Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Toronto SMS Blaster Case Fits Global Pattern of Chinese Cybercrime Operations Linked to State-Level Technology and Remote Command
Canadian police have charged three men with 44 offences after uncovering a mobile SMS‑blasting operation that disrupted over 13 million cellular connections across the Greater Toronto Area. The equipment, built with military‑grade components and shipped from China, was operated from vehicles that broadcast phishing messages to tens of thousands of phones per shift. Investigators say the model mirrors a global network of Chinese‑directed scams that have appeared in Bangkok, Jakarta, Athens and the London Underground. The case highlights Toronto’s emerging role as a command node for transnational cybercrime and illicit finance.

Government Hacking Tools Are Now in Criminals' Hands (with Lorenzo Franceschi-Bicchierai)
A former Trenchant employee covertly sold government‑grade zero‑day exploits to a Russian firm, which subsequently passed the tools to the Russian state and possibly Chinese criminal networks. The leak, detailed by TechCrunch journalist Lorenzo Franceschi‑Bicchierai on the 404 Media podcast,...

Why California's Data Broker Registry Matters More than Its Delete Button
California’s Delete Request and Opt‑Out Platform (DROP) shifts focus from consumer‑driven deletions to a public data‑broker registry that forces disclosure of sensitive data practices. Brokers must report whether they collect minors’ information, geolocation, or health‑related data, giving regulators a centralized...

LINKEDIN BROWSERGATE
Fairlinked’s BrowserGate investigation reveals that LinkedIn embeds a 2.7 MB JavaScript bundle that silently fingerprints every visitor and scans installed Chrome extensions. The system, named APFC/DNA, collects 48 browser characteristics and probes a hard‑coded list that grew from 5,459 to 6,167...

⚡ Weekly Recap: Fast16 Malware, XChat Launch, Federal Backdoor, AI Employee Tracking & More
A newly uncovered Lua‑based malware called fast16, dating back to 2005, predates the infamous Stuxnet worm and appears designed to subtly corrupt high‑precision calculation software. Threat groups are active: UNC6692 is impersonating Microsoft Teams help desks to deliver a Snow...

Are Tech Leaders Risking a Cyber Resourcing Crisis?
Cybersecurity is now a top priority as global cybercrime costs are projected to hit $12.2 trillion by 2031. However, a new Tech Talent & Salary Report 2026 shows that only 29% of cyber professionals received a pay rise last year, making...

Widely Used Browser Extensions Selling User Data
A LayerX Security study identified more than 80 widely used browser extensions that explicitly disclose they sell user data. The extensions span streaming, ad‑blocking and productivity categories and together have millions of installations. While 71% of Chrome Web Store extensions...

Never Click Email Links—Phishers Exploit Gmail Quirks
Phishing emails getting smarter and smarter. Gmail ignores "." in address (and also "+xyz"). Simplest rule is to never click on any link in an email.

Why AI Is Forcing a Reset of the Identity Stack
Gartner warns that the rapid rise of generative AI and autonomous agents is forcing a fundamental reset of the identity and access management (IAM) stack. AI agents are being elevated to first‑class identities that are dynamic, short‑lived, and often operate...

BoE Governor Flags AI‑Driven Cyber Threats as Top Global Risk, Overshadowing Iran Conflict
Bank of England Governor Andrew Bailey told G7 and IMF leaders that the new AI system Claude Mythos, developed by Anthropic, could cripple payment networks and bond markets. The warning shifts focus from the Iran‑Hormuz crisis to a cyber‑security risk that...

Florida Ransomware Negotiator Pleads Guilty, Faces Up to 40 Years in Prison
Angelo Martino, a Florida‑based professional ransomware negotiator, pleaded guilty to conspiring with hackers to launch attacks on at least five U.S. companies. The Department of Justice says he supplied attackers with insurance limits and negotiation tactics, and helped deploy ransomware...

Cyber Security Update
Rail operators face new cyber‑security mandates as Europe’s NIS2 directive and the UK’s Cyber Security and Resilience Bill come into force, imposing board‑level accountability, 24‑hour breach reporting and fines up to 2% of global turnover. At the same time, the...

Regulators Target Hotel AI Use Over Data Privacy
Regulators turn attention to hotel AI governance “Hotels are increasingly deploying AI for functions such as … dynamic pricing, and personalised marketing. These systems rely on large volumes of behavioural and transactional data, raising questions about consent, storage, and secondary...

Germany Suspects Russia Is Behind Signal Phishing that Targeted Top Officials
German prosecutors are probing a suspected Russian‑backed phishing campaign that compromised roughly 300 Signal accounts belonging to high‑level politicians, military officials and journalists. The attackers used a counterfeit Signal security chatbot to trick victims into entering PINs or scanning QR...

OpenSSH Flaw Allowing Full Root Shell Access Lurked for 15 Years
Security firm Cyera disclosed a critical OpenSSH vulnerability, CVE‑2026‑35414, that has existed for roughly 15 years. The flaw stems from mishandling commas in SSH certificate principal names, allowing a low‑privilege identity to be interpreted as root. Because the exploit bypasses...

Singapore Investigates Cybersecurity Incident Involving Government Contractor
Singapore’s Land Transport Authority (LTA) has suspended a construction contractor’s access to its digital platform after the firm was implicated in a cybersecurity breach, Bloomberg reports. The incident prompted an immediate investigation by Singapore’s authorities to determine the scope of...

Securing the Vibe: Tanya Janca on AI-Generated Code, Mythos, and the New AppSec Reality
In this episode of the Resilient Cyber Show, host Chris Hughes talks with application security veteran Tanya Janca about the rapid shift from traditional DevSecOps to "vibe coding," where AI generates most of the code with little human oversight. Janca...

AWS Security Digest #258 - Vercel of Secrets
Vercel disclosed a security incident on April 19, 2026 after an attacker leveraged a compromised third‑party AI productivity tool, Context.ai, to hijack an employee’s Google Workspace account and pivot into Vercel. The breach allowed the threat actor to enumerate and...
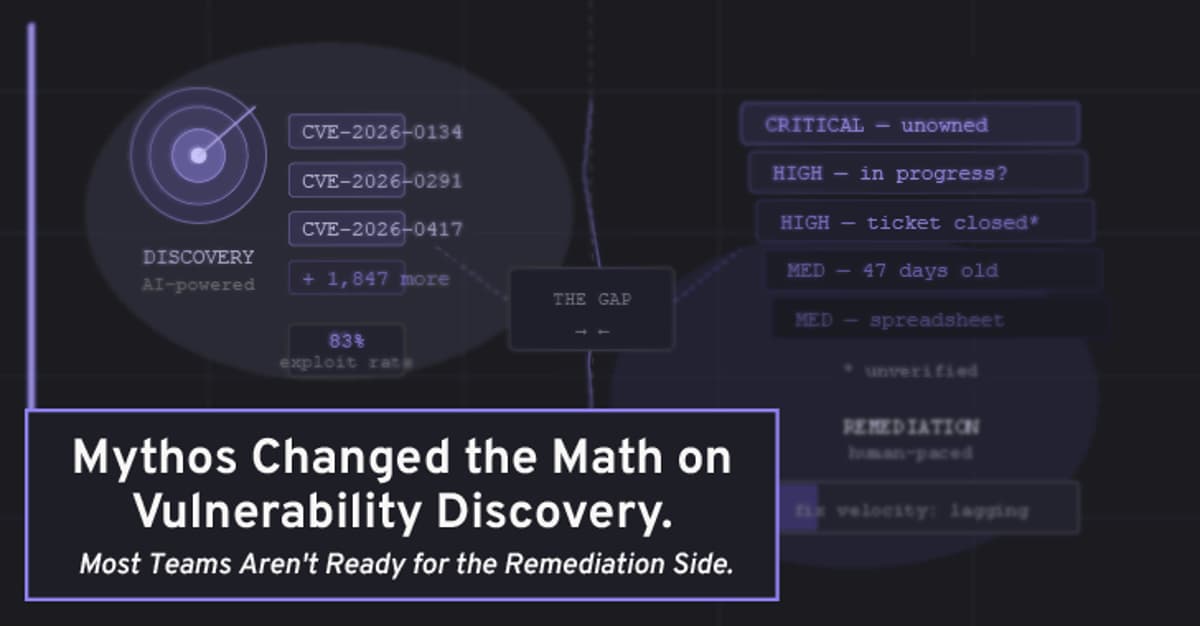
Mythos Changed the Math on Vulnerability Discovery. Most Teams Aren't Ready for the Remediation Side
Anthropic’s Claude Mythos AI dramatically accelerates vulnerability discovery, promising ten‑fold higher finding rates than traditional pentests. However, the article warns that most organizations lack the remediation infrastructure to handle the surge, creating a widening gap between detection and fix. It...

Elisa Ties up with Danske Bank to Protect Finnish Mobile Transactions
Finnish telecom operator Elisa has partnered with Denmark‑based Danske Bank to bolster the security of mobile transactions in Finland. The collaboration will offer customers tools and support to safeguard connected devices, focusing on the vulnerabilities of outdated smartphones and operating systems....

Operation TrustTrap Reveals 16,800 Fake Domains Exploiting User Trust
Cyble Research and Intelligence Labs uncovered Operation TrustTrap, a massive domain‑spoofing campaign that leveraged more than 16,800 fraudulent web addresses to harvest credentials and payment data. The scheme mimics U.S. government portals—especially DMV, toll and vehicle‑registration sites—using a technique called...

OpenClaw Reveals Hidden Security Risks of Agentic AI
OpenClaw, an open‑source platform that lets AI agents share system access, was exposed as a major security liability. A February report identified nearly 43,000 public control panels in 82 countries and a mis‑configured database leaking 1.5 million authentication tokens and 35,000...
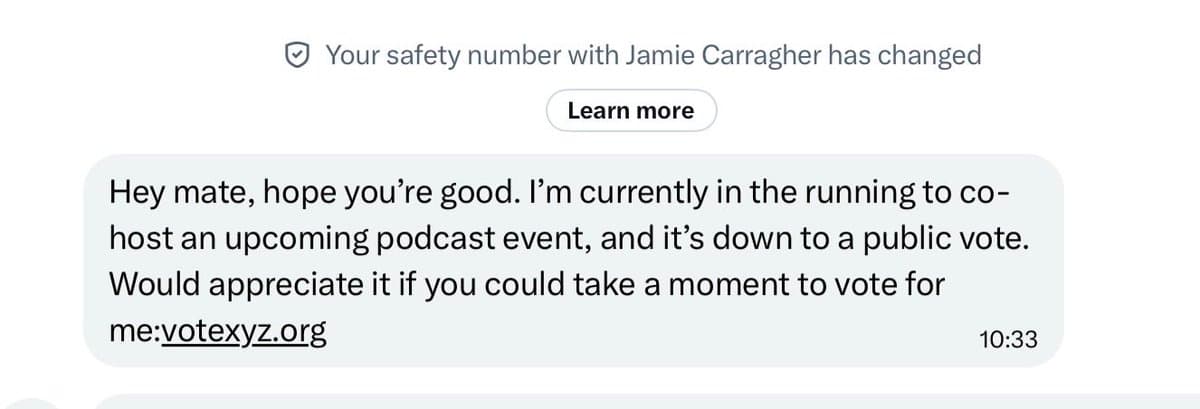
Jamie Carragher's Account Hacked—Avoid Suspicious DM Links
If you get a DM from Jamie Carragher asking to click on a link for a competition or see some unusual posts on his account do NOT engage. Someone has hacked his account and it’s a scam. Has happened to...

Hackers Fabricate Problems, Then Pose as IT Helpdesk
Hackers first create a problem then try to "solve it" by pretending to be IT helpdesk. https://t.co/UqeWuAgF4r
Indian Banks Boost Digital Defence as AI‑driven Cyber Threat Looms
Finance Minister Nirmala Sitharaman said the Indian government is working with banks and cyber agencies after Anthropic’s Claude Mythos AI model was flagged as a major cyber risk. The warning has spurred major Indian banks to upgrade digital‑defence systems, signaling...

Researchers Uncover Fast16, a 2005 Sabotage Framework That Beats Stuxnet
SentinelLABS disclosed Fast16, a malware framework first seen in 2005 that modifies high‑precision calculation software at runtime. The discovery shows the tool predates Stuxnet by five years and highlights a long‑standing threat to software supply‑chain integrity.

Google Settles Android Data‑usage Lawsuit for $135 Million
Google has agreed to a $135 million settlement to resolve a class‑action lawsuit alleging its Android operating system transmitted users’ cellular data without permission. The deal could cover as many as 100 million Android owners, with a deadline to opt out by...

Jamtara Was the Trailer; the Real Story Is AI-Powered Fraud
Indian digital lenders are being hit by AI‑generated synthetic identity fraud. A mid‑size lender lost money after granting loans to 38 AI‑crafted applicants, exposing the limits of rule‑based fraud filters. RBI reports over 36,000 digital payment fraud cases in FY23‑24,...
Vidar Infostealer Spreads via Fake CAPTCHAs, Hides in JPEG and TXT Files
Point Wild’s Lat61 team uncovered a revamped Vidar infostealer that hides its payload in ordinary JPEG and TXT files. The campaign uses fake CAPTCHA prompts, compromised GitHub repositories, and steganography to deliver a multi‑stage, file‑less infection chain leveraging Windows LotL...

NordVPN: Canadian Digital Financial Data Among World’s Cheapest
NordVPN, in partnership with NordStellar, released a tool that maps the street value of digital identities on the dark web, revealing that Canadian data is among the cheapest globally. A stolen Canadian credit‑card lists for about $2, a full identity...

EBay Struggles with Widespread Outage, Disrupting Transactions and API Access
eBay experienced a widespread outage beginning late Sunday, April 26, 2026, that extended into Monday, disrupting core functions such as search, listings, checkout, and its API. Downdetector recorded more than 1,300 user complaints, with reports peaking around 3:30 PM ET. Unverified claims...

Cybersecurity Talent Exodus: 49% of Professionals Consider Leaving Amid Pay Gap and Burnout
A new Harvey Nash Global Tech Talent & Salary Report shows 49% of cybersecurity professionals intend to change jobs within a year, driven by a stark pay mismatch and mounting pressure from AI‑enabled threats. The findings highlight a looming talent...

U.S. Companies Back Sam Altman’s World ID Even as Much of the World Pushes Back
World, the iris‑scanning digital ID platform co‑founded by Sam Altman, announced strategic integrations with Tinder, Zoom and DocuSign to curb fraud and deepfakes. The service, which assigns a "proof of humanity" after scanning a user’s iris, now claims more than...

AI Is Reshaping DevSecOps to Bring Security Closer to the Code
Artificial intelligence is fundamentally reshaping DevSecOps by embedding security controls directly into code‑generation tools, expanding vulnerability detection with large‑language‑model scanners, and automating remediation suggestions. AI‑assisted coding assistants now enforce policies at the point of creation, while LLMs identify logic flaws...

AI PCs, Endpoint Security and the End of Time-Based Refresh Cycles
Enterprises are moving AI workloads from the cloud to the endpoint, giving rise to the AI PC – a laptop or desktop equipped with on‑device neural processing units. Analysts project AI PCs will capture 55 % of the PC market by...
When Security Becomes the Attack Surface: Why Endpoint Protection Must Evolve
Attackers are increasingly disabling the very endpoint tools meant to stop them, turning security agents into a primary attack surface. A recent IDC survey shows 61% of organizations suffered third‑party data breaches and more than half are dissatisfied with current...

The ‘Manager of Agents’: How AI Evolves the SOC Analyst Role
AI is reshaping the Security Operations Center by turning Tier‑1 analysts from data‑gatherers into orchestrators of autonomous agents. Instead of manually investigating each alert, AI agents now query systems, correlate signals and build evidence chains in real time. Analysts shift...

Fast16: Pre-Stuxnet Malware that Targeted Precision Engineering Software
SentinelOne uncovered Fast16, a sabotage‑oriented malware first seen in 2005 that predates Stuxnet by at least five years. The code embeds a Lua virtual machine, uses an encrypted carrier (svcmgmt.exe) and a kernel driver (fast16.sys) to stealthily modify floating‑point calculations...

Firefox Vulnerability Allows Tor User Fingerprinting
Researchers disclosed CVE‑2026‑6770, a vulnerability in Firefox’s IndexedDB API that leaks the internal ordering of database names. The flaw lets unrelated sites generate a stable identifier that survives Private Browsing sessions and links user activity across domains. Because Tor Browser...

FBI, Indonesian Authorities Team to Take Down Site Ripping Off Users for Millions
The FBI’s Atlanta Field Office partnered with Indonesian law‑enforcement to dismantle the W3LL phishing kit operation, which has facilitated roughly $20 million in attempted fraud. The kit, sold for about $500, enabled the theft of over 25,000 compromised accounts and was...

Secret Management in Production: Vault, KMS, and Rotation Strategies
The post outlines a three‑layer secret‑management model that separates key management (KMS), secret storage (Vault or cloud secret managers), and application consumption. It explains envelope encryption, showing how KMS protects data‑encryption keys while Vault handles lifecycle tasks such as rotation,...
Italy Moves to Extradite Chinese National to the U.S. over Hacking Charges
Italy’s courts have approved the extradition of Chinese national Xu Zewei, arrested at Milan’s Malpensa Airport in July 2025, to the United States on cyber‑espionage charges. U.S. prosecutors allege Xu participated in the state‑backed Hafnium (aka Silk Typhoon) campaign that stole...

Data Breaches Expose Surprisingly Odd Email Address Patterns
Fascinating the sorts of email addresses that appear in some of these data breaches 🤣 https://t.co/grfbmi39Qf

A Week in Security (April 20 – April 26)
Malwarebytes’ weekly roundup spotlights a surge of high‑profile security incidents, from the leak of half‑a‑million UK volunteers' medical records on Alibaba to Apple’s emergency iOS patch that stops deleted notifications from being exposed. The report also covers Roblox’s tightened chat...

LABJ Stock Index: April 27
A senior executive discovered that a free AI therapist app had inadvertently captured detailed, confidential information about a family office, highlighting the hidden privacy risks of generative AI. The article warns that AI agents, especially emerging "agentic" models, can store,...

The $700 Million Question: How Cyber Risk Became a Market Cap Problem
Cyber risk has moved from an IT‑only concern to a market‑cap driver, as regulators now require near‑real‑time breach disclosures and investors treat incidents as material financial events. A 5% stock decline on a $14 billion firm translates to roughly $700 million erased...

Safe Vulnerability Disclosure for UK SMEs: A Practical Guide
UK small and medium‑size enterprises can adopt a simple safe vulnerability disclosure process that provides a clear reporting channel, structured triage, and consistent communication. The guide stresses a proportionate policy, dedicated inbox, and ownership to avoid confusion and protect trust....

Get Ready to Be Attacked - NCSC
The National Cyber Security Centre (NCSC) warned that the UK’s critical national infrastructure—from energy and transport to health and finance—is facing a rising risk of severe cyber threats that could cause extended outages, financial loss, and public‑safety hazards. The agency...
Identity Theft Is Really Just Data Theft
#DigitalIdentity #HotTake 1/6 There is no such thing as identity theft; there is only data theft. Data breaches do not represent an “identity” problem but a data quality problem. More: https://t.co/0JJyam6o0T
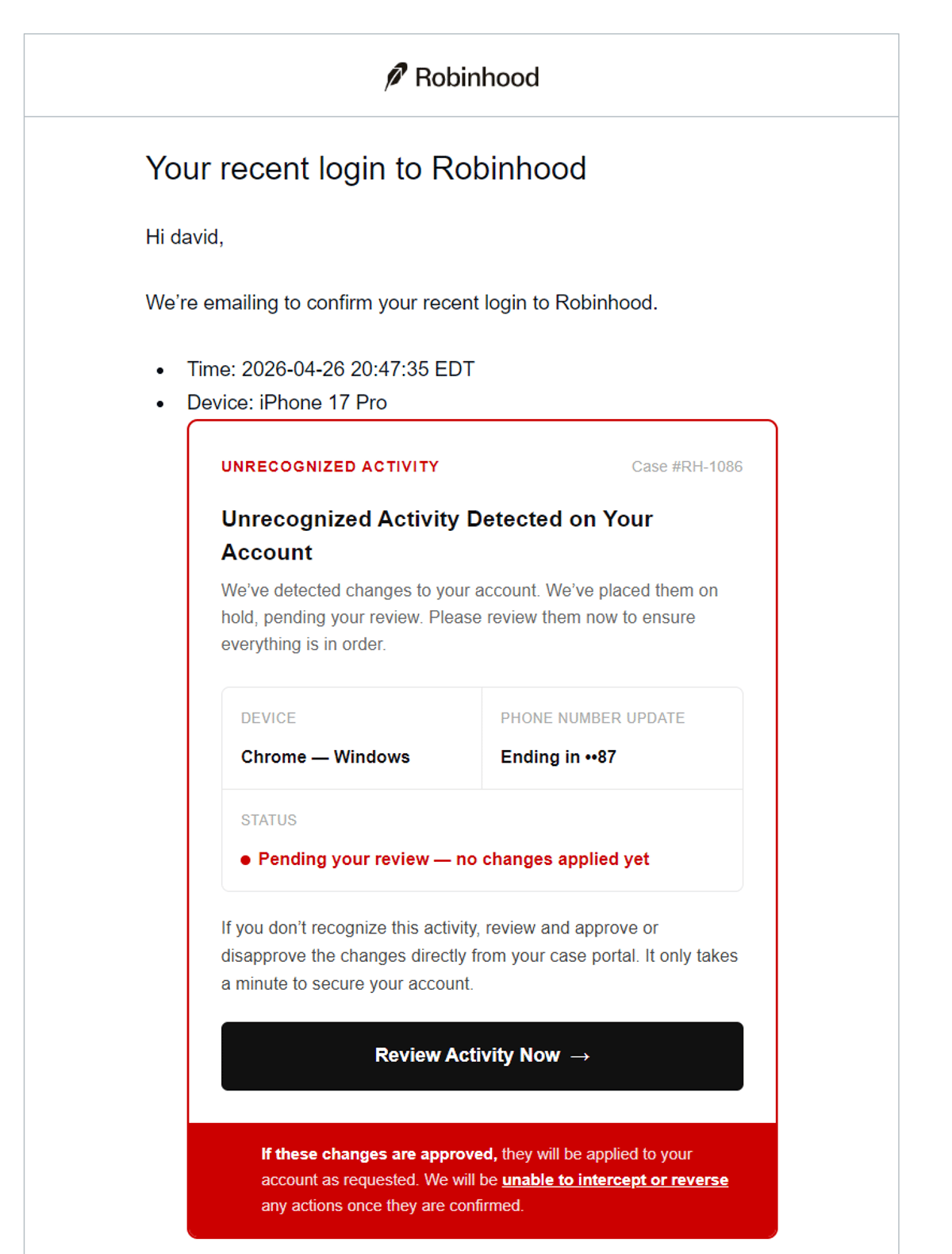
Robinhood Emails Are Phishing Attempts—Stay Vigilant
WARNING: Any emails you get that appear to be from Robinhood (and may actually be from their email system) are phishing attempts. Example: https://t.co/oJilpQqJdp