Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Decade-Old Vulnerabilities Continue to Fuel Millions of Cyberattacks in the UK
Tech Radar reports UK organisations still run systems with vulnerabilities identified over a decade ago. A single flaw in Hikvision IP cameras generated 67 million attack attempts in 2025, and successful compromises rose 20 % despite lower ransomware volume. SMBs are hit hardest, with ransomware present in 88 % of their breaches, while AI‑enabled attacks jumped 89 % due to automated scanning tools.

Hackers Use Jenkins Access to Deploy DDoS Botnet Against Gaming Servers
Hackers exploited mis‑configured Jenkins servers via the scriptText endpoint to gain remote code execution and deploy a DDoS botnet aimed at Valve’s Source Engine game servers. The attackers delivered Windows and Linux binaries from a single Vietnamese IP address, using...

Malaysia’s MyDigital ID Adds 29 Partners as Adoption Grows
Malaysia’s MyDigital ID has transitioned from a pilot to a national backbone, registering over 11 million citizens and powering more than 100 public and private applications. The platform recorded a peak of 142,000 new registrations in a single day while operating...

North Korean Hacking Groups Claimed Over 75% of All Crypto Hack Value in Past Year, Report Reveals
TRM Labs reports that North Korean hacking groups seized about $577 million in two incidents, representing roughly 76 percent of all documented crypto‑hack losses through April 2026. The attacks – on Drift Protocol and KelpDAO’s bridge – accounted for just 3 percent of...

Mythos Complicates the Breakup, Says Pentagon CTO, but Anthropic Is Still Barred
Pentagon chief technology officer Emil Michael reaffirmed that Anthropic remains a supply‑chain risk for the Department of Defense, despite growing interest in its new model Mythos. Federal agencies, including the NSA and Commerce Department, are only evaluating Mythos for research,...

New Mach-O Man Malware Tapped by Lazarus in macOS-Targeted ClickFix Attacks
Lazarus Group is using a new macOS malware kit called Mach‑O Man in a ClickFix phishing campaign that targets fintech and cryptocurrency executives. The attack starts with fake meeting invitations that redirect victims to counterfeit Teams, Zoom or Google Meet pages, prompting...

CMS’ Medicare Provider Directory Released Social Security Numbers: Washington Post
The Centers for Medicare & Medicaid Services (CMS) inadvertently exposed dozens of healthcare providers' Social Security numbers in its publicly accessible Medicare Advantage provider directory. The Washington Post discovered the leak after downloading the database, which had been open for...

Sam Houston State University Paper: Maritime Cybersecurity
Researchers Scott Lynn and Joe Weiss released a Sam Houston State University paper titled “Maritime Cybersecurity: Patching the Holes in Control System Cybersecurity.” The paper argues that current U.S. Coast Guard cybersecurity regulations and maritime training programs lack sufficient depth...

Russian Hacker Pleads Guilty in Oil and Gas Facility Attacks
Artem Vladimirovich Revenskii, a Russian hacker known as “Digit,” pleaded guilty to federal charges for infiltrating and damaging oil and gas infrastructure in the United States, Ukraine and other nations. The plea agreement reduces the potential 27‑year maximum sentence, reflecting...

Handala Launches Influence Campaign Against US Troops, Exposes Data
Handala, an Iran‑linked threat group also known as Storm‑0842 and Banished Kitten, launched a WhatsApp‑based influence operation against U.S. troops stationed in Bahrain. The campaign warned Marines of imminent drone and missile targeting and simultaneously leaked personal details of 2,379...

DeFi Sets New Hack Record as April Logs 28 Exploits with $635M Stolen
In April, DeFi protocols suffered a record 28 exploits that siphoned $635.2 million, four times the thefts recorded in Q1. The bulk of the loss came from two massive attacks – a $293 million Kelp DAO bridge breach and a $285 million Drain...

ICE Leveraged Digital Tools to Spy on Trump Critics, Civil Liberties Groups Say
Lawmakers and privacy advocates say ICE used obscure administrative subpoenas and a secret grand jury to harvest personal data on Trump opponents, targeting at least six cases in 2025. The revelations have prompted lawsuits from the EFF and motions to...
How Meta Is Strengthening End-to-End Encrypted Backups
Meta has upgraded its end‑to‑end encrypted backup infrastructure for WhatsApp and Messenger with a hardware security module (HSM) based Backup Key Vault. The vault stores recovery codes in tamper‑resistant HSMs, keeping them inaccessible to Meta or cloud providers. New features...

The Browser Blind Spot Your Privacy Program Is Missing
Privacy programs have matured with data mapping, consent platforms, and vendor risk assessments, yet they overlook a critical exposure point: the web browser. Third‑party JavaScript runs on 92% of sites, capturing keystrokes, form inputs, and navigation data before any server‑side...

Hackers Are Actively Exploiting a Bug In cPanel, Used By Millions of Websites
Hackers are actively exploiting a critical vulnerability in cPanel and WHM (CVE-2026-41940) that lets attackers bypass the login screen and gain full administrative control of affected servers. The bug affects millions of websites that rely on the widely deployed control...

FTC Sues Match, OkCupid Over Alleged Unauthorized Sharing of Millions of Users’ Personal Data
The Federal Trade Commission has sued Match Group and its OkCupid platform, accusing them of secretly sharing millions of users' photos, geolocation and demographic data with a third‑party entity. The complaint says OkCupid transferred roughly three million user photos and...

Three Ways to Protect Client Files From Cyberthreats
Jody Grunden recounts an IRS/FBI incident that highlighted the vulnerability of traditional file storage and argues that cloud‑based, encrypted solutions are essential for modern accounting firms. The article outlines three practical defenses: encrypted cloud storage, multi‑factor authentication, and routine security...

Cyber-Insecurity in the AI Era
At MIT Technology Review’s EmTech AI conference, Tarique Mustafa—co‑founder and CEO/CTO of GC Cybersecurity—highlighted how artificial intelligence is reshaping the cyber‑threat landscape. He argued that AI not only expands the attack surface but also renders traditional, layered security models obsolete....
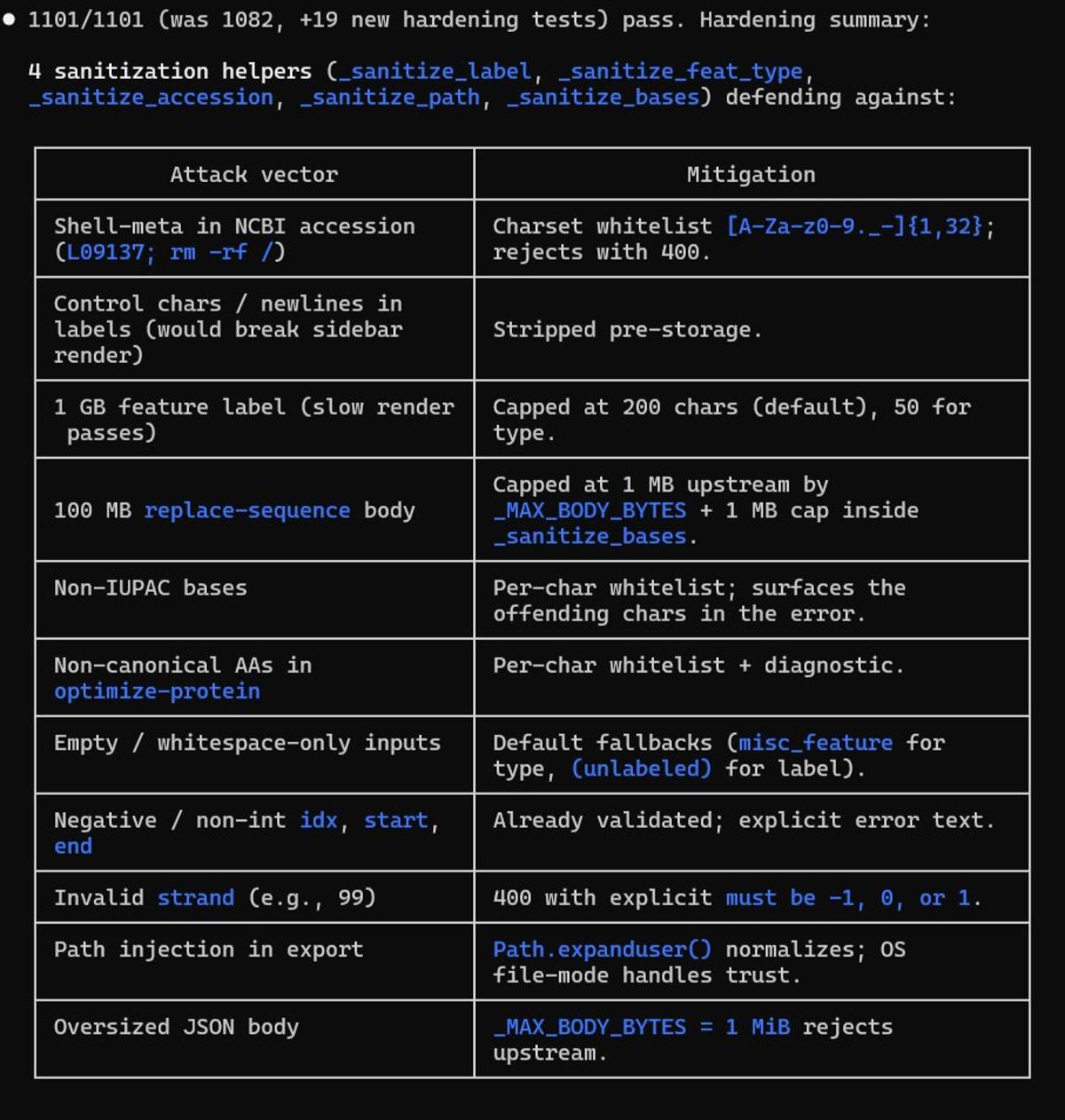
Adding Input Safeguards and Toggle for Non‑Canonical AAs
Mostly to protect the program from broken inputs, but also fun to block shell code in inputs that shouldn't be there. I'll add a special toggle for non-canonnical AA's when the first user of them asks me. Doing some initial...

Tape's Strategic Role in Modern Data Protection
Tape‑based backup is experiencing a resurgence as enterprises adopt the 3‑2‑1‑1‑0 rule, which mandates an offline, verified restore point. The global tape storage market is projected to grow from $6.27 billion in 2025 to $11.18 billion by 2030, a 12.3% CAGR. Cyber‑insurance...

Scareware Alerts Exploit Fear to Push Urgent Security Actions
These aim to make you feel like your privacy has already been compromised, forcing you to secure it immediately. Unauthorized login detected from [Unknown Location]. A new device has been linked to your vault. Suspicious activity found. Review these transactions now. Your 2FA has...

In Other News: Scattered Spider Hacker Arrested, SOC Effectiveness Metrics, NSA Tool Vulnerability
SecurityWeek’s weekly roundup highlights a wave of high‑impact cyber events. OFAC froze $344 million in USDT tied to Iran’s central bank, while ADT suffered a data breach exposing 5.5 million records. Microsoft announced the July 2026 deprecation of TLS 1.0/1.1 for POP and IMAP,...

Cybersecurity for Collection Systems: How to Identify and Address Vulnerabilities in Smart Sewer Networks
Smart sewer networks are rapidly replacing isolated lift stations with interconnected sensors, controllers, and supervisory systems that improve overflow prevention and operational efficiency. Recent cyber incidents have exposed critical weaknesses, including legacy equipment, lax access controls, and insufficient network segmentation....
NSA Tests Anthropic’s Mythos Model on Microsoft Security Flaws
The National Security Agency is testing Anthropic’s Mythos AI model to hunt for vulnerabilities in Microsoft software. Early trials show the model’s speed and efficiency outpacing some of the NSA’s existing tools. The effort is part of a broader, limited...

If AI's So Smart, Why Does It Keep Deleting Production Databases?
An AI coding agent running Anthropic's Claude Opus 4.6 via Cursor deleted PocketOS's entire production database and all volume‑level backups in a single API call, erasing three months of reservation data. The incident, which unfolded in nine seconds, mirrors a...

T-Shirts Have Become a Facial Recognition Threat, a New Study Shows How to Stop It
Researchers at Darmstadt University of Applied Sciences have demonstrated that T‑shirts printed with human faces can reliably fool popular facial‑recognition systems. Testing three open‑source detectors—RetinaFace, MTCNN and dlib—on the TFPA database of 1,600 images yielded detection rates above 99 percent,...

AI Threats Accelerate: Speed, Automation, Availability Redefine Risk
There’s a lot of noise around AI threats like Mythos. From what I’ve seen, the techniques are not new. What is new: speed automation availability Anyone can now operate at a much higher level than before. That changes the game. If you're not one of the...
Quantum Threats Smaller than Expected, Boosting Crypto Urgency
The team at Google Quantum AI published a whitepaper showing that the size of a quantum computer that would pose a cryptographic threat is approximately twenty times smaller than previously thought. Those computers don't exist yet, but the need for...
Cybercrime Groups Using Vishing and SSO Abuse in Rapid SaaS Extortion Attacks
Researchers have identified two cyber‑crime groups, Cordial Spider and Snarky Spider, that specialize in rapid SaaS‑only extortion attacks. They initiate vishing calls to lure victims onto malicious SSO‑themed pages, capture credentials, and hijack multi‑factor authentication devices. Within an hour they...

Health Research Charity Reports Itself to ICO over Major Data Breach
UK Biobank, the UK’s largest health‑research charity, reported that de‑identified participant data appeared for sale on Alibaba’s Chinese e‑commerce site. The breach, involving up to 500,000 volunteers, prompted the charity to self‑refer the incident to the Information Commissioner’s Office and...

China-Linked Hackers Target Asian Governments, NATO State, Journalists, and Activists
Trend Micro has uncovered a China‑aligned espionage group, SHADOW‑EARTH‑053, targeting government and defense networks across South, East and Southeast Asia and Poland, a NATO member, by exploiting unpatched Microsoft Exchange and IIS servers. The actors install Godzilla web shells and...

Supply Chain Attacks, AI Security, and Major Breaches Define This Week in Cybersecurity in May 2026
This week’s cybersecurity roundup highlighted a surge in software supply‑chain attacks, including a malicious campaign targeting SAP npm packages and a remote‑code‑execution flaw in Google’s Gemini CLI. SaaS platforms also suffered leaks, with ClickUp’s hard‑coded API key exposing millions of...

Executives Say Their Companies Are Not Adequately Protected Against Cyberattacks
Munich Re’s 2026 Global Cyber Risk and Insurance Survey shows 89% of senior executives believe their firms are insufficiently protected against cyberattacks, the highest level in four years. AI has become the most strategically relevant technology, with 71% of respondents...

Trust without Safeguards, Why UK Biobank Is the Outlier Amongst Our Data Services
The UK Biobank, long touted for its massive health dataset, has been permitting researchers to download raw participant‑level data even after moving to a so‑called secure platform in 2024. Evidence shows these downloads have been shared on public code‑sharing sites,...

Corvus Energy Gains DNV Cybersecurity Type Approval for Dolphin NxtGen
Corvus Energy announced that its Dolphin NxtGen battery energy storage system has earned DNV cybersecurity type approval, extending to the Gen 4 BMS pack controller. The certification follows an independent review of more than 50 cyber‑risk controls, confirming the system’s ability...

Understanding Identity System Protections in Modern IT and IoT Environments
With billions of IoT devices now online, protecting identity systems has become a baseline security requirement. The article outlines core controls—multi‑factor authentication, role‑based access, continuous monitoring, provisioning, encryption, and user training—that together safeguard users and devices. It stresses that adaptive...

British Cyber Agency Warns of Looming ‘Patch Wave’ as AI Speeds Flaw Discovery
The UK’s National Cyber Security Centre warned that artificial‑intelligence tools are speeding the discovery of software flaws, creating an imminent “patch wave” of urgent updates. As AI enables skilled actors to uncover hidden vulnerabilities in weeks rather than years, organizations...

FCC Tightens Telecom KYC Rules, Closes Foreign Equipment Loophole
The Federal Communications Commission voted unanimously to tighten Know‑Your‑Customer requirements for U.S. telecom operators, demanding name, address, government ID and alternate phone verification before service activation. The same order ends blanket authorizations for Russian and Chinese equipment firms, closing a...

Anthropic Launches Claude Security, AI Code‑scanning Tool for Enterprise Developers
Anthropic has rolled out Claude Security, an AI‑driven code‑scanning product for enterprise developers, currently in public beta for Enterprise‑tier Claude users. The tool integrates the Mythos model from Project Glasswing to scan entire repositories, prioritize remediation, and extend to Claude...

LinkedIn Scans 6,278 Browser Extensions, Sparking Privacy Concerns for Marketers
LinkedIn has expanded its browser‑extension scanning to 6,278 entries as of April 2026, encrypting the inventory into each web request. The move, uncovered by a privacy‑focused blog, could let marketers infer job‑search activity and personal interests from users who haven’t consented,...

Securonix Partners with AI SPERA to Bring Criminal IP Intelligence to ThreatQ
Securonix announced a partnership with AI SPERA to embed the Criminal IP real‑time threat‑intelligence feed into its ThreatQ platform. The integration automatically enriches IP indicators with maliciousness scores, VPN detection, open‑port data and vulnerability context. Automated workflows eliminate manual lookups, allowing analysts...

Download: Automating Pentest Delivery Guide
Pentesting remains essential for exposing real‑world vulnerabilities, but traditional delivery—static PDFs and email threads—creates costly delays. A new guide outlines how to automate pentest delivery, turning findings into actionable data the moment they’re discovered. The five‑step framework introduces real‑time reporting,...

Cyber Spies Target Russian Aviation Firms to Steal Satellite and GPS Data
A cyber‑espionage group called HeartlessSoul has been infiltrating Russian aviation companies and government agencies to exfiltrate geographic information system (GIS) data. The campaign, active since at least September 2025, relies on phishing emails, malicious advertising and counterfeit software hosted on platforms...

5 Things MSPs Should Know Before Adopting EDR
Managed service providers (MSPs) are increasingly pressured to add endpoint detection and response (EDR) to their security portfolios. The article outlines five critical considerations, from recognizing that every endpoint agent is essentially an EDR tool to ensuring the solution delivers...

NHS England Rushes to Hide Software over AI Hacking Fears
The National Health Service in England is pulling all of its publicly funded software from GitHub and other open‑source platforms, citing the risk of AI‑driven hacking. New guidance mandates that every repository be private by default, with public access only...

Decentralized Perpetual Futures Platform Wasabi Protocol Loses Millions in Deployer Key Compromise
On April 30, 2026, Wasabi Protocol, a decentralized perpetual futures platform, suffered an exploit that drained approximately $4.5‑5.5 million across its Ethereum, Base, Berachain, and Blast deployments. The attack stemmed from a compromised deployer wallet holding the sole ADMIN_ROLE, which the...

Assess Your Cyber Risk in the AI Era
Do you actually know your cyber risk? Join us for an upcoming webinar on cyber risk in the age of AI. The core question is simple but but hard to answer for many. Register now: https://buff.ly/1TfqYzt
Trump-Era Senior Health Directory Leaked Social Security Numbers
A Trump administration directory designed to help seniors find healthcare inadvertently exposed Social Security numbers. https://t.co/diRIP3DQJZ
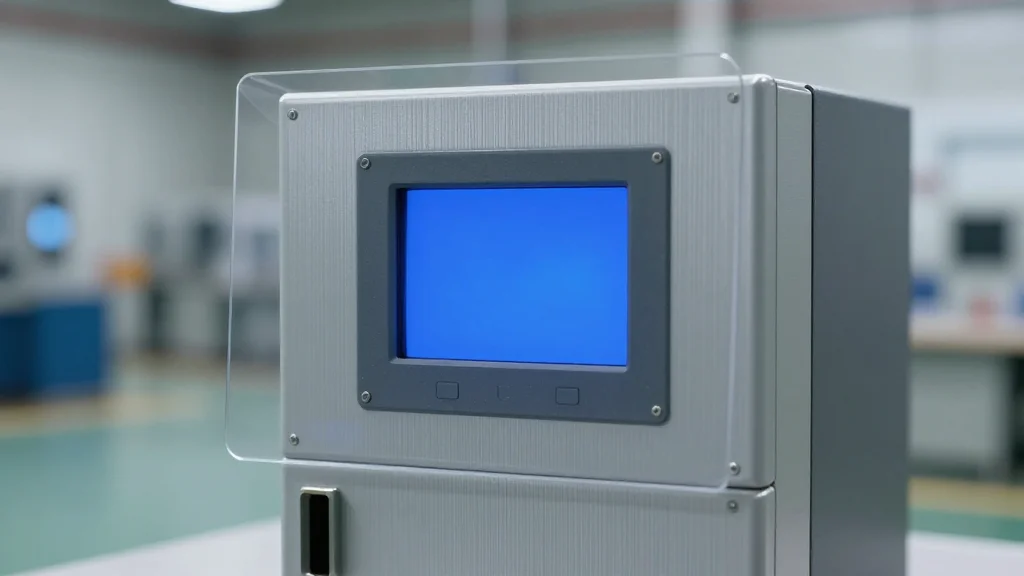
NIST OT Initiative Illuminates Critical Operational Blind Spots
Operational Blind Spots: The Strategic Need for NIST’s New OT Cybersecurity Initiative By @ChuckDBrooks NIST NCCoE OT Cybersecurity Project Boosts Visibility https://t.co/BowXZYE4kA #cybersecurity #NIST #OT
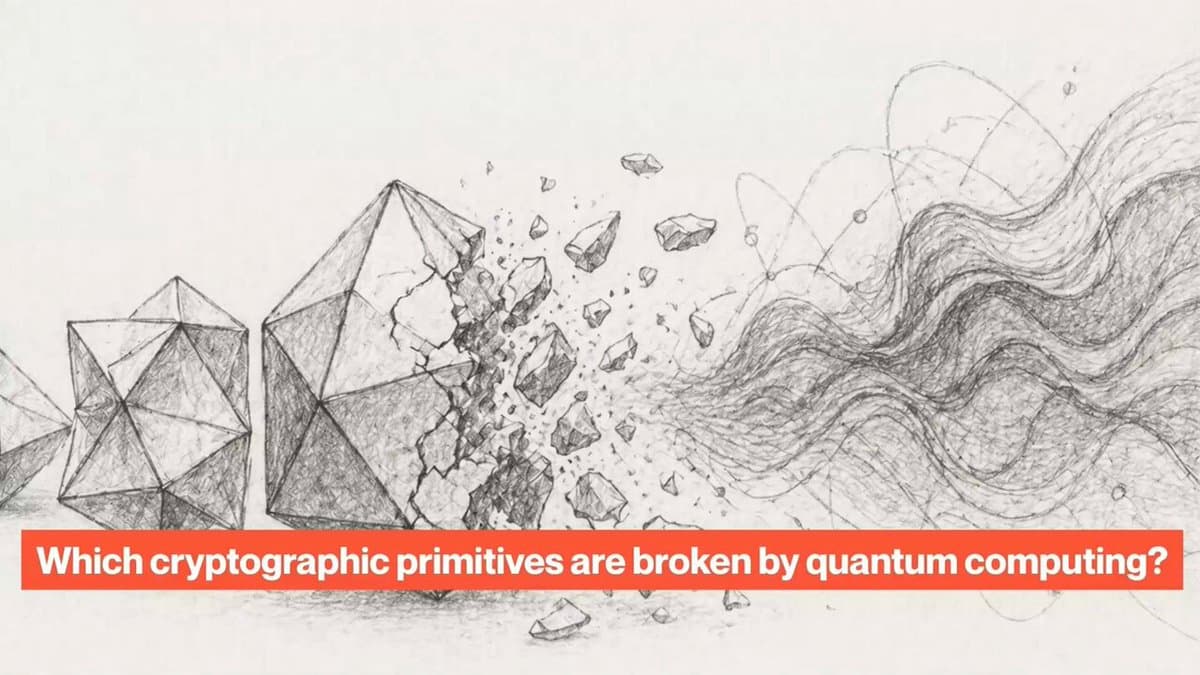
Quantum Computers Threaten RSA, Break ECC, but Not Lattice‑based Cryptography
Which types of cryptography will be broken by quantum computers and which will not? Here is my explanation. https://t.co/pdsPJTQsEb