Glasswing Secured the Code. The Rest of Your Stack Is Still on You
Companies Mentioned
Why It Matters
The breakthrough proves AI can surface hidden flaws that traditional scanners overlook, urging security teams to adopt context‑aware tools before attackers exploit the far more common configuration gaps.
Key Takeaways
- •Mythos Preview identified 16‑year‑old FFmpeg bug missed by 5M scans.
- •Traditional scanners rely on pattern matching, not code intent understanding.
- •Misconfigurations, exposed credentials cause most breaches, not zero‑days.
- •Glasswing’s disclosures will trigger a wave of patches across vendors.
- •Organizations must unify asset inventory to act on AI‑driven insights.
Pulse Analysis
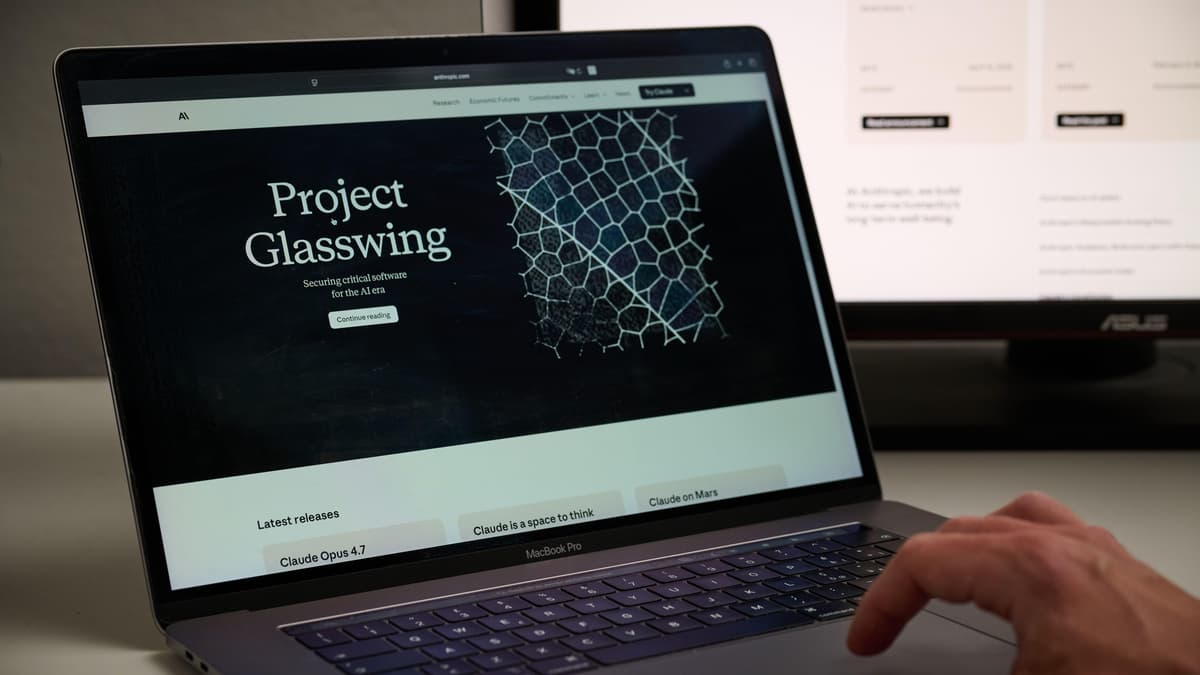
Anthropic’s Project Glasswing has thrust generative AI into the spotlight of application security. By deploying Mythos Preview, a model that parses code semantics, the team exposed a decades‑old FFmpeg flaw that evaded five million conventional fuzzer passes. This achievement underscores a fundamental limitation of today’s security stack: most tools operate on enumeration—matching known signatures or version numbers—rather than truly understanding software behavior. As AI models become adept at reasoning about intent, they promise to close gaps that human analysts once guarded alone.
Yet the article reminds readers that code‑level exploits represent only a fraction of real‑world incidents. The majority of breaches arise from misconfigurations, stale credentials, and forgotten cloud assets—issues that persist regardless of AI sophistication. Current CSPM, IAM, and configuration‑management solutions still depend on rule‑based checks, leaving blind spots when environments evolve faster than policies. The Glasswing episode, where a sandbox escape hinged on an unreviewed outbound email service, illustrates how a single configuration oversight can nullify even flawless code security.
For enterprises, the immediate implication is twofold. First, Glasswing’s coordinated disclosures will generate a surge of patches and advisories, demanding rapid SBOM verification and asset inventory updates. Second, security leaders must look beyond scanners and invest in platforms that synthesize data across identity, configuration, and posture layers, delivering context‑rich alerts. Embracing AI that reasons about entire environments—not just code—will be essential to stay ahead of attackers who continue to exploit the low‑hanging fruit of mismanaged assets.
Glasswing Secured the Code. The Rest of Your Stack Is Still on You
Comments
Want to join the conversation?
Loading comments...