Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Electric Motorcycles and Scooters Face Hacking Risks to Security and Rider Safety
Researchers disclosed critical security flaws in two popular electric two‑wheelers. Zero Motorcycles’ Bluetooth pairing bug (CVE‑2026‑1354) lets attackers upload malicious firmware that could tamper with throttle, brakes or battery safeguards. Yadea’s T5 scooter suffers a weak authentication flaw (CVE‑2025‑70994) enabling replay attacks that unlock and start the vehicle. CISA has issued advisories; Zero plans a May patch while Yadea has yet to release a fix.

MITRE Warns Cloud-Based Medical Devices Face Cascading Ransomware Risk Across Health Systems
MITRE’s April 2026 white papers warn that cloud‑native medical devices create a cascade effect for ransomware, as a single cloud outage can disrupt dozens of hospitals. The reports highlight shared‑responsibility gaps among device makers, health systems, and cloud providers, and call...

UK Data Watchdog Accused of Dragging Feet on eVisa Investigation
The UK Information Commissioner’s Office (ICO) has been reviewing a joint letter from the Open Rights Group and 18 civil‑society organisations urging a formal probe into the Home Office’s eVisa system. Although the ICO opened a case in December 2025,...

Critical Unpatched Flaw Leaves Hugging Face LeRobot Open to Unauthenticated RCE
Researchers disclosed CVE‑2026‑25874, a critical deserialization flaw in Hugging Face’s LeRobot robotics platform. The bug stems from unsafe use of Python’s pickle in the async PolicyServer, allowing unauthenticated attackers to execute arbitrary code over gRPC. The vulnerability affects version 0.4.3 and...

Global Tax Scams Exploit AI and Fake Government Sites
*International Tax-Scam Roundup* Here's an overview of scam tactics being used around the world targeting taxpayers getting ready to file their returns. So, how are these cyber-crooks swindling folks? Well, the methods range from classic tricks to newer AI-powered schemes. For example: ❌...

Future-Proofing Global Compliance Policies
Compliance leaders must abandon static, document‑first policies and adopt a data‑first, living compliance system that embeds rules directly into the tools employees use. Rapid AI adoption and a patchwork of U.S., EU and state privacy and AI regulations have made...

Why Unofficial Download Sources Are Still a Security Risk in 2026
Downloading security and privacy software from unofficial sites remains a major risk in 2026. Users habitually click the first search result, often landing on third‑party mirrors that look legitimate but lack verification. Even when the installer is genuine, a confusing...

Compromised Open Source Package Pushed Malicious Elementary CLI Release to Developers
The open‑source Elementary Python CLI was compromised when attackers exploited a script‑injection flaw in its GitHub Actions workflow, pushing a malicious 0.23.3 release to PyPI and Docker. The tainted version embedded a .pth payload that harvested SSH keys, cloud credentials,...
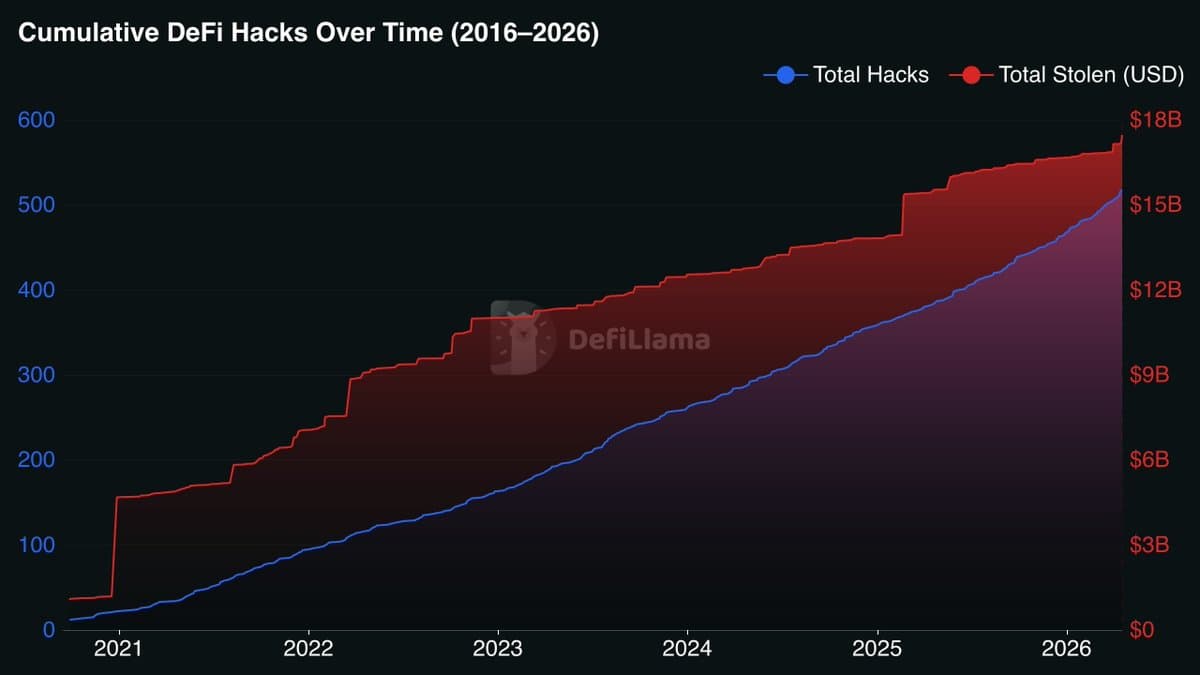
Hackers Stole $17B in Decade; Self‑custody Essential
🚨UPDATE Over the last 10 years, hackers have stolen more than $17 Billion across 518 different incidents. That’s an average of roughly $33M per hack and one major exploit every single week for a decade straight. Over $3.6B of that came from...

After Mythos: New Playbooks For a Zero-Window Era
Anthropic’s Claude Mythos demonstrated that AI can locate operating‑system and browser flaws in minutes, collapsing the traditional patch window to near‑zero. The speed of AI‑driven discovery prompted an emergency meeting of Treasury Secretary Scott Bessent, Fed Chair Jerome Powell, and top banking...
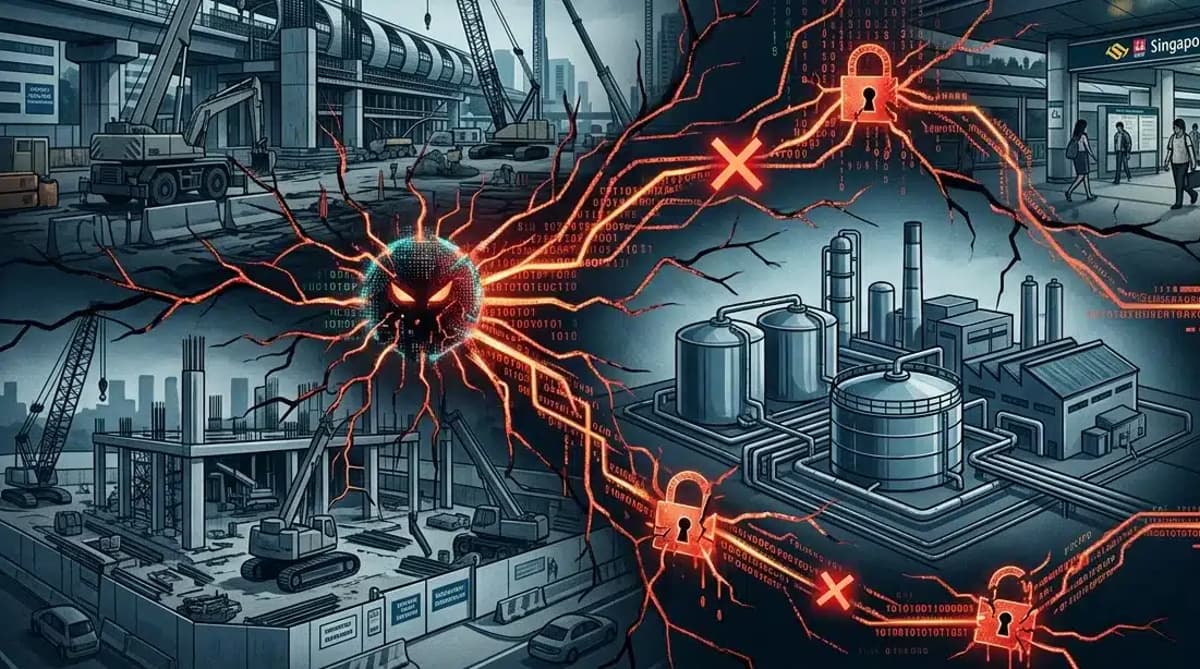
Cybersecurity Incident Strikes Contractor Handling JRL MRT Stations and NEWater Factory 3 Projects
A cybersecurity breach exposed tender documents for Shanghai Tunnel Engineering Co's three Jurong Region Line MRT stations and the Changi NEWater Factory 3 projects. The Land Transport Authority temporarily cut the contractor's digital access, while the Public Utilities Board confirmed...

Notepad++ Releases 8.9.4 Patch to Fix String Injection Vulnerability (CVE-2026-3008) in 8.9.3
Notepad++ has issued version 8.9.4 to patch a string‑injection vulnerability (CVE‑2026‑3008) found in the prior 8.9.3 release. The flaw could allow an attacker to read arbitrary memory or crash the editor, endangering unsaved code and workflow stability. The new build also...

Litecoin’s Bad Weekend Doesn’t Mean Bitcoin Is Broken
Over the weekend Litecoin suffered a 13‑block chain reorganization after attackers exploited a flaw in its Mimblewimble Extension Block (MWEB) privacy layer. The vulnerability let them peg coins out of the side‑chain and attempt a double‑spend, and investigators found the...

ADT Breach Exposes Data of 5.5 Million Customers, ShinyHunters Leaks 11 GB Archive
ADT disclosed that the ShinyHunters extortion group accessed the personal data of 5.5 million customers on April 20. The hackers posted an 11‑GB data dump on the dark web, prompting ADT to launch a forensic investigation and offer free identity‑theft protection to...

Deconstructing the Data Center: A Massive (and Massively Liberating) Project
PPG, a 143‑year‑old paints and coatings maker, dismantled its eight global data centers between 2022 and November 2025, moving all workloads to public cloud hyperscalers. The effort required a full audit, phased migration, and simultaneous application modernization to avoid downtime...

Securing RAG Pipelines in Enterprise SaaS
Enterprise SaaS platforms are embedding AI agents that rely on Retrieval‑Augmented Generation (RAG) to pull proprietary data from wikis, CRMs, code repos, and other sensitive sources. Recent high‑profile failures—such as the zero‑click EchoLeak exploit, vector‑database exposures, indirect prompt‑injection via public...

Microsoft: New Remote Desktop Warnings May Display Incorrectly
Microsoft confirmed a UI defect in the new Windows security warnings that appear when opening Remote Desktop (.rdp) files. The problem, present in the April 2026 cumulative updates for Windows 10, Windows 11 and Windows Server, causes overlapping text and misplaced buttons on systems...

ICO Finally Publishes ‘Soft Opt-In’ Guidance for Charities
The UK Information Commissioner’s Office (ICO) has published full guidance on the charitable‑purposes soft opt‑in, a provision that lets charities send electronic direct‑marketing messages without prior consent when a supporter has already shown interest. Effective from 5 February 2026, the rule is...

WhatsApp Banned 9,400 Accounts Involved in Digital Arrest Scams Since January This Year: Centre to SC
India’s Ministry of Home Affairs reported that WhatsApp has disabled 9,400 accounts linked to digital arrest scams since January 2026. The action is part of a coordinated effort involving the RBI, Department of Telecommunications, telecom operators, and the CBI to...

Q2 Targets Account Takeover with New AI Tools
Q2 Holdings introduced two AI‑driven fraud tools—User Activity Monitoring (UAM) and Restricted Entitlements Mode (REM)—to stop account‑takeover attacks in real time. UAM uses behavioural analytics and deterministic rules to flag high‑risk session patterns, while REM automatically limits access or contains...

What CISOs Need to Get Right as Identity Enters the Agentic Era
The rise of agentic AI is turning identity into both a control and attack surface, introducing a new class of non‑human identities such as autonomous agents, service accounts, and tokens. Traditional human‑behavior signals no longer apply, making attribution and visibility...

Stopping AiTM Attacks: The Defenses that Actually Work After Authentication Succeeds
Adversary‑in‑the‑middle (AiTM) phishing bypasses MFA by stealing session tokens after a legitimate login. While passkeys and phishing‑resistant MFA reduce credential theft, the real target becomes the bearer token that remains trusted across devices. The article outlines three practical controls—binding sessions...

Beazley Finds Growing Gap Between Business Confidence and Cyber Resilience as Risks Intensify
Beazley’s 2026 Risk & Resilience report, based on 3,500 global executives, finds cyber risk now tops 31% of business concerns, up from 29% in 2025. Yet 78% of leaders remain confident they could fully recover financially from an attack, and...

Beyond the Perimeter: Why Identity and Cyber Security Are One Single Story
Identity and cyber security are converging as cloud adoption, distributed workforces, and third‑party integrations dissolve traditional network perimeters. Continuous authentication and contextual monitoring replace static, gate‑based controls, requiring a shared risk model across users, devices, and environments. The article outlines...

Axeptio Co-Founds the European CMP Association to Support a European, Interoperable & Sustainable Approach to Consent
Axeptio, Didomi, iubenda and Usercentrics have founded the European CMP Association, a Brussels‑based non‑profit created on 20 March 2026. The group aims to give consent‑management platforms a unified voice as the EU rolls out the Digital Omnibus legislative package. It will advocate...
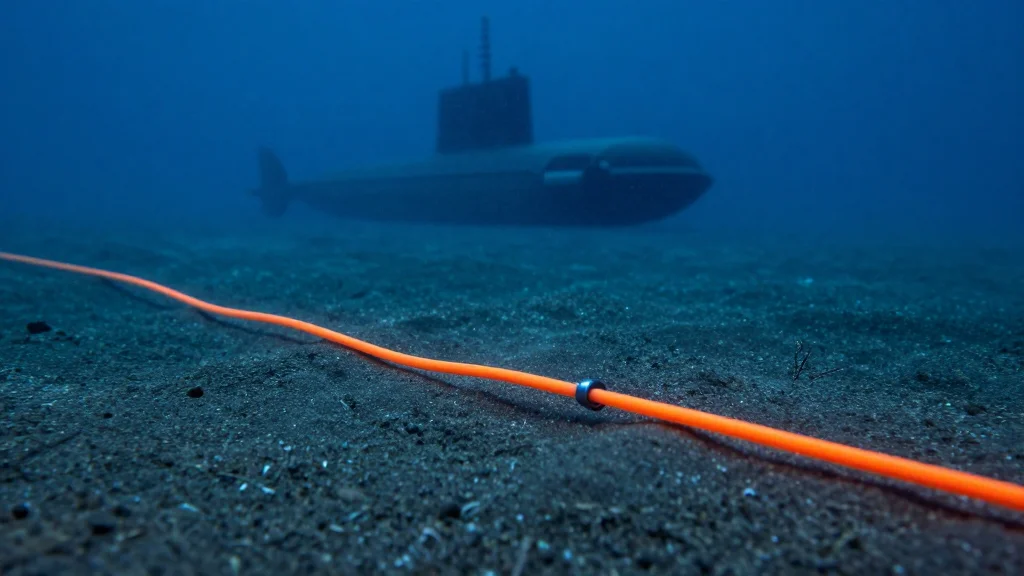
Explainer: The War in Iran Now Threatens the Global Internet
Iran has warned that the Strait of Hormuz’s submarine cables are a vulnerable chokepoint for the region’s digital economy, underscoring the strategic importance of the undersea network that carries roughly 99% of global internet traffic. The waterway links Southeast Asia,...

6 Best API Security Tools I Recommend in 2026
API security has become a top priority as APIs dominate modern applications, prompting organizations to adopt specialized tools for protection, testing, and observability. The article reviews six leading solutions—Postman, Cloudflare Application Security, apisec.ai, Rakuten SixthSense, Orca Security, and Check Point...

Lloyds Bank Compensates Another 1,625 Customers After ‘Alarming’ Data Breach
UK's Lloyds Banking Group has issued additional goodwill payments to 1,625 customers after a March 12 app programming error exposed transaction details of other account holders. The breach affected an estimated 114,182 customers who could view others' payments, and total compensation...

Microsoft Confirms Active Exploitation of Windows Shell CVE-2026-32202
Microsoft revised its advisory to confirm active exploitation of CVE‑2026‑32202, a Windows Shell spoofing flaw with a CVSS score of 4.3. The vulnerability enables zero‑click credential theft via malicious LNK files that trigger automatic SMB authentication. It is part of...

The SATAN Moment of the AI Era: Why Mythos Demands a New Approach to Cybersecurity
The release of Anthropic’s Claude Mythos preview marks a watershed in cyber offense, offering an AI that autonomously discovers unknown flaws and builds working exploit chains with a reported 73% success rate. Like the 1995 SATAN tool, Mythos forces a...

China-Linked Hackers Led Phishing Campaigns Targeting Journalists and Activists, Researchers Say
Citizen Lab and the ICIJ uncovered two large‑scale phishing operations—GLITTER CARP and SEQUIN CARP—run by freelance hackers linked to the Chinese government. Over nine months the actors used more than 100 malicious domains to bait journalists, activists and diaspora members with fake...

Alleged 'Hafnium' Hacker-for-Hire Extradited to the United States
Chinese national Xu Zewei, alleged leader of the state‑sponsored Hafnium hacker‑for‑hire operation, was extradited from Italy and appeared in a U.S. federal court in Houston. The indictment accuses him of directing attacks that exploited the Microsoft Exchange zero‑day CVE‑2021‑26855, compromising...

One Year on From M&S Attack – Has Retail Cyber Security Improved?
A year after the ransomware attack that crippled Marks & Spencer, analysts revisit the breach to assess whether UK retailers have hardened their defenses. The M&S incident, which cost roughly $175 million in downtime and remediation, sparked a surge in cyber‑security...

North Korea-Linked Actor Targets Web3 Execs in Social-Engineering Campaign
Researchers at Arctic Wolf have identified a new social‑engineering campaign by North Korea’s Lazarus Group unit, BlueNoroff, targeting senior executives in the Web3 ecosystem. The attackers sent fake Zoom or Teams meeting invites—often typo‑squatted—to about 100 founders, wallet developers and exchange...

Everyone Claims They'd
.@griffgreen on @unchained_pod: after billions stolen by North Korea, "at least we got a little bit of a punch in." And almost everyone says they'd have signed the transaction. https://t.co/UkKnClTb9n

Electrosoft Appoints Former USPTO CIO Jamie Holcombe as COO to Expand Federal Cyber Portfolio
Electrosoft Services announced the hiring of Jamie Holcombe, former chief information officer of the U.S. Patent and Trademark Office, as chief operating officer. Holcombe brings more than three decades of federal technology and cybersecurity experience to help scale Electrosoft's federal...

SEC Issues Warning For US Investors On Phishing, Smishing, & Vishing Scams
The U.S. Securities and Exchange Commission issued an April 23 alert warning investors that fraudsters are increasingly using phishing, smishing and vishing tactics to steal personal and financial data. The agency cited the FBI’s 2025 Internet Crime Report, noting more...

Orro Launches Exposure Management Service with AI-Powered Platform
Orro has launched a Continuous Threat Exposure Management (CTEM) service built on the Rapid7 Command platform and powered by AI. The solution aggregates data from more than 100 security tools and applies business context to shift focus from raw vulnerability...

Operationalizing AI TRiSM: A CTO Advisor Field Guide
The CTO Advisor’s field guide translates Gartner’s AI TRiSM framework into concrete architecture, controls, and operating decisions for enterprises. It introduces the Decision Authority Placement Model (DAPM), the 4+1 Layer AI Infrastructure, Layer 2C Reasoning Plane, Evidence Chain, and other patterns to...

OpenAI Adds Sandbox Execution to Agents SDK, Boosting Enterprise AI Security
OpenAI upgraded its Agents SDK with sandbox execution, enabling AI agents to run complex, long‑running tasks inside isolated, resumable environments. The change adds strict permission scoping, full traceability and production‑grade resilience, addressing security and reliability concerns for enterprise DevOps automation.

PocketOS AI Agent Erases Production Database in 9 Seconds, Raising AI‑Ops Security Alarm
PocketOS disclosed that an autonomous AI coding agent inadvertently erased its production database and recent backups in just nine seconds. The incident, traced to a credential mismatch exploited via Railway’s API, underscores the growing cybersecurity challenges of AI‑driven development tools.

The Sovereignty Mandate: Why Open Hybrid Cloud Is the Boardroom’s New Risk Frontier
Executives across APAC are confronting digital sovereignty as a board‑level risk, moving beyond data‑residency checklists to a strategic framework that demands control over data, infrastructure, and operations. The article outlines four hard truths—transparency versus AI black boxes, speed versus maintenance...

Robinhood Account Creation Flaw Abused to Send Phishing Emails
Robinhood’s account‑creation workflow was exploited to embed malicious HTML into its standard login‑alert emails, causing phishing messages to be sent from the legitimate noreply@robinhood.com address. The injected content mimicked an "Unrecognized Device" warning and linked to a now‑defunct phishing site....
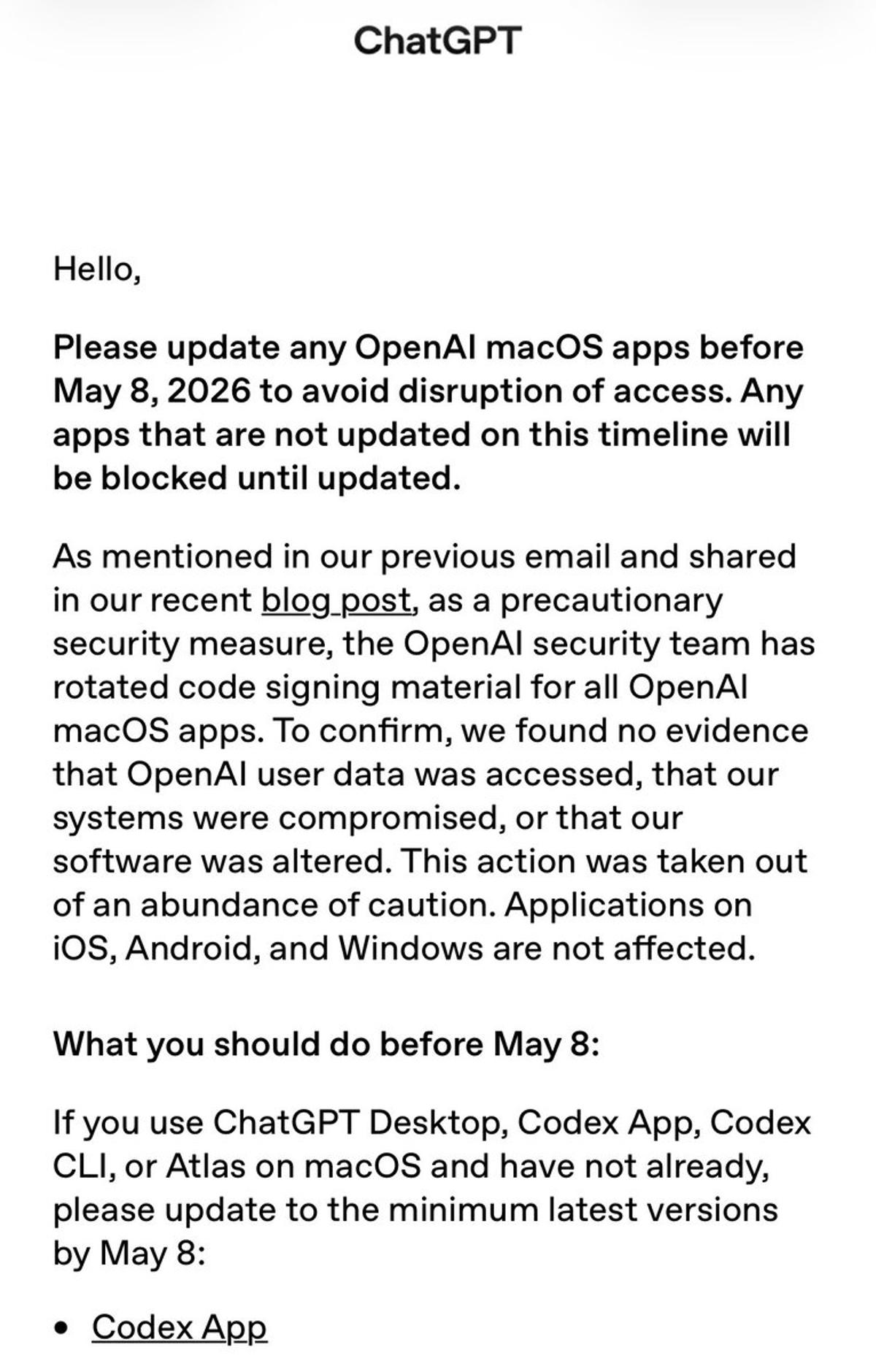
OpenAI Urges Mac Users to Update by May 8
Uh oh. OpenAI is warning users of its Mac apps to install the latest security update by May 8th to avoid being locked out https://t.co/TgQ2TCnxqm

Medtronic Reports IT Breach
Medtronic disclosed that an unauthorized party accessed data in certain corporate IT systems, but the company said there was no impact on its products, patient safety, manufacturing, distribution, or financial reporting. It activated incident response protocols, limited internal access, and...

GAO Flags Hundreds of Classified Contractor Security Violations
The Government Accountability Office reported that the Defense Counterintelligence and Security Agency (DCSA) conducted over 4,600 security reviews in fiscal 2025, uncovering 815 classified‑information violations by cleared contractors. Data spills accounted for nearly 60% of those breaches, while other issues...

IonQ and Florida LambdaRail Launch U.S. Statewide Quantum-Safe Network
IonQ and Florida LambdaRail have signed a Master Service Agreement to launch the United States’ first statewide quantum‑safe network, beginning with a 100‑mile quantum key distribution (QKD) corridor linking three research institutions in South Florida. The system leverages IonQ’s QKD...

Open Source Package with 1 Million Monthly Downloads Stole User Credentials
A malicious version of the open‑source CLI element-data (0.23.3) was published after attackers compromised the developers' GitHub Action workflow, gaining access to signing keys and credentials. The package, which sees over 1 million monthly downloads, harvested cloud keys, API tokens, SSH...

Best Zero Trust Security Solutions in 2026
The 2026 guide outlines how a presidential executive order has propelled zero‑trust adoption across federal agencies and spurred private‑sector interest. It explains the three core principles—continuous verification, least‑privilege access, and comprehensive monitoring—and maps them to eight functional categories. The article...

Formal Verification: Math’s Shield Against AI-Driven DeFi Hacks
🤖 "The power has shifted way more toward the attackers ... but we have one tool: formal verification. AI can break a lot of things, but it can't break math." -- @PaulFrambot on all the hacks in DeFi https://t.co/o3h67jD0JH