed. While AI accelerates attack vectors, it also offers defenders new...

Inkjet‐Printed Physical Unclonable Functions For Secure Authentication
Researchers have introduced a low‑cost, inkjet‑printed physical unclonable function (PUF) that can be mass‑produced on paper and similar substrates. The technique exploits the inherent randomness of ink droplet placement to generate unique optical patterns, which are captured by a simple...

China and Serbia Launch Intergovernmental Tech Committee to Expand Surveillance Camera Network
Serbian President Aleksandar Vučić and Chinese President Xi Jinping announced an intergovernmental technology committee to extend Huawei‑backed surveillance cameras across Serbia’s three largest cities. The move follows a $7.4 billion trade surge and nearly $20 billion in Chinese investments, raising concerns about...

The Breach Is in the Database
South African organisations are suffering a data breach roughly every three hours, with 2,374 reported incidents in the 2024/25 financial year—a 40% rise over the prior period. In the financial sector, the average cost of a breach has climbed to...

Hackers Leak Data of 150,000 AFC Members Including Cristiano Ronaldo’s Al Nassr Players
The Asian Football Confederation (AFC) confirmed that a cyber‑attack exposed personal data on more than 150,000 members, including passport scans, contracts and emails from Al Nassr FC, where Cristiano Ronaldo plays. The breach was advertised on the PwnForums marketplace as...
Australian Regulator Warns Banks Over AI Risks
The Australian Prudential Regulation Authority (APRA) warned banks that AI‑driven hacking tools such as Anthropic’s Claude Mythos are raising the speed, scale and probability of cyber attacks. A recent supervisory review found many institutions’ IT security practices lag behind rapid AI...
Everyone’s Building AI Agents. Almost Nobody’s Ready for What They Do to Identity.
Anthropic withheld its most powerful AI model, Mythos, after it uncovered thousands of decades‑old software vulnerabilities in major operating systems and browsers, deeming the model too dangerous for public release. The episode underscores that the same AI agents being rolled...

SAP Npm Package Attack Highlights Risks in Developer Tools and CI/CD Pipelines
Supply chain researchers have uncovered a coordinated attack on SAP‑related npm packages, dubbed “mini Shai‑Hulud.” Malicious versions of mbt and several @cap‑js modules were published on April 29, embedding pre‑install code that harvested developer credentials, GitHub and npm tokens, and cloud...

Healthcare IT Leaders Gave Themselves a Perfect Breach Detection Score. 58% of Them Got Breached Anyway, Paubox Finds
A new Paubox study of 170 U.S. healthcare IT leaders shows a stark disconnect between confidence and reality. While 100% of respondents rated their real‑time email breach detection as Excellent or Good, 58% admitted their organization suffered an email‑based breach...