Today's Cybersecurity Pulse

CISA adds critical Android and Linux flaws to KEV catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) listed two high‑severity vulnerabilities in its Known Exploited Vulnerabilities catalog: Android CVE‑2025‑48595, an integer overflow that enables privilege escalation on Android 14‑16 without user interaction, patched in June 2026; and Linux CVE‑2022‑0492, a kernel flaw also deemed actively exploited.
Also developing:
By the numbers: Ingeteam secures $82.5M loan from EIB for renewable energy R&D

Does The New Federal Data Privacy Bill Have A Snowball’s Chance Of Passing?
House Republicans introduced the SECURE Data Act, a federal privacy bill that would establish a single national standard and preempt state regulations. The legislation applies to companies handling data from over 200,000 consumers or generating at least $25 million in revenue, and grants the FTC primary enforcement authority without a private right of action. While industry groups welcome the preemption and streamlined rules, experts warn that entrenched opposition from states like California and partisan divides make passage this year unlikely.

UK Cyber Chief Warns of State‑Backed Attack Surge as £90M Funding Boosts Defences
National Cyber Security Centre head Richard Horne warned that the UK will face a surge in state‑backed cyber attacks and announced a £90 million ($115 m) funding package to accelerate AI‑powered defences for public bodies and SMEs. The warning comes as the...

45 African Nations Enact Data‑Protection Laws, Boosting Fintech and Crypto Compliance
Yellow Card’s 2026 report shows that 45 African nations have enacted data‑protection legislation, while 16 have adopted AI strategies, creating a more predictable regulatory environment for fintech, stablecoins and cross‑border payments.

#241: How Open-Source Cybersecurity Tools Could Have Helped Prevent the Kido International Cyberattack
In 2025 a ransomware‑driven breach at Kido International, a UK nursery chain, exposed personal data of roughly 8,000 children and staff, with information later posted on a dark‑web leak site. The attack stemmed from a compromised third‑party platform used to...

ShinyHunters Dumps Data From 40+ Companies, Exposing 38 Million Records
ShinyHunters has published sensitive data from more than 40 companies, totaling roughly 38 million records and terabytes of internal files. The leak, which includes 9 million Medtronic records, marks one of the year’s largest multi‑industry data dumps and forces affected firms into...

What Claude and OpenClaw Vulnerabilities Reveal About AI Agents
Security researchers at Oasis disclosed two critical vulnerability chains affecting Anthropic's Claude and the open‑source OpenClaw AI agents. In both cases a single manipulated input—whether a crafted search‑ad link or a malicious website—allowed an attacker to hijack the agent and...

DeFi’s $300M Kelp Hack Forces Liability Debate
The Kelp DAO exploit put a real number — $300M — on the question DeFi keeps avoiding: Who's liable when the infrastructure fails? @kkirkbos @TuongvyLe12 and Jessi Brooks on @DEXintheCityPod. 🎧 Timestamps: 🎙️ 0:00 Introduction live from the Eve Wealth Summit, Phoenix 🔓 2:08...

Why Cyber Threats to Critical Infrastructure Demand a New Homeland Response Model
A recent Texas flash‑flood response revealed how volunteers used the civilian Technical Awareness Kit (CIVTAK) to coordinate via personal mobile devices. The article warns that nation‑state cyber actors such as Salt Typhoon, Volt Typhoon and CARR have already infiltrated U.S....

Bill Shielding CT Residents From Data Brokers and Surveillance Passes Senate
The Connecticut Senate approved Senate Bill 4, passing 31‑4, to give residents new powers over personal data. The bill lets consumers request deletion of information held by data brokers and bans the sale of precise geolocation data. It also requires...

US, Allies Warn of Industrialized Chinese Botnets
The United States, United Kingdom and eight allied nations warned that Chinese state‑backed groups are operating industrial‑scale botnets using compromised routers and IoT devices. The joint advisory identified the Volt Typhoon operation, which hijacks outdated Cisco and Netgear routers to expand...
Hasbro Expects March Cyberattack to Impact Second-Quarter Revenue
Hasbro disclosed that a March 2026 cyberattack will affect its second‑quarter revenue and operating profit. The breach forced key order‑processing, shipping and invoicing systems offline, prompting a forensic investigation and added costs. The company expects most delays to be recovered...

Top 5 Roadblocks for MSPs, and How MDR Helps
Managed service providers (MSPs) are grappling with talent shortages, rising costs, and complex security environments, making cyber resiliency a top strategic priority for 35% of them. OpenText’s managed detection and response (MDR) service offers 24/7 threat monitoring, AI‑driven alert triage,...

US Lawmakers Push National Data Privacy Rules Amid State Preemption Concerns
House Republicans introduced two sweeping federal privacy bills—the SECURE Data Act for non‑financial firms and the GUARD Financial Data Act for banks and lenders—to replace a patchwork of state rules. Both proposals grant consumers rights to access, correct, delete, and...

SymphonyAI Helps Payments Giant Slashes Compliance
A global payments processor handling over 200 billion transactions in FY 2024 replaced its fragmented, legacy compliance stack with SymphonyAI’s cloud‑native platform. The new active‑active SaaS solution delivers 99.99% availability and leverages agentic AI to orchestrate workflows, cutting alert processing time by...

Sri Lanka Sets Roles for Digital ID Rollout with DRP, GovTech Split
Sri Lanka has designated the Department of Registration of Persons (DRP) as the legal custodian of its national digital identity system, SL‑UID, while GovTech Sri Lanka will manage technical delivery and ongoing operations. The rollout will be phased, beginning with...
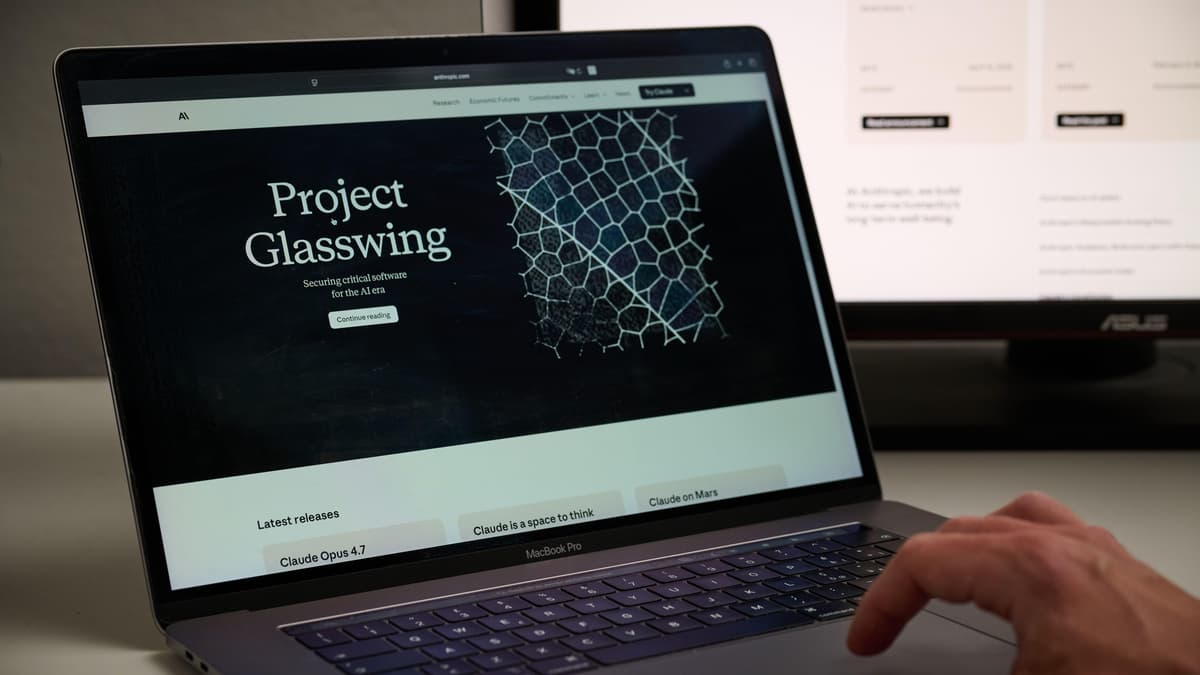
Glasswing Secured the Code. The Rest of Your Stack Is Still on You
Anthropic’s Project Glasswing, showcased by the Mythos Preview model, uncovered a 16‑year‑old FFmpeg vulnerability that five million conventional scans missed. The AI’s ability to read code intent, rather than merely enumerate patterns, marks a shift from signature‑based tools toward understanding‑driven security. While...
4 Easy Ways to Stay on Top of Cybersecurity in the Workplace
The article outlines four practical steps for keeping workplace cybersecurity robust: isolating corporate systems from personal devices, preparing staff for AI‑driven threats, strengthening authentication, and maintaining up‑to‑date software. It emphasizes remote‑work realities, the rise of AI‑enabled attacks, and the need...

Commvault Cosies up to Google’s Cloud
Commvault has launched its Commvault Cloud platform and the Clumio SaaS service on Google Cloud, extending unified data protection and ransomware‑resilient backups to GCP workloads. The offering includes native protection for BigQuery, Compute Engine, GKE, Cloud SQL, and Google Workspace,...

Governments on High Alert After CISA Snuffs Out Firestarter Backdoor on Fed Network
CISA disclosed that a previously unknown backdoor malware, dubbed Firestarter, breached a U.S. Federal Civilian Executive Branch agency by compromising a Cisco Firepower ASA firewall. The malware can retain persistent access even after firmware updates, allowing attackers to re‑enter networks...

Windows 10 Support Is Over. Here Are 6 Options for Users
Microsoft ended mainstream support for Windows 10 on Oct. 14 2025, leaving an estimated 500 million PCs exposed to unpatched vulnerabilities. Users can upgrade to Windows 11 for free if their hardware meets TPM 2.0 and other specs, buy a new device, or rent a cloud‑hosted...

In Other News: Unauthorized Mythos Access, Plankey CISA Nomination Ends, New Display Security Device
The weekly roundup highlights several high‑profile security developments: Anthropic’s Claude Mythos AI model was accessed by unauthorized testers through a third‑party vendor, prompting tighter access restrictions. Sean Plankey withdrew his nomination for CISA director, leaving the agency without a permanent leader....

How AI Is Changing Healthcare Compliance and Why Most Apps Aren’t Ready
Artificial intelligence is now a staple in healthcare compliance, powering automated audit‑trail analysis, policy management, continuous risk scoring, and rapid incident detection. However, once AI models ingest protected health information, they fall under HIPAA, state privacy statutes, and breach‑notification rules,...

More Ancient Linux Device Support Faces the Chop
The Linux kernel community is accelerating the removal of legacy drivers to curb long‑standing bugs exposed by LLM‑powered vulnerability scanners. Andrew Lunn’s 18‑patch series targets 3Com Ethernet cards, several Xircom and PCMCIA devices, and newer but still two‑decade‑old adapters like...
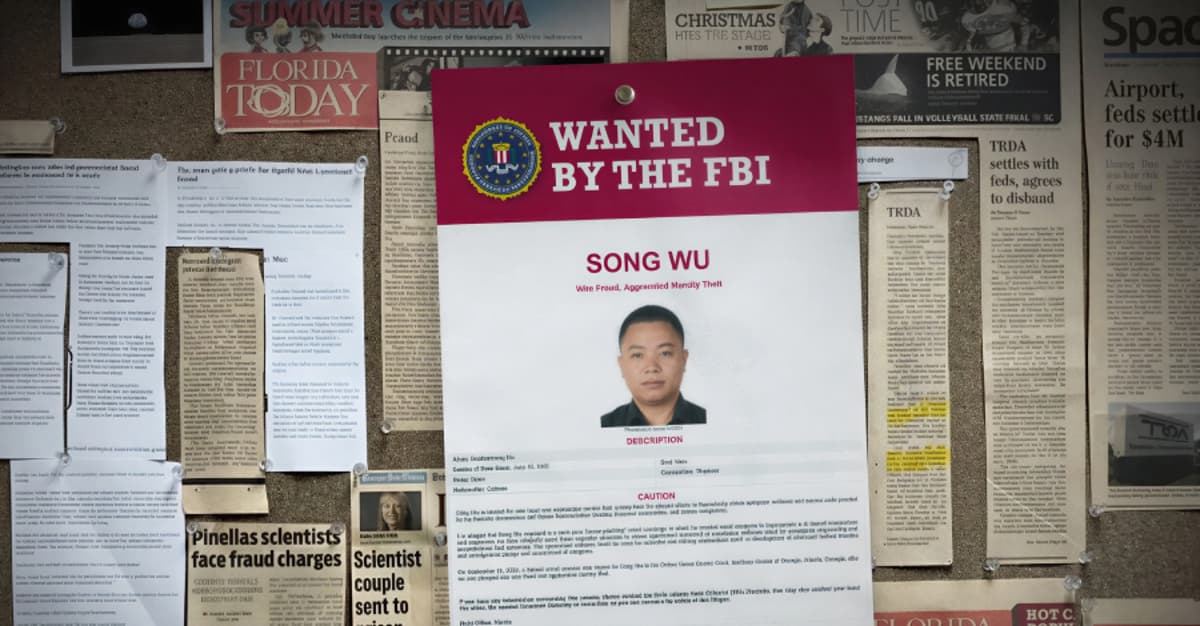
NASA Employees Duped in Chinese Phishing Scheme Targeting U.S. Defense Software
The U.S. Office of Inspector General disclosed that a Chinese national, Song Wu, impersonated American researchers to obtain NASA and defense‑related aerospace software through a multi‑year spear‑phishing campaign. The scheme targeted employees at NASA, the military services, universities and private...

DORA and Operational Resilience: Credential Management as a Financial Risk Control
The EU's Digital Operational Resilience Act (DORA) took effect on January 17, 2025, turning credential security into a binding financial risk control for banks and other financial entities. Article 9 mandates least‑privilege access, mandatory phishing‑resistant MFA, and cryptographic key protection, with...

Mid-Size Firms See Cybersecurity as Essential, Not Optional
From ISMG: cybersecurity is becoming a must have for mid sized firms, not a nice to have. https://buff.ly/HzPfKHs The interesting shift is not the decision to invest. It is how organizations are deciding what actually moves the needle.

Strategies for Security and Governance in AI with Insightsoftware, Informatica, and OpenText
Public disclosures of AI‑related risks have surged, with 72% of S&P 500 firms reporting concerns by 2025, up from just 12% in 2023. A DBTA roundtable titled “Taming AI Risks” featured insightsoftware, Informatica and OpenText discussing how to secure data, models,...

Signal Phishing Campaign Targets Germany’s Bundestag President Julia Klöckner
Germany’s Bundestag President Julia Klöckner was compromised in a Signal phishing attack that used a fake CDU group chat. Attackers tricked her into revealing her PIN and verification code, bypassing Signal’s encryption without breaking the protocol. The incident follows earlier warnings...

‘As Deployments Grow, so Does the Need,’ Says Sungrow North America Cybersecurity Director
Sungrow’s North America cybersecurity director Michael Hudson says the company builds its battery‑energy‑storage‑system (BESS) security on the IEC 62443 framework for utility‑scale and commercial‑industrial products, while residential inverters follow IoT standards such as EN 303645 and EN 18031. He notes the cybersecurity team...

Toronto Police Arrest Three in Canada’s First Mobile SMS Blaster Case
Toronto police have arrested three men in Canada’s first known case involving a mobile SMS blaster, a device that impersonates cellular towers to send mass phishing texts. The investigation, which began in November, uncovered tens of thousands of phones connecting...

Over 10,000 Zimbra Servers Vulnerable to Ongoing XSS Attacks
Shadowserver reports more than 10,500 publicly exposed Zimbra Collaboration Suite servers remain vulnerable to CVE‑2025‑48700, a cross‑site scripting flaw that lets attackers run arbitrary JavaScript without user interaction. Synacor issued patches in June 2025, but many installations, especially in Asia and...

The Cost of One Wrong Click How Businesses Reduce Digital Risk
A single phishing click can trigger weeks of downtime, costly recovery, legal exposure, and brand damage. The article explains that modern digital risk requires layered defenses—people, processes, and technology—rather than one‑off tools. It details financial, reputational, and productivity impacts, and...

Cybersecurity Meets Geopolitics at Top EU Court
Advocate General Tamara Ćapeta issued a non‑binding advisory opinion in the Elisa Eesti v Estonia case, concluding that EU law permits member states to exclude hardware and software from telecom networks when the supplier is deemed a national‑security risk. The opinion validates...

India's Finance Minister Calls for AI‑Driven Cybersecurity Overhaul in Banks
Finance Minister Nirmala Sitharaman told Indian banks to adopt new, AI‑centric defenses after a high‑level meeting on April 24. She warned that advanced models such as Anthropic's Claude Mythos could weaponise software vulnerabilities, prompting the Indian Banks Association to lead...

US Warns of China‑Backed AI Model‑Theft Campaigns Threatening Big Data Assets
The White House Office of Science and Technology Policy disclosed a large‑scale campaign by Chinese actors to steal proprietary AI models, using tens of thousands of fake accounts to bypass safeguards. Officials say the effort threatens U.S. intellectual property and...

Proton CEO Warns Age‑verification Mandates Could Kill Online Anonymity, Reshape Digital Ads
Proton founder‑CEO Andy Yen warned that worldwide pushes for mandatory age verification will end online anonymity, a change that could upend data‑driven advertising. At the same time, the VPN Trust Initiative cautioned the UK’s child‑safety consultation could strip essential privacy...

85% of Enterprises Are Running AI Agents. Only 5% Trust Them Enough to Ship.
Eighty‑five percent of enterprises are running AI‑agent pilots, yet only five percent have moved those agents into production, highlighting a massive trust gap. Cisco’s President Jeetu Patel blamed the lack of a trust architecture and announced a suite of security...

Infra Provider's Data Integrity Breach Triggers Real WTH Moment
A terrible incident coming from an infra provider. This is not an outage resulting in downtime, or data lost on the cloud (that is trivial to restore from local git.) It’s a data integrity issue, which sounds hard and difficult to...

Wave of Account Hacks Prompts Call for Platform Action
A number of folks accounts have been hacked recently, including it seems Robin Brooks -- please read this X needs to do something; I haven't been hacked but I have seen a wave of bad impersonators https://t.co/t06AZKPM5y

Why Cybersecurity Must Rethink Defense in the Age of Autonomous Agents
At RSA 2026, the cybersecurity community highlighted the emergence of agentic AI—autonomous systems that can act without human direction. Frameworks such as Mythos demonstrate how AI can orchestrate multi‑step attacks, while defenders are urged to counter with AI‑driven tools. Analysts...

Cybersecurity Now the Gatekeeper to Business Growth
Cybersecurity is becoming a gatekeeper to business. Companies that can’t prove strong security risk losing access to supply chains, insurance, and markets. Cyber maturity is now a key differentiator for growth. https://t.co/Qup5czOaF2

Secure Crypto with SOPs and Hardware Wallets
Learn how to deal with crypto: → Use a hardware wallet → Sign from a dedicated computer → Build an SOP: verify the data, simulate the tx, validate expectations, etc → Run the SOP every single time. No exceptions. Start today, don't wait until you...

Locked Shields 2026: 41 Nations Strengthen Cyber Resilience in World’s Biggest Exercise
Locked Shields 2026, the NATO‑run live‑fire cyber defence exercise, wrapped up with over 4,000 participants representing 41 nations. Teams defended simulated attacks on air‑defence systems, e‑voting platforms and other critical infrastructure while also confronting disinformation and political pressure. The three...

Cybercrime Goes Corporate: AI‑Powered Attacks Demand Faster Security
Cybercrime is no longer a side hustle. Groups run like companies, with R&D, automation, & AI in daily use. They test, refine, and scale attacks with speed. AI gives them faster recon, stronger impersonation, and wider reach. If you build fast, secure with the...

Beware: @Teasri Hacked, Fraudulent DM Links Circulating
New scam underway. Unfortunately @teasri appears to have been hacked. DMs are being sent with a link that certainly appears fraudulent. Be on guard.

CISA, NCSC UK, and Global Partners Issue Advisory on Chinese Government-Linked Covert Cyber Networks
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the U.K.’s National Cyber Security Centre (NCSC‑UK), together with FBI, NSA, DoD and partners from nine allied nations, issued a joint advisory on Chinese government‑linked covert networks. The advisory details how...

Botnets Conceal Origins While Powering DDoS Attacks
The botnets are used to hide locations and launch Distributed Denial of Service attacks. https://t.co/s6FzDuqe1h
AI Enables Hyper-Personalized Scams Exploiting Your Data
AI is making scams far more personal. Messages can now be tailored with real details about you, making them harder to detect and more convincing. The shift is subtle but serious. The more AI knows, the easier it becomes to exploit trust....

Bounty Platforms Need Spam Detection Like Email Systems
Instead of no bug bounty companies like HackerOne need to figure out how to flag potential bounty spam the same way email systems flag spam.

Hidden ID Bug Lets Sites Track Private Mode Users
Researchers found a bug where websites could create a hidden ID and track users even in Private Mode. https://t.co/BkljdOYXC0