Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

TeamPCP Hits SAP Packages With 'Mini Shai-Hulud' Attack
TeamPCP launched a “Mini Shai‑Hulud” supply‑chain attack that injected malicious pre‑install scripts into four SAP npm packages used in the Cloud Application Programming Model and MTA Build Tool. The compromised versions were published on Wednesday, quickly detected by security firms Wiz, Socket and Aikido, and removed within days. The payload harvests GitHub, npm, Kubernetes, CI/CD and cloud credentials, encrypts the data, and can propagate via stolen tokens. SAP responded with a security note for customers while researchers point to a misconfigured CircleCI token as a likely entry point.

Samsung’s Free Android Upgrade Brings Better Security to Galaxy Phones
Samsung is preparing a free One UI 8.5 upgrade for supported Galaxy devices, adding theft protection, app‑blocking and inactivity‑restart security controls. The rollout is expected to begin in Korea with a global launch around May 4, 2026. However, recent Samsung security patches have...

Another AI-Assisted Software Scan Yields 9-Year-Old Linux Bug
Researchers at Xint used an AI‑assisted scan to uncover a nine‑year‑old Linux kernel flaw dubbed Copy Fail (CVE‑2026‑31431). The bug lets any local user overwrite four bytes in memory, granting deterministic root access across all Linux distributions. A ten‑line proof‑of‑concept demonstrates...

Why Recovery Speed Matters when the Homeland Is the Cyber Battlefield
The article argues that the homeland is now a continuous cyber battlefield and that the speed of cyber recovery has become a decisive factor for U.S. military strength. Lt. Gen. Jeth Rey urges a shift from pure prevention to a...
Anthropic Opens Claude Security Public Beta to Scan Enterprise Codebases for Vulnerabilities
Anthropic has rolled out Claude Security in public beta, giving Enterprise‑tier Claude customers a tool that scans entire codebases for vulnerabilities and generates targeted patches using the Opus 4.7 model. The launch follows a closed preview that reportedly helped hundreds of...

U.S. Department of War Rolls Out 12‑Month Cyber Apprenticeship to Build Defense Talent
The U.S. Department of War unveiled the Cyber Registered Apprenticeship Program (Cyber RAP), a 12‑month, skills‑first training track announced by CIO Kirsten Davies on April 28. The initiative aims to fast‑track cyber‑defense analysts, infrastructure specialists and incident responders for the...

Zulip 12.0 Launch Adds End‑to‑End Encryption and Docker Upgrade for SaaS Chat
Zulip announced the 12.0 release of its open‑source SaaS chat platform, introducing end‑to‑end encryption for mobile push notifications and a major Docker upgrade. The update follows 5,500 new commits from 160 contributors, underscoring rapid development and a new AI‑use policy...

CISA Flags Data‑theft Bug in NSA‑built OT Tool GrassMarlin (CVE‑2026‑6807)
The Cybersecurity and Infrastructure Security Agency (CISA) has issued an advisory that all versions of the NSA‑developed OT networking tool GrassMarlin are vulnerable to CVE‑2026‑6807, a data‑theft flaw exploitable via XML External Entity attacks. The bug, first disclosed by Dragos...

Agencies Release Joint Guide on Zero Trust Adoption in Operational Technology
The Cybersecurity and Infrastructure Security Agency, together with other federal bodies, released a joint guide to help organizations apply zero‑trust principles to operational technology (OT) systems. The guide outlines how to navigate OT’s unique constraints, tackle visibility challenges, and prioritize...
AI Sandboxing Is Having Its Kubernetes Moment
Anthropic unveiled its Mythos model, which independently discovered and exploited zero‑day vulnerabilities in major operating systems and browsers, including a 27‑year‑old kernel bug. The demonstration highlights the danger of running thousands of workloads on a shared Linux kernel in Kubernetes,...
Cyberattack Shows Connected Cars Can Be Rendered Inoperable
This March, A cyberattack on backend systems on a breathalyzer device prevented drivers across the U.S. from accessing their vehicles. A new problem is emerging in connected vehicles: Systems can fail and render perfectly functional vehicles useless. https://spectrum.ieee.org/connected-vehicle-risks

Phishers Leverage Trusted Email and Fatigue to Evade Defenses
Attackers exploit trusted email platforms, user fatigue, and legitimate infrastructure to bypass defenses, making phishing attacks more effective and harder to detect. https://t.co/xIHzGt3zK5

After Dissing Anthropic for Limiting Mythos, OpenAI Restricts Access to Cyber, Too
OpenAI announced that its upcoming GPT‑5.5 Cyber tool will be released only to vetted "critical cyber defenders" after Sam Altman publicly criticized Anthropic for limiting access to its Mythos product. Prospective users must complete an online application that verifies their...

Human Oversight Essential: AI Can't Fully Guard Cybersecurity
Why We Can’t Let #AI Take the Wheel of Cyber Defense by Steve Durbin @SecurityWeek Learn more: https://t.co/m9sL8PCrDB #CyberSecurity #Infosec #IT #Technology https://t.co/10zENgTC6l

Anthropic's Mythos Has Landed: Here's What Comes Next for Cyber
Anthropic unveiled Claude Mythos, a large‑language model that can automatically locate and exploit zero‑day vulnerabilities across major operating systems and browsers, demonstrating the find on a 27‑year‑old OpenBSD flaw. The rapid, machine‑speed discovery has alarmed the cybersecurity community, prompting fears of...

Cybersecurity Tactics for Medical IoT Devices
The Internet of Medical Things (IoMT) is projected to surge from $60 billion in 2024 to $814 billion by 2032, driven by real‑time patient monitoring and cost‑saving benefits. However, 2024 saw over 14,000 IoMT IPs exposed, with 36% stemming from unsecured medical...

Misconfigured Server Run by Hackers Leaks 345,000 Stolen Credit Cards
Researchers discovered a mis‑configured server operated by the Jerry’s Store card‑ing market, exposing 345,000 stolen credit cards after an AI‑assisted coding tool, Cursor, generated an unauthenticated web directory. The leak, uncovered on April 16, revealed over 145,000 active cards that...

AI Fuels ‘Industrial’ Cybercrime as Time-to-Exploit Shrinks to Hours
FortiGuard’s 2025 Global Threat Landscape Report warns that cybercrime has become an industrial‑scale operation powered by AI and automation. New AI‑enabled tools such as WormGPT, FraudGPT, HexStrike AI, APEX AI and BruteForceAI dramatically shorten the time‑to‑exploit, now often 24‑48 hours after...

Cybersecurity and the New Threat Landscape for U.S. Utilities
In this episode of Schweitzer Drive, Frank Harrell interviews Sharla Arts, Vice President of Security and Resilience Policy at Accel Energy, about the rapidly evolving cyber threat landscape facing U.S. utilities. Arts explains how nation‑state actors, AI‑enabled ransomware, and the...

32TB Encrypted Drive Offloads Security, Cuts Software Attacks
Apricorn’s 32TB encrypted drive removes the host computer from security processes, reducing software-based attack exposure while introducing new physical access considerations. https://t.co/Gst9CCmTTk

How AI Moves Businesses From Damage Control to Near-Instant Recovery After a Data Crisis
AI‑powered continuous data protection (CDP) is replacing the decades‑old nightly backup model, allowing enterprises to capture changes in near‑real time. By using intelligent prediction and tiering, AI can prioritize critical files while discarding redundant I/O, making CDP affordable at scale....

Datalink Taps Arctic Wolf for AI-Led Security Operations
Datalink Networks has teamed up with Arctic Wolf to embed the Aurora Superintelligence Platform and Aurora Agentic SOC into its managed‑service portfolio for U.S. and Canadian clients. The AI‑led security operations solution promises faster detection, investigation, response and recovery without requiring...

Chinese Bots Target AI Data Centers, Vital Economic Asset
In case you’re wondering why there are so many Chinese bots on social media trying to kill our data centers and AI, this is why. It’s the most important part of our economy.

Enforcing Trust and Transparency: Open-Sourcing the Azure Integrated HSM
Microsoft announced that its Azure Integrated Hardware Security Module (HSM) will be open‑sourced through the Open Compute Project. The HSM, built into every new Azure server, meets FIPS 140‑3 Level 3 and provides tamper‑resistant, server‑local key protection. Firmware, drivers and software stacks...

Warning: Possible Hack on @Rendy_jones, Avoid Voting Link
I think poor @rendy_jones has been hacked and I’d advise not clicking on any link to vote for him hosting Google’s new podcast

DeFi's Social Layer: Unpriced Attack Vector Driving Exploits
"There's a very clear attack vector on the social layer in DeFi that needs to be priced, and that presents itself in exploits." ⚠️ ~ @dunleavy89 https://t.co/GyyjXhZlgW

The Ozkaya Board Briefing Framework: How CISOs Win the 15 Minutes
Dr. Erdal Ozkaya proposes a four‑step Board Briefing Framework—Risk, Decision, Metric, Ask—to replace the typical technical deep‑dives that leave boards disengaged. He shows how most CISO updates fail by speaking in jargon, presenting vanity metrics, or offering no decision, resulting...

Linux Bug “Copy Fail”: Short Python Script Gives Root on… Everything?
A newly disclosed Linux kernel vulnerability, dubbed “Copy Fail,” allows a short Python script to gain root privileges on any distribution. The exploit was crafted after Xint Code fed a large language model the kernel source for roughly an hour,...

OpenAI Rolls Out ‘Advanced’ Security Mode for At-Risk Accounts
OpenAI announced an optional Advanced Account Security tier for ChatGPT and Codex users deemed at risk of phishing attacks. The new mode eliminates passwords, requiring two physical security keys or passkeys, and removes email/SMS recovery in favor of recovery keys....

Taylor Swift And Rihanna TikTok Scams Are Surging
AI‑generated deepfake videos of celebrities such as Taylor Swift and Rihanna are flooding TikTok, prompting users to click fraudulent "TikTok Pay" or rewards links that harvest personal data. Copyleaks reports a sharp rise in these synthetic scams, noting that many clips...

Anthropic’s Claude Security Emerges From Closed Preview to Scan Your Codebases for Vulnerabilities
Anthropic has taken Claude Security out of closed preview, launching a beta version for Claude Enterprise customers while extending access to Team and Max plans soon. The AI‑driven tool scans entire codebases with parallel agents, validates findings to curb false...

Keeping Customer Data More Secure with AI
Customer data breaches have surged 40% worldwide, with weekly attack volumes up 70% since 2023. Companies are turning to artificial intelligence to monitor signals, detect anomalies, and enforce policies in real time, according to CIO Sean Hauver of Alorica. Experts...

GPT5.5 Matches Mythos, Boosting Defender Advantage over Attackers
GPT5.5 performs as well as Mythos in a multi-step hacking test. Prediction: In the long run this will help defenders more than attackers. Also: Again we see that there is no moat.

What NIST’s CVE Shift Means for ERP Security Teams
The National Institute of Standards and Technology announced a shift to a prioritized CVE enrichment model, limiting detailed analysis to high‑impact and federal‑critical vulnerabilities. As a result, many CVE entries in the National Vulnerability Database will no longer include full...

FBI Links Cybercriminals to Sharp Surge in Cargo Theft Attacks
The FBI warned that cyber‑enabled cargo theft surged to an estimated $725 million in losses across the United States and Canada in 2025, a 60% jump from the prior year. Confirmed incidents rose 18% while the average value per theft climbed...

PyTorch Lightning and Intercom-Client Hit in Supply Chain Attacks to Steal Credentials
Threat actors compromised the PyTorch Lightning PyPI package, publishing malicious versions 2.6.2 and 2.6.3 on April 30, 2026. The payload drops the Bun JavaScript runtime and executes an obfuscated script that harvests GitHub tokens, cloud keys, and other developer credentials....

Claude Code, Copilot and Codex All Got Hacked. Every Attacker Went for the Credential, Not the Model.
A wave of credential‑focused exploits has hit major AI coding agents—OpenAI's Codex, Anthropic's Claude Code, GitHub Copilot, and Google Vertex AI. Researchers demonstrated how unsanitized inputs such as crafted branch names, pull‑request descriptions, or command chains can exfiltrate OAuth tokens and bypass...

Cloudflare Connect San Francisco 2026
Cloudflare Connect San Francisco 2026 will run Oct. 19‑23 at Moscone West, drawing more than 2,500 security, networking and AI professionals. The five‑day conference features over 100 technical sessions, keynotes, and hands‑on labs through Cloudflare University. Attendees can explore new connectivity strategies,...

Processor‑Level AI Cuts Ecommerce Fraud, Outperforming Bolt‑On Tools
Juniper Research projects ecommerce fraud losses could reach $107 billion by 2029, but new processor‑level AI solutions are already delivering measurable cuts. North’s native AI integration has helped push the global order‑rejection rate down to 5%, a stark improvement over fragmented...
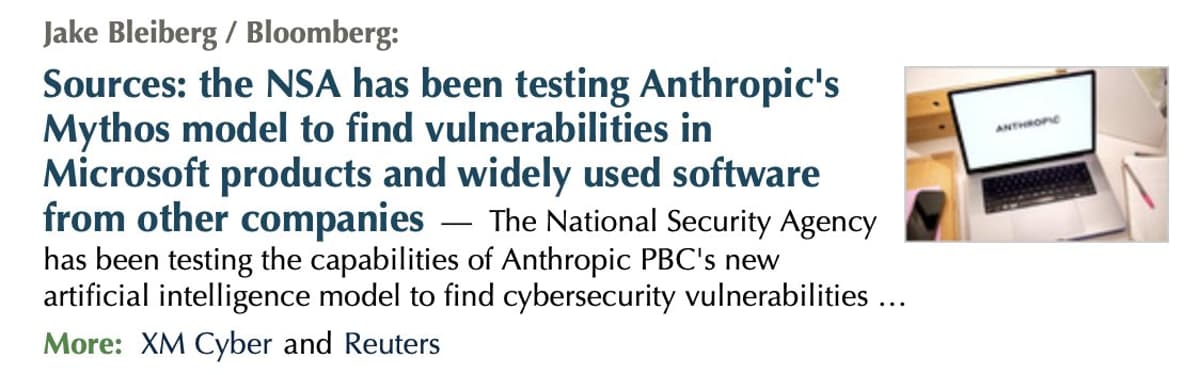
NSA Allegedly Exploiting Anthropic's Mythos for Global Hacking
My guess: the NSA is using Anthropic's Mythos to hack the world's nations. That's exactly what I suspected they would do ... https://t.co/vaxdfITSDJ

It’s a Biometric World After All: Disney Offers Facial Matching for California Park Entry
Disney has rolled out facial‑recognition entry lanes at Disneyland Resort in Anaheim, covering both Disneyland Park and Disney California Adventure. The system captures a facial template when a ticket or pass is first used, converts it to a numeric value...

Critical WHM Flaw Grants Attackers Full Server Control
A new critical severity vulnerability can give attackers full control over WHM servers, allowing them to steal data, upload malware, and delete websites. https://t.co/dS4HCtncCk

Proton CEO Andy Yen Warns AI‑driven Privacy Threats, Unveils Encrypted Google‑Workspace Rival
At a Semafor World Economy panel, Proton founder‑CEO Andy Yen warned that AI is accelerating data‑theft and mass surveillance, then announced a fully encrypted Google Workspace competitor. He also blasted broad age‑verification mandates as a danger to online anonymity.

Proton CEO Andy Yen Warns Age‑verification Laws Could End Online Anonymity
Proton chief Andy Yen cautioned that new age‑verification legislation in the UK, US and EU is "far too broad in scope" and could force ID checks for every internet user, ending anonymity. He warned that the resulting data hoarding would...

Vimeo Confirms Data Access via Compromised Anodot Integration, Ransom Threat Looms
Vimeo disclosed that a breach of third‑party analytics provider Anodot allowed an unauthorized actor to view limited user data, including video titles, metadata and some email addresses. The incident, linked to ransomware group ShinyHunters, has prompted Vimeo to disable the...

SPIFFE: Securing the Identity of Agentic AI and Non-Human Actors
SPIFFE, an open standard for workload identities, is being positioned as a solution for securing autonomous AI agents. The framework issues cryptographically verifiable SPIFFE IDs, enabling zero‑trust, federated trust and dynamic credential rotation. HashiCorp’s Vault Enterprise 1.21 and 2.0 releases...

KryBit Retaliates Against 0APT with Extensive Data Leak
KryBit, a newly identified ransomware‑as‑a‑service (RaaS) operation, retaliated against rival gang 0APT by leaking the latter’s complete operational data, including access logs, system files and PHP source code. The leak shows 0APT fabricated claims of breaching more than 190 victims...

OpenAI Makes Frontier Model Available to Critical Cyber Defenders
OpenAI is rolling out its new cybersecurity‑focused model, GPT‑5.5‑Cyber, to the U.S. federal government and a vetted pool of critical cyber defenders. The launch is paired with a Cybersecurity Action Plan that outlines shared‑defense pillars and coordination between public and...

Novel Minecraft-Targeting Stealer Tapped by Reemergent LofyGang
Brazilian threat group LofyGang resurfaced after a three‑year lull, deploying the LofyStealer (GrabBot) malware against Minecraft players. The attack begins with the “Slinky” hack, which mimics the official game icon and runs a JavaScript loader to inject the stealer. LofyStealer...

At Salesforce, We Take the Protection of Your Data Very Seriously
Salesforce recently began freezing user accounts and revoking OAuth tokens when it detects what it deems token reuse, often triggered by VPN connections or bulk data fixes. The company automatically resets passwords and locks the affected user, even if that...