Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, and Linux CVE‑2022‑0492. Google released patches for the Android bug in June 2026.
Also developing:
By the numbers: Ingeteam receives $82.5M loan from EIB

Open Source Package with 1 Million Monthly Downloads Stole User Credentials
A malicious version of the open‑source CLI element-data (0.23.3) was published after attackers compromised the developers' GitHub Action workflow, gaining access to signing keys and credentials. The package, which sees over 1 million monthly downloads, harvested cloud keys, API tokens, SSH keys and other secrets before being removed 12 hours later. Developers responded by pulling the package, rotating all credentials, and releasing a safe 0.23.4 version. They now urge users to uninstall the tainted release, delete caches, and rotate any exposed secrets.

Best Zero Trust Security Solutions in 2026
The 2026 guide outlines how a presidential executive order has propelled zero‑trust adoption across federal agencies and spurred private‑sector interest. It explains the three core principles—continuous verification, least‑privilege access, and comprehensive monitoring—and maps them to eight functional categories. The article...

EY and IIF Survey Shows Cybersecurity and AI Redefine Risk Leadership in Global Insurance
A joint survey by Ernst & Young and the Institute of International Finance reveals that cybersecurity has become the dominant risk focus for insurers, while artificial intelligence is reshaping the responsibilities of chief risk officers. The findings, released on April...

UNC6692 Combines Social Engineering, Malware, Cloud Abuse
Google Threat Intelligence Group and Mandiant disclosed a new financially motivated threat group, UNC6692, that combines social‑engineering lures, legitimate AWS S3 infrastructure, and custom malware to infiltrate enterprises. The campaign starts with phishing emails and Microsoft Teams messages that deliver...

NIST Scales Back NVD CVE Enrichment, Leaving Vulnerability Gaps for Users
The National Institute of Standards and Technology announced it will stop enriching every CVE in the National Vulnerability Database, focusing only on entries that meet specific criteria such as the CISA KEV catalog and federal software. The shift follows a...

Nessus Agent Flaw Grants SYSTEM-Level Access on Windows
A critical vulnerability (CVE‑2026‑33694) in Tenable’s Nessus Agent for Windows allows local attackers to exploit NTFS junction handling and execute arbitrary code with SYSTEM privileges. The flaw, rated 8.2 on the CVSS v3 scale, enables deletion of arbitrary files and...

500,000 UK Biobank Records Leaked and Listed for Sale on Alibaba
On April 23, 2026, listings for the health records of 500,000 UK Biobank participants appeared on the Chinese e‑commerce platform Alibaba. The data, while stripped of direct identifiers, includes age, sex, socioeconomic status and detailed health measurements, raising re‑identification concerns....
One Password, No Storage: Secure, Easy Logins
Cryptographers created a browser extension password manager that only requires you to remember one #password and stores none of your passwords, allowing you to log in to as many sites as you require. People reported feeling more secure and found...

Medtronic Discloses Security Incident After ShinyHunters Claimed Theft of 9M+ Records
Medtronic confirmed a cyberattack on its corporate IT systems after hacker group ShinyHunters claimed to have stolen more than 9 million records. The breach was limited to internal corporate networks and did not affect product safety, manufacturing, or patient care. Medtronic...
World ID Makes Case for Enterprise-Scale Authentication, but some Aren’t Buying It
World ID, the iris‑scanning identity platform co‑founded by OpenAI CEO Sam Altman, announced new enterprise‑grade features and partnerships with Zoom, DocuSign, Shopify, Okta, Tinder and VanEck. The upgrade adds multi‑key support, account‑based architecture, key rotation, recovery and session management to...

Medtronic Reports Data Breach on Corporate IT Systems
Medtronic disclosed an unauthorized access to its corporate IT systems but said the breach did not affect product, manufacturing or patient‑care networks. The company activated its incident‑response plan, engaged external cybersecurity experts, and is reviewing whether personal data was exposed....

Medtronic Says Cyberattack Did Not Disrupt Its Operations
Medtronic announced on April 24 that a Handala‑linked cyberattack breached its corporate IT systems, granting unauthorized access to data. The company emphasized that its product, patient‑safety, manufacturing, distribution and financial reporting networks remained untouched thanks to strict segmentation. While no...

How CISOs Need To Prepare For The Claude Mythos Era Of Cyberattacks: Experts
Following Anthropic’s preview of Claude Mythos, security leaders warn that AI‑driven vulnerability discovery could trigger a 20‑fold surge in software flaws. Experts say the real danger lies not just in zero‑days but in the attackers’ ability to move laterally, making enterprise‑wide...

Fidelity Fined $1.25 Million Over Client Data Breach
Massachusetts regulators fined Fidelity Brokerage Services $1.25 million after a breach exposed sensitive data of 77,000 clients. An unauthorized party exploited a flaw in the firm’s online document viewer, manipulating image IDs to retrieve records that included Social Security numbers, credit‑card...

How Npm Supply Chain Attacks Actually Work and How Teams Are Stopping Them
A wave of self‑propagating supply‑chain attacks has hit the npm ecosystem, with compromised packages stealing credentials, publishing malicious versions, and spreading like worms. Recent incidents include a hijacked Bitwarden CLI, token‑stealing install scripts, and a takeover of the Axios maintainer...

How Account Takeover Is Reshaping Higher-Ed Cyber Risk
A new Scoop News Group report, funded by Proofpoint, finds account takeover (ATO) attacks now dominate cyber risk on college campuses. More than 70% of successful breaches involve phishing or credential misuse, and nearly 60% of compromised accounts are used...

YouTube Built a Tool To Protect Celebrity Likenesses. But It Does Not Pay Them.
YouTube has launched a deep‑fake detection tool that lets high‑profile individuals upload their likenesses to Google’s cloud for automated monitoring. The service, first opened to politicians and journalists, now covers actors, athletes, creators and musicians, flagging or removing videos that...

Australia Plans Biometric Liveness Detection Refresh for National Digital ID
Australia’s tax authority is issuing an RFI for a SaaS biometric liveness‑detection solution to upgrade its national digital ID, myID, against sophisticated spoofing attacks. The new capability must support up to 10,000 facial verifications per hour with one‑second response times...

IN Groupe Outlines Workforce Identity Risks as Credential Attacks Rise
IN Groupe’s 2026 workforce identity report warns that credential compromises are fueling cyber‑attacks as digital onboarding, hybrid work, and distributed teams expand. It urges firms to align remote identity verification with eIDAS 2.0, GDPR and AML rules, and to adopt password‑less,...

AuthID Adds Post-Quantum Cryptography to Biometric Signature Platform
AuthID, a U.S. identity‑verification firm, has upgraded its biometric digital‑signature platform with three NIST‑standardized post‑quantum cryptographic algorithms—ML‑DSA‑65, SLH‑DSA‑128s, and SLH‑DSA‑256s. The company’s PrivacyKey architecture generates a cryptographic proof of a person’s presence without storing facial templates at rest, offering quantum‑resistant...

SaaS Founders Battle Relentless Bot Scraping of Landing Pages
Something I hear from more and more SaaS founders is that they have to actively fight and mitigate massive bot fleets scraping their pSEO pages. Solo-founder-run businesses fighting billion-dollar companies. Cloudflare mitigates SOME stuff, but there's still a lot to handle. I'm...

Hacker Who Allegedly Carried Out Cyberattacks for China Is Extradited to US
The U.S. Justice Department has secured the extradition of Xu Zewei from Italy, accusing him of acting as a contractor for China’s Ministry of State Security. Prosecutors allege Xu participated in Hafnium‑linked attacks that stole COVID‑19 research from U.S. universities...
Japan Assembles Task Force to Assess AI’s Financial Services Risks
Anthropic's new Mythos AI model uncovered thousands of critical vulnerabilities across operating systems and browsers used by financial institutions, prompting alarm over potential exploitation. In response, Japan announced a high‑level task force comprising the Financial Services Agency, Bank of Japan,...

Senators Seek Answers About Hackers Obtaining Sensitive Student Data From Ostensibly Anonymous Tip Line
Senators Maggie Hassan and Jim Banks have sent a letter to Navigate360 demanding answers after a hack on its P3 Global Intel tip line reportedly exposed sensitive student information. The company, which provides anonymous safety‑reporting tools to more than 30,000...
Apple Sends a “Signal” To Law Enforcement: EDiscovery Trends
Apple disclosed and patched a logging flaw that caused iOS devices to retain push‑notification snippets of Signal messages for up to a month, even after the messages disappeared or the app was removed. The retained data allowed the FBI to...

Eurail Breach Exposes Passport Data, Fuels Dark Web Identity Trade
A cyberattack on Eurail in December exposed passport numbers, personal details and contact information of more than 300,000 customers, and the data appeared for sale on the dark web last week. Travelers are scrambling to replace passports, with a UK...

ShinyHunters Leaks Data of Udemy, Zara, 7-Eleven in Salesforce Linked Breach
The ShinyHunters hacker group posted dark‑web listings that claim to expose data from Udemy, Zara and 7‑Eleven, all allegedly harvested from Salesforce‑linked environments. Udemy’s dump is said to total 2.3 GB and over 1.4 million records, 7‑Eleven’s 12.8 GB contains more than 600,000...
What the Medtronic Breach Means for Security Experts
Medtronic confirmed a breach of its corporate IT systems, with hacker group ShinyHunters taking credit. The company said the intrusion did not affect manufacturing, product distribution, financial reporting, patient safety, or its ability to meet patient needs. Security experts highlighted...

RunZero Masterfully Secures Fragile OT and ICS Environments
...In which hdmoore and I go "full packet-rat" and dig into what runzero have been developing to support the complicated , fragile, often safety-critical OT and ICS world. If you've ever knocked over a dusty Solaris box with an nmap...

Slack Query Exposes Massive IaC Drift Across Multi‑Cloud Stack
An engineering team at a mid‑size SaaS firm used a Slack question to discover that its documented Infrastructure‑as‑Code (IaC) inventory diverged sharply from reality across four cloud providers. The finding highlights a systemic blind spot in multi‑cloud governance and has...

GnuPG 2.5.19 Adds Kyber Post‑Quantum Encryption to Mainline Release
The GNU Privacy Guard project released version 2.5.19 on April 24, 2026, bringing Kyber (ML‑KEM/FIPS‑203) post‑quantum encryption to its mainline codebase. The update also flags the imminent end‑of‑life for the 2.4 series, urging users to upgrade promptly.

Crypto Hacks Drain $606 Million in April, Spotlighting DeFi Security Gaps
Two North Korean‑linked attacks on Solana and Ethereum projects wiped out more than $606 million in the first 24 days of April, accounting for 95% of all crypto thefts that month. The breaches triggered massive capital flight from DeFi protocols, raising...

Why Energy Infrastructure Is Cybersecurity’s Next Frontier
The energy sector’s rapid shift toward electrification, renewables, and digital grid modernization is dramatically expanding its cyber‑attack surface. Traditional, perimeter‑based security models are being replaced by a sprawling network of distributed assets—solar inverters, smart meters, storage units, and IoT sensors—that...

AI only Reports Real Bugs; Scaling Triage Is Temporary Fix
AI is not going to flood you with real vuln reports unless you have a ton of real vulns. Adding resources to a vuln disclosure process to keep up with triage & bug fixing is a temporary investment at the loud...

Not A Vendor, Still A Breach: Vercel’s Third-Party Risk Failure
Vercel’s breach occurred when an employee granted a free AI tool, Context.ai, broad OAuth permissions via a corporate Google account. Because the tool wasn’t listed as a vendor, it fell outside Vercel’s third‑party risk program, allowing attackers to infiltrate internal...

Game Over For Trust: A Roblox Cheat Gives Attackers The Advantage
Vercel suffered a supply‑chain breach after a developer downloaded a Roblox cheat that contained Lumma Stealer malware. The malware harvested OAuth and AWS tokens from Context.ai, a SaaS tool the employee had linked with a corporate Google account. Attackers used...
_Sergey_Tarasov_Alamy.png?width=1280&auto=webp&quality=80&disable=upscale)
Unpatched 'PhantomRPC' Flaw in Windows Enables Privilege Escalation
Kaspersky researcher Haidar Kabibo disclosed an unpatched Windows vulnerability dubbed PhantomRPC, which exploits a flaw in the Remote Procedure Call (RPC) architecture to let low‑privilege processes impersonate higher‑privileged ones and obtain SYSTEM rights. The bug allows an attacker to register...

The Supply Chain Is the Breach Vector. Data Recovery Is the Power Move.
The Notepad++ supply‑chain breach demonstrates how trusted development tools can become covert attack vectors, slipping past zero‑trust defenses. With 98 % of organizations expanding open‑source usage, a single compromised component can cascade across countless systems. Experts urge continuous verification, proactive SBOM...

Red Teams Leverage LLM-Generated Exploits to Strengthen Security
LLMs can chain obscure bugs into full exploits; the interesting part is how red teams are using that same capability to harden real systems. https://spectrum.ieee.org/anthropic-claude-mythos-preview-code?share_id=9389166

Bankers Most Worried About Cybersecurity, Economy: Survey
The IntraFi Bank Executive Business Outlook Survey for Q1 2026 reveals that cybersecurity has become the top concern for community‑bank executives, cited by 29 % of respondents, while worries about an economic downturn have risen to 22 %. Geopolitical tensions, especially the U.S.–Iran...
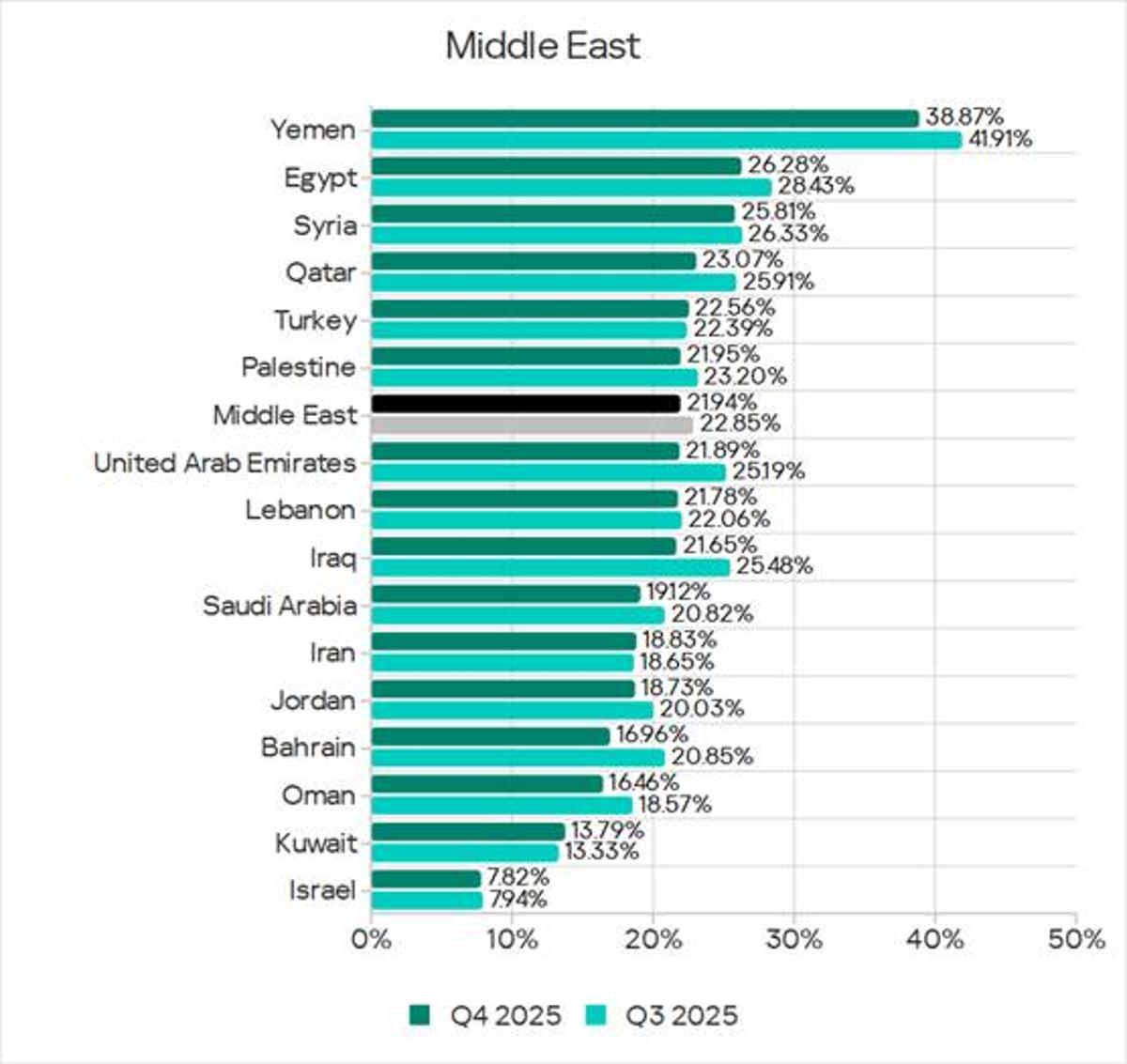
Yemen Ranks Second in ICS Attacks; Israel Among Safest
The threat landscape for industrial automation systems in the Middle East – Q4 2025: high risk of targeted attacks, network segmentation issues, and numerous espionage attacks. Yemen ranks second globally for the share of ICS computers attacked, while Israel is...

Formal Verification: Math’s Shield Against AI-Driven DeFi Hacks
🤖 "The power has shifted way more toward the attackers ... but we have one tool: formal verification. AI can break a lot of things, but it can't break math." -- @PaulFrambot on all the hacks in DeFi https://t.co/o3h67jD0JH
How Can Modern Professionals Navigate Security Risks in 2026?
Yash Jain, PwC Ireland’s cybersecurity manager, argues that security must be treated as a core business function rather than a compliance checkbox. He highlights the twin challenges of aligning security strategy with business goals and the persistent talent shortage. Jain...

Mether Pins Kelp Hack Blame on Kelp, LayerZero, Aave
.@0xMether's breakdown of fault in the Kelp hack is worth watching. He doesn't let Kelp, LayerZero, or Aave off easy. @bitsandbips https://t.co/5zLVFRyZo4

First OpenAI Spoof Spam Lands, They're Officially Big
Got my first @OpenAI related spoof spam attempt. They are now technically big time :)

Toronto SMS Blaster Case Fits Global Pattern of Chinese Cybercrime Operations Linked to State-Level Technology and Remote Command
Canadian police have charged three men with 44 offences after uncovering a mobile SMS‑blasting operation that disrupted over 13 million cellular connections across the Greater Toronto Area. The equipment, built with military‑grade components and shipped from China, was operated from vehicles...

Secure Mobile Communications: T-Priority Bridges VPN Mobility Gap
Having served as a public safety director, first responder safety is always top of mind, including secure communications when units move. Tunnel-based VPNs were never built for movement. T-Priority with T-SIMsecure closes the gap. @T_Priority Partner https://t.co/CHTZbTwufN

SMS CAPTCHAs Are Scams that Can Cost You
CAPTCHAs asking you to send an SMS are actually a scam that can cost you big time. https://t.co/IhoxFfJzCH

Government Hacking Tools Are Now in Criminals' Hands (with Lorenzo Franceschi-Bicchierai)
A former Trenchant employee covertly sold government‑grade zero‑day exploits to a Russian firm, which subsequently passed the tools to the Russian state and possibly Chinese criminal networks. The leak, detailed by TechCrunch journalist Lorenzo Franceschi‑Bicchierai on the 404 Media podcast,...

New Unpatched Windows RPC Privilege Escalation Disclosed
We reveal details of a previously unknown privilege escalation technique in Windows RPC. The vulnerability is due to an architectural flaw and is currently unpatched. We also discuss risk mitigation measures: https://t.co/TexY19gONO https://t.co/7zo8vuhtF1