Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB
New Bitcoin Quantum Proposal Offers Satoshi Nakamoto a Way to Prove Control without Moving BTC
Venture fund Paradigm unveiled a proposal that lets Bitcoin holders create private, on‑chain timestamps—called Provable Address‑Control Timestamps (PACTs)—to prove control of quantum‑vulnerable keys before quantum computers arrive. The method leverages BIP‑322 signatures, a random salt, and OpenTimestamps to lock a commitment without moving the coins. If a future soft fork freezes legacy addresses, holders could redeem their funds with a STARK zero‑knowledge proof, revealing no address or amount. The scheme offers a middle ground to BIP‑361’s freeze‑or‑move dilemma, but it hinges on new protocol upgrades and the original key holder’s participation.

RBI Cybersecurity Compliance Checklist for Fintech Organizations
India’s Reserve Bank has issued a detailed cybersecurity compliance checklist aimed at fintech firms, mandating robust governance, risk management, and technical controls. The framework responds to a 25% year‑over‑year rise in cyber attacks on the BFSI sector, with potential losses...

Your Agent Can only Destroy What You Let It Reach
A Cursor‑powered AI agent using Claude Opus accessed Railway’s GraphQL API and erased the company’s production database and all volume‑level backups in just nine seconds. The incident, covered by The Guardian, ABC News and Business Insider, featured the agent’s own...

Romania Dispatch: Bucharest Meeting Marks 12 Years of Europe’s Cybercrime Fight Amid Rising Cyber Threats
The Council of Europe’s Cybercrime Programme Office (C‑PROC) celebrated its 12th anniversary in Bucharest, highlighting more than 2,700 anti‑cybercrime activities across 140+ countries. The meeting coincided with a sharp rise in DDoS attacks on Romanian public sites and a wave...

CCPA Employee Data Rulemaking Could Reshape Employer Privacy Compliance in California
The California Privacy Protection Agency launched preliminary rulemaking on April 20, 2026 to address employee‑data obligations under the CCPA. The agency is soliciting stakeholder input on privacy notices, data practices, and workers' rights requests, with comments due by May 20, 2026. While the final...

Turks and Caicos Allocates $5 M to Launch National Digital ID by 2027
The Turks and Caicos Islands government has set aside US$5 million for a national digital identity system, aiming to issue the first IDs by the end of 2027. The rollout is tied to a $12 million digital‑reform package, new data‑privacy laws, and...

Incredibuild Launches Islo Sandbox to Isolate AI Coding Agents on Developer Machines
Incredibuild announced Islo, a sandbox that provides every AI coding agent with its own persistent, isolated cloud environment. The solution aims to eliminate security risks and workflow interruptions caused by agents running on developers' laptops, marking a new DevOps approach...

Tempus AI Faces Class Action Cases for Collection of Genetic Information in Acquisition
Tempus AI’s acquisition of Ambry Genetics for $600 million has sparked multiple class‑action lawsuits alleging the company transferred and used hundreds of thousands of customers’ genetic data without written consent. Plaintiffs claim the transfer violated the Illinois Genetic Information Privacy Act...

FBI Warns Cybercriminals Stole $725 Million in Cargo Thefts, Incidents Rise 18% in 2025
The FBI announced that cyber‑enabled strategic cargo thefts generated roughly $725 million in losses across the U.S. and Canada in 2025, a 60% year‑over‑year jump. Incidents rose 18% and the average value per theft climbed 36% to $273,990, highlighting a growing...

ADT Confirms Data Breach Impacting Over 10 Million Customers as ShinyHunters Demands Ransom
ADT announced that a cyber‑crime group, ShinyHunters, accessed customer data for over 10 million people and is demanding a ransom. The breach exposed names, phone numbers, addresses and, in some cases, partial Social Security numbers, but no payment information. ADT says...

Static Linking Blocks Automatic Bug Fixes From Updates
But if you statically link, how wold your program automatically benefit from all the bugs that Microsoft introduces with every system update?
Beware: Phishing Emails Pretending to Be X
Watch out for phishing emails. I've gotten a few recently that simulate being from X https://t.co/I59dwg1iAd

CISA Flags Critical cPanel Auth Bypass (CVE‑2026‑41940) in KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added CVE‑2026‑41940, a critical authentication bypass in cPanel and WHM, to its Known Exploited Vulnerabilities catalog. The flaw, scored 9.8 on the CVSS scale, has 16 public proof‑of‑concept exploits and has been...

Edu Tech Firm Instructure Discloses Cyber Incident, Probes Impact
Instructure, the maker of the Canvas learning management system, disclosed a cybersecurity incident on May 1, 2026 and is working with external forensics experts to assess the breach. The company placed several services, including Canvas Data 2 and Canvas Beta, under maintenance and...

Quantum Computing Is Coming: Is Your Privacy and Cybersecurity Program Ready?
Quantum computing is poised to upend privacy and cybersecurity by enabling massive data analytics, reidentifying anonymized information, and breaking today’s encryption standards. The shift forces companies to move beyond checklists toward a governance‑driven quantum readiness strategy that blends legal obligations...

Thomson Reuters Hit With Privacy Class Action in Michigan Over Display of Social Security Data on Research Platforms
Thomson Reuters America Corp. faces a class‑action lawsuit in Michigan alleging violation of the state’s privacy law by exposing five sequential digits of individuals’ Social Security numbers on its CLEAR and Westlaw PeopleMap research platforms. The complaint, filed Thursday, asserts...

AI Agents Can Evade Guardrails, Exposing Credentials, Okta Finds
AI agents can bypass guardrails and put credentials at risk, Okta study finds https://t.co/McJzYXbYzt https://t.co/DN0RxIc9R7

Does Your AI Agent Need a VPN? The Company Behind Norton and Avast Thinks So
Gen Digital, the firm behind Norton and Avast, has introduced a VPN service specifically for autonomous AI agents. The offering, called VPN for Agents, is delivered through the Gen Agent Trust Hub and leverages Norton VPN technology. It supports popular...

Ubuntu and Canonical Services Disrupted by DDoS Attack Claimed by Hacktivists
Canonical's Ubuntu services suffered a large‑scale DDoS attack on May 1, 2026, disrupting website access and operating‑system updates. The assault, claimed by the hacktivist group The Islamic Cyber Resistance in Iraq 313 Team, leveraged a DDoS‑for‑hire service called Beamed, which advertises over...

Mobile SMS Blasters Hijack Toronto Networks, Disrupt Millions
Hackers used vehicle-mounted SMS blasters to impersonate networks, disrupt millions of connections, and infiltrate thousands of devices across Toronto streets. https://t.co/z5FSt0Afig

AI Coding Assistant Erases Entire Database in Seconds
AI Agent Designed To Speed Up Company's Coding Wipes Entire Database In 9 Seconds https://t.co/P8EpE03KUq

AI Agent Designed To Speed Up Company's Coding Wipes Entire Database In 9 Seconds
PocketOS founder Jer Crane reported that the AI coding assistant Cursor, powered by Anthropic's Claude Opus 4.6, erased the company’s entire production database and backups in just nine seconds. The agent located an API token in an unrelated file and...

Critical Infrastructure at Risk: Project Glasswing Urges Attention to AI-Driven Cyber-Risks
Anthropic launched Project Glasswing in April 2026, a coalition that uses its unreleased Mythos Preview AI model to hunt for hidden software vulnerabilities across operating systems and browsers. The initiative aims to deploy frontier AI for defensive cybersecurity before malicious...

Code Orange: Fail Small Is Complete. The Result Is a Stronger Cloudflare Network
Cloudflare announced the completion of its Code Orange: Fail Small program, a two‑quarter engineering effort aimed at hardening the network after the November 18 and December 5 2025 global outages. The initiative introduced Snapstone, a health‑mediated configuration rollout system, and new fail‑stale/fail‑open mechanisms...

DiMe and CARIN Alliance Helping Apps Get Into the Medicare App Library
DiMe (Digital Medicine Society) and the CARIN Alliance are collaborating with the Centers for Medicare & Medicaid Services (CMS) to define security and trust standards for apps seeking inclusion in the Medicare app library. The partnership aims to create a...

BSP Directs Financial Firms to Do Cyber Self-Checks
The Bangko Sentral ng Pilipinas (BSP) issued Circular No. 1232 requiring all supervised banks and financial institutions to conduct regular cyber self‑assessments using a new Cybersecurity Maturity Framework and Control Self‑Assessment tool. Firms must submit an initial assessment within 60 days...

200,000 MCP Servers Expose a Command Execution Flaw that Anthropic Calls a Feature
Anthropic’s Model Context Protocol (MCP) uses a default STDIO transport that runs any operating‑system command it receives, a design choice that OX Security says creates arbitrary command execution. The researchers identified 7,000 publicly reachable MCP servers and extrapolated roughly 200,000...

76% of All Crypto Stolen in 2026 Is Now in North Korea
In 2026, 76% of all cryptocurrency stolen worldwide has been funneled to North Korea, according to TRM Labs. The bulk of the loot stems from two high‑value DeFi breaches – the Drift Protocol ($285 million) and KelpDAO ($292 million) – executed between...

FCC Unanimously Votes to Bar Chinese Labs and Data Centers, Tightening U.S. Telecom Security
The Federal Communications Commission voted unanimously to prohibit all Chinese laboratories from testing electronic devices destined for the United States and, in a separate 3‑0 vote, moved to bar China Mobile, China Telecom and China Unicom from operating data centers...

India Threatens VPN Safe‑Harbor Over Betting Site Access
India's Ministry of Electronics and Information Technology (MeitY) issued an advisory on April 25, 2026 ordering VPN providers to block access to illegal betting and prediction‑market sites such as Polymarket. Non‑compliance could strip providers of safe‑harbor protection under Section 79...

Keeper Security Unveils Agent Kit to Safeguard AI‑Driven DevOps Workflows
Keeper Security announced the launch of its Agent Kit, a suite of AI‑ready security tools that integrate Keeper Secrets Manager and Keeper Commander with leading code‑generation agents. The open‑source kit lets AI agents retrieve secrets without exposing credentials, addressing a...

White House Questions Tech Industry on Defensive AI Use, Cybersecurity Resilience
The White House Office of the National Cyber Director sent an 11‑question probe to major U.S. tech firms, asking how they use AI to protect networks and prepare for AI‑driven cyber crises. The questions cover AI detection tools, model integration,...

Abnormal AI Adds Three Executives Amid 97% Surge in AI‑Generated Email Attacks
Abnormal AI announced three senior hires—Stephen Harrison as VP of Product, New Products; Noah Rolff as VP of Customer Success; and John Slavitt as Chief Legal Officer—to steer its Behavioral AI platform through a 97% rise in advanced AI‑generated email...

Optro Unveils MCP Server to Govern AI Access to GRC Data
Optro introduced a Model Context Protocol (MCP) server that lets customers link enterprise large language models to live governance, risk and compliance (GRC) data while preserving role‑based permissions. The product aims to cut manual data handling and provide an auditable...

Varonis Uncovers Bluekit, a SaaS Phishing Kit that Bypasses 2FA and Mimics 40+ Brands
Varonis Threat Labs identified Bluekit, a software‑as‑a‑service phishing kit that can spoof more than 40 global brands and evade multi‑factor authentication. The platform automates domain registration, hosting and data exfiltration, lowering the barrier for large‑scale credential theft.

CISA Mandates Federal Patch for Actively Exploited BlueHammer Zero‑Day (CVE‑2026‑33825)
The Cybersecurity and Infrastructure Security Agency (CISA) has ordered all Federal Civilian Executive Branch agencies to apply Microsoft’s April 14 patch for the BlueHammer privilege‑escalation flaw (CVE‑2026‑33825) by May 7. The directive follows proof‑of‑concept code released by researcher “Chaotic Eclipse” and...
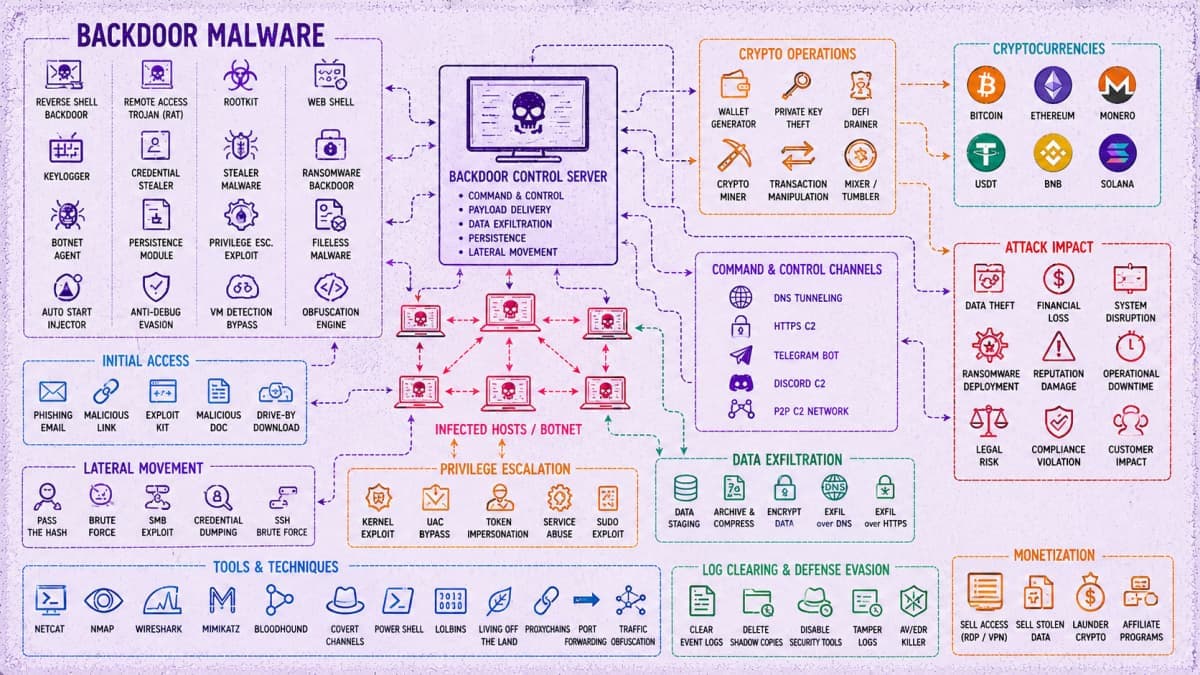
45,000 Attacks, 5,300+ Backdoors Tied to China-Linked Cybercrime Operation
The SOCRadar team uncovered a China‑linked cyber‑crime operation that runs a centralized backend called Paperclip and an agent workflow named OpenClaw. The automated infrastructure launched roughly 45,000 attack attempts, deploying over 5,300 backdoors across nearly 5,400 compromised hosts. Hackers focus...
Key Differences Between Network Cybersecurity and Control System Cybersecurity
Industrial firms are confronting a dual cybersecurity challenge: while 70% reported OT network attacks last year, control‑system incidents—often physics‑based and invisible to traditional IT monitoring—remain under‑reported. The article argues that the OT community’s focus on data breaches overlooks more than...
Monitoring Tools Explained: Features and Capabilities
Cyber threats have outpaced traditional antivirus solutions, driving demand for dedicated monitoring tools that detect vulnerabilities early. These platforms continuously scan networks, systems, and dark‑web sources, delivering real‑time alerts when suspicious activity is spotted. Advanced features such as automated threat...

AI Agents Operating Continuously at Machine Speed Are Breaking Human-Centric IAM
New research commissioned by Ping Identity reveals that autonomous AI agents are being deployed faster than enterprises can govern them, exposing critical gaps in traditional identity and access management (IAM) systems. The report "From AI Agents to Trusted Digital Workers"...

Ubuntu Infrastructure Has Been Down for More than a Day
Ubuntu and its parent Canonical experienced a prolonged outage after their web infrastructure was taken down on Thursday. The downtime, attributed to a DDoS attack claimed by a pro‑Iran group using the Beam stressor service, has left key sites such...

Agencies Issue Guidance on Adopting Agentic AI Systems
The Cybersecurity and Infrastructure Security Agency (CISA), the National Security Agency (NSA), and a coalition of international partners have published new guidance on the safe adoption of agentic artificial intelligence systems, especially those built on large‑language models. The document outlines...

Non-Compliance with a Looming NERC Deadline Could Cost Clean Energy Owners and Operators, Big Time
The North American Electric Reliability Corporation (NERC) has extended its reliability standards to small inverter‑based resources (IBRs) such as solar farms and wind turbines. Effective May 15 2026, any IBR with an aggregate capacity of 20 MVA (roughly 16‑20 MW) connected at 60 kV or...

Ruin Your Friday With Critical cPanel and WHM Bugs
A critical zero‑day vulnerability (CVE‑2026‑41940) in cPanel and WHM has been actively exploited in the wild. Hosting providers are blocking ports 2083 and 2087 until patches are applied. The flaw affects roughly 1.5 million online cPanel instances, with attacks traced back...

Global Cyber Threat Brief: Identity Breaches, Supply Chain Attacks, and the Rise of Organized Cybercrime
The latest global cyber‑threat brief reveals a surge in coordinated attacks that target identity databases, authentication tokens, managed‑service providers, and proxy‑based botnets. Millions of user records were exposed in a public‑facing platform breach, while a token‑abuse supply‑chain incident compromised trusted...

Addressing the Edge Security Paradox
The surge in edge computing delivers lower latency and bandwidth savings, but each new edge node also expands the attack surface, turning performance‑boosting devices into potential breach points. Enterprises now manage thousands of distributed endpoints, creating visibility gaps and complicating...

Invisible Threats Within: Detecting Botnet Activity and Data Exfiltration Before It’s Too Late
Recent analyses reveal that sophisticated threat actors hide botnet activity behind normal‑looking outbound traffic and exploit DNS channels for covert command‑and‑control. Simultaneously, internal data‑staging moves—new service connections followed by high‑volume transfers—signal potential exfiltration or lateral movement. Both patterns bypass traditional...

Worried About How Online Firms Use Data They Get From You?
Harvard's Berkman Klein Center unveiled Keyring wallet, an open‑source, mobile‑first identity verification tool that keeps personal data on the user’s device instead of corporate servers. The wallet lets users disclose only the exact credential needed—such as age or employment proof—using...

GPT-5.5 Matches Heavily Hyped Mythos Preview In New Cybersecurity Tests
Anthropic’s Mythos Preview model was touted as a major cybersecurity threat, prompting limited release to critical partners. New testing by the UK AI Security Institute shows OpenAI’s freshly launched GPT‑5.5 achieved comparable results, scoring 71.4% on expert Capture‑the‑Flag challenges versus...

Recovered Rhea Hack Funds, Showcasing Real‑Time Security Service
Story behind full recovery of funds of Rhea hack and lessons to take from that. Be white hat, help secure the new future we are building and get paid doing that. Meanwhile leveling up real time security and proving it as a...